Essence
Zero-knowledge applications in decentralized finance represent a shift from public verification to private computation. In the context of options and derivatives, this technology addresses the fundamental conflict between transparency and competitive execution. Traditional DeFi order books, by broadcasting every transaction and pending order to the public memory pool, create an environment ripe for front-running and value extraction by automated bots.
Zero-knowledge proofs provide a mechanism to verify the validity of a transaction ⎊ such as a margin call or an options trade settlement ⎊ without revealing the specific details of the underlying data. This allows for the creation of private execution environments where market participants can interact without exposing their strategic intent to adversarial agents. The core function is to maintain a high level of verifiability while simultaneously achieving informational opacity, a critical requirement for institutional-grade trading where order flow information has significant monetary value.
Zero-knowledge applications create a private execution environment for options trading by separating the public verification of transaction validity from the private disclosure of transaction details.
This architecture enables a new form of market microstructure where a trader can prove they have sufficient collateral for an options position without revealing the size or composition of their portfolio. The system validates the proof ⎊ that a specific mathematical condition holds true ⎊ rather than checking the data itself. This separation of concerns is essential for mitigating a significant portion of systemic risk, specifically the risk associated with a transparent order book being exploited by MEV (Maximal Extractable Value) strategies.

The Problem of MEV in Options
Maximal Extractable Value in options protocols manifests in several ways, primarily through front-running and sandwich attacks. A transparent order book allows searchers to observe large pending options orders. By submitting their own orders immediately before and after the large order, searchers can manipulate the price to capture the difference.
This reduces the profitability for the original trader and increases the cost of capital for the protocol. ZK-based systems counter this by concealing the order flow from the public, making it impossible for searchers to identify and exploit large trades.

Origin
The concept of zero-knowledge proofs originated in cryptography during the 1980s, primarily with the work of Goldwasser, Micali, and Rackoff.
Their initial research focused on theoretical problems of proving knowledge without revealing information. The application remained largely academic until the development of blockchain technology, where the need for both transparency and privacy created a direct use case. Early applications in cryptocurrency, such as Zcash, focused on private transactions where a user could prove they had sufficient funds without revealing the source or destination of the funds.
The transition to DeFi involved applying these concepts to more complex financial logic. The demand for private options protocols arose from the limitations of early AMM (Automated Market Maker) models, which suffered from high slippage and inefficient capital deployment. The subsequent move to order book models in DeFi exposed these protocols to the MEV risks inherent in public blockchains.

The Shift from Transaction Privacy to State Privacy
The initial use of ZK proofs in crypto focused on hiding simple transfers. However, derivatives protocols require hiding complex state changes and computations. An options protocol must verify a trader’s margin requirements against the risk profile of their position, which involves complex calculations of value at risk (VaR) or Greeks.
The challenge was to prove these calculations were performed correctly on private data. This led to the development of specific ZK-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) and ZK-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge) tailored for complex arithmetic circuits. The goal shifted from proving “I have X coins” to proving “My portfolio meets the margin requirements based on this pricing model, even though you cannot see my portfolio’s contents.”

Theory
The theoretical foundation of ZK applications in options protocols rests on the separation of computation from data disclosure.
The core mechanism involves a prover creating a cryptographic proof that a specific statement about a hidden state is true. The verifier then checks this proof without ever accessing the hidden state itself. In a ZK options protocol, the key statement is often related to margin and risk calculations.

Probabilistic Risk Modeling in Private Environments
A significant challenge in designing a private options protocol is how to model systemic risk when individual positions are hidden. Traditional risk models aggregate all positions to calculate total protocol risk and set liquidation thresholds. When positions are private, this aggregation is impossible.
ZK-enabled protocols address this by forcing individual traders to submit proofs that their positions satisfy a pre-defined risk threshold. The protocol verifies that the sum of all individual proofs meets a certain systemic requirement, without knowing the specific contributions of each trader. This creates a probabilistic model where the system relies on the high probability that individual proofs accurately represent risk, rather than on a deterministic calculation based on full data transparency.

ZK-SNARKs Vs. ZK-STARKs for Derivatives
The choice between ZK-SNARKs and ZK-STARKs involves trade-offs between proof size, computational overhead, and trust assumptions. For options trading, where computational efficiency is critical for rapid execution and pricing, the choice impacts the feasibility of the system.
| Feature | ZK-SNARKs | ZK-STARKs |
|---|---|---|
| Proof Size | Smaller proof size | Larger proof size |
| Computational Cost (Prover) | Higher computational overhead for prover | Lower computational overhead for prover |
| Trust Assumption | Requires a trusted setup phase | Transparent setup (no trusted setup) |
| Scalability | Less scalable for complex computations | Highly scalable for complex computations |
ZK-SNARKs, with their smaller proof sizes, are efficient for on-chain verification but require a trusted setup. ZK-STARKs, while having larger proofs, offer greater transparency and scalability for complex calculations, which makes them highly suitable for the complex arithmetic required for options pricing models like Black-Scholes or implied volatility calculations.

Approach
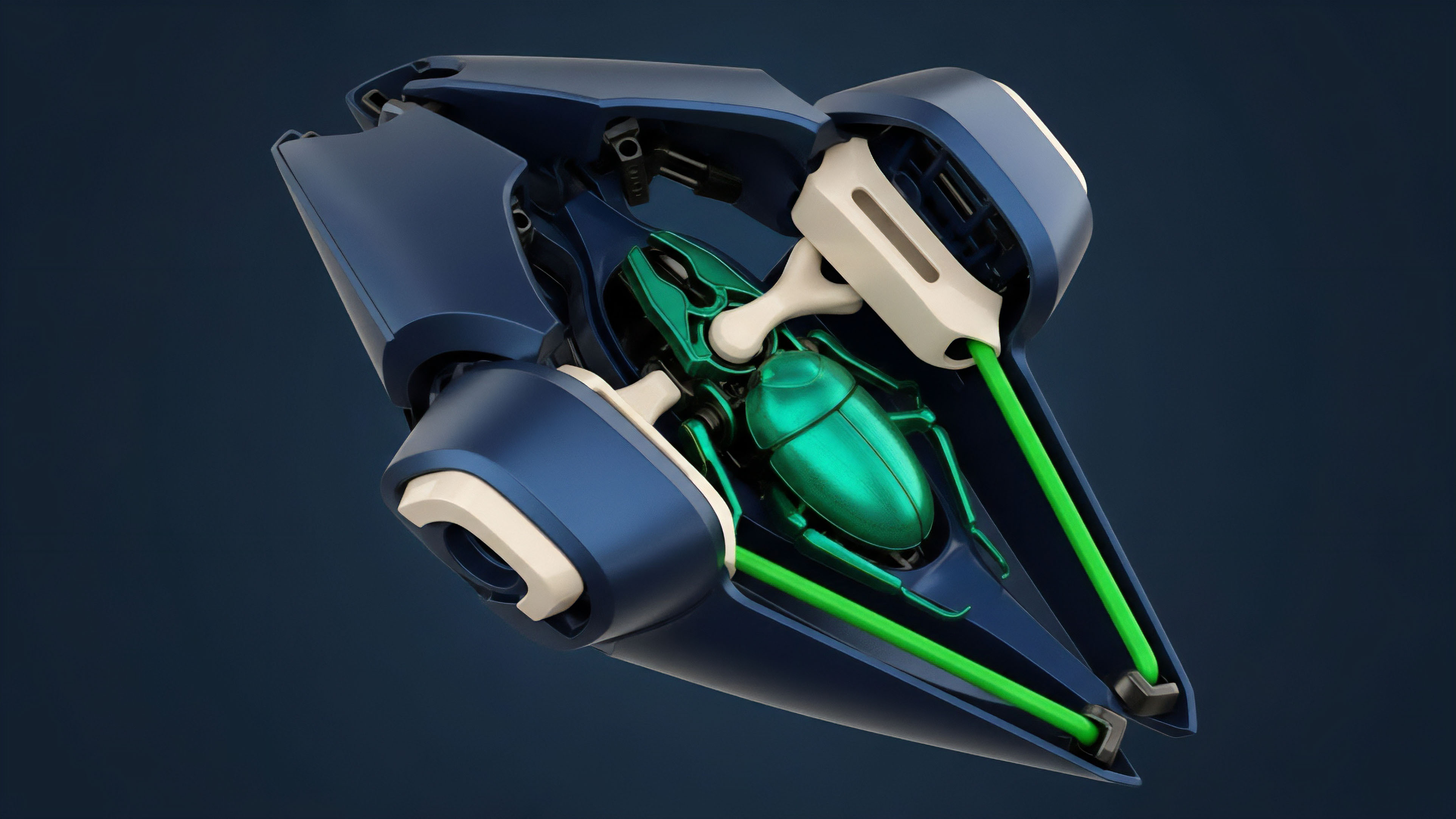
The implementation of zero-knowledge applications in options protocols typically involves a two-layer architecture.
The first layer is the public blockchain, which serves as the settlement layer and verifies the ZK proofs. The second layer is the private execution environment where trades are matched and proofs are generated. This approach aims to preserve the security of the underlying blockchain while providing the necessary privacy for trading.
Market Microstructure and Private Order Flow
The introduction of ZK proofs changes the market microstructure from a fully transparent order book to a private dark pool model. In a traditional transparent order book, liquidity providers face the risk of adverse selection because their resting orders are visible to high-frequency traders. ZK-based systems prevent this by allowing orders to be submitted and matched without revealing the specific details to the public mempool.
This creates a more level playing field for market makers and reduces the information asymmetry that favors front-runners. The execution logic of the protocol verifies that a trade is valid (e.g. within a specific price range and satisfying margin requirements) without revealing the specific price or size of the order.
The implementation of ZK proofs for options trading transforms transparent public order books into private dark pools, mitigating information asymmetry and reducing adverse selection risk for liquidity providers.

The Impact on Risk Management and Liquidation
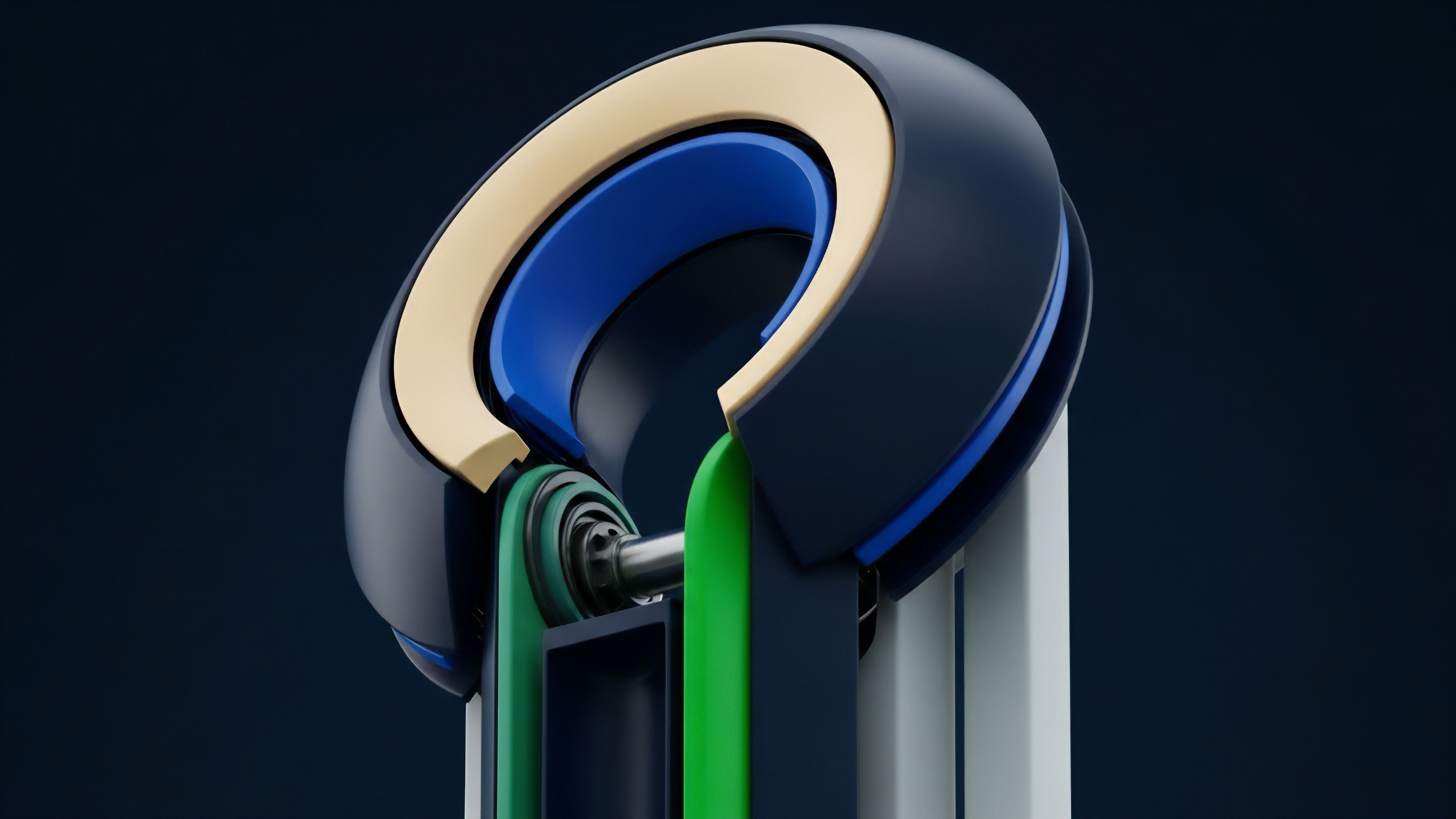
In a ZK options protocol, the liquidation process must be handled differently. Instead of a public check of a user’s collateral against their position, a ZK proof is used to demonstrate that a user’s collateral has fallen below the liquidation threshold. The system relies on a constant flow of proofs from users attesting to their position health.
If a user fails to provide a valid proof, or if their proof indicates insolvency, the protocol initiates a liquidation event. This shifts the burden of proof to the user, who must continuously demonstrate solvency to avoid liquidation. This approach requires a robust system for handling proof generation and verification, as a delay or failure in proof generation could lead to a cascading failure of liquidations across the protocol.
Evolution
The evolution of options protocols in DeFi has followed a path from rudimentary AMM designs to complex order book architectures. Early AMM protocols, such as Hegic or Opyn v1, relied on liquidity pools where users could buy or sell options against a pre-funded pool. These models were highly capital inefficient and suffered from high slippage, making them unsuitable for professional market makers.
The next generation of protocols introduced order books, which provided better price discovery and capital efficiency. However, these order book protocols inherited the fundamental problem of MEV from the underlying public blockchains.
From AMMs to ZK-Enabled Dark Pools
The current state of ZK applications represents the third wave of development in options protocols. The shift from AMMs to order books was driven by the need for better pricing and capital efficiency. The move to ZK-enabled dark pools is driven by the need for privacy and MEV resistance.
This evolution reflects a growing understanding that financial applications require a different set of properties than simple token transfers. The high-stakes nature of options trading, where information asymmetry is a primary source of profit and loss, necessitates a private execution environment. This architectural change directly addresses the behavioral game theory of options trading, where participants are constantly attempting to exploit information advantages.
- AMM-Based Protocols: Initial options protocols relied on liquidity pools. These pools were simple but suffered from significant capital inefficiency and high slippage.
- Order Book Protocols: The introduction of order books improved price discovery and capital efficiency but exposed traders to front-running and MEV due to public transaction visibility.
- ZK-Enabled Dark Pools: The current generation uses zero-knowledge proofs to hide order flow, mitigating MEV and enabling more robust, professional trading strategies.

Horizon
The future of ZK applications in DeFi options points toward fully composable, private financial primitives. The ability to verify complex calculations without revealing data opens the door for exotic options and structured products that are currently infeasible in a transparent environment. Imagine a scenario where complex multi-leg options strategies or structured notes can be created and traded without revealing the specific components of the position to the public.
This level of privacy will allow institutional participants to deploy sophisticated strategies without fear of information leakage.
The ZK-Powered Liquidity Aggregator
A significant development on the horizon is the creation of ZK-powered liquidity aggregators. These systems will allow traders to access liquidity across multiple private options protocols without revealing their full order details to each individual protocol. The aggregator would use ZK proofs to demonstrate that the user has sufficient collateral across the aggregated liquidity sources to execute the trade, while simultaneously hiding the specific breakdown of collateral across different protocols.
This architecture will create a highly efficient, deep liquidity environment that is resistant to systemic risk contagion because individual protocols do not have full visibility into the aggregated risk.
Regulatory Implications and Systems Risk
The rise of ZK-enabled dark pools presents a complex challenge for regulators. While ZK proofs offer a high degree of privacy, they also create a new challenge for oversight. Regulators require visibility into financial activity to prevent illicit behavior and monitor systemic risk.
ZK-based systems could potentially offer a solution through “proof-of-compliance” mechanisms, where a protocol can generate a proof that all activity within the system adheres to specific regulatory rules without revealing the private details of individual transactions. This creates a new regulatory framework where compliance is enforced through mathematical proof rather than data disclosure.
Zero-knowledge applications in options trading are moving toward creating fully private, composable financial primitives that allow for sophisticated strategies while challenging traditional regulatory oversight models.

Glossary

Zero-Knowledge Gas Attestation

Zero Knowledge Hybrids

Decentralized Applications Development

Zero-Knowledge Proof Compliance
Zero-Knowledge Derivatives Layer

Zero-Knowledge Starks

Zero-Knowledge Proofs Risk Verification

Zero-Knowledge Margin Call

Proof of Compliance