Essence
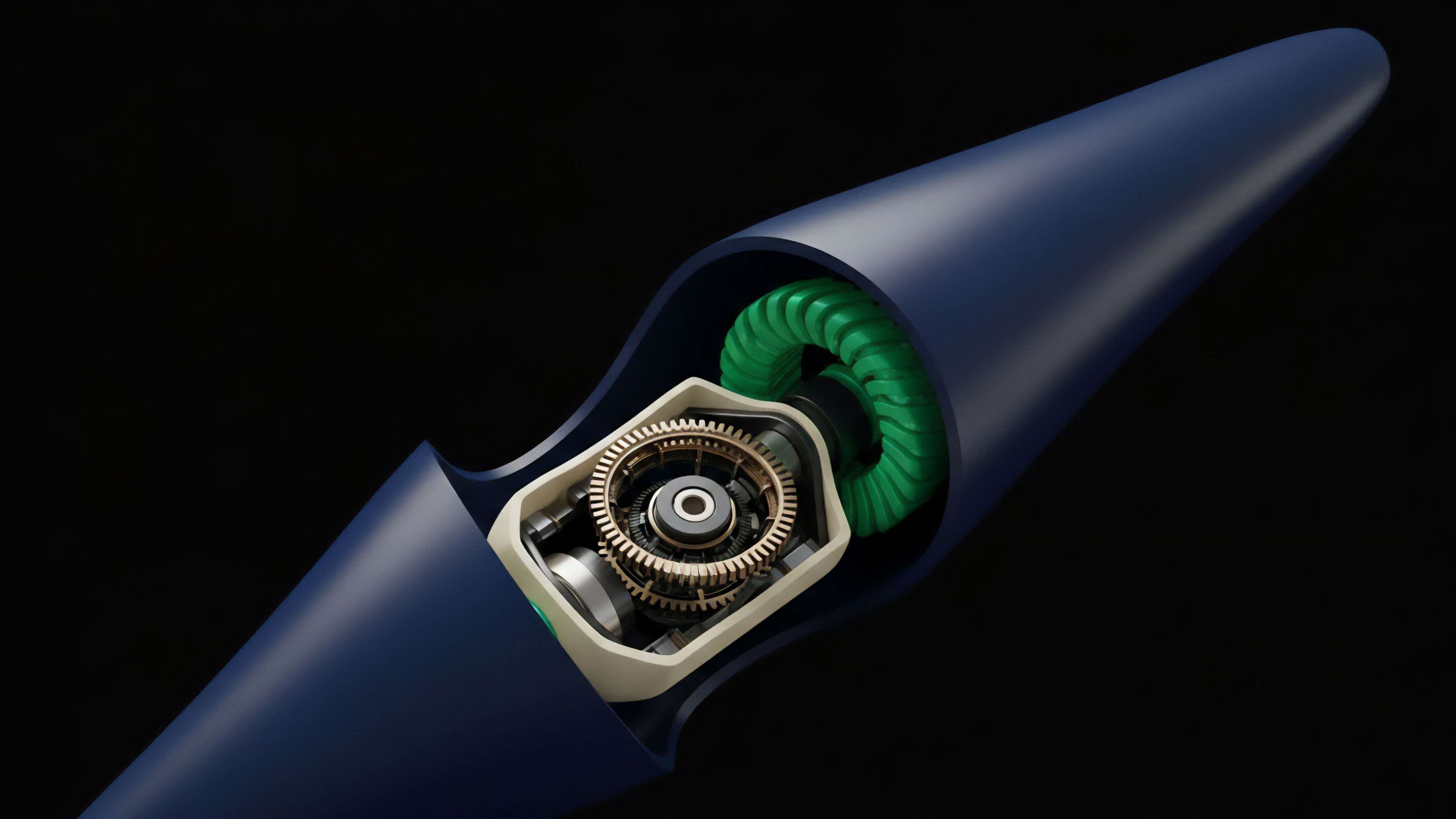
Front-running in crypto options markets is the exploitation of information asymmetry in a public transaction queue. It is a fundamental challenge rooted in the design of decentralized systems, where pending transactions ⎊ and specifically, large options orders ⎊ are broadcast to a transparent mempool before being confirmed on-chain. This transparency creates a time-sensitive window of opportunity for sophisticated market participants, known as searchers, to execute profitable trades based on the anticipated market impact of the incoming order.
The vulnerability arises because a large options trade, particularly one involving non-linear instruments, carries significantly more information than a simple spot trade. A large purchase of call options, for instance, signals a specific directional bias and potentially changes the implied volatility surface, allowing a front-runner to adjust their own positions or create new ones to capitalize on the expected price movement before the original order settles. This dynamic creates a cost for the initial trader, effectively reducing the liquidity available to them and creating systemic inefficiencies within the protocol.
Front-running in crypto options markets exploits the public nature of pending transactions to gain an informational edge and execute trades based on anticipated market impact.
The core issue is that options pricing models are highly sensitive to volatility, and large orders directly impact the implied volatility (IV) surface. A front-runner, observing a large order for a specific strike price, can predict the resulting shift in IV and trade other options on the same surface before the change propagates through the system. This extraction of value ⎊ often referred to as Maximal Extractable Value (MEV) ⎊ is a direct consequence of the adversarial nature of open financial systems where transaction ordering is a source of profit.
The vulnerability is not simply about price slippage; it is about the decay of a protocol’s core function, where the cost of participation for sophisticated traders increases, leading to reduced liquidity provision and less accurate pricing for all users.

Origin
The concept of front-running predates decentralized finance, having its roots in traditional financial markets where it typically involved a broker executing trades on their own account based on knowledge of a client’s large pending order. This form of front-running was illegal and regulated by bodies like the SEC.
The shift to high-frequency trading (HFT) introduced a different form of front-running based on latency arbitrage, where firms with faster connections to exchanges could execute trades milliseconds ahead of others. The advent of decentralized finance, however, created a unique environment where this vulnerability became an intrinsic part of the protocol’s architecture. The origin story of crypto front-running is tied directly to the public mempool and the block production mechanism.
The initial manifestation of front-running in DeFi began with simple arbitrage bots scanning the mempool for large swaps on decentralized exchanges. These bots would identify a pending swap that would significantly move the price of an asset, then execute a trade before the swap and sell immediately after to capture the price difference. In options markets, this evolved with the rise of on-chain options protocols.
Unlike spot markets, options protocols require specific liquidity provision and pricing models that are particularly sensitive to large orders. The vulnerability was initially a side effect of transparent transaction queues, but it quickly evolved into a sophisticated, institutionalized industry with the advent of MEV. The transition from Proof-of-Work (PoW) to Proof-of-Stake (PoS) in Ethereum changed the mechanics of front-running.
In PoW, miners could reorder transactions within a block to extract MEV. With PoS, the role shifted to validators and a new set of actors called searchers and builders. This created a new market for block space where searchers compete to create profitable bundles of transactions (including front-running attacks) and pay builders (who create the blocks) for inclusion.
This shift formalized front-running from an opportunistic attack into a core component of market microstructure.

Theory
The theoretical underpinnings of front-running in options markets lie at the intersection of market microstructure, game theory, and quantitative finance. The primary theoretical model for options pricing is Black-Scholes-Merton (BSM), which relies on several assumptions, including continuous trading and efficient markets where information is instantaneously reflected in prices.
Front-running violates these assumptions by creating an information lag between the public mempool and on-chain settlement. The front-runner acts as a latency arbitrageur, exploiting the time delay inherent in block production.

Mempool Information and Price Discovery
The mempool acts as a pre-price discovery mechanism. When a large options order enters the mempool, it contains information about future price expectations or volatility. A front-runner analyzes this information to predict the impact on the implied volatility surface.
The front-runner’s profit is derived from the difference between the pre-trade price and the post-trade price, minus the cost of the transaction fee (gas). This process is an application of a zero-sum game where the front-runner’s gain is the original trader’s loss.

Adversarial Game Theory and Order Flow
From a game theory perspective, front-running is an adversarial interaction where participants attempt to maximize their individual utility within a system of transparent information. The interaction can be modeled as a dynamic game with three main players:
- The User: A large trader seeking to execute an options trade at the best possible price.
- The Searcher/Front-Runner: An automated agent monitoring the mempool for profitable opportunities.
- The Validator/Builder: The entity responsible for including transactions in a block and determining their order.
The searcher’s strategy involves identifying profitable opportunities, calculating the optimal sandwich attack parameters, and bidding for priority inclusion in the block. The validator’s strategy involves selecting the most profitable block from a set of proposals, effectively monetizing the searcher’s activity. The user, in turn, attempts to mitigate this risk by using private relays or other methods.

Options Greeks and Volatility Arbitrage
The financial theory of front-running options centers on the options Greeks, specifically Vega (sensitivity to implied volatility) and Delta (sensitivity to underlying price changes). A large options order can signal a shift in implied volatility. For instance, if a large order for out-of-the-money call options is placed, a front-runner can anticipate an increase in implied volatility across the entire options chain.
The front-runner can then quickly purchase other options with high vega exposure before the price update. This form of front-running is more complex than simple spot arbitrage because it requires a deeper understanding of options pricing dynamics and the interconnectedness of different strike prices and maturities.
| Attack Vector | Affected Options Greek | Mechanism |
|---|---|---|
| Sandwich Attack (Spot) | Delta | Front-runner buys before large spot trade, sells after, profiting from price slippage. |
| Volatility Arbitrage (Options) | Vega | Front-runner buys options based on anticipated shift in implied volatility from a large options order. |
| Liquidation Front-Running | Gamma/Delta | Front-runner liquidates a position before a large, pending liquidation, avoiding the price drop. |

Approach
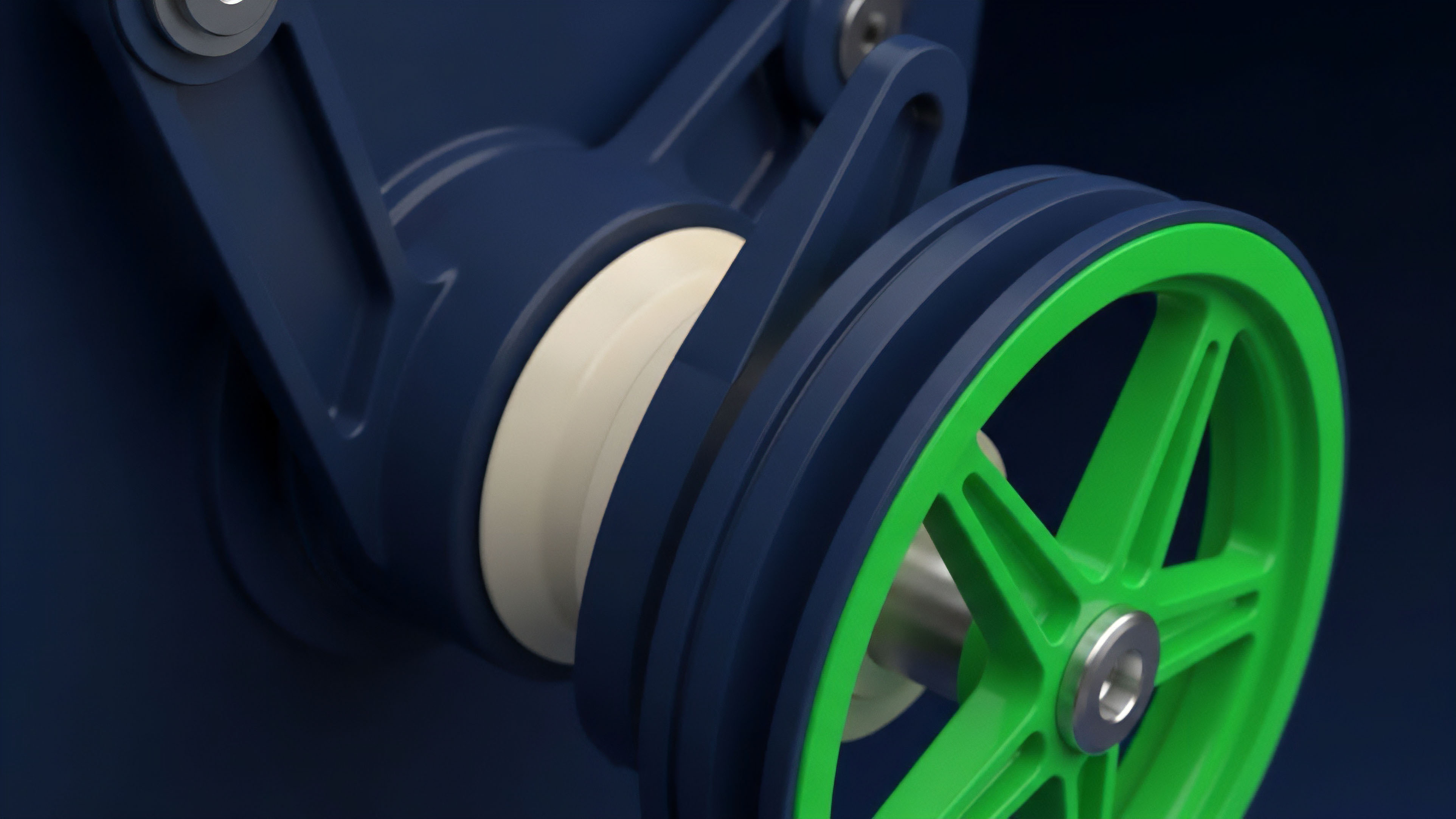
Front-running attacks on options protocols utilize specific strategies tailored to the market’s structure. The most common attack, the sandwich attack, involves three steps: first, identifying a large options order in the mempool; second, placing a front-running order to execute immediately before the target order; and third, placing a back-running order to execute immediately after the target order. The front-runner profits from the price difference caused by the target order’s execution.
This approach is highly automated, relying on bots that continuously scan mempools for profitable opportunities.
Private Relays and Transaction Obfuscation
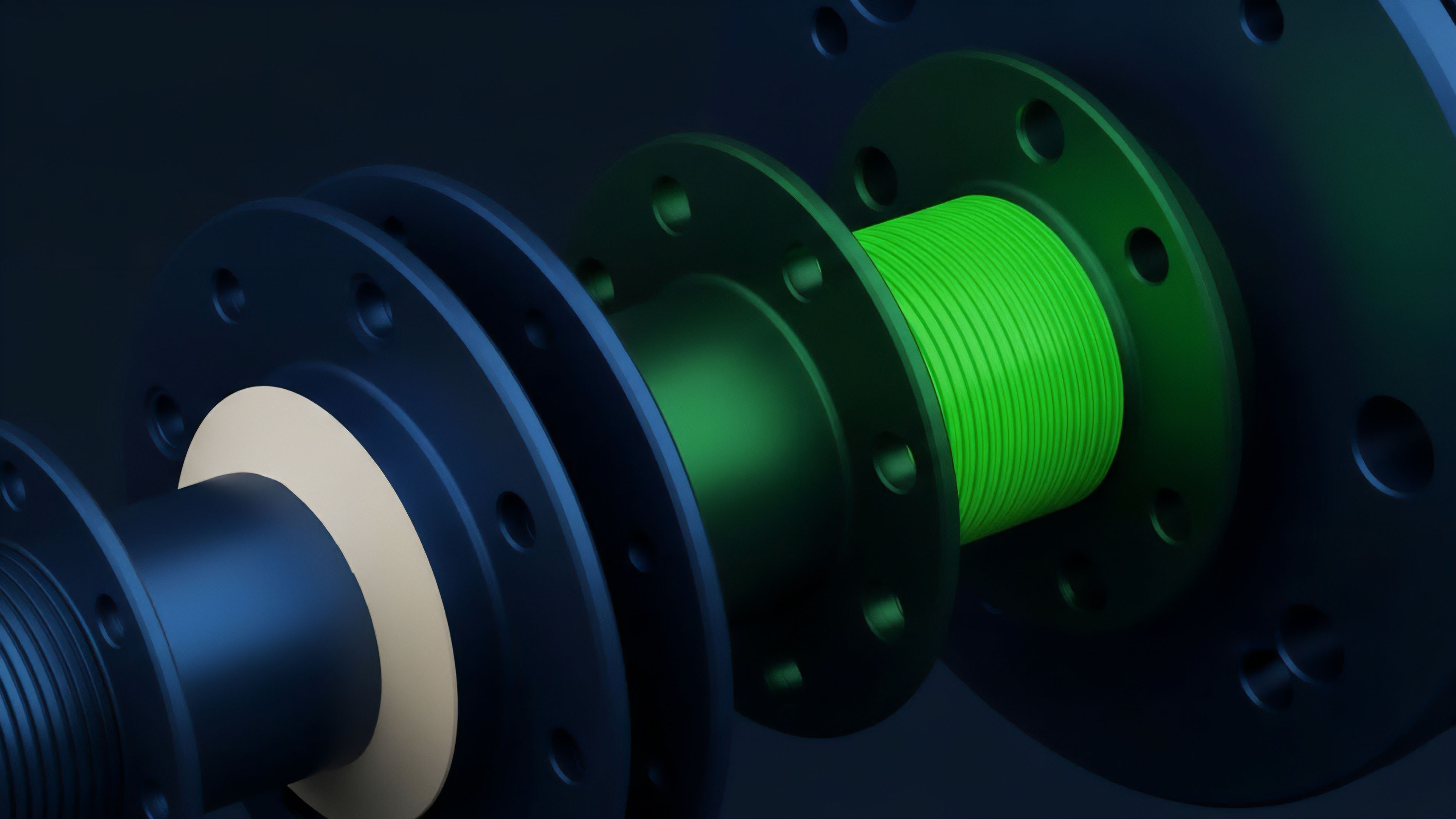
The primary mitigation strategy against front-running involves preventing the initial order from entering the public mempool. This is achieved through private transaction relays. A private relay sends the transaction directly to a block builder, bypassing the public mempool entirely.
The builder then includes the transaction in a block without revealing it to other searchers. This approach significantly reduces the front-running opportunity for sandwich attacks, though it introduces trust assumptions between the user and the private relay/builder.

Batch Auctions and Periodic Settlement
An alternative approach to mitigate front-running is the use of batch auctions, where orders are collected over a specific time period and settled at a single, uniform price. This removes the sequential ordering advantage that front-runners exploit. Orders are submitted in a hidden or encrypted format, and a solver finds the optimal clearing price for all orders in the batch.
This approach shifts the competition from transaction ordering to solver efficiency, making it difficult for front-runners to gain an advantage by anticipating a specific order’s execution price.
Order Flow Auctions and MEV-Boost
The current state of MEV extraction has led to a market where searchers pay block builders for priority transaction inclusion. This system, often facilitated by MEV-boost, has formalized the process of front-running. The approach here for a protocol is to either compete in this market or to attempt to capture the MEV generated by its users.
The protocol can offer order flow auctions, where users’ order flow is sold to searchers, and the profits are returned to the user in the form of a rebate. This transforms the front-running cost into a revenue stream for the user, mitigating the negative impact of the attack.
| Mitigation Strategy | Mechanism | Trade-off/Limitation |
|---|---|---|
| Private Relays | Bypass public mempool, send directly to builder. | Trust assumption on the builder; centralization risk. |
| Batch Auctions | Orders settled at a single price at fixed intervals. | Reduced execution speed; potential for price staleness. |
| Encrypted Commits (F-MEC) | Orders are encrypted in the mempool; revealed only after block inclusion. | Requires specific cryptographic assumptions; potential for decryption delays. |

Evolution
Front-running vulnerabilities have evolved significantly, moving from simple, opportunistic arbitrage to sophisticated, systemic MEV extraction. Initially, front-running was a simple race condition where the fastest bot could execute a trade ahead of another. This “gas war” model involved searchers competing to pay the highest gas price to ensure their transaction was included first.
The introduction of MEV-focused infrastructure transformed this dynamic. The evolution of front-running in options markets closely mirrors the development of MEV extraction in general. The initial stage involved simple, on-chain arbitrage.
The second stage saw the rise of sophisticated searchers and MEV relays. The third stage, particularly with the transition to PoS, introduced Proposer-Builder Separation (PBS). In PBS, block building is separated from block proposal.
Builders create blocks that contain MEV, and proposers (validators) select the most profitable block to include. This formalization has led to a competitive marketplace where front-running is institutionalized. This evolution has created new challenges for options protocols.
The value extracted by front-runners often comes directly from the protocol’s liquidity providers and users. This creates a negative feedback loop where high front-running costs deter participation, reducing liquidity and making the market less efficient. The design of options protocols must now account for this adversarial environment, moving beyond simple pricing models to incorporate mechanisms that actively mitigate MEV extraction.
The evolution of front-running has forced protocols to consider privacy as a core design principle, rather than an afterthought.
The evolution of front-running has transitioned from simple, opportunistic arbitrage to sophisticated, institutionalized MEV extraction, fundamentally altering market microstructure.

Horizon
Looking ahead, the future of front-running in options markets will be defined by a fundamental tension between transparency and efficiency. The current model, where all order flow is public, is inherently flawed for complex financial instruments like options. The logical conclusion is a move toward more private or obfuscated order flow.
This shift will likely manifest in two distinct pathways. The first pathway involves the continued dominance of MEV infrastructure, where front-running becomes so sophisticated that decentralized options protocols cannot compete on price efficiency with centralized exchanges. This scenario leads to a consolidation of options trading onto centralized platforms where order flow is private by default, and on-chain options protocols become niche or illiquid.
The second pathway involves the development of new architectural primitives designed specifically to counter front-running. This includes the implementation of Fully Homomorphic Encryption (FHE) or other cryptographic techniques that allow computations on encrypted data. A more immediate and practical solution lies in intent-based architectures.
A Conjecture on Intent-Based Architectures
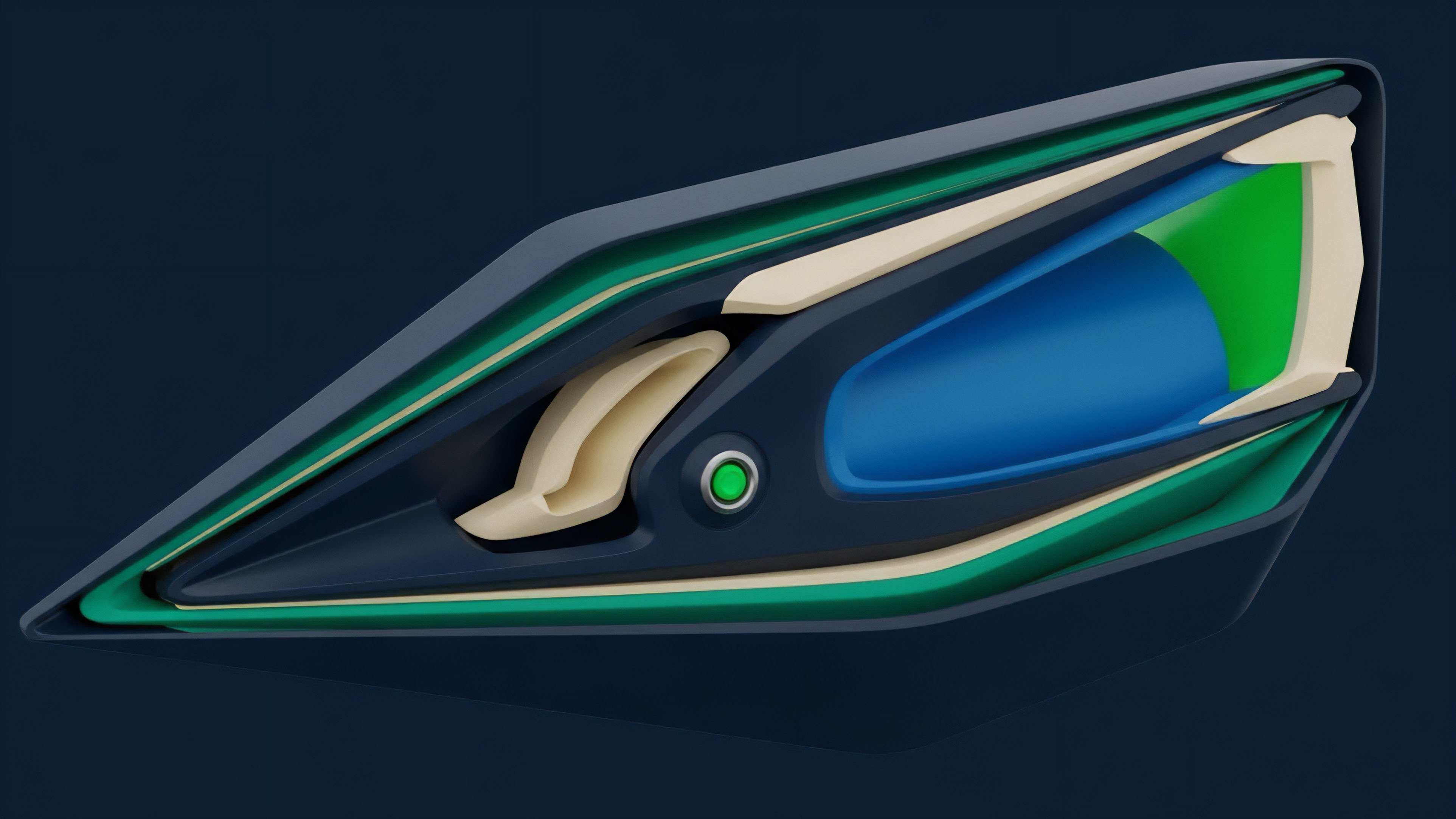
The future of front-running mitigation for options protocols lies in shifting from a transaction-based model to an intent-based model. In this model, users express their desired outcome (e.g. “I want to buy X call options at a maximum price of Y”) rather than specifying the exact transaction details.
A network of solvers then competes to find the optimal execution path for this intent. The key insight here is that the solver network can find the best execution path by utilizing private order flow and batch auctions, effectively internalizing the MEV and returning the value to the user.
Instrument of Agency a Framework for Intent-Based Options Settlement
To address front-running, a new architecture must be implemented that separates the user’s intent from the execution details. The following framework outlines a potential design for an intent-based options settlement layer:
- Intent Submission: A user submits an encrypted intent to a private mempool or relay. The intent specifies the desired options trade (e.g. strike, expiry, size) and a maximum acceptable price.
- Solver Competition: A network of competing solvers receives the encrypted intent. Solvers are incentivized to find the best possible execution path by accessing private liquidity pools and external markets.
- Batch Execution: Solvers bundle multiple intents together and execute them in a single batch at a uniform clearing price. This eliminates sequential ordering advantages.
- Proof of Execution: The winning solver submits a cryptographic proof that the execution was completed according to the user’s intent and at the best available price.
This framework re-architects the market microstructure to remove the information asymmetry that front-running exploits. The user no longer needs to trust that their transaction will be fairly executed; they only need to trust that the solver network will find the optimal solution for their intent. The transition to this model will be necessary to ensure decentralized options protocols can offer competitive pricing and liquidity against centralized venues.
The true test for decentralized options protocols is whether they can transition from transparent, sequential order books to private, intent-based architectures without sacrificing the core tenets of permissionless finance.
What new economic incentives must be created to ensure solvers prioritize user welfare over MEV extraction in a fully decentralized, intent-based options market?
Glossary

Market Microstructure Analysis

Protocol Optimization

Protocol Design Principles
Financial System Design Principles
Blockchain Architecture Design

Systemic Risk

Decentralized Options Protocols

Options Greeks Calculation Methods and Their Implications

Decentralized Infrastructure