Essence
Zero-Knowledge Proofs Risk Reporting (ZKPRR) addresses the fundamental tension between financial transparency and strategic privacy within decentralized systems. In traditional finance, risk reporting often relies on a centralized intermediary ⎊ an auditor or regulator ⎊ who possesses full visibility into a firm’s positions to verify solvency and systemic risk. In decentralized finance (DeFi), the public nature of the blockchain ledger creates a paradox: while transparency is necessary for trustless verification of collateral, it also exposes proprietary trading strategies and counterparty positions.
This data leakage hinders institutional participation and market efficiency. ZKPRR offers a cryptographic solution by enabling a protocol or market participant to prove a specific risk condition ⎊ such as a collateralization ratio exceeding a threshold or a value-at-risk (VaR) calculation remaining within bounds ⎊ without revealing the underlying assets, liabilities, or trading history used to generate that proof. The system separates the verifiability of a calculation from the disclosure of the inputs, thereby creating a new architectural primitive for risk management in permissionless markets.
ZKPRR enables a financial entity to cryptographically prove compliance with risk thresholds without revealing sensitive proprietary positions or underlying data.
The core functionality of ZKPRR rests on the ability to generate a succinct, non-interactive argument of knowledge. This argument, or proof, attests to the execution of a specific computation on private inputs. The verifier can check the proof’s validity in seconds, often requiring significantly less computational resources than running the original calculation itself.
This capability shifts the paradigm from trusting an intermediary with sensitive data to trusting a mathematical proof of compliance. For derivatives markets, where counterparty risk and collateral management are paramount, ZKPRR provides a mechanism for continuous, automated risk monitoring without compromising the competitive edge of market makers or the privacy of individual users. This redefines the concept of auditability in a decentralized context, moving away from full disclosure toward verifiable assertions.

Origin
The theoretical foundation of ZKPRR stems from the seminal work on Zero-Knowledge Proofs by Goldwasser, Micali, and Rackoff in the mid-1980s. The initial application of ZKPs focused primarily on identity verification and private transactions. However, the practical application of ZKPs to financial systems, particularly risk management, gained traction with the emergence of decentralized finance.
The challenge of systemic risk in DeFi, highlighted by numerous protocol failures where hidden leverage or fractional reserves led to cascading liquidations, underscored the need for verifiable solvency. Early attempts to address this relied on full transparency, but this approach proved untenable for large-scale financial institutions accustomed to proprietary data protection. The first practical implementations of ZKPRR appeared in the form of “proof-of-reserves” for centralized exchanges (CEXs) following major market events.
These proofs, while rudimentary, demonstrated the viability of using ZKPs to prove a specific balance sheet condition without revealing individual user account details. The evolution from these initial, static proofs to continuous, dynamic risk reporting for complex derivatives protocols marks the current phase of development.
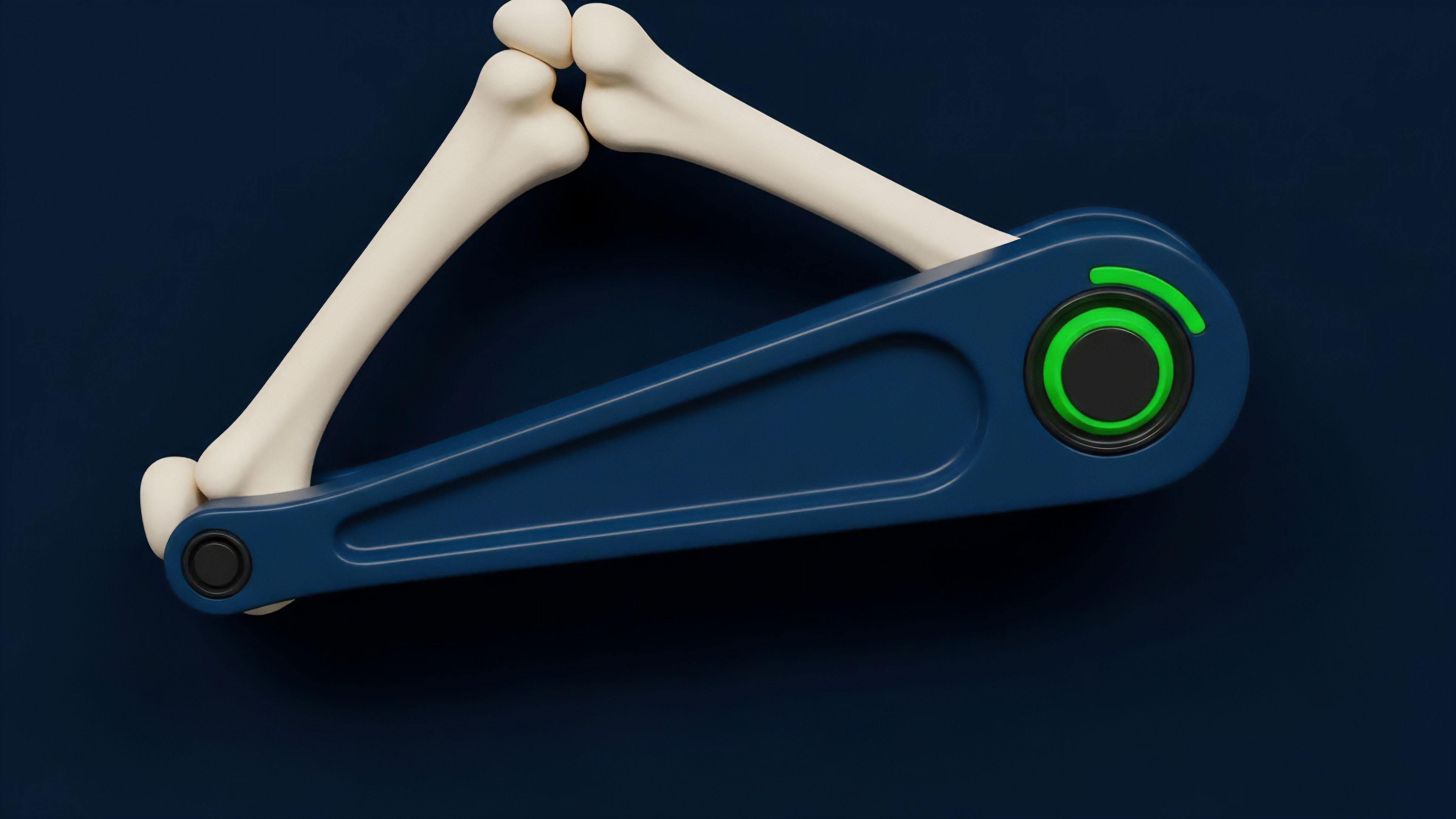
The need for ZKPRR in derivatives markets is particularly acute due to the complexity of risk calculations and the high-stakes nature of leverage. Traditional financial models, such as Black-Scholes for option pricing or Monte Carlo simulations for VaR, require extensive input data. Applying these models to decentralized systems created a conflict: either expose all inputs on-chain, making the protocol vulnerable to front-running and data extraction, or keep inputs private, rendering the protocol unauditable and susceptible to insolvency risks.
ZKPRR provides the necessary bridge by allowing a protocol to prove that a calculation, based on private inputs, results in a compliant output. This development is a direct response to the market’s demand for both privacy and trust, enabling sophisticated financial instruments to operate securely on public infrastructure.
Theory
The theoretical underpinning of ZKPRR involves a specific application of cryptographic techniques to financial modeling. The process begins with a set of private inputs (e.g. individual collateral values, debt positions, option strike prices) and a public function (e.g. a specific risk model or collateralization ratio formula). The core challenge is to prove that applying the function to the private inputs yields a compliant result without revealing the inputs themselves.
This is achieved through a multi-step process involving circuit design and proof generation.
Proof Generation and Verification Mechanics
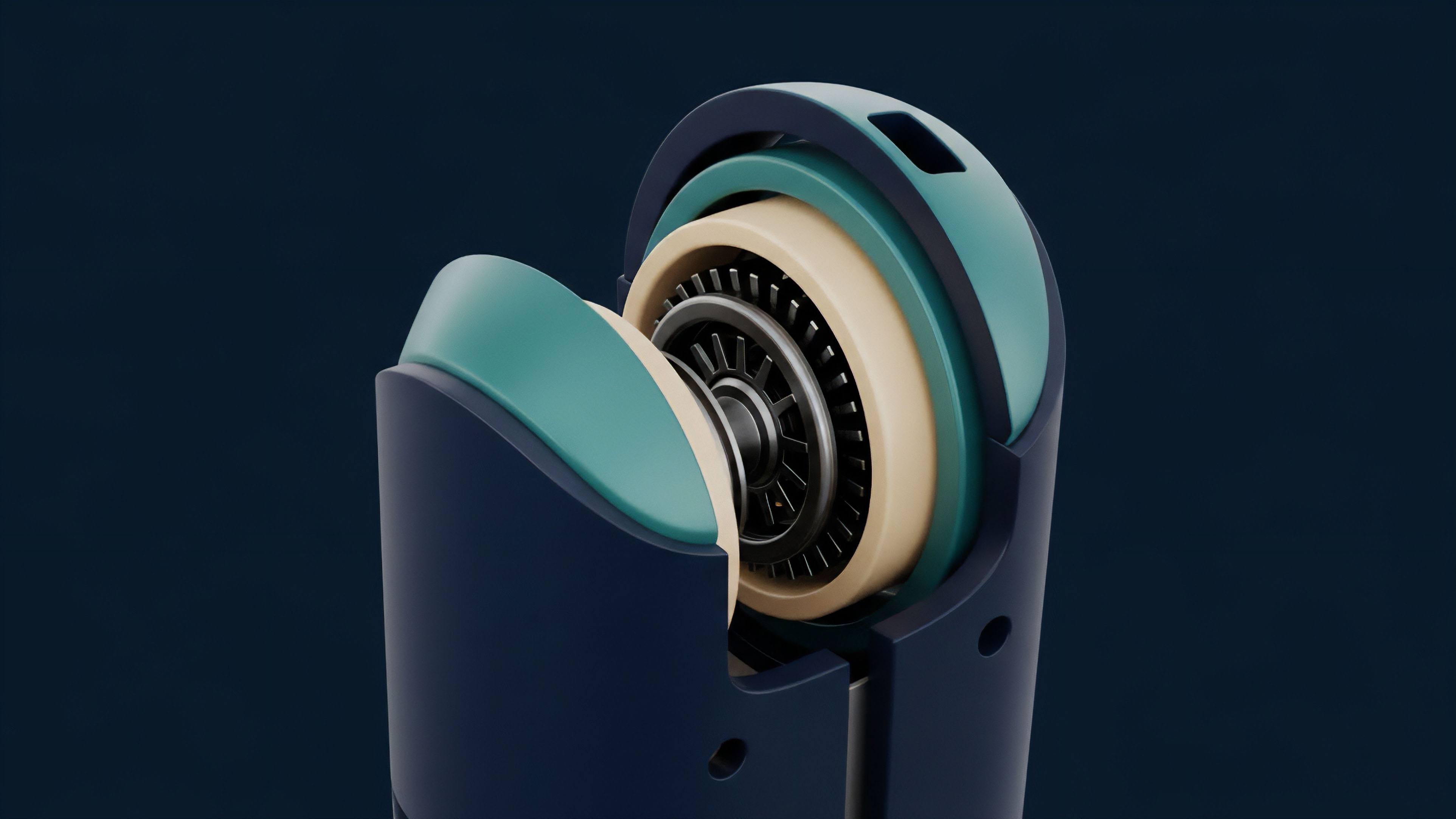
The first step involves translating the financial logic into a cryptographic circuit. A circuit represents the computation as a series of gates, where each gate performs a basic arithmetic operation. The complexity of this circuit determines the cost and time required for proof generation.
For derivatives, this can involve complex calculations such as calculating a portfolio’s VaR or determining the margin requirement based on multiple asset correlations. The prover generates a proof that verifies the execution of this circuit. The verifier then uses this proof, along with public parameters and the public output (the compliant status), to confirm the validity of the statement without ever accessing the private inputs.
This process relies on mathematical properties that ensure the proof cannot be forged or manipulated. The security of the system is predicated on the hardness of certain mathematical problems, such as the discrete logarithm problem or elliptic curve cryptography, depending on the specific ZKP scheme used.
The choice of ZKP scheme ⎊ zk-SNARKs versus zk-STARKs ⎊ involves significant trade-offs for risk reporting applications. zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) offer small proof sizes and fast verification times, making them suitable for on-chain verification where gas costs are a concern. However, many zk-SNARK constructions require a “trusted setup,” where a set of initial parameters must be generated securely. If this setup is compromised, proofs could potentially be forged. zk-STARKs (Zero-Knowledge Scalable Transparent Argument of Knowledge) avoid the need for a trusted setup and offer greater scalability for complex computations, but often produce larger proofs, increasing verification costs.
For continuous risk reporting, the trade-off between trusted setup risk and verification cost is a critical architectural decision.

Risk Model Integration
ZKPRR fundamentally alters how risk models are applied and verified. Instead of providing an auditor with access to the full model and input data, the system allows for the cryptographic verification of specific model outputs. Consider a derivatives protocol that needs to prove its overall solvency.
The protocol can generate a proof that the sum of all collateral exceeds the sum of all liabilities, without revealing the individual positions of users or the total value of assets under management. This approach allows for a continuous, real-time audit where a verifier can check the proof’s validity at any time. The core benefit is the ability to maintain continuous solvency verification, moving beyond static, point-in-time audits.
This shift is particularly relevant in high-leverage environments where market movements can rapidly change a protocol’s risk profile.
The complexity of risk reporting circuits often requires careful design to balance proof generation cost with verification speed, making the choice between zk-SNARKs and zk-STARKs a central architectural consideration.
The application of ZKPs to risk reporting also requires a re-evaluation of how risk parameters are defined. A system must ensure that the risk model used for proof generation accurately reflects the true risk of the underlying assets. This involves designing the cryptographic circuit to enforce specific financial rules, such as collateral haircut percentages or liquidation thresholds.
The challenge lies in ensuring that the circuit accurately represents the real-world financial dynamics without introducing vulnerabilities or oversimplifying the risk calculation to a point where it becomes ineffective. This process requires a tight collaboration between cryptographers and quantitative finance experts.

Approach
The implementation of ZKPRR in practice involves a strategic decision regarding the location of proof generation and verification. Most implementations adopt an off-chain generation, on-chain verification approach. This minimizes gas costs and leverages the scalability of off-chain computation while ensuring the verifiability of the proof on the public ledger.
The process begins with the protocol’s risk engine, which continuously monitors all user positions and calculates the necessary risk metrics. The data is kept private, but a proof is generated to attest to the protocol’s compliance with predefined parameters. This proof is then submitted to a smart contract on the blockchain for verification.
The verification contract simply checks the validity of the proof, which confirms the protocol’s health without revealing any sensitive information.

Current Implementation Models
There are several distinct models for applying ZKPRR in current decentralized markets. The most common model focuses on solvency proofs. In this model, a protocol periodically generates a proof that its total assets exceed its total liabilities.
This approach is primarily used by centralized entities seeking to provide transparency to users while maintaining privacy. A more sophisticated model, used in decentralized derivatives protocols, involves continuous risk monitoring. Here, the protocol continuously generates proofs that ensure individual user accounts remain above specific collateralization thresholds.
This enables a real-time, trustless liquidation mechanism where a proof of insufficient collateral can trigger a liquidation without revealing the exact amount of collateral or debt.
Another implementation model involves private options vaults where users deposit assets into a vault, and the vault manager generates proofs that attest to the vault’s adherence to a specific investment strategy. The users can verify that the vault is operating according to its mandate without seeing the specific trades being executed. This allows for complex, automated strategies to operate in a trustless environment where the manager’s alpha (proprietary strategy) is protected while still providing transparency regarding risk management.
The challenge in this approach lies in designing the circuit to capture all relevant risk parameters without becoming computationally prohibitive.

Practical Trade-Offs and Challenges
The primary challenge in deploying ZKPRR today is the computational overhead associated with proof generation. Generating proofs for complex financial calculations, especially those involving large data sets or iterative processes like Monte Carlo simulations, can be resource-intensive and time-consuming. This introduces proof latency, where the time required to generate a proof can lag behind rapid market movements.
If a protocol’s risk profile changes faster than a proof can be generated, the system’s security can be compromised. Furthermore, the cost of verifying proofs on-chain, while less than generation, still represents a significant overhead for protocols operating on high-demand blockchains. The trade-off between the complexity of the risk model and the feasibility of generating a timely proof is a critical design consideration for any ZKPRR system.
| Risk Reporting Method | Transparency Level | Data Privacy | Systemic Risk Verification | Implementation Complexity |
|---|---|---|---|---|
| Traditional Audit (Off-chain) | High (to auditor only) | Low (to auditor) | Reactive/Periodic | Medium (manual process) |
| Full On-chain Transparency | High (to all users) | None | Continuous | Low (simple implementation) |
| Zero-Knowledge Proofs | Verifiable (to all users) | High (to all users) | Continuous/Proactive | High (cryptographic design) |
Evolution
The evolution of ZKPRR reflects a transition from static, point-in-time solvency verification to dynamic, continuous risk management. Early implementations of ZKPRR were primarily focused on providing proof-of-reserves for centralized exchanges. This approach involved generating a snapshot proof that the exchange’s total assets exceeded its total liabilities at a specific moment in time.
While valuable for building trust after high-profile failures, this method failed to address continuous systemic risk in a rapidly moving market. The current evolution focuses on integrating ZKPRR directly into the protocol’s core logic, enabling real-time risk checks and automated responses.

From Static Proofs to Dynamic Risk Management
The next generation of ZKPRR systems moves beyond simple balance sheet verification to encompass more sophisticated risk metrics. This involves generating proofs for continuous calculations of risk parameters such as VaR (Value at Risk) or Expected Shortfall (ES). In a derivatives context, this means a protocol can prove that its aggregate exposure to a specific asset or market condition remains below a predetermined threshold.
This shift changes the role of risk reporting from a post-mortem analysis to a proactive risk mitigation tool. When a proof fails to verify, it signals an immediate breach of risk policy, potentially triggering automated mechanisms to reduce leverage or increase collateral requirements across the protocol. This level of automation significantly reduces the reliance on human intervention and centralized risk committees.
The transition from point-in-time solvency checks to continuous, dynamic risk monitoring is reshaping how protocols manage leverage and systemic risk.
The development of ZKPRR also enables new forms of financial engineering. By allowing for verifiable privacy, protocols can design complex, multi-asset derivatives products where counterparty risk is managed cryptographically. This allows for the creation of new market structures where participants can engage in sophisticated trading strategies without revealing their positions to other market makers or to the public.
This shift facilitates greater institutional participation in DeFi by mitigating the data leakage that currently prevents large players from bringing proprietary strategies on-chain. The system’s ability to verify complex calculations without revealing the inputs opens the door to private lending pools, dark pools for options trading, and other financial instruments where information asymmetry is critical to strategy execution.

Horizon
Looking forward, ZKPRR represents a foundational shift in the architecture of financial systems. The horizon for this technology extends beyond simple protocol compliance to encompass a new framework for regulatory oversight and market design. The ultimate goal is to create a financial ecosystem where all risk data is continuously verifiable, yet all proprietary data remains private.
This changes the role of the regulator from an entity that demands full access to sensitive data to one that simply verifies a cryptographic proof of compliance. This new paradigm offers a pathway for decentralized finance to achieve regulatory acceptance without sacrificing its core principles of privacy and decentralization.

The Regulatory Implications of Verifiable Privacy
ZKPRR creates a new form of regulatory arbitrage. If a protocol can prove compliance with capital adequacy requirements or anti-money laundering (AML) checks without revealing the identities or transaction histories of its users, it presents a compelling alternative to current regulatory frameworks. Regulators can verify the integrity of the system and ensure systemic stability without compromising individual privacy.
This changes the dynamic of compliance from a data-intensive process to a cryptographic verification process. The challenge lies in standardizing the cryptographic circuits used for risk calculations, ensuring that all protocols are verifying against the same, agreed-upon risk model. This requires a new layer of standardization and cooperation between regulatory bodies and protocol developers.

Future Market Structures and Risk Aggregation
The future of ZKPRR involves its application to aggregated systemic risk reporting. Imagine a system where multiple derivatives protocols can collectively prove that the total leverage in the market remains below a certain threshold. This requires a mechanism for aggregating proofs from different protocols without revealing the specific positions of each protocol.
This allows for a holistic view of systemic risk across the entire ecosystem while maintaining the privacy of individual market participants. This capability is essential for managing contagion risk, where a failure in one protocol can cascade through the system due to interconnected leverage. ZKPRR offers a path to build this aggregated risk monitoring system, creating a more resilient and stable decentralized financial infrastructure.
A further development on the horizon is the use of ZKPRR for private financial modeling. This involves running complex risk simulations on private data and generating proofs that attest to the accuracy of the model’s output. For instance, a fund could prove to its limited partners that its VaR calculation accurately reflects the risk of its portfolio without revealing the specific assets held.
This capability enables new forms of investment products and risk management services where proprietary information is protected while still providing verifiable assurance to investors. The integration of ZKPRR with AI and machine learning models for risk analysis is a natural progression, where the integrity of a model’s output can be verified without revealing the underlying training data or parameters.
| Application Area | Current State (Post-Mortem Audits) | Future State (ZKPRR Integration) |
|---|---|---|
| Solvency Verification | Static snapshot proofs (CEXs) | Continuous, dynamic proofs (DeFi protocols) |
| Regulatory Compliance | Data disclosure required | Verifiable compliance without disclosure |
| Systemic Risk Monitoring | Fragmented and non-aggregated | Aggregated proofs for cross-protocol risk |
| Private Financial Products | Trust-based or fully transparent | Cryptographically verifiable private vaults |

Glossary

Soundness Completeness Zero Knowledge

Regulatory Reporting Frameworks

Zero-Knowledge Margin Call

Economic Soundness Proofs

Hardware Agnostic Proofs
Volatility Arbitrage Risk Reporting

Risk Management

Derivatives Reporting
Market Efficiency






