Essence
Surveillance remains the default state of the blockchain. Private Transaction Validation functions as the cryptographic substrate for financial autonomy, ensuring that ledger integrity remains decoupled from data visibility. This architecture permits the existence of a public truth constructed from private facts.
By shielding the identity of participants and the magnitude of transfers, the protocol prevents the exploitation of order flow by predatory actors.
Private Transaction Validation enables the decoupling of ledger integrity from data visibility.
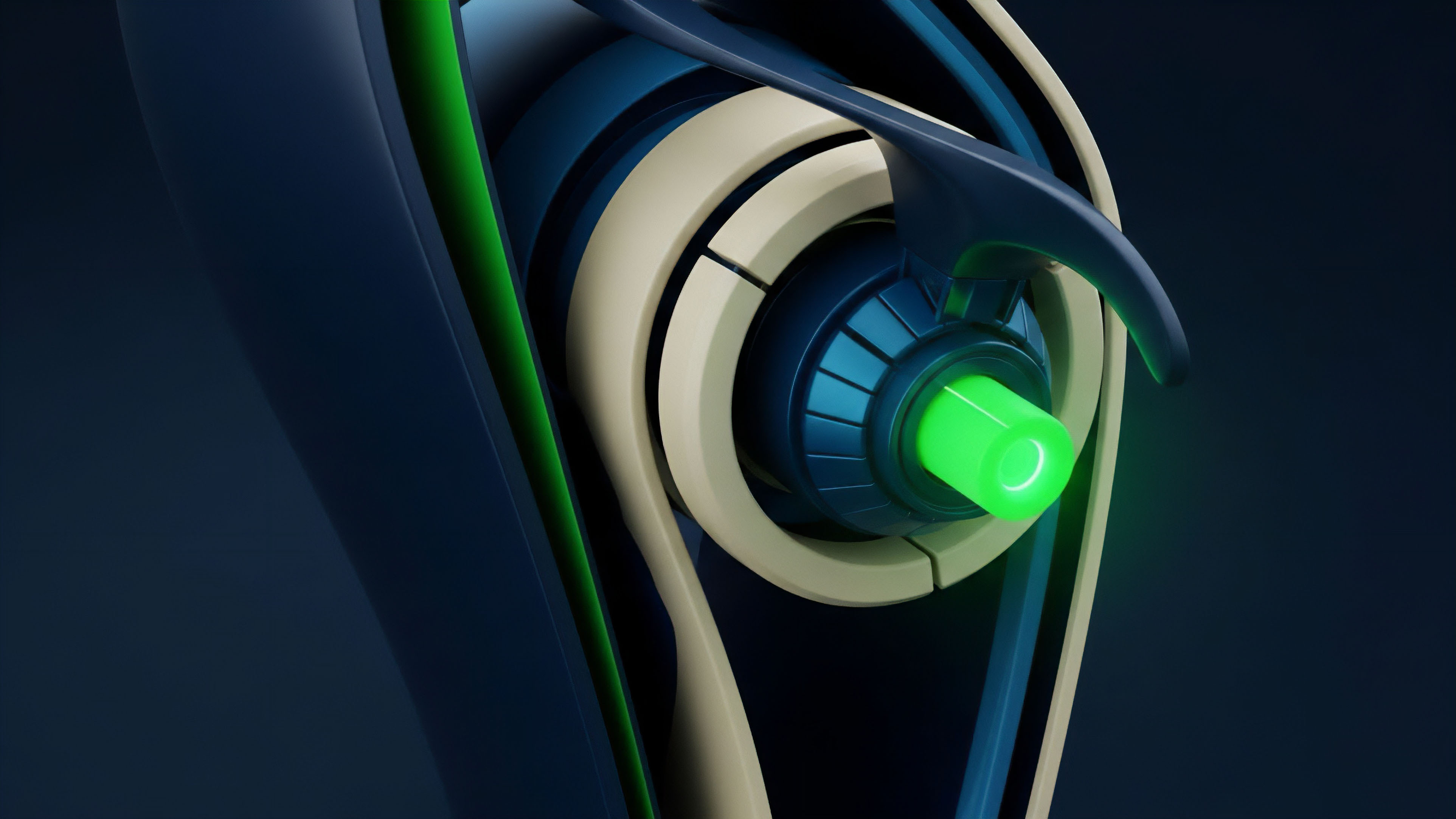
The primary function of this mechanism involves the verification of state transitions without the disclosure of the underlying transaction parameters. It transforms the blockchain from a transparent audit log into a secure execution environment. Within the context of decentralized finance, this confidentiality is a requirement for institutional participation, as it protects proprietary trading strategies and prevents front-running.
The protocol ensures that every participant maintains control over their financial footprint while satisfying the consensus requirements of the network.

Origin
The drive for Private Transaction Validation stems from the inherent surveillance risk of public ledgers. Early blockchain iterations treated transparency as a security feature, creating a permanent, global audit trail for every participant. This structural exposure necessitated a shift toward cryptographic proofs that separate the validity of a transfer from its metadata.
The development of ring signatures and stealth addresses provided the first practical methods for obfuscating transaction participants.
The drive for cryptographic privacy emerged as a response to the systemic risks of permanent, public ledger transparency.
Early cypherpunk research into electronic cash emphasized the necessity of anonymity to mirror the properties of physical currency. As the digital asset market matured, the limitations of simple obfuscation became apparent, leading to the adoption of zero-knowledge proofs. These mathematical structures allowed for the verification of complex statements without revealing any information beyond the statement’s validity.
This shift marked the transition from basic privacy to verifiable, programmable confidentiality.

Theory
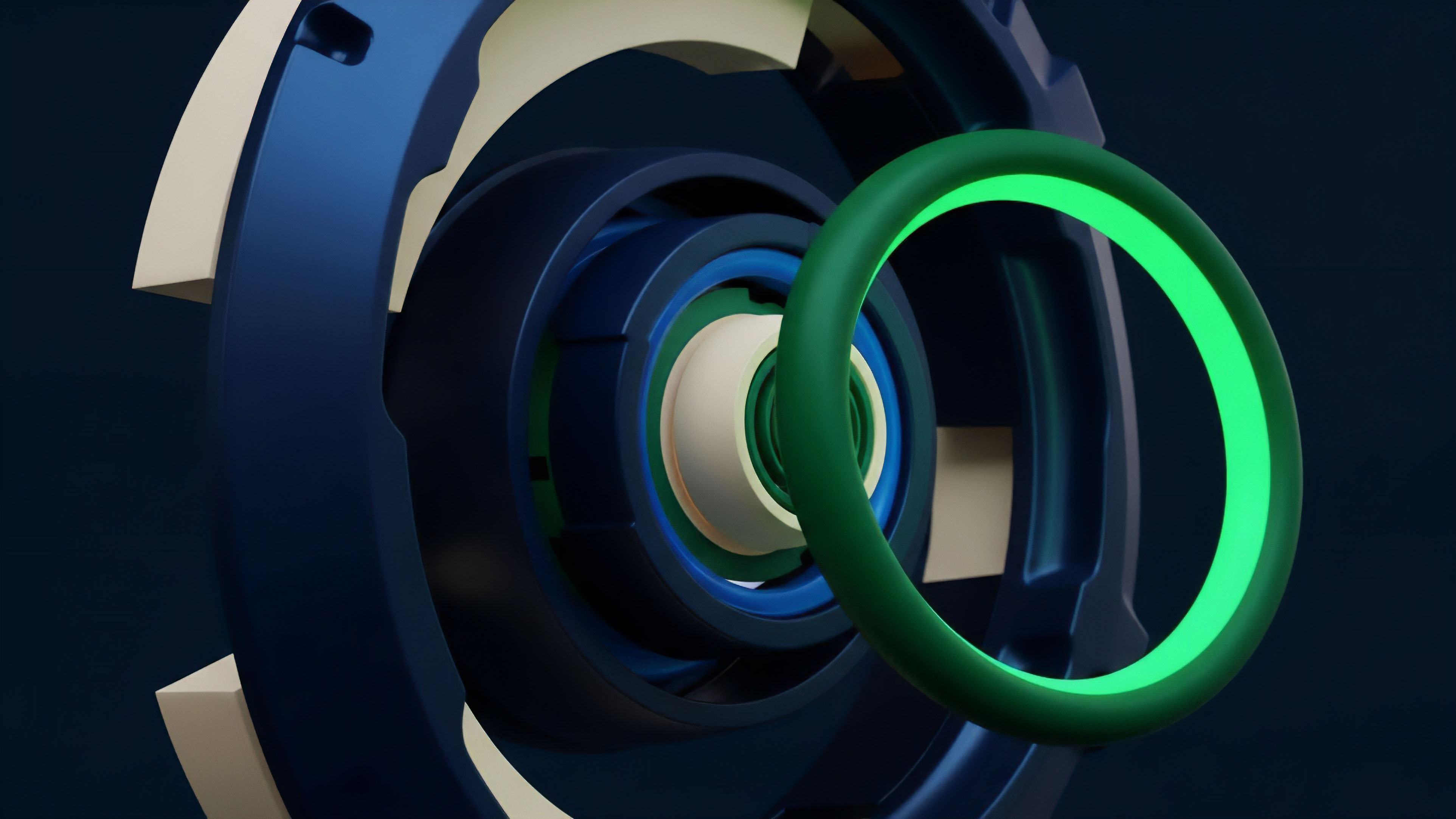
Mathematical structures for Private Transaction Validation rely on the computational hardness of specific problems within elliptic curve cryptography. Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge (zk-SNARKs) allow a prover to convince a verifier of a statement’s truth without revealing the statement itself. This process reduces transaction overhead while maintaining the security properties of the underlying consensus mechanism.
Just as the double-slit experiment reveals the observer’s impact on physical reality, the act of observing a transaction in a public ledger alters its market value through information leakage.

Cryptographic Proof Systems
The integrity of private validation depends on the selection of a specific proving system. Each system offers different trade-offs regarding proof size, verification time, and the necessity of a trusted setup.
- Succinctness refers to the ability of the proof to be verified much faster than the original computation.
- Non-Interactivity ensures that the prover and verifier do not need to be online simultaneously.
- Soundness guarantees that a malicious prover cannot convince a verifier of a false statement.
- Zero-Knowledge ensures that the verifier learns nothing about the private inputs used to generate the proof.

Mathematical Constraints
The construction of a private transaction involves defining a circuit that represents the rules of the protocol. This circuit includes constraints that ensure the sum of inputs equals the sum of outputs and that the sender possesses the necessary private keys. The proof generation process converts these constraints into a polynomial that can be verified by the network.
This ensures that the state transition is valid without exposing the specific values involved in the computation.

Approach
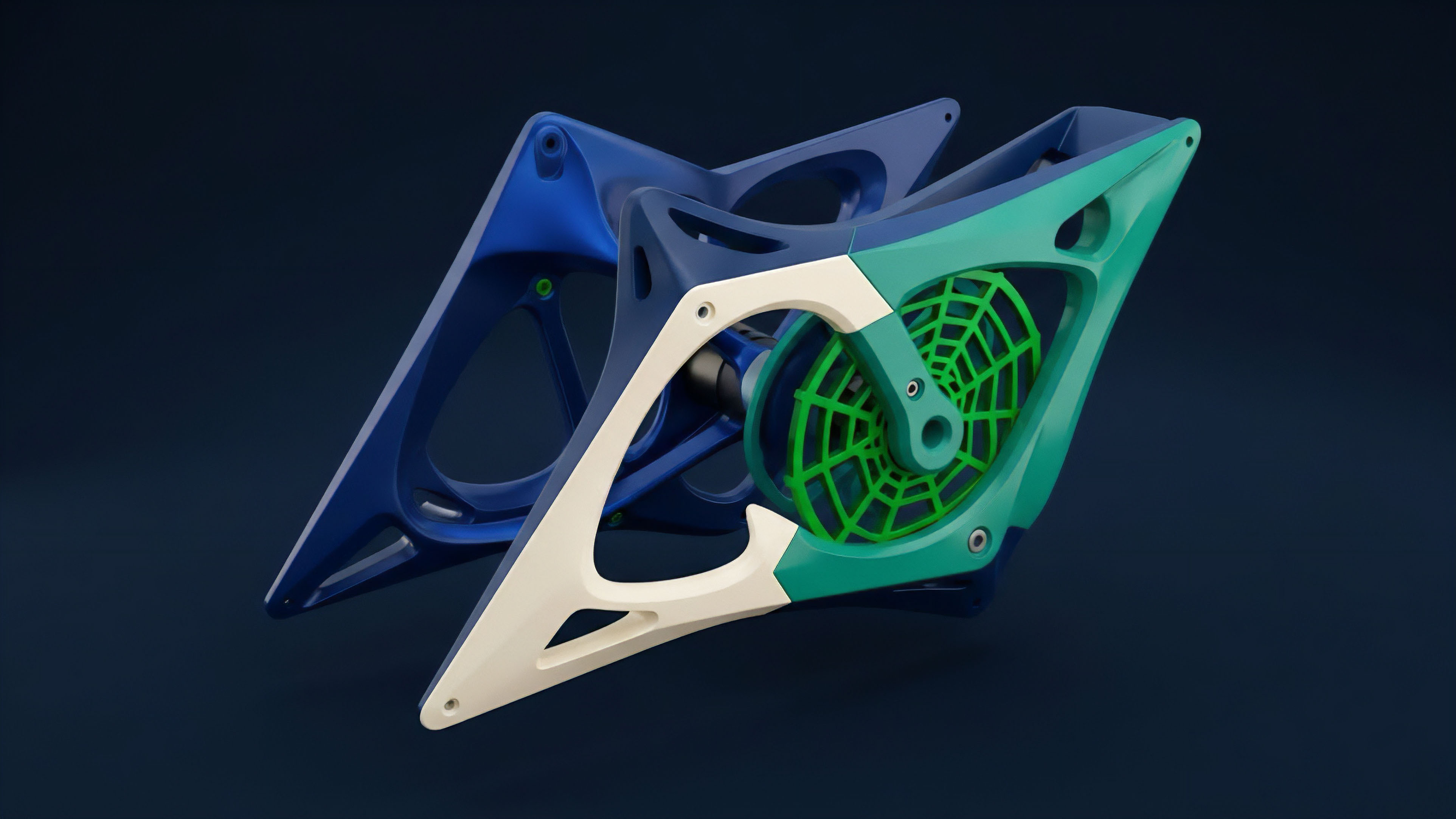
Current execution of Private Transaction Validation utilizes Recursive Proof Composition to scale private environments. Systems leverage these proofs to create private execution layers on top of transparent base protocols. This method allows for the aggregation of multiple private transactions into a single proof, significantly reducing the data footprint on the main ledger.
Mathematical proofs allow for the verification of state transitions without exposing the underlying transaction parameters.

Comparative Validation Architectures
Different methodologies exist for achieving transaction privacy, each with distinct security profiles and performance characteristics.
| Feature | Zero-Knowledge Proofs | Trusted Execution Environments | Multi-Party Computation |
|---|---|---|---|
| Trust Assumption | Mathematical Hardness | Hardware Manufacturer | Honest Majority |
| Proving Speed | Computationally Intensive | Near-Native Speed | Network Latency Bound |
| Privacy Guarantee | Cryptographic Certainty | Hardware Dependent | Shared Secret Security |
| Scalability | High via Recursion | Limited by Hardware | Limited by Participants |
Implementation Layers
Protocols implement private validation at various levels of the technology stack. Some integrate it directly into the base layer, while others utilize secondary layers to provide privacy as a service. This modularity allows users to opt-in to privacy based on their specific needs and regulatory requirements.
The use of View Keys provides a mechanism for selective disclosure, allowing participants to share transaction details with authorized third parties for auditing or compliance purposes.
Evolution
The trajectory of Private Transaction Validation has shifted from simple obfuscation to complex, programmable confidentiality. Early protocols focused on asset-level privacy, whereas modern architectures enable private smart contracts. This shift allows for institutional-grade dark pools where order flow remains hidden from predatory arbitrageurs.
The integration of Compliance-Aware Privacy allows for the verification of user attributes without revealing their identity, satisfying regulatory requirements while maintaining user sovereignty.

Stages of Development
The maturation of privacy technology follows a clear path of increasing complexity and utility.
- Obfuscation utilized mixing services and coinjoin protocols to break the link between senders and receivers.
- Shielded Transfers introduced zero-knowledge proofs to hide transaction amounts and addresses at the protocol level.
- Private Execution enabled the development of smart contracts that can process private data and maintain a private state.
- Selective Disclosure provided the tools for users to prove compliance without sacrificing their overall privacy.
Regulatory Adaptation
The interaction between private validation and legal frameworks is a primary driver of protocol design. Modern systems incorporate features that allow for the verification of Know Your Customer (KYC) credentials through zero-knowledge proofs. This allows users to prove they meet specific criteria, such as residency or accreditation, without sharing their personal identification documents.
This balance between privacy and compliance is vital for the long-term viability of decentralized financial systems.

Horizon
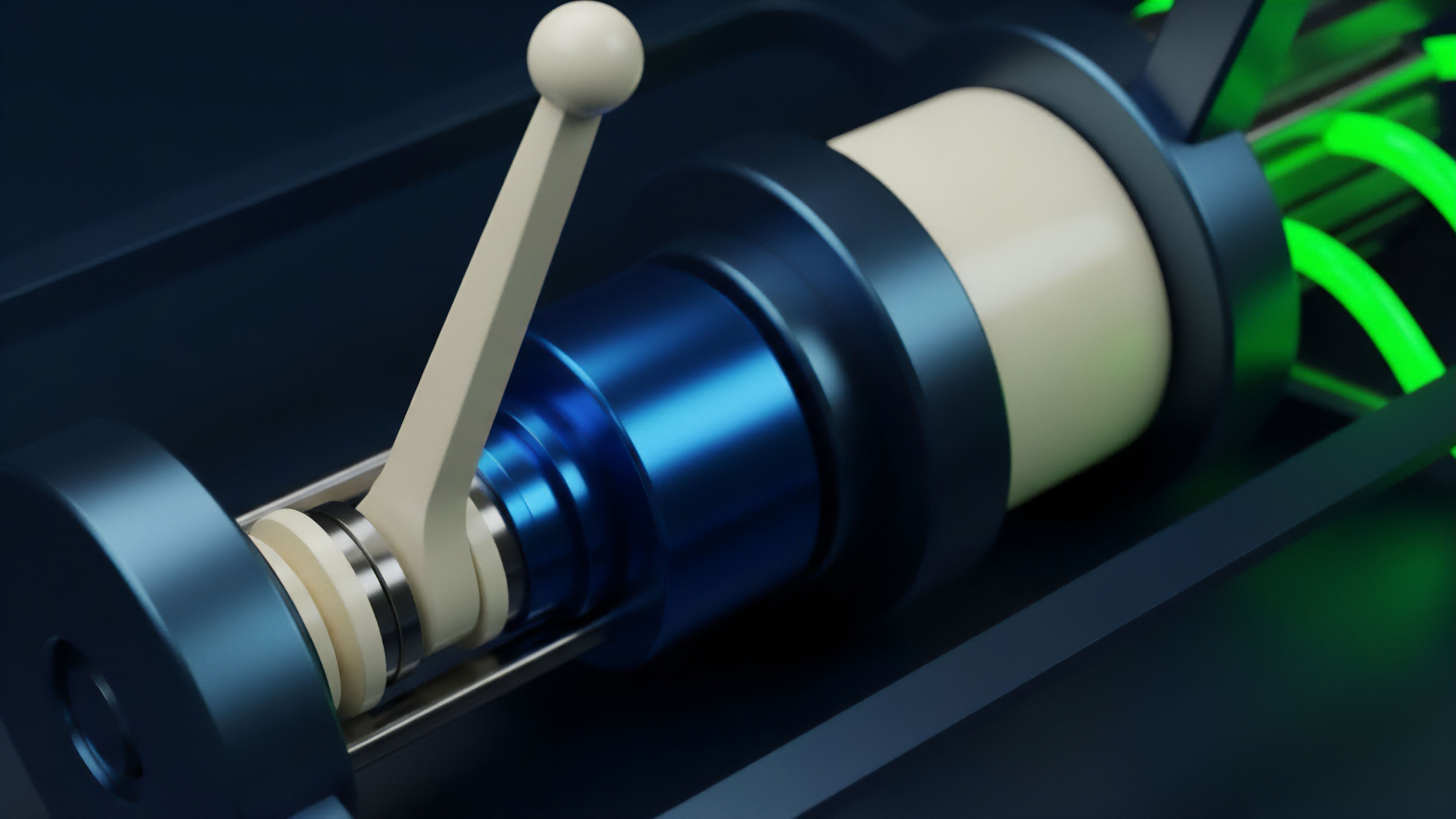
Future iterations will integrate Fully Homomorphic Encryption (FHE) to allow computation on encrypted data without decryption. This eliminates the need for trusted setups and enables a new class of privacy-preserving primitives. Regulatory structures will eventually demand selective disclosure, forcing a convergence between absolute privacy and jurisdictional compliance.
The development of Hardware-Accelerated Proving will reduce the time required to generate complex proofs, making private validation as fast as transparent transactions.
The shift toward programmable confidentiality marks the transition from simple asset shielding to complex private execution.

Emerging Technologies
The next generation of privacy protocols will leverage several advancing fields to enhance security and performance.
| Technology | Functional Impact | Systemic Implication |
|---|---|---|
| Fully Homomorphic Encryption | Computation on Encrypted Data | Elimination of Data Exposure |
| Post-Quantum Cryptography | Quantum-Resistant Proofs | Long-Term Security Assurance |
| Recursive STARKs | Massive Batching of Proofs | Hyper-Scalable Private Layers |
| Zero-Knowledge KYC | Identity-Less Compliance | Regulatory Friction Reduction |

Systemic Convergence
The distinction between private and transparent blockchains will fade as privacy becomes a standard feature of all high-performance networks. Institutional demand for confidentiality will drive the adoption of private validation across all asset classes, including tokenized real-world assets and sovereign digital currencies. The final state of the market will be one where privacy is the default, and transparency is a selective, user-controlled choice.

Glossary

Zk-Snarks

Hardware Accelerated Proving

Recursive Starks

Proprietary Strategy Protection

Jurisdictional Compliance

Zk-Starks

Private Transaction Validation

Polynomial Commitments

Stealth Addresses