
Essence
Sovereign financial interactions require the separation of validity from visibility. Zero-Knowledge Privacy Proofs constitute the mathematical foundation for verifying the legitimacy of a transaction or a state transition without exposing the underlying data. This capability resolves the tension between public ledger transparency and the confidentiality requirements of professional market participants.
In the digital asset derivative markets, where strategy obfuscation is a requirement for alpha preservation, these cryptographic constructs permit traders to prove collateral sufficiency and margin health without revealing specific positions or strike prices.
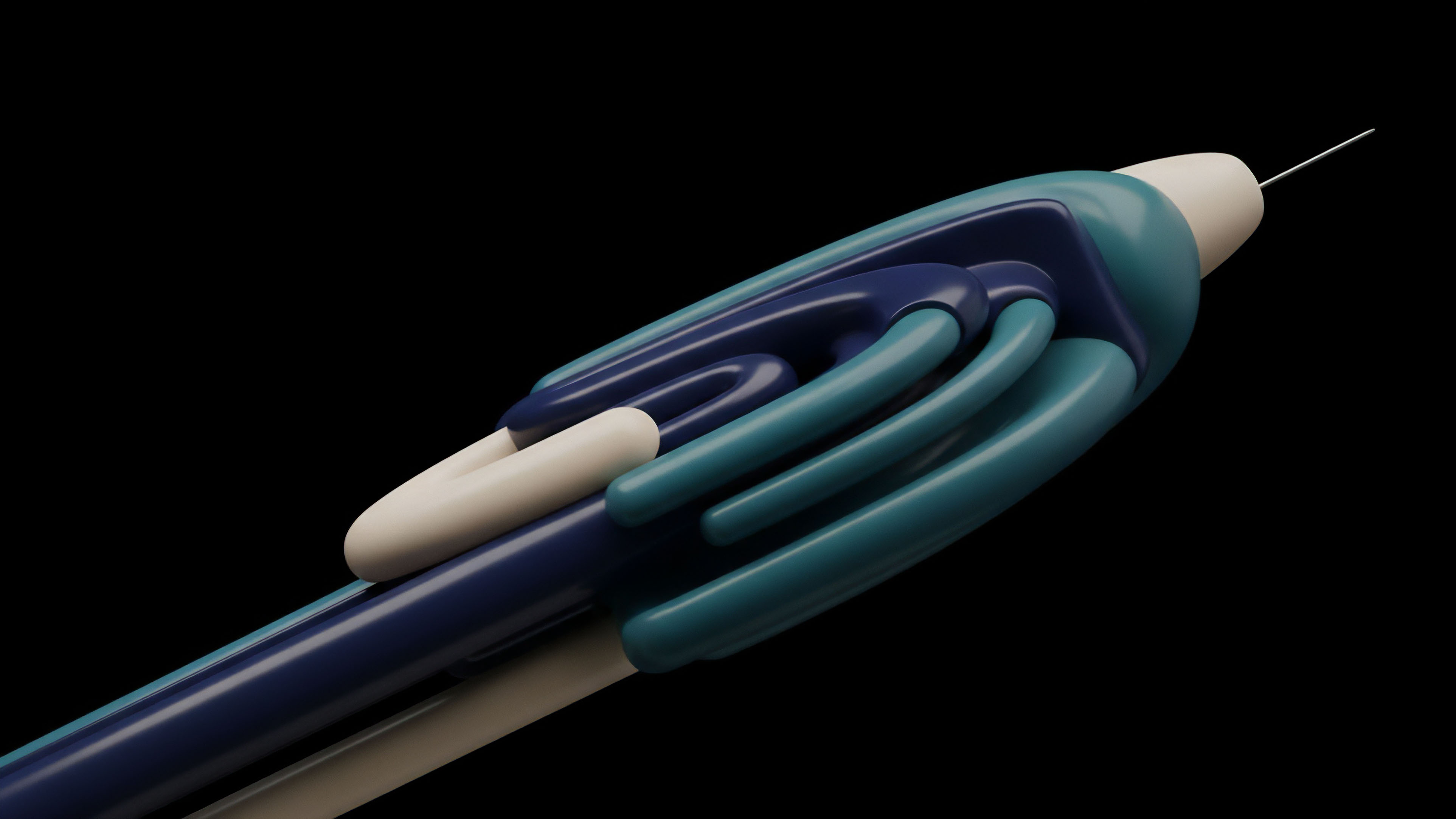
Privacy acts as the primary shield for institutional capital seeking to operate within permissionless derivative markets.
The implementation of these proofs transforms the blockchain from a surveillance machine into a secure execution environment. By utilizing Zero-Knowledge Privacy Proofs, a protocol can confirm that an options contract is fully collateralized and that the user possesses the requisite permissions to execute the trade, all while keeping the user’s balance and trade history hidden from competitors. This structural shift is mandatory for the migration of high-frequency trading and sophisticated hedging strategies from centralized silos to decentralized networks.
Confidentiality as Market Liquidity
Institutional liquidity providers avoid venues where their positions are public, as transparency invites predatory front-running and “copy-trading” that erodes their edge. Zero-Knowledge Privacy Proofs mitigate this risk by providing a “dark” execution layer that maintains the trustless properties of the base chain. The mathematical guarantee of correctness ensures that even though the market cannot see the order flow, it can trust that every trade adheres to the protocol’s risk parameters.
This creates a fertile environment for deep liquidity and narrow spreads, as participants can deploy capital with the same privacy expectations found in legacy dark pools.

Origin
The conceptual genesis of these proofs dates back to the mid-1980s with the work of Shafi Goldwasser, Silvio Micali, and Charles Rackoff. They introduced the idea of interactive proof systems where a prover could demonstrate knowledge of a secret to a verifier without disclosure.
The transition into the digital asset space occurred with the implementation of Zcash, which utilized zk-SNARKs to enable shielded transactions. This technological leap shifted the focus from simple value transfer to the validation of complex computational statements.

From Academic Theory to Financial Infrastructure
Early iterations required multiple rounds of communication between the prover and verifier, making them unsuitable for the asynchronous nature of blockchain settlement. The advancement of Non-Interactive Zero-Knowledge (NIZK) proofs allowed for a single, succinct proof to be broadcast and verified by any participant. As decentralized finance matured, the need for Zero-Knowledge Privacy Proofs expanded from basic transaction privacy to the verification of elaborate derivative logic and cross-chain state.
- Goldwasser-Micali-Rackoff: The 1985 paper that established the three properties of ZKPs: completeness, soundness, and zero-knowledge.
- Zcash Launch: The first large-scale application of SNARKs, proving that privacy could be maintained at the protocol level.
- Ethereum Integration: The introduction of precompiles for pairing-friendly elliptic curves, enabling ZK verification on a smart contract platform.

Theory
At the technical level, Zero-Knowledge Privacy Proofs rely on the arithmetization of programs into mathematical constraints. This process converts a computational circuit into a set of algebraic equations, typically represented as Rank-1 Constraint Systems (R1CS) or Quadratic Arithmetic Programs (QAP). The prover demonstrates knowledge of a “witness” that satisfies these equations without revealing the witness itself.
This mathematical reduction mirrors the way physical systems minimize energy states to reach equilibrium, where the proof serves as the lowest-energy confirmation of truth.
Mathematical certainty replaces legal recourse in the settlement of high-frequency options contracts.

Computational Integrity and Succinctness
The efficiency of these systems is measured by proof size and verification time. zk-SNARKs offer small proof sizes and near-constant verification time, making them ideal for on-chain settlement where block space is expensive. Conversely, zk-STARKs utilize hash functions instead of elliptic curves, providing quantum resistance and eliminating the need for a trusted setup, albeit at the cost of larger proof sizes.
| Feature | zk-SNARKs | zk-STARKs | Bulletproofs |
|---|---|---|---|
| Proof Size | Small (~288 bytes) | Large (~45-100 KB) | Medium (~1.5 KB) |
| Verification Speed | Very Fast | Fast | Slow (Linear) |
| Trusted Setup | Required (usually) | Transparent | Transparent |
| Quantum Resistance | No | Yes | No |

Polynomial Commitments and Arithmetization
The prover encodes the computation into a polynomial and commits to it. The verifier then queries the polynomial at a random point to check if the constraints are satisfied. This probabilistic check ensures that the probability of a false proof being accepted is infinitesimally low.
In the context of Zero-Knowledge Privacy Proofs for options, the constraints might include the Black-Scholes pricing model or margin requirement formulas, ensuring that the trade is mathematically valid before it is ever committed to the ledger.

Approach
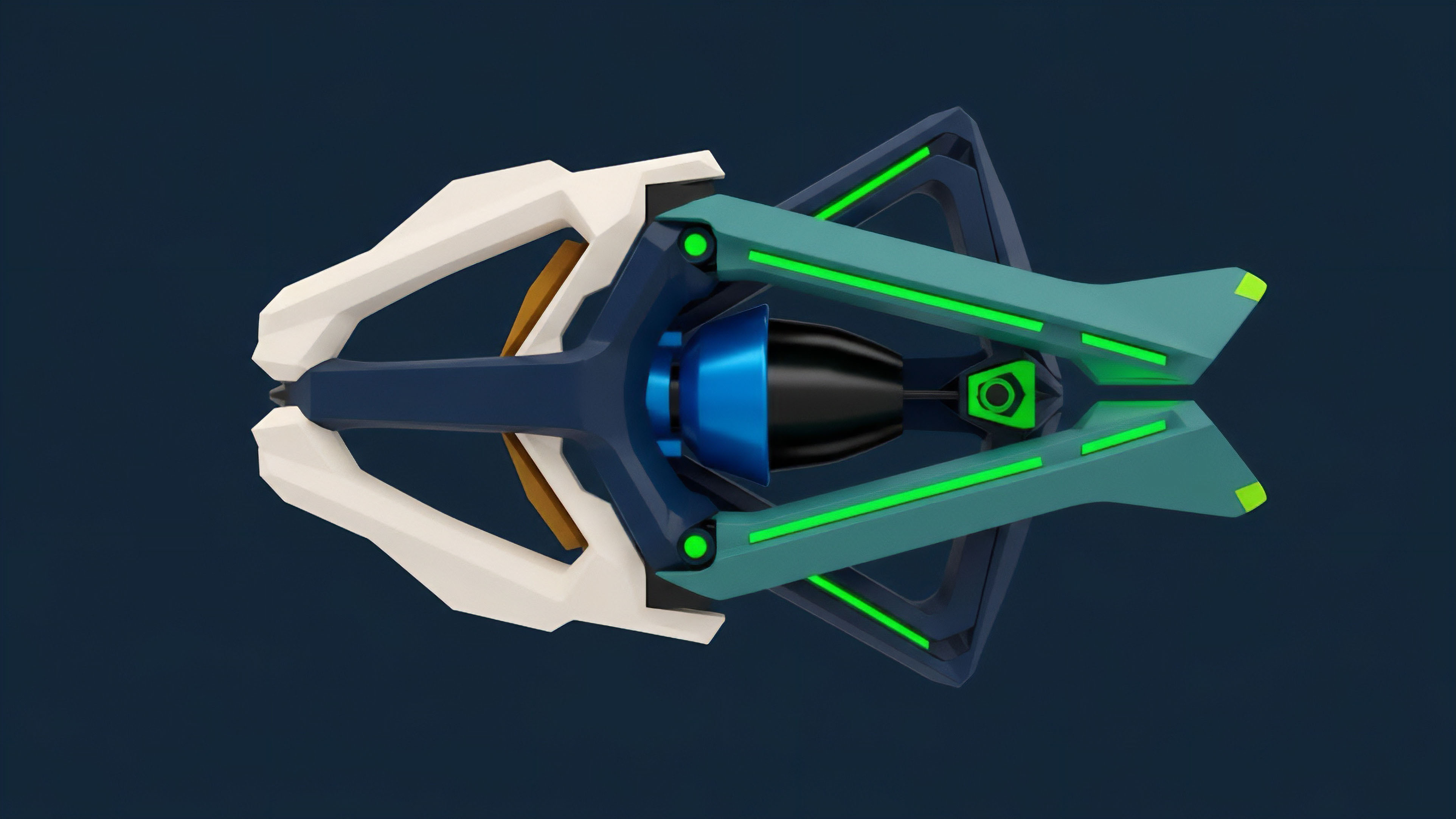
Current implementations utilize these proofs to scale decentralized exchanges and options platforms. By aggregating thousands of trades into a single proof, ZK-Rollups reduce the data burden on the base layer while maintaining the security guarantees of the underlying blockchain.
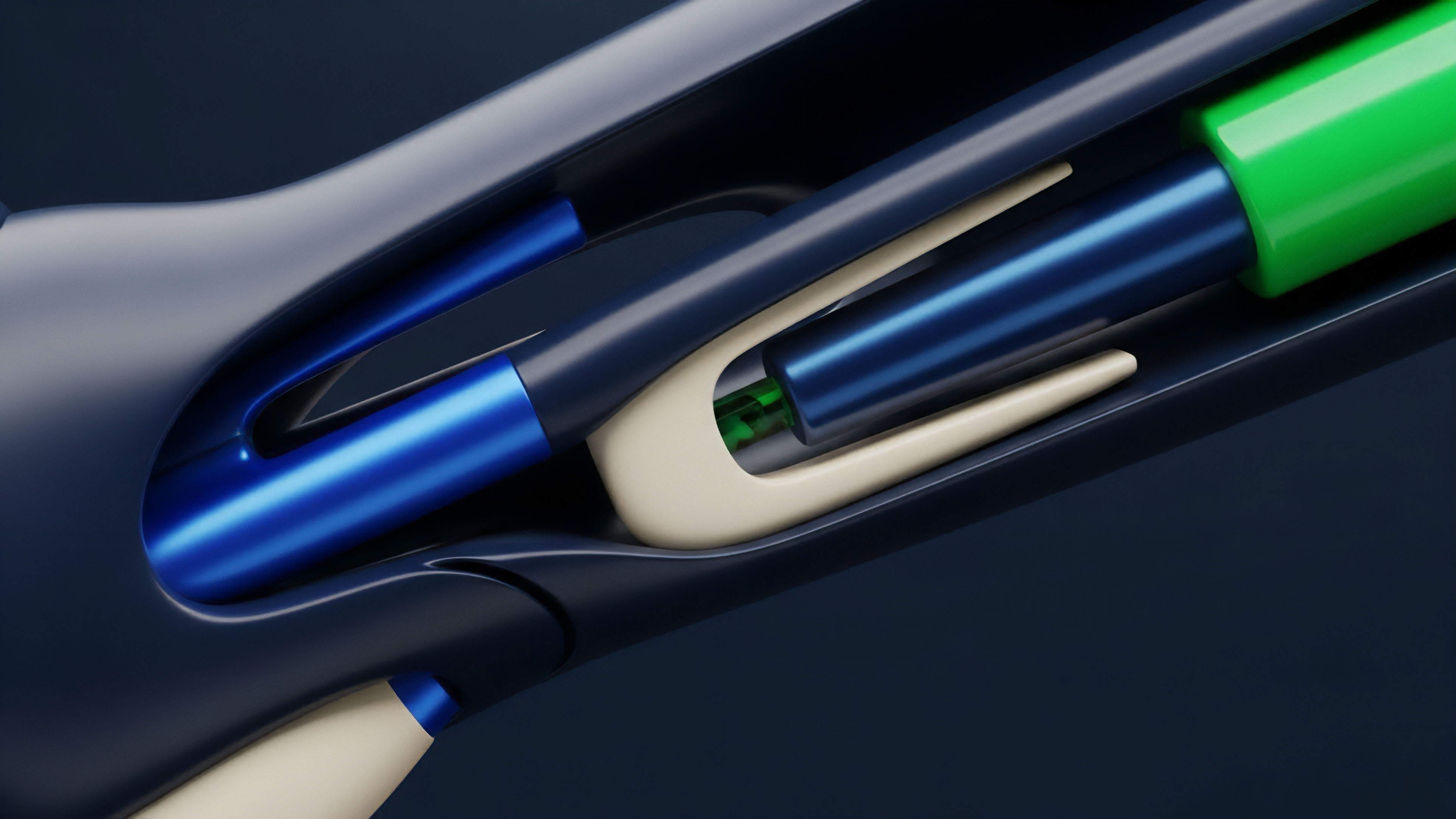
This methodology permits the execution of complex derivative logic off-chain, with only the proof of correctness and the updated state root being posted on-chain.
Operational Flow of ZK-Derivatives
The lifecycle of a private derivative trade involves several distinct stages to ensure both privacy and settlement finality.
- Commitment Generation: The trader creates a commitment to their trade parameters and collateral, keeping the details hidden.
- Off-chain Computation: The ZK-Rollup operator executes the trade matching and margin calculations in a prover environment.
- Proof Generation: The prover generates a Zero-Knowledge Privacy Proof demonstrating that all trades in the batch followed the protocol rules.
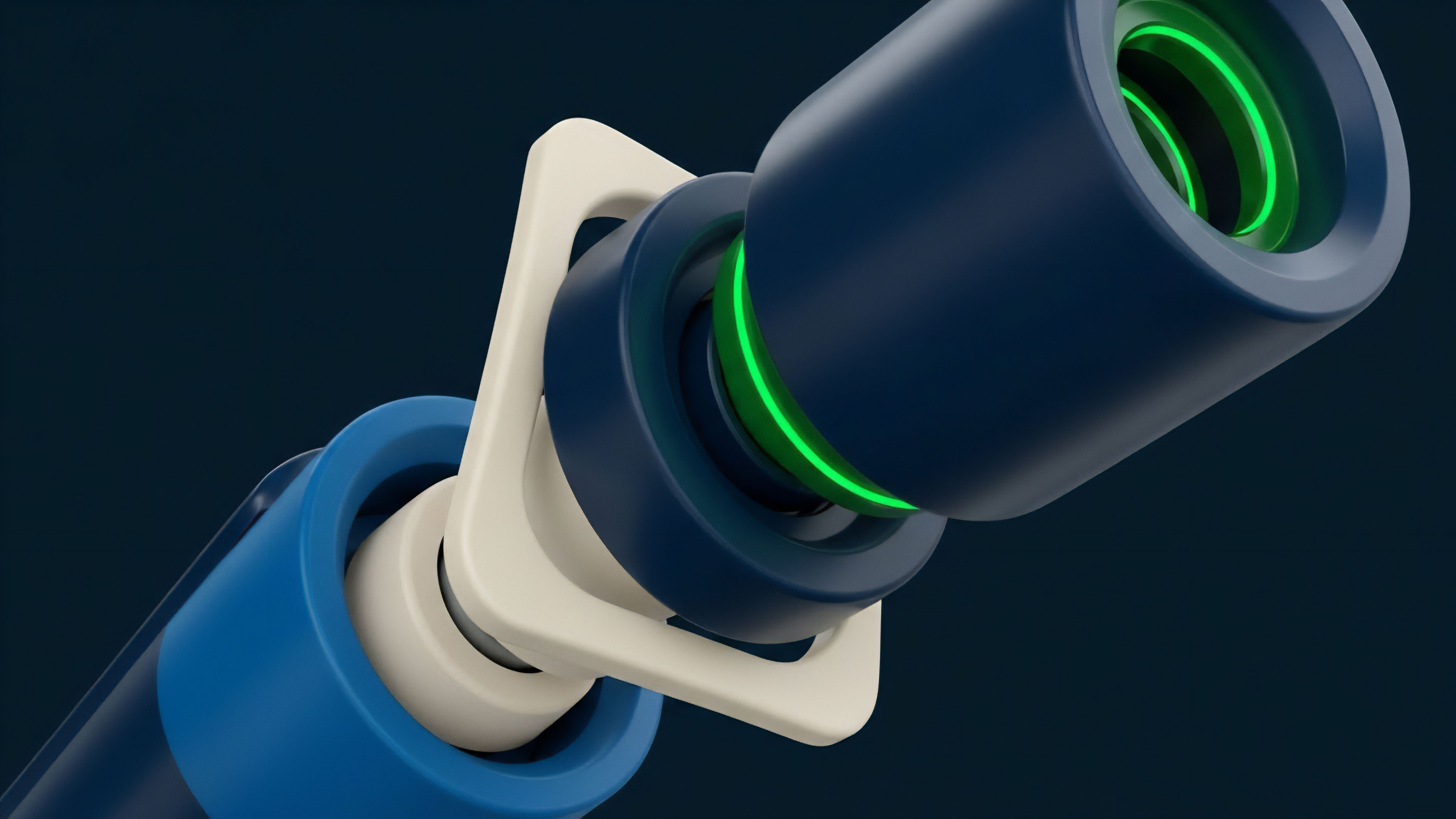
- On-chain Verification: The smart contract on the base layer verifies the proof and updates the global state root.

Risk Management and Margin Verification
In a ZK-based margin engine, the system verifies that a user’s net equity exceeds the maintenance margin without disclosing the specific assets held. This is achieved through range proofs and set membership proofs. Zero-Knowledge Privacy Proofs allow the protocol to liquidate underwater positions by proving to the network that the liquidation threshold was breached, without leaking the trader’s entry price or gearing levels to the broader market.
| Metric | Standard DEX | ZK-Powered DEX |
|---|---|---|
| Transaction Privacy | Public | Shielded |
| Throughput (TPS) | Low (~15-50) | High (2,000+) |
| Settlement Cost | High per trade | Low (amortized) |
| Capital Efficiency | Medium | High |

Evolution
The progression of this technology has moved from systems requiring a “trusted setup” to transparent systems. This removes the risk of a “toxic waste” scenario where the initial parameters could be used to forge proofs. Modern Zero-Knowledge Privacy Proofs are increasingly recursive, meaning a proof can verify other proofs.
This allows for massive compression of history, where the entire state of an options exchange can be represented by a single, small proof.

Hardware Acceleration and Prover Markets
As the computational intensity of generating proofs remains high, the industry is shifting toward specialized hardware. Field Programmable Gate Arrays (FPGAs) and Application-Specific Integrated Circuits (ASICs) are being developed specifically for ZK-SNARK and STARK generation. This development reduces the latency of trade finality, bringing decentralized options closer to the sub-millisecond execution speeds of centralized competitors.
- Recursive SNARKs: Enabling a single proof to verify a batch of proofs, leading to hyper-scalability.
- PLONK and Halo2: Advanced arithmetization schemes that simplify the creation of ZK-circuits for complex financial logic.
- ASIC Development: The transition from CPU-based proving to hardware-accelerated proving to minimize latency.

Horizon
The future trajectory involves the integration of compliance-ready privacy. Zero-Knowledge Privacy Proofs will enable “selective disclosure,” where a user can prove to a regulator that they are not on a sanctions list or that they have paid their taxes, without revealing their entire transaction history to the public. This balance of privacy and compliance is the only viable path for institutional adoption of decentralized derivatives.
The convergence of zero-knowledge proofs and regulatory requirements defines the next epoch of digital asset sovereignty.

Programmable Privacy and View Keys
Future protocols will likely incorporate “view keys” that allow specific third parties to audit certain aspects of a trader’s activity. This creates a tiered privacy model where the default is total anonymity, but transparency can be granted for specific legal or financial requirements. Zero-Knowledge Privacy Proofs will serve as the gatekeeper, ensuring that only the authorized information is disclosed while the rest remains mathematically shielded.

Systemic Resilience and Proof of Solvency
The ultimate application of this technology is the continuous, real-time proof of solvency for entire exchanges. Instead of relying on periodic audits, an exchange can provide a Zero-Knowledge Privacy Proof every block, demonstrating that its total liabilities do not exceed its verified reserves. This eliminates the risk of bank runs and hidden insolvency, creating a more stable and trustless global financial network.

Glossary

Confidential Settlement

Cryptographic Privacy

On-Chain Verification

View Keys

Front-Running Mitigation

Proof-of-Solvency
Zero Knowledge Proofs
Trustless Settlement

Recursive Proofs






