Essence
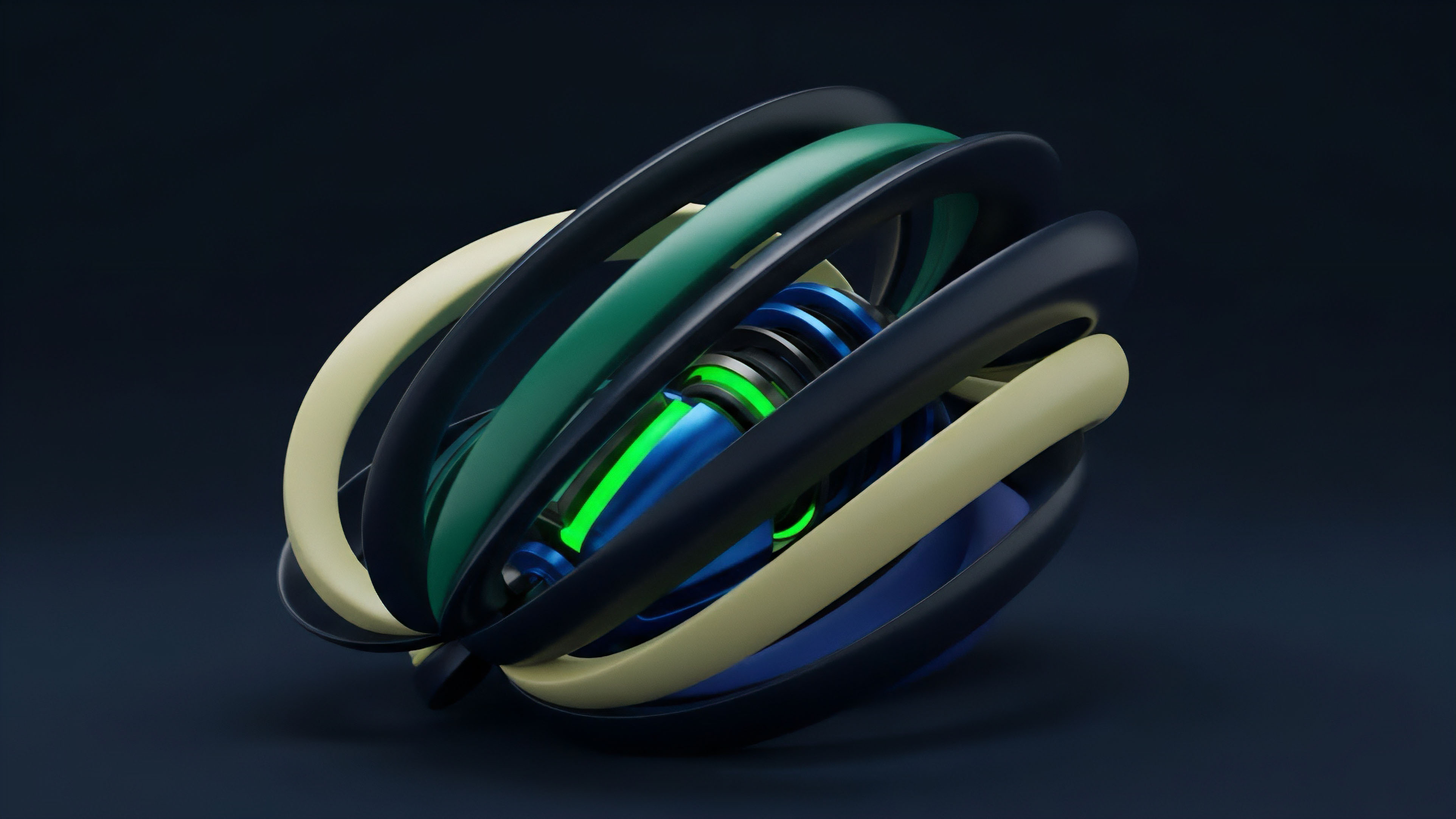
Elliptic Curve Cryptography (ECC) is the foundational mathematical primitive enabling digital ownership and transaction validation across nearly all modern decentralized financial systems. Its core function is to provide asymmetric key pairs ⎊ a public key and a private key ⎊ that allow a user to prove ownership of an asset without revealing the private key itself. The security of this mechanism is derived from the computational difficulty of solving the Elliptic Curve Discrete Logarithm Problem (ECDLP).
For a decentralized options protocol, this primitive underpins every layer of trust, from the security of the collateralized assets to the validation of complex contract execution. The non-custodial nature of decentralized finance relies entirely on the cryptographic assurance that only the owner of the private key can authorize a transfer or a derivative settlement.
ECC provides the non-custodial foundation for decentralized finance by allowing users to prove asset ownership without revealing the underlying private key.
In the context of options, ECC secures the collateral required for writing an option and verifies the signature required to exercise it. A protocol’s ability to operate without a central intermediary hinges on the mathematical certainty that a signature produced by the private key is authentic and cannot be forged. This cryptographic primitive ensures that the rules of the smart contract are enforced trustlessly, preventing fraudulent claims or unauthorized liquidations.
The efficiency of ECC, specifically its ability to generate strong security with smaller key sizes compared to older methods like RSA, directly impacts the scalability and cost-effectiveness of decentralized exchanges.

Origin
The theoretical underpinnings of ECC trace back to the mid-1980s, when Neal Koblitz and Victor Miller independently proposed using elliptic curves for cryptography. The core innovation was leveraging the mathematical properties of points on an elliptic curve over a finite field. This approach offered a significant advantage over existing public-key cryptography standards, such as RSA, which relied on the difficulty of factoring large numbers.
While RSA required keys of increasing length (2048 bits or more) to maintain security against advancing computational power, ECC could achieve equivalent security with much shorter keys (256 bits for comparable strength to 3072-bit RSA). This efficiency was initially explored for constrained environments like smart cards and mobile devices, where computational resources were limited.
The adoption of ECC in digital asset systems was cemented with the release of the Bitcoin whitepaper in 2008. Bitcoin’s implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) for transaction signing established ECC as the default standard for decentralized value transfer. This choice was not accidental; the efficiency gains were crucial for minimizing the data footprint of transactions, which directly translated into lower network fees and improved throughput.
The transition from theoretical concept to practical application in Bitcoin created the first large-scale, adversarial testing ground for ECC, proving its robustness in a high-stakes financial environment where every transaction’s security is continuously challenged by network participants seeking to exploit vulnerabilities.

Theory
The mathematical foundation of ECC rests on the properties of an elliptic curve defined by a specific equation, typically y2 = x3 + ax + b, over a finite field. The security relies on the difficulty of the Elliptic Curve Discrete Logarithm Problem (ECDLP). Given a base point G on the curve and a public key point P, it is computationally trivial to calculate P by performing scalar multiplication (P = k G) where k is the private key.
However, calculating k given only P and G is computationally infeasible for sufficiently large curves. This one-way function forms the core of digital signatures.
In practice, a user generates a private key, which is simply a large random integer. This private key is then used to derive the public key through a one-way mathematical operation on the elliptic curve. The private key remains secret, while the public key is shared publicly.
When a user wishes to authorize an action, such as exercising an options contract, they use their private key to create a digital signature. This signature is then broadcast to the network. Any node on the network can use the corresponding public key to verify that the signature was created by the owner of the private key without needing access to the private key itself.
This separation of signing authority and verification enables the entire non-custodial financial ecosystem.
The choice of specific elliptic curves, such as secp256k1 used by Bitcoin and Ethereum, has significant implications for system performance and security. The specific curve parameters determine the size of the key space and the efficiency of the underlying calculations. The selection process involves trade-offs between speed, security level, and resistance to potential side-channel attacks.
The financial implications of this choice are substantial for high-frequency trading in decentralized options markets. A protocol that selects a curve optimized for speed will reduce latency and gas costs, directly impacting profitability for market makers and arbitrageurs. The systemic risk here is that an improperly chosen curve could introduce vulnerabilities that compromise the entire system.

Approach
The application of ECC in a decentralized options protocol primarily manifests through the implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA). This algorithm provides the mechanism for users to prove their intent to enter, modify, or settle a derivatives position. The process involves several key steps that are fundamental to the protocol’s security model:
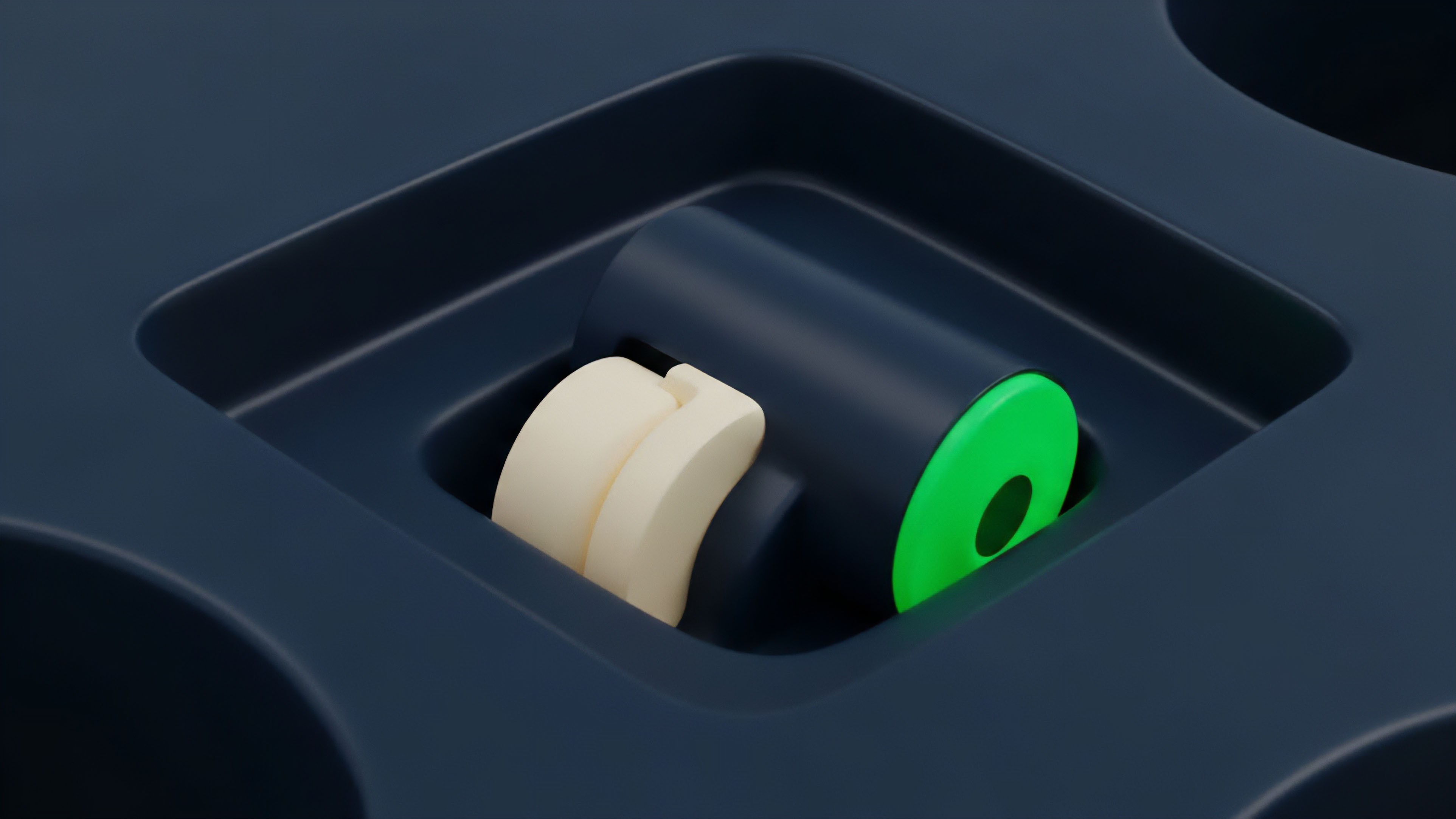
- Key Generation: The user creates a private key, typically a random number. This private key is used to generate the public key, which is then used to derive the user’s on-chain address.
- Transaction Signing: When a user wants to interact with an options contract (e.g. exercising a call option), they first create a transaction message. This message details the specific parameters of the interaction. The private key is then used to generate a digital signature for this message.
- Verification: The smart contract or a network node receives the signed message. Using the user’s public key, it performs a verification calculation to confirm that the signature is valid and corresponds to the message content. If the verification passes, the contract executes the action.
For options protocols, the efficiency of this signing and verification process is paramount. Derivatives trading often involves frequent interactions and time-sensitive operations. The computational overhead of signature verification directly translates to gas costs on a blockchain like Ethereum.
Protocols that optimize this process, or leverage newer cryptographic techniques, gain a competitive advantage in attracting market liquidity. A market maker operating on a decentralized exchange must factor in these transaction costs when calculating the expected value and risk of their positions. The system’s architecture must balance security with operational cost to maintain financial viability for high-volume strategies.
The efficiency of ECDSA signature verification is a critical factor in decentralized options market microstructure, directly influencing gas costs and the viability of high-frequency trading strategies.
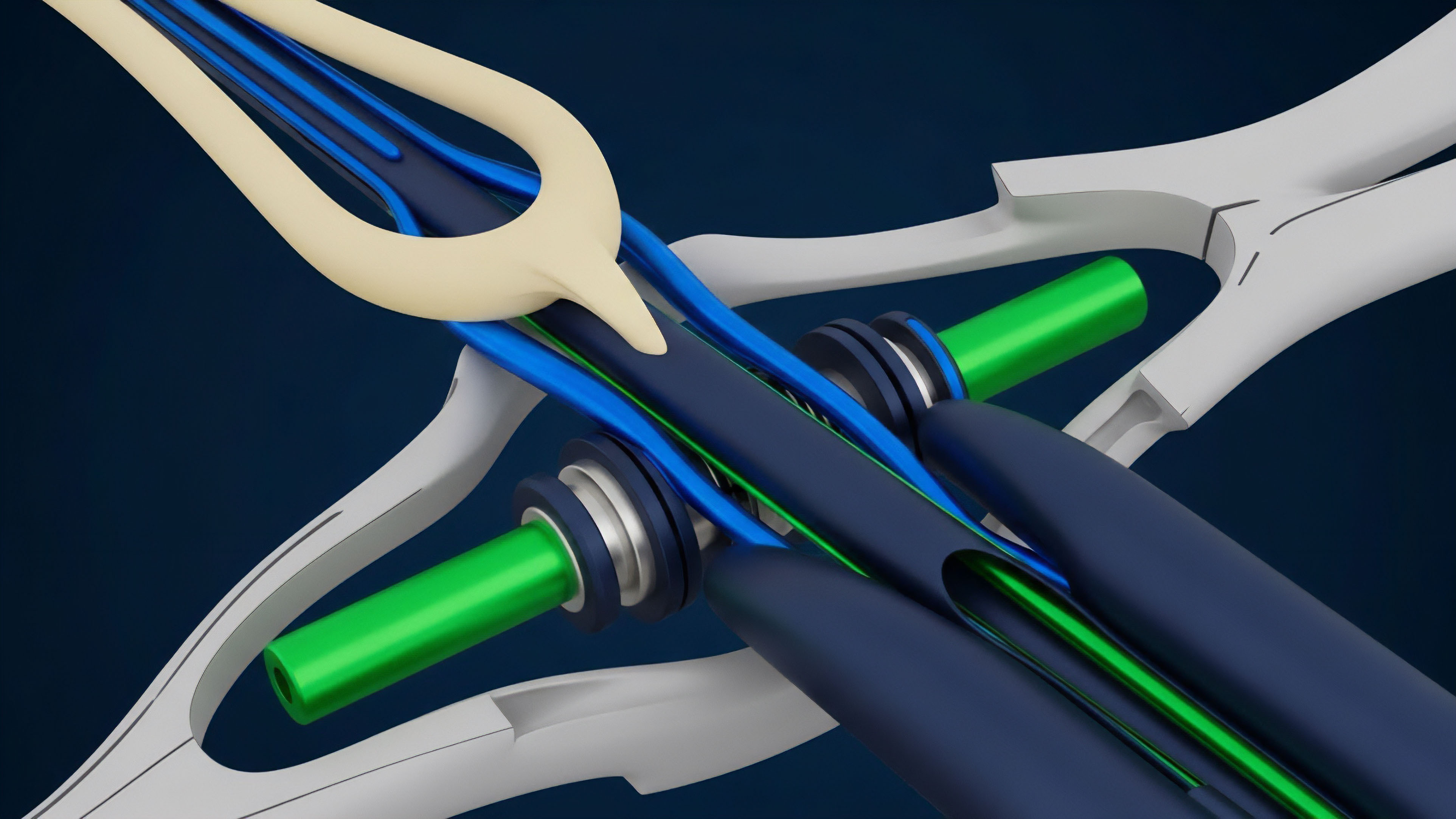
Beyond basic transaction signing, ECC enables more advanced financial primitives through multi-party computation (MPC) and threshold signatures. In a decentralized options vault, multiple participants might need to sign off on a settlement or a change in governance parameters. Threshold signatures allow a predefined number of participants (e.g.
3 out of 5) to collectively sign a message without any single participant having full control over the private key. This mitigates single points of failure and enhances systemic security for high-value contracts. This distributed key management approach shifts the risk model from individual key security to a collective governance problem, which is a significant architectural decision for complex derivatives platforms.

Evolution
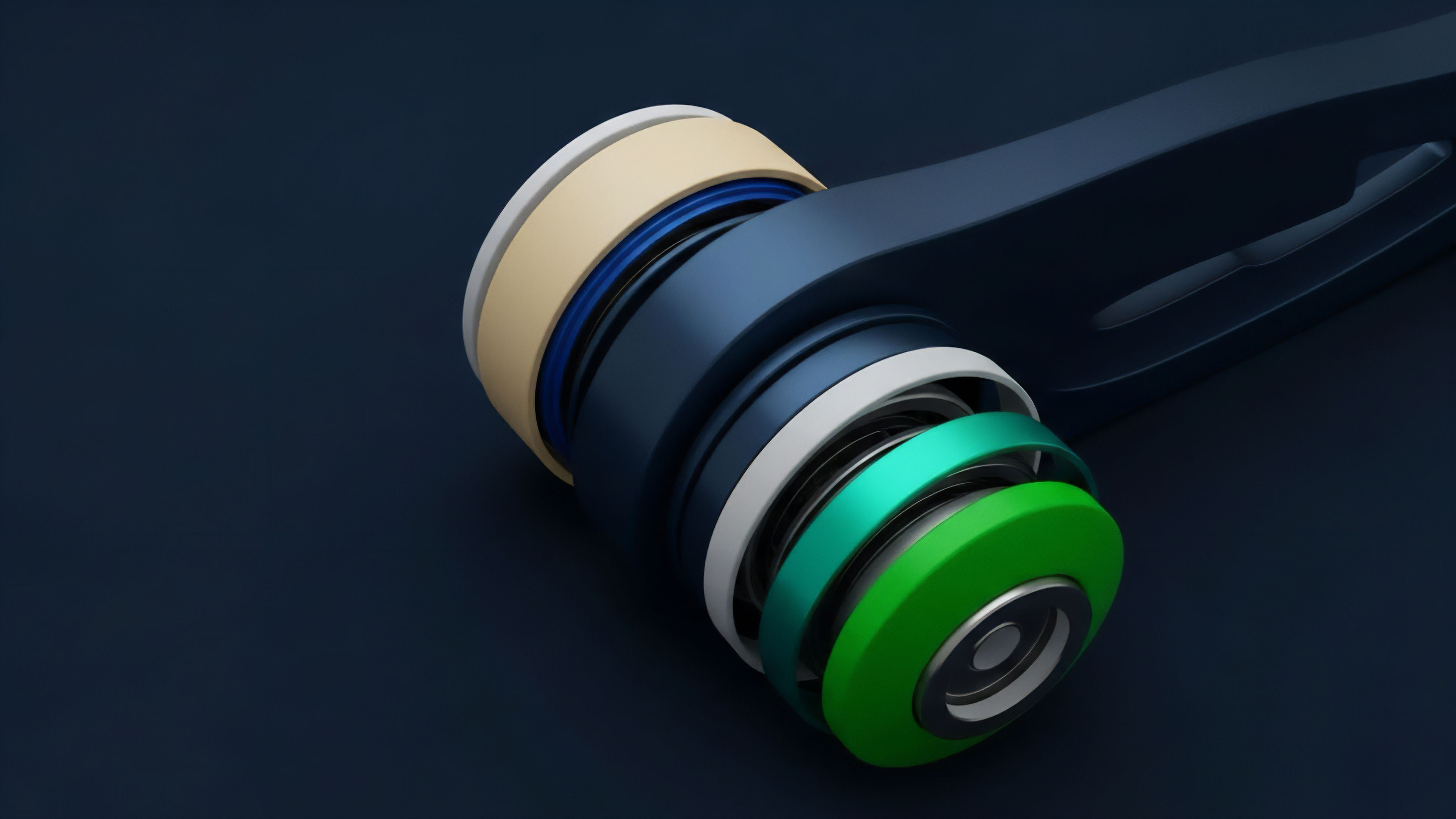
The evolution of ECC within decentralized finance is driven by the demand for increased efficiency and enhanced functionality, moving beyond simple ECDSA. The initial implementation of ECDSA in Bitcoin, while robust, has limitations regarding signature size and the ability to aggregate signatures from multiple parties. This led to the development and adoption of Schnorr signatures, which offer two key advantages: improved efficiency and native support for key aggregation.
With Schnorr signatures, multiple signatures from different parties can be combined into a single, valid signature. This is particularly relevant for options protocols where complex strategies might involve multiple inputs or collateral sources. By aggregating signatures, transaction sizes are reduced, leading to lower gas costs and increased throughput.
The transition to more sophisticated financial products, particularly those requiring privacy or multi-party control, has pushed ECC to new frontiers. Zero-knowledge proofs (ZKPs) are increasingly being integrated into decentralized options protocols to allow users to prove certain facts about their position (e.g. collateral amount) without revealing the exact details. ECC provides the mathematical foundation for certain types of ZKPs, specifically through elliptic curve pairings.
This allows for privacy-preserving derivatives, where market participants can prove solvency or eligibility for a trade without leaking sensitive information that could be exploited by front-running bots or adversarial market makers.
A significant architectural challenge facing decentralized derivatives platforms is the inherent tension between security and functionality. The current standard, ECDSA, is robust but lacks the flexibility needed for complex, multi-party operations. The adoption of advanced techniques like threshold signatures (t-of-n) represents a strategic shift in risk management.
A threshold signature scheme distributes a single private key among multiple key holders. To sign a transaction, a minimum number of key holders must cooperate. This model eliminates the single point of failure inherent in a single-key system, making it suitable for managing large collateral pools or protocol governance in a decentralized options vault.
The challenge is in designing the incentive structures and governance mechanisms around these distributed key holders to ensure they act in the protocol’s best interest. The shift from a single-user security model to a distributed security model introduces game-theoretic challenges where a rational actor might defect if the incentives are misaligned.

Horizon
The future trajectory of ECC in decentralized finance faces two primary vectors of change: the near-term implementation of advanced primitives and the long-term threat of quantum computing. In the near term, the widespread adoption of threshold signatures and MPC will redefine how decentralized options protocols manage risk and execute complex strategies. We are moving toward a system where the security of high-value derivatives is not reliant on a single private key, but rather on a distributed network of key shares.
This allows for a more robust governance model where the collective decision of a decentralized autonomous organization (DAO) can control a large collateral pool. The systemic implication here is a significant reduction in single points of failure and an increase in the resilience of the financial system against internal collusion or external attacks.
Post-quantum cryptography research is actively developing new primitives to replace ECC, ensuring long-term security against quantum computing threats.
However, the long-term horizon is dominated by the looming threat of quantum computing. A sufficiently powerful quantum computer, specifically one capable of running Shor’s algorithm, would render ECC obsolete. Shor’s algorithm can solve the ECDLP efficiently, effectively breaking the mathematical foundation of nearly all current digital asset security.
While a practical quantum computer capable of this attack does not yet exist, the potential for its development necessitates a proactive approach to post-quantum cryptography (PQC). The financial industry must prepare for a transition to new cryptographic primitives that are resistant to quantum attacks. The transition to PQC for decentralized derivatives protocols involves significant architectural changes, as new signature algorithms will have different performance characteristics and potentially higher computational overhead.
This transition requires careful planning to avoid a catastrophic security failure in the future. The design of a robust options protocol must account for this eventual transition by implementing modularity in its cryptographic stack, allowing for seamless upgrades to PQC algorithms without disrupting the underlying financial logic.
The development of ZKPs and homomorphic encryption also represents a critical pathway for ECC’s future relevance. By leveraging ECC pairings, ZKPs allow for a new class of privacy-preserving derivatives where trading strategies can be executed without revealing proprietary information to the public ledger. This creates a more sophisticated and efficient market microstructure by mitigating front-running and providing greater anonymity for large institutional participants.
The evolution of ECC is not just about security; it is about enabling a new level of financial complexity and privacy that will define the next generation of decentralized markets.

Glossary

Asymmetric Cryptography

Institutional Cryptography

Elliptic Curve Digital Signature Algorithm

Quantum Computing Threat

Elliptic Curve Signature Costs

Yield Curve Construction

Anti-Money Laundering Cryptography

Expiration Curve Dynamics
Funding Rate Curve