Blockchain Network Security Vulnerabilities


Meaning ⎊ Blockchain network security vulnerabilities represent structural failures in cryptographic or economic logic that threaten the finality of capital.
Blockchain Network Security Vulnerabilities and Mitigation


Meaning ⎊ Blockchain network security vulnerabilities represent systemic risks to settlement finality, requiring rigorous economic and cryptographic mitigation.
Blockchain System Vulnerabilities


Meaning ⎊ Blockchain System Vulnerabilities represent the structural defects in protocol logic that undermine deterministic settlement in derivative markets.
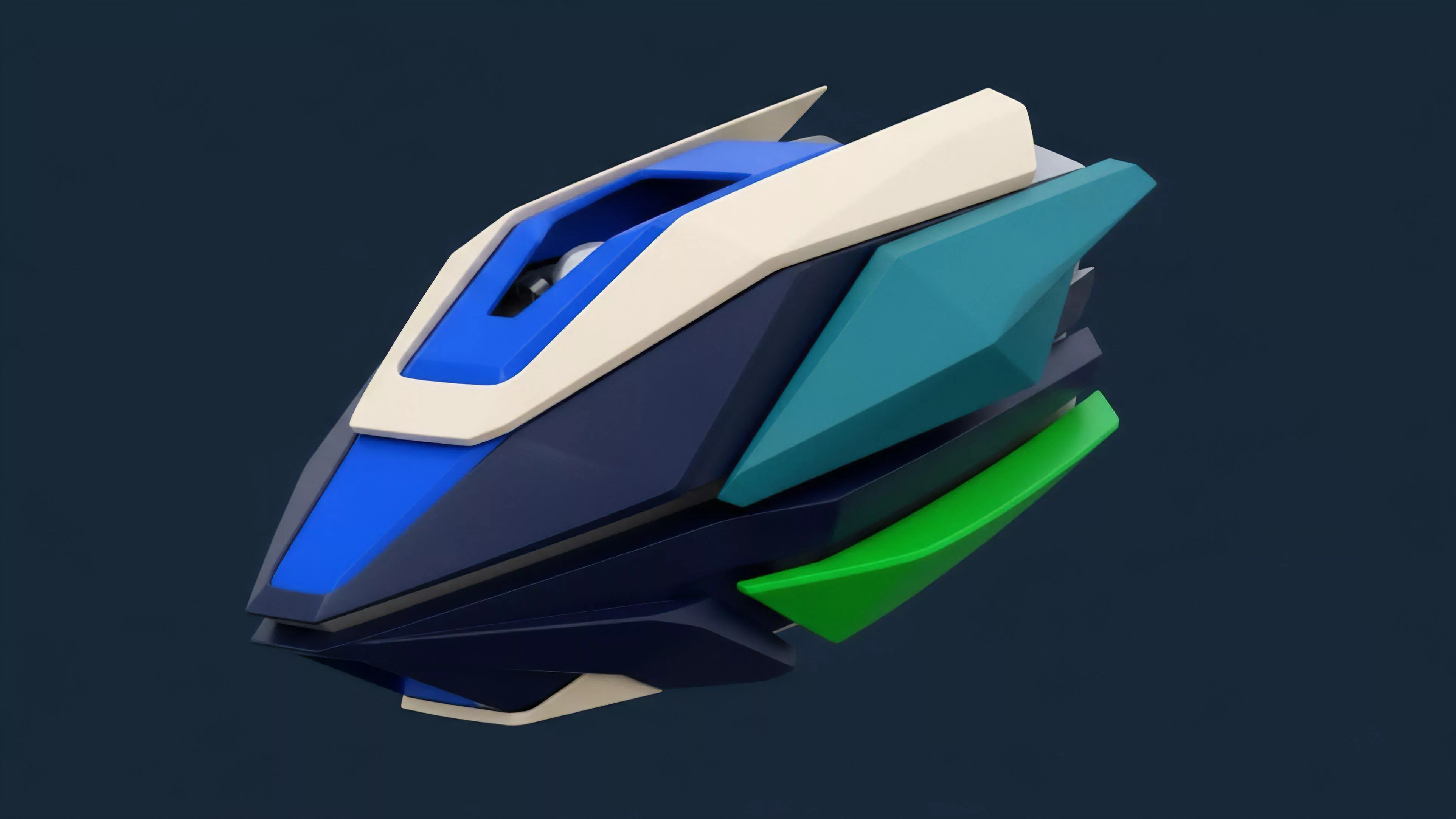
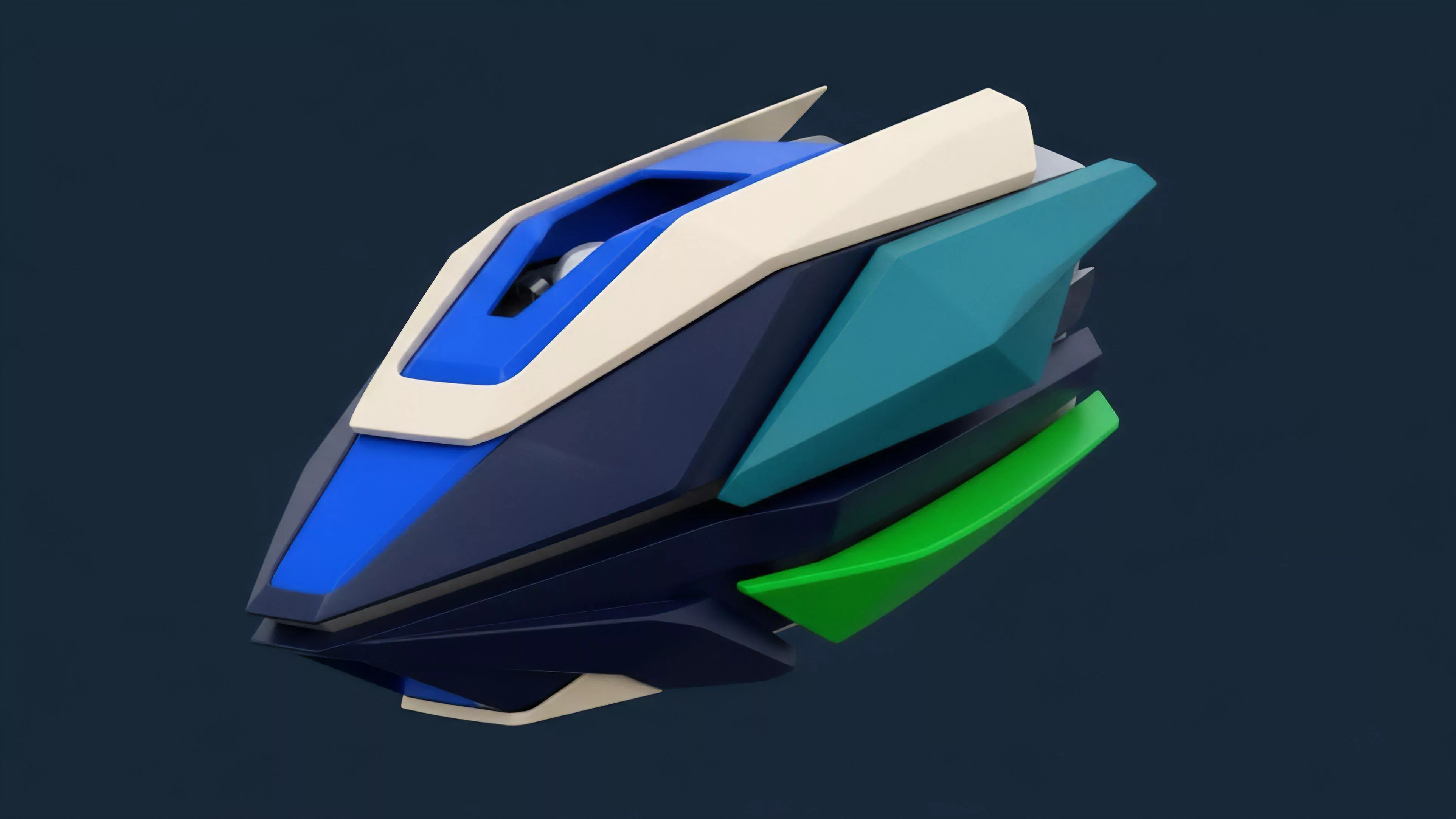
Protocol Architecture Design


Meaning ⎊ The Decentralized Volatility Engine Architecture is a systemic framework for abstracting and dynamically managing aggregated options risk and liquidity through automated, quantitative models.
Order Book Architecture Design Future


Meaning ⎊ Order Book Architecture Design Future establishes a deterministic framework for verifiable, high-speed matching of crypto derivatives without central risk.
Order Book Architecture Evolution Trends


Meaning ⎊ Order Book Architecture Evolution Trends define the transition from opaque centralized silos to transparent high-performance decentralized execution layers.
Order Book Architecture Evolution Future


Meaning ⎊ The Hybrid Liquidity Nexus is an architectural synthesis combining high-speed off-chain order matching with trustless on-chain collateral and risk settlement for crypto options.
Hybrid Order Book Architecture


Meaning ⎊ Hybrid Order Book Architecture integrates high-speed off-chain matching with on-chain settlement to achieve institutional performance and custody.
Hybrid Model Architecture


Meaning ⎊ The Decentralized Liquidity Hybrid Architecture combines off-chain order matching with an on-chain AMM and settlement layer to achieve capital-efficient, low-latency, and trustless crypto options trading.
Margin Model Architecture


Meaning ⎊ Standardized Portfolio Margin Architecture optimizes capital efficiency by netting risk across diverse positions while maintaining protocol solvency.
Order Book Architecture Design


Meaning ⎊ HCLOB-L2 is an architecture that enables high-frequency options trading by using off-chain matching with on-chain cryptographic settlement.
Margin Calculation Vulnerabilities


Meaning ⎊ Margin calculation vulnerabilities represent the structural misalignment between deterministic liquidation logic and the fluid reality of market liquidity.
Order Book Security Vulnerabilities


Meaning ⎊ Order Book Security Vulnerabilities define the structural flaws in matching engines that allow adversarial actors to exploit public trade intent.
Smart Contract Security Vulnerabilities


Meaning ⎊ Oracle Manipulation and Price Feed Vulnerabilities compromise the integrity of derivatives contracts by falsifying the price data used for collateral, margin, and final settlement calculations.
Modular Architecture


Meaning ⎊ Decentralized Options Vault architecture automates options strategies and aggregates liquidity to capture the volatility risk premium, improving capital efficiency in decentralized markets.
Oracle Manipulation Vulnerabilities


Meaning ⎊ Oracle manipulation vulnerabilities exploit external data dependencies in smart contracts to trigger unfair liquidations or misprice derivative settlements.
Code Vulnerabilities


Meaning ⎊ Code vulnerabilities in crypto options protocols create systemic financial risks by enabling economic exploits through logic flaws or external input manipulation.
Black-Scholes Model Vulnerabilities


Meaning ⎊ The Black-Scholes model's core vulnerability in crypto stems from its failure to account for stochastic volatility and fat tails, leading to systemic mispricing in decentralized markets.
Decentralized Finance Vulnerabilities


Meaning ⎊ Decentralized Finance Vulnerabilities represent the emergent systemic risks inherent in protocol composability and automated capital flows, requiring a shift from static code audits to dynamic risk management.
Security Vulnerabilities


Meaning ⎊ Security vulnerabilities in crypto options are systemic design flaws in smart contracts or economic models that enable value extraction through oracle manipulation or logic exploits.
Margin Engine Vulnerabilities


Meaning ⎊ Margin engine vulnerabilities represent systemic risks in derivatives protocols where failures in liquidation logic or oracle data can lead to cascading bad debt and market instability.
Consensus Mechanism Vulnerabilities


Meaning ⎊ Consensus mechanism vulnerabilities threaten derivative settlement integrity by compromising price feeds and collateral finality through state manipulation and network failures.
Delta Hedging Vulnerabilities
Meaning ⎊ Delta hedging vulnerabilities in crypto arise from high volatility and fragmented liquidity, causing significant gamma and slippage losses for market makers.
Front-Running Vulnerabilities


Meaning ⎊ Front-running vulnerabilities in crypto options exploit public mempool transparency and transaction ordering to extract value from large trades by anticipating changes in implied volatility.
Protocol Vulnerabilities


Meaning ⎊ Protocol vulnerabilities represent systemic design flaws where a protocol's economic logic or smart contract implementation allows for non-sanctioned value extraction by sophisticated actors.
Modular Blockchain Architecture


Meaning ⎊ Modular Blockchain Architecture separates execution from settlement to enable high-performance derivatives trading by optimizing throughput and reducing systemic risk.
Hybrid Architecture Models


Meaning ⎊ Hybrid architecture models for crypto options balance performance and trustlessness by moving high-speed matching off-chain while maintaining on-chain settlement and collateral management.
Multi-Chain Architecture


Meaning ⎊ Multi-Chain Architecture optimizes options trading by segmenting risk and unifying liquidity across different blockchains, enhancing capital efficiency for decentralized derivatives markets.
CLOB-AMM Hybrid Architecture


Meaning ⎊ CLOB-AMM hybrid architecture combines order book precision with automated liquidity provision to create efficient and robust decentralized options markets.
