Essence
The core function of Non-Interactive Zero-Knowledge Proofs (NIZKPs) in decentralized finance is to resolve the fundamental conflict between market transparency and participant privacy. In traditional finance, a centralized clearinghouse or exchange acts as a trusted intermediary, holding private data on all participants while publicly providing aggregated market data. Decentralized markets, by design, demand transparency to build trust in a permissionless environment, yet full transparency of individual positions and strategies creates an inefficient and exploitable market microstructure.
NIZKPs offer a cryptographic solution, enabling a prover to demonstrate the truth of a statement ⎊ such as possessing sufficient collateral or having correctly calculated an options premium ⎊ without revealing any information beyond the validity of the statement itself. This allows for verifiable computation and private state transitions on public ledgers, which is essential for scaling complex derivatives markets without compromising user privacy or revealing proprietary trading strategies. The non-interactive property is critical; it allows a single proof to be generated once and verified many times, decoupling the prover from the verifier and eliminating the need for real-time, back-and-forth communication.
Non-Interactive Zero-Knowledge Proofs allow a system to prove a fact without revealing the underlying data, balancing market transparency with individual privacy.
The ability to verify complex calculations off-chain, and then submit a small, verifiable proof on-chain, drastically reduces gas costs and increases transaction throughput. This scalability is a prerequisite for high-frequency trading and complex financial instruments, such as options and perpetual swaps, where price updates and liquidations must occur rapidly. The application of NIZKPs in this context moves beyond simple private transactions to enable complex, private financial logic.

Origin
The concept of zero-knowledge proofs originated with the seminal work of Goldwasser, Micali, and Rackoff (GMR) in 1985. Their initial formulation introduced the three core properties: completeness, soundness, and zero-knowledge. However, these early proofs were “interactive,” requiring a back-and-forth communication protocol between the prover and verifier.
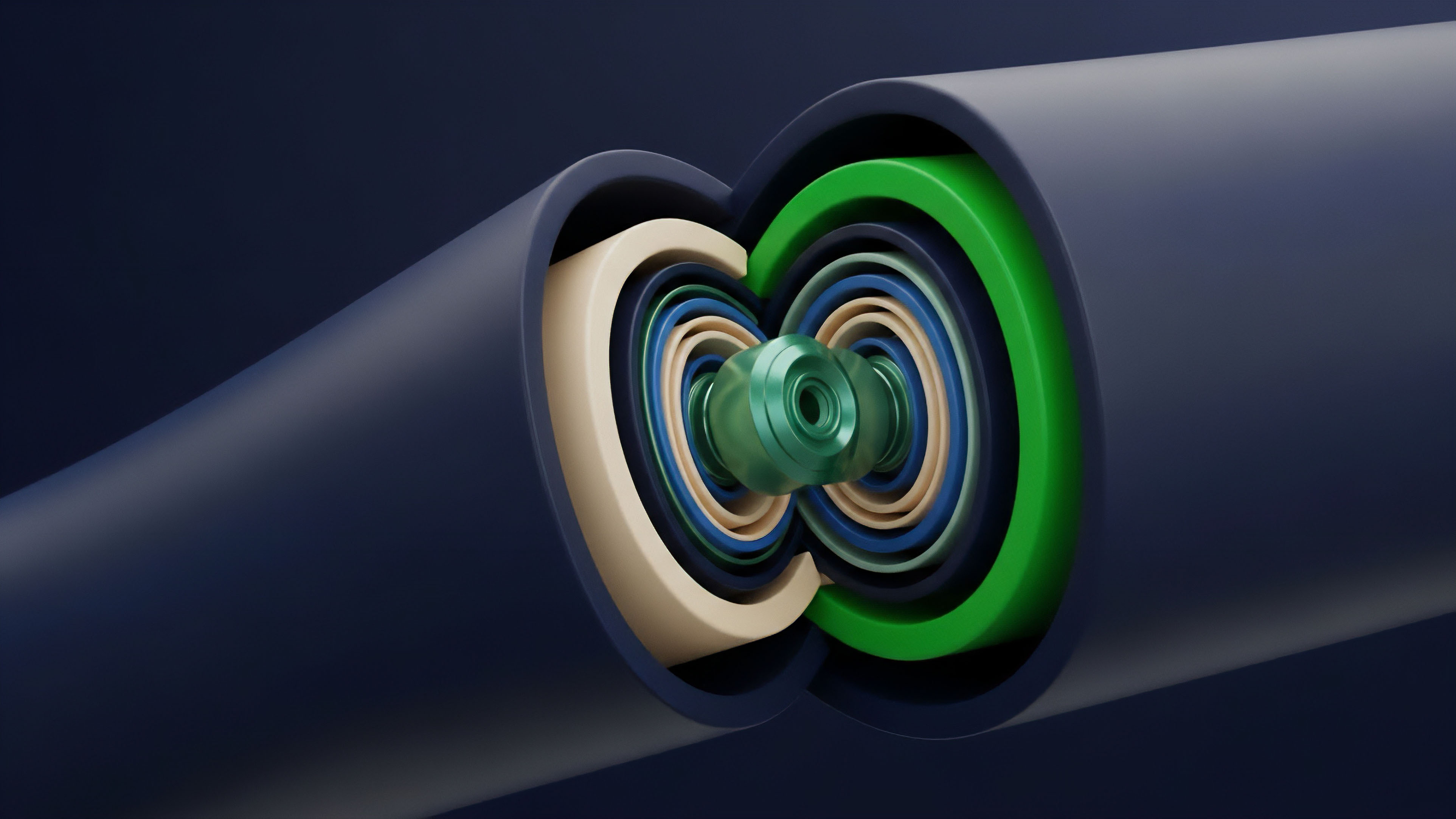
This interactive nature made them impractical for blockchain applications, where a verifier (the network) cannot engage in real-time dialogue with every prover. The critical innovation leading to NIZKPs came from the work of Blum, Feldman, and Micali (BFM), which introduced the idea of a Common Reference String (CRS) or “trusted setup.” The CRS acts as a shared, public parameter generated once and used by all participants to create and verify proofs. This setup transforms the interactive protocol into a non-interactive one, where a single proof message can be generated and broadcast for verification by anyone holding the CRS.
The development of zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) in the mid-2000s, building on advancements in pairing-based cryptography, provided the first practical implementation of NIZKPs suitable for decentralized systems. This architectural shift from interactive to non-interactive proofs enabled the transition from theoretical possibility to practical implementation in decentralized applications, allowing for private state transitions and verifiable computation in a trustless environment.

Theory
The theoretical foundation of NIZKPs rests on three core properties that define their functionality within a cryptographic system.
These properties ensure the proof’s validity and utility in a decentralized setting.
- Completeness: If the statement being proven is true, then an honest prover can generate a valid proof that will always be accepted by an honest verifier.
- Soundness: If the statement being proven is false, then no dishonest prover can generate a valid proof that will be accepted by an honest verifier, except with negligible probability.
- Zero-Knowledge: The verifier learns nothing from the proof beyond the fact that the statement is true. The proof reveals no additional information about the underlying secret data used to generate it.
The practical implementation of NIZKPs relies on complex mathematical structures, often involving elliptic curve cryptography and polynomial commitments. A key component of many NIZKPs, particularly zk-SNARKs, is the Common Reference String (CRS). The CRS is a set of public parameters generated during a “trusted setup” ceremony.
The security of the entire system depends on the secrecy of the “toxic waste” ⎊ the random numbers used to create the CRS ⎊ being destroyed after generation. If this toxic waste is compromised, a malicious actor could create fraudulent proofs for false statements. The design space of NIZKPs involves trade-offs between proof size, verification time, and the necessity of a trusted setup.
The choice of scheme directly impacts the market microstructure of a derivative protocol. For example, a protocol prioritizing low latency and minimal on-chain cost might accept the trade-off of a trusted setup, while a protocol prioritizing censorship resistance and long-term security might avoid it entirely.
Comparison of NIZKP Architectures
| Scheme | Trusted Setup Required | Proof Size | Verification Time | Post-Quantum Secure |
|---|---|---|---|---|
| Groth16 | Yes (Specific to circuit) | Very Small (Constant size) | Very Fast (Constant time) | No |
| Plonk | Yes (Universal) | Small (Logarithmic) | Fast (Logarithmic) | No |
| zk-STARKs | No | Large (Logarithmic) | Fast (Logarithmic) | Yes |
The Knowledge Extractor concept further refines the theoretical model. It posits that a malicious prover who successfully generates a valid proof for a statement must, by necessity, possess the underlying secret knowledge required to prove that statement. The verifier does not see the knowledge itself, but the existence of the valid proof guarantees that the prover must have had access to it.
This mechanism underpins the trustless nature of NIZKPs in financial applications.
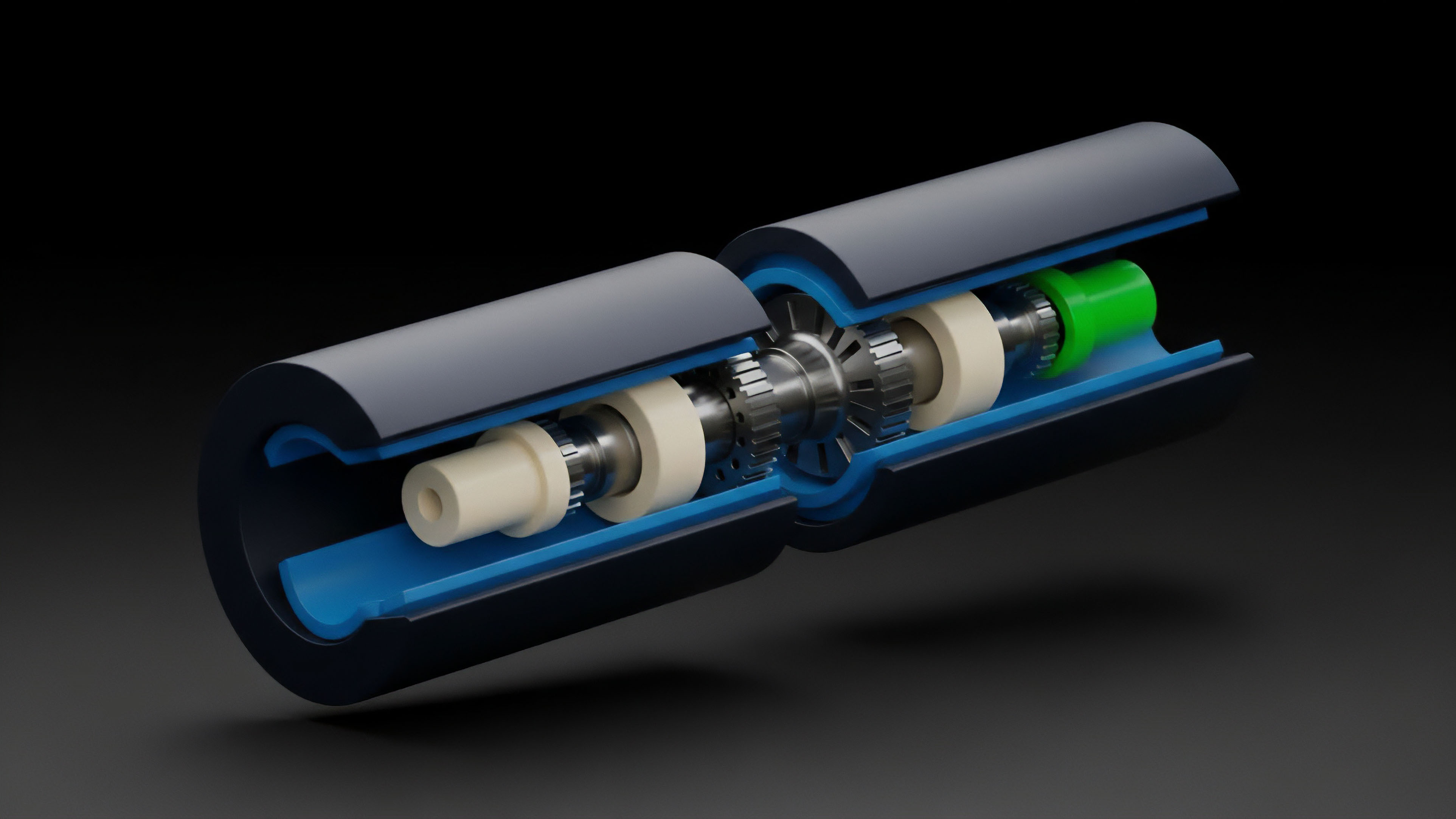
Approach
In the context of crypto derivatives, NIZKPs are applied to address two primary challenges: privacy in order matching and verifiable solvency in margin systems. When applied to a decentralized exchange (DEX) order book, NIZKPs allow a participant to submit an order without revealing the exact price or size of their bid or ask.
The protocol can then use a NIZKP to prove that a match occurred according to specific rules ⎊ for example, that a bid price was higher than an ask price ⎊ without revealing the specific prices themselves. This prevents front-running and provides a level of market privacy that is necessary for large institutional participants. The second critical application lies in margin and collateral management.
In a traditional options market, a clearinghouse calculates a participant’s margin requirements based on their total portfolio risk. In a decentralized setting, a participant must prove to the protocol that their collateral covers their risk exposure without revealing their entire portfolio composition. NIZKPs allow a user to prove a complex financial statement, such as “My collateral value (C) is greater than my margin requirement (M), where M is a function of my portfolio risk (R),” without revealing the specific values of C or R.
- Private Order Matching: Provers submit encrypted orders and generate NIZKPs demonstrating compliance with matching logic. The verifier confirms the match without decrypting the orders.
- Verifiable Solvency Proofs: Users generate NIZKPs proving their collateral exceeds margin requirements based on a complex risk model. This enables trustless leverage without exposing individual positions.
- Off-chain Computation: Complex options pricing calculations (like Black-Scholes or Monte Carlo simulations) can be performed off-chain, with NIZKPs used to verify the correctness of the result before settlement on-chain.
The use of NIZKPs in this context shifts the security paradigm from “trusting a central entity to hold secrets” to “verifying cryptographic proofs of secrets.” This approach ensures that the system remains permissionless while simultaneously supporting the complex, high-stakes financial strategies required for a mature derivatives market.

Evolution
The evolution of NIZKPs for financial applications has centered on moving away from the security trade-offs inherent in early designs. The first practical NIZKPs, such as Groth16, were highly efficient in terms of proof size and verification time, making them suitable for early scalability solutions like zk-rollups.
However, these schemes required a “trusted setup” ceremony, where a set of initial parameters was generated and the corresponding secret information had to be destroyed. The risk of this trusted setup being compromised created a single point of failure, which contradicts the core ethos of decentralized systems. The subsequent evolution focused on two key areas: universal setups and non-trusted setups.
Universal setups, exemplified by schemes like Plonk, require a trusted setup only once. The resulting CRS can then be reused for multiple applications, reducing the frequency of the risk. A more profound architectural shift occurred with the development of zk-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge).
STARKs eliminated the need for a trusted setup entirely, relying instead on a different cryptographic foundation based on collision-resistant hash functions. This makes them “transparent” and removes the single point of failure associated with the CRS. While STARK proofs tend to be larger than SNARK proofs, the trade-off in security and long-term viability for decentralized systems is substantial.
The transition from trusted setups to transparent setups represents a critical shift in NIZKP architecture, prioritizing long-term security over initial efficiency gains.
This evolution directly impacts market design. A derivatives protocol built on a zk-STARK architecture offers greater assurance of long-term security against a compromised setup, making it more appealing for institutional capital. Conversely, protocols built on SNARKs prioritize efficiency, allowing for lower gas fees and faster execution. The market is currently in a phase where both architectures compete for different use cases, with SNARKs dominating high-throughput, capital-efficient rollups and STARKs gaining traction in applications where transparency and post-quantum security are paramount.

Horizon
Looking ahead, the next phase of NIZKP development involves the creation of private smart contracts and verifiable risk engines. The current applications primarily focus on privacy for transactions or state transitions. The future extends this to privacy for the execution logic itself. A private smart contract would allow a derivatives protocol to execute complex financial logic ⎊ such as calculating a liquidation price or exercising an option ⎊ without revealing the specific parameters of the calculation. This moves beyond simply hiding data to hiding the code’s execution state from external observers. The most profound impact on derivatives markets will be the implementation of verifiable risk engines. In traditional finance, risk models are proprietary and opaque, often leading to systemic crises when underlying assumptions fail. NIZKPs enable a decentralized protocol to prove that its risk model correctly calculates margin requirements based on verifiable inputs, without revealing the proprietary model itself. This creates a new form of “trustless compliance,” where regulators or auditors can verify a system’s adherence to risk standards without accessing sensitive market data. This new architecture creates both significant opportunities and systemic risks. The opportunity lies in creating truly robust and efficient decentralized markets that can compete with traditional financial institutions. The systemic risk arises from the potential for NIZKPs to obscure underlying leverage and interconnectedness. If every participant’s collateral and risk are private, the network may lose its ability to perform real-time, system-wide risk analysis. The challenge for future architects is to design NIZKP systems that allow for private calculations while simultaneously providing aggregate data necessary for managing contagion risk.

Glossary

Cryptographic Data Proofs for Efficiency
Zero-Knowledge Ethereum Virtual Machines

Zero-Knowledge Settlement Proofs
Zero Knowledge Proof Evaluation
Zero Knowledge Proof Solvency Compression

Cryptographic Liability Proofs

Zero Knowledge Virtual Machine

Data Integrity Proofs
End-to-End Proofs