Essence
The current architecture of decentralized finance exposes every participant to a predatory panopticon where transaction intent serves as a signal for exploitation. In this environment, the visibility of bid parameters allows automated agents to extract value through front-running and sandwich attacks, degrading the quality of price discovery. Zero Knowledge Bid Privacy functions as a cryptographic shield, allowing market participants to commit to specific trade parameters without revealing the price or volume to the network or the auctioneer until the settlement phase.
This mechanism ensures that the competitive advantage of a private valuation remains with the bidder, preventing the leakage of alpha to opportunistic observers.
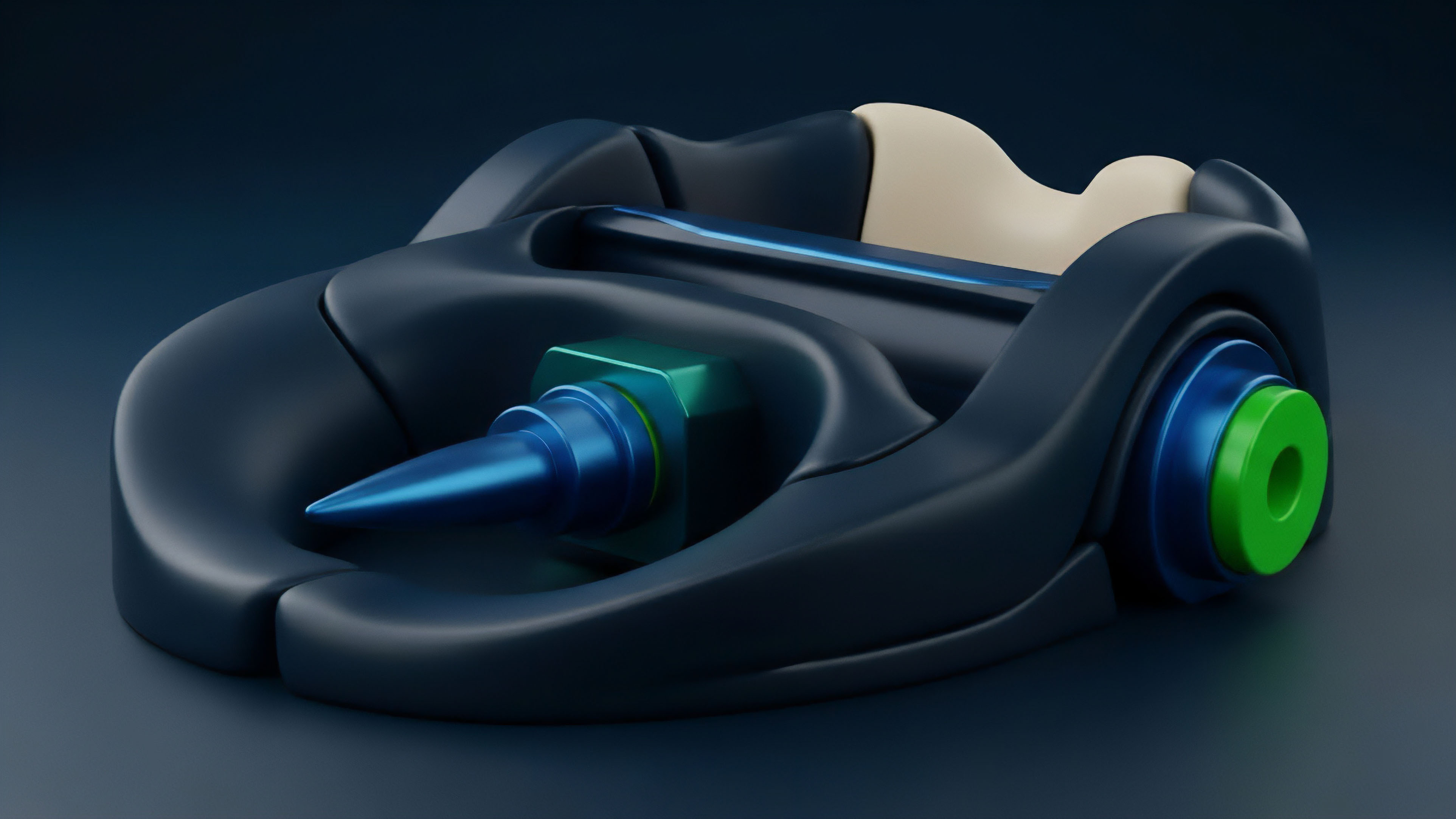
Zero Knowledge Bid Privacy provides a secure environment for price discovery by hiding bid values from all participants until the auction concludes.
The systemic relevance of this technology lies in its ability to restore the integrity of the auction process within adversarial settings. By utilizing non-interactive proofs, a protocol can verify that a bid adheres to specific rules ⎊ such as being within a certain range or backed by sufficient collateral ⎊ without exposing the bid itself. This shift from transparent to shielded order flow transforms the market from a game of latency and observation into a game of pure valuation.
The result is a more resilient financial system where liquidity providers and takers can interact without the constant tax of information asymmetry. Market participants often face a dilemma between liquidity and privacy. Zero Knowledge Bid Privacy resolves this by decoupling the verification of a bid’s validity from the disclosure of its contents.
This separation is vital for institutional players who require confidentiality to execute large-scale strategies without moving the market against themselves. In the absence of such privacy, the decentralized ledger acts as a public broadcast of intent, inviting front-running that increases slippage and reduces capital efficiency. By implementing cryptographic commitments, protocols can facilitate a fair exchange where the best price wins based on merit rather than visibility.

Origin
The lineage of Zero Knowledge Bid Privacy traces back to the theoretical foundations of sealed-bid auctions, specifically the Vickrey-Clarke-Groves (VCG) mechanisms designed to incentivize truthful bidding.
In traditional finance, these auctions relied on a trusted third party to maintain the secrecy of the bids. However, the transition to decentralized ledgers removed the possibility of a central arbiter, initially forcing all bid data into the public domain. Early attempts at on-chain auctions suffered from massive value extraction, as miners and searchers could observe bids in the mempool and insert their own transactions to manipulate the outcome.
The need for a trustless alternative led to the adaptation of Zero-Knowledge Proofs (ZKP), originally conceptualized by Goldwasser, Micali, and Rackoff in the 1980s. The integration of these proofs into financial bidding systems represents a significant shift in protocol design. Rather than trusting a human auctioneer, the system relies on the mathematical hardness of elliptic curve cryptography.
The first generation of private bidding systems utilized simple commit-reveal schemes, but these were limited by the requirement for bidders to return and reveal their bids, creating a bottleneck and a risk of non-revelation.
The transition from trusted auctioneers to cryptographic proofs allows for private bidding without relying on a central authority.
Modern Zero Knowledge Bid Privacy emerged with the advancement of zk-SNARKs and zk-STARKs, which allowed for more complex proofs and faster verification. These technologies enabled the creation of shielded pools and private order books where the proof of a bid’s validity is submitted alongside a commitment. This progression was driven by the realization that transparency, while a virtue for settlement, is a liability for execution.
The development of these systems has been a direct response to the increasing sophistication of Maximal Extractable Value (MEV) strategies that target transparent intent on public blockchains.

Theory
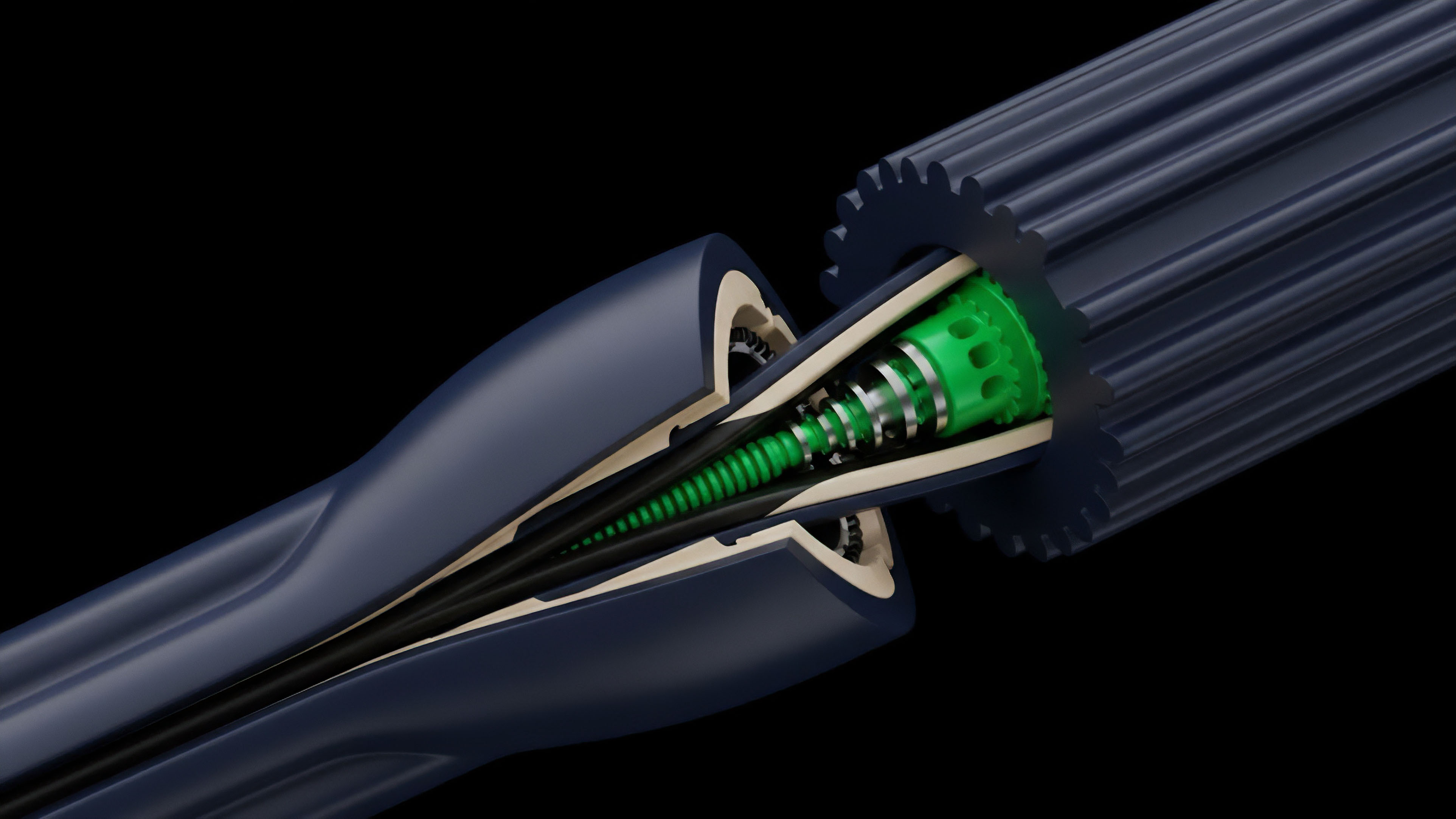
The logic of Zero Knowledge Bid Privacy is built upon the interaction between cryptographic commitments and range proofs. A bidder generates a commitment to their bid, typically using a Pedersen commitment, which is both hiding and binding. This commitment is submitted to the smart contract along with a zero-knowledge proof that the bid is valid according to the protocol rules.
The proof demonstrates that the hidden value exists within a predefined set of parameters without revealing the value itself. This allows the matching engine to process the bid without knowing the exact price or size until the matching criteria are met.
Cryptographic Primitives
The system relies on specific mathematical structures to ensure both security and efficiency. The choice of the proof system impacts the computational overhead for the bidder and the gas cost for the network.
| Attribute | zk-SNARKs | zk-STARKs | Bulletproofs |
|---|---|---|---|
| Trusted Setup | Required | Not Required | Not Required |
| Proof Size | Very Small | Large | Medium |
| Verification Speed | Very Fast | Fast | Slow |
| Quantum Resistance | No | Yes | No |

Game Theoretic Stability
From a game theory perspective, Zero Knowledge Bid Privacy alters the Nash Equilibrium of the auction. In a transparent auction, bidders may engage in “sniping” or price shading based on observed competition. In a private environment, the dominant strategy shifts toward bidding one’s true valuation, as there is no information available to exploit.
This leads to more efficient price discovery and reduces the incentive for adversarial behavior. The protocol physics of these systems ensure that the settlement is deterministic and verifiable, even though the inputs remain shielded during the bidding phase.
Cryptographic commitments ensure that a bid cannot be altered after submission, while zero-knowledge proofs verify its validity without disclosure.
The mathematical verification of a private bid involves checking that the commitment matches the proof and that the proof satisfies the circuit constraints. These constraints might include verifying that the bidder has sufficient balance in a shielded pool or that the bid price does not exceed a certain threshold. The matching engine then uses homomorphic properties or specialized circuits to compare these commitments.
This allows for the execution of a “dark” matching process where the clearing price is determined through a series of cryptographic operations that only reveal the final result to the participants involved.

Approach
The execution of Zero Knowledge Bid Privacy in modern decentralized protocols involves a multi-stage process designed to minimize information leakage. Current systems often utilize batch auctions where bids are collected over a specific period and then matched simultaneously. This method prevents the “last look” advantage and ensures that all participants are treated equally.
Protocols like CowSwap or Gnosis Protocol have pioneered these batching techniques, although they are increasingly moving toward more advanced cryptographic shielding to further protect user intent.
- Commitment Phase: The participant generates a secret value and a commitment, submitting the latter to the blockchain to lock their intent.
- Proof Generation: A zero-knowledge proof is constructed to show that the hidden bid satisfies the auction requirements, such as minimum price or collateralization.
- Submission and Validation: The commitment and proof are sent to the network, where the smart contract verifies the proof before accepting the bid into the pool.
- Matching and Settlement: The matching engine identifies the optimal clearing price using the shielded data, and the final trades are settled on-chain, revealing only the necessary details for execution.
Comparative Execution Models
Different protocols prioritize different aspects of the trade-off between privacy, speed, and cost. Some systems use a hybrid approach where only the price is hidden, while others shield the entire transaction, including the identities of the participants.
| Mechanism | Privacy Level | Latency | Cost Efficiency |
|---|---|---|---|
| Batch Auctions | Medium | High | High |
| ZK Dark Pools | High | Medium | Medium |
| Commit-Reveal | Low | Very High | High |
| FHE Matching | Very High | Very High | Low |
The integration of Zero Knowledge Bid Privacy into automated market makers (AMMs) is a significant area of development. By shielding the swap parameters, these protocols can prevent sandwich attacks and other forms of MEV. The challenge lies in maintaining the efficiency of the constant product formula while operating on encrypted or committed data.
Advanced implementations use specialized circuits to perform the necessary calculations within the zero-knowledge environment, ensuring that the liquidity pool remains balanced without exposing the individual trade sizes that would otherwise signal market direction to observers.

Evolution
The progression of Zero Knowledge Bid Privacy has been marked by a shift from theoretical academic papers to production-ready financial instruments. Initially, the high computational cost of generating zero-knowledge proofs limited their use to niche applications. As hardware acceleration and more efficient proof systems emerged, the feasibility of private bidding improved.
The development of recursive SNARKs has been particularly influential, allowing for the aggregation of multiple private bids into a single proof, which drastically reduces the on-chain verification costs and improves scalability.
The development of recursive proofs and hardware acceleration has reduced the cost of maintaining private order books.
Market dynamics have also forced a change in how privacy is perceived. In the early stages of the digital asset market, transparency was viewed as a primary feature. However, as institutional capital entered the space, the lack of execution privacy became a barrier to entry. This led to the creation of institutional-grade dark pools that utilize Zero Knowledge Bid Privacy to provide a familiar trading environment within a decentralized framework. These systems have evolved to include regulatory compliance features, such as “view keys” that allow authorized parties to audit transactions without exposing the data to the general public. The adversarial environment of the mempool has acted as a catalyst for this technological growth. As MEV extraction became more systematic, the demand for shielded order flow increased. This has led to a diversification of privacy techniques, with some protocols opting for Trusted Execution Environments (TEEs) while others double down on pure cryptographic solutions. The current state of the art involves a combination of these methods, aiming to provide the highest level of security while maintaining the performance required for high-frequency trading and complex derivative strategies.

Horizon
The future of Zero Knowledge Bid Privacy is moving toward the integration of Fully Homomorphic Encryption (FHE), which would allow for arbitrary computations on encrypted data. This would eliminate the need for specialized zero-knowledge circuits for every type of auction, allowing for a more flexible and programmable private finance layer. In this future, the entire lifecycle of a derivative ⎊ from bidding and matching to margin management and liquidation ⎊ could occur within a shielded environment. This would provide a level of privacy that surpasses even traditional centralized exchanges, as not even the exchange operator would have access to the underlying trade data. The rise of cross-chain liquidity also presents new challenges and opportunities for Zero Knowledge Bid Privacy. As trading activity fragments across multiple layers and chains, maintaining privacy across these boundaries becomes vital. Protocols are developing cross-chain zero-knowledge proofs that allow a participant to prove their standing on one chain to participate in a private auction on another. This will lead to a unified, private liquidity layer that spans the entire decentralized environment, reducing fragmentation and improving price discovery for all participants. Finally, the regulatory environment will play a significant role in the adoption of these technologies. The challenge will be to balance the need for individual and institutional privacy with the requirements for transparency in systemic risk management. Zero Knowledge Bid Privacy offers a potential solution through selective disclosure, where participants can prove compliance with specific regulations without revealing their entire trading history. This “programmable privacy” will likely become the standard for the next generation of financial protocols, enabling a more mature and resilient market structure that respects both confidentiality and the law.

Glossary

Maximal Extractable Value

Non-Interactive Zero-Knowledge Proofs

Multi-Party Computation

Trusted Setup

View Keys

Proof-of-Solvency

Proof Generation Time

Dark Pools

Mathematical Integrity