Cryptographic Identity of Private Ballots
Transparent ledgers create a structural paradox where the absolute visibility required for trust destroys the privacy required for authentic human expression. Zero-Knowledge Voting resolves this tension by utilizing non-interactive proofs to decouple the identity of a participant from the content of their choice. In the context of decentralized finance, this system serves as a shield against the predatory observation of governance signals, preventing market actors from front-running protocol changes or retaliating against specific stakeholders.
The validity of each ballot is mathematically verified through a circuit that confirms the voter possesses a valid stake and has followed the protocol rules, yet the specific data points remain hidden from the public record.
Zero-Knowledge Voting establishes a mathematical guarantee that a collective result is accurate without exposing the individual data points that comprise the total.
The systemic relevance of Zero-Knowledge Voting extends to the stabilization of market microstructure. When large-scale treasury movements or parameter shifts are decided through public voting, the resulting information leakage triggers reflexive volatility as high-frequency algorithms react to the perceived intent of major holders. By masking these signals, Zero-Knowledge Voting reduces the information asymmetry that often favors automated agents over long-term participants.
This cryptographic insulation allows for a more stable transition between protocol states, as the market only reacts to the finalized outcome rather than the speculative noise of the voting process itself.

Historical Necessity of Shielded Consensus
The drive toward private consensus mechanisms began when early blockchain participants realized that radical transparency is an adversarial environment. In the early days of decentralized governance, every vote was a public broadcast of a user’s wallet balance and their political alignment. This created a fertile ground for bribery and coercion, as malicious actors could easily verify whether a “bought” vote was actually cast.
The historical shift toward Zero-Knowledge Voting was a direct response to these governance attacks, drawing on the foundational work of the cypherpunks who argued that privacy is a prerequisite for a free society. As decentralized organizations began managing billions in assets, the stakes of governance shifted from social experimentation to high-stakes financial engineering. The need for a digital secret ballot became a survival requirement for protocols that wished to avoid capture by centralized entities or aggressive hedge funds.
The adoption of Zero-Knowledge Voting represents a maturation of the space, moving away from the naive transparency of early ledgers toward a more sophisticated architecture that respects the strategic value of information. This progression mirrors the development of modern financial markets, where dark pools and shielded orders are used to execute large trades without causing massive price dislocations.

Structural Mechanics of Proof Circuits
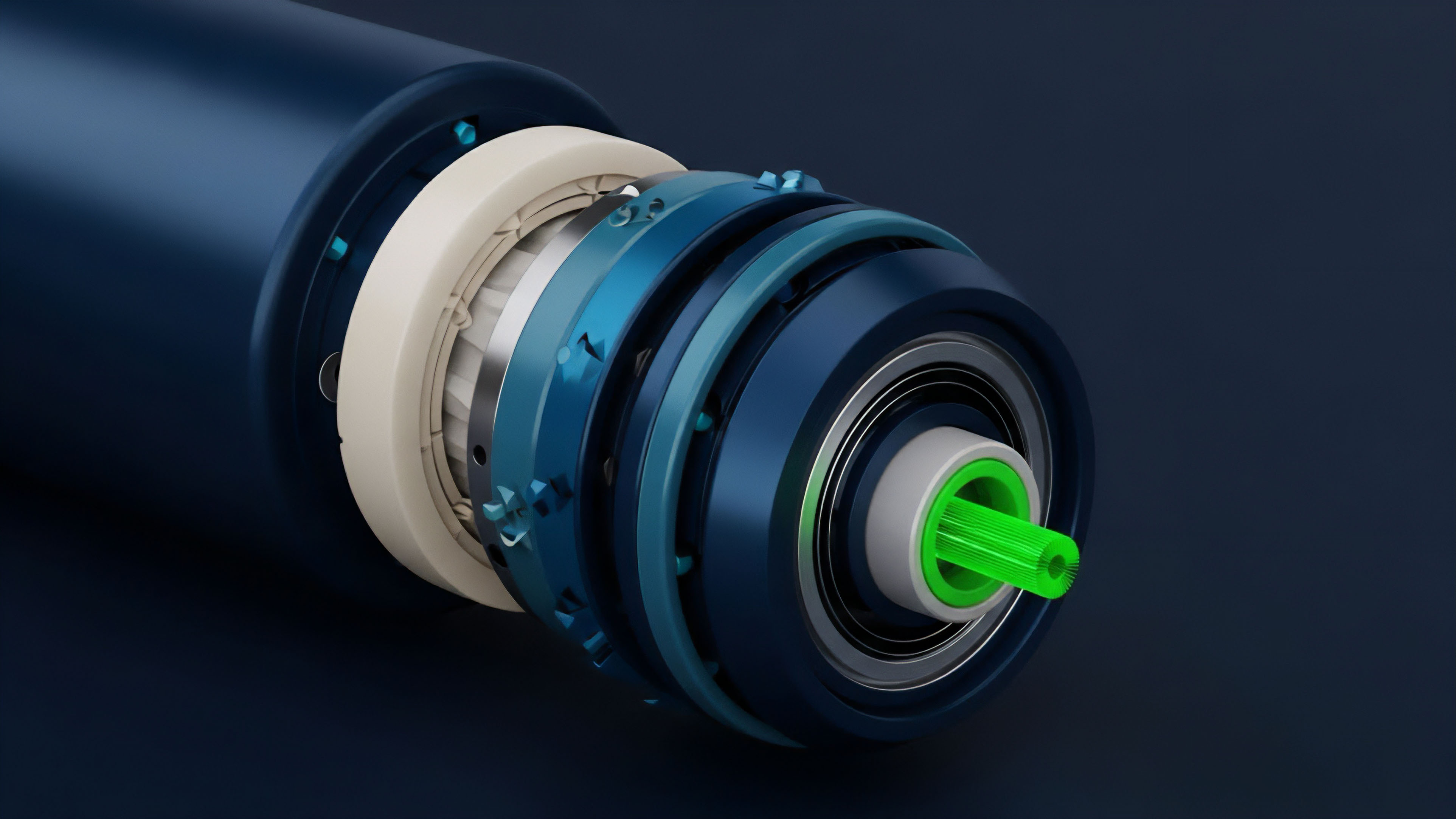
The architecture of Zero-Knowledge Voting is built upon arithmetic circuits that translate logical statements into polynomial equations. These circuits function as the gatekeepers of the system, ensuring that only authorized participants can submit a ballot.
A participant generates a proof of membership ⎊ often using a Merkle tree ⎊ to show they are part of the eligible set of voters. This proof is then combined with a nullifier, which is a unique cryptographic marker that prevents double-voting. The nullifier is derived from the user’s secret key and the specific voting event, ensuring it cannot be linked back to the user’s identity across different ballots.
| Structural Component | Functional Role |
|---|---|
| Arithmetic Circuit | Defines the logical constraints that a vote must satisfy to be considered valid by the protocol. |
| Nullifier Hash | Acts as a single-use token that marks a vote as cast without revealing the identity of the voter. |
| Polynomial Commitment | Secures the vote value in a compressed form that can be verified against the circuit logic. |
The complexity of these circuits mirrors the biological pathways of signal transmission, where a specific input must trigger a precise response without exposing the internal state of the neuron. In Zero-Knowledge Voting, the proof acts as the signal, carrying only the minimum amount of information necessary to update the state of the governance contract. This efficiency is vital for maintaining the scalability of the network, as the cost of verifying a proof must remain low enough for decentralized validators to process.
The use of nullifiers ensures that the integrity of the one-voter-one-vote principle is maintained without creating a traceable link between the individual and the ledger.
By applying quantitative modeling to these circuits, developers can estimate the probability of a collision or a failure in the proof generation process. The security of Zero-Knowledge Voting relies on the hardness of specific mathematical problems, such as the discrete logarithm problem or the security of elliptic curves. As the computational power available to adversaries increases, the parameters of these circuits must be adjusted to maintain the same level of protection, a process that requires constant vigilance and technical expertise.

Current Method of Discrete Participation
Modern implementations of Zero-Knowledge Voting often utilize a coordinator-based system to manage the tallying process.
This method involves participants sending encrypted votes to a central or distributed set of processors who aggregate the data and produce a final proof of the result. While this introduces a point of coordination, the integrity of the result is still cryptographically guaranteed, as the coordinator cannot alter the votes without breaking the proof logic.
- Succinct Non-Interactive Proofs: These allow for the rapid verification of large batches of votes, reducing the gas costs associated with on-chain governance.
- Anti-Collusion Infrastructure: This specific structure prevents voters from proving how they voted to a third party, effectively neutralizing the market for vote-buying.
- Recursive Proof Aggregation: This technique allows multiple proofs to be folded into a single proof, significantly increasing the throughput of the voting system.
- Stealth Address Integration: This method obscures the destination of governance rewards, ensuring that participation does not inadvertently reveal the user’s financial position.
The application of Zero-Knowledge Voting in the options market allows for the private adjustment of risk parameters. For instance, a decentralized options vault might use shielded voting to decide on the volatility surface or the strike price intervals for its next epoch. By keeping these decisions private until they are finalized, the vault prevents predatory traders from positioning themselves against the vault’s future liquidity.
This strategic use of privacy enhances the capital efficiency of the protocol and protects the returns of the liquidity providers.

Historical Progression of Proof Systems
The transition from early private voting experiments to the current generation of Zero-Knowledge Voting protocols has been defined by a relentless focus on removing trusted setup requirements. Early systems required a “ceremony” where a group of individuals generated the initial parameters of the system. If these individuals conspired, they could potentially create fake proofs.
The shift toward transparent and universal setups has eliminated this systemic risk, allowing for a more robust and permissionless governance model. This progression has also seen a dramatic reduction in the size of the proofs and the time required to generate them, making Zero-Knowledge Voting accessible to users with standard hardware. The current state of the art involves recursive SNARKs and STARKs, which provide the highest level of security and scalability.
This long period of technical refinement has moved the concept from a theoretical curiosity to a basal requirement for any protocol that values long-term stability and resistance to external manipulation. The accumulation of these technical improvements has created a environment where private governance is no longer a luxury but a standard expectation for decentralized financial systems.
| System Generation | Setup Type | Proof Size |
|---|---|---|
| First Generation | Trusted Ceremony | Large / Linear |
| Second Generation | Universal Setup | Succinct / Constant |
| Third Generation | Transparent / No Setup | Logarithmic / Recursive |
The removal of trusted setups has shifted the security of private voting from human trust to mathematical certainty.

Future Trajectory of Governance Privacy
The integration of Zero-Knowledge Voting into the global financial fabric will likely involve the use of multi-party computation and fully homomorphic encryption. These technologies will eventually eliminate the need for coordinators, allowing for a truly decentralized and private tallying process. This will enable a new class of “dark governance” protocols where the entire state of a DAO remains hidden, only revealing the outcomes of specific actions when they interact with the public market.

Synthesis of Divergence
The gap between public governance and shielded systems creates a divide in market efficiency. Public systems are prone to the “tragedy of the transparent,” where the fear of social or financial reprisal leads to suboptimal decision-making. Shielded systems foster authentic preference expression but require more sophisticated auditing tools to ensure that the proof circuits themselves have not been compromised.
The critical pivot point for the industry will be the standardization of these proof circuits to allow for cross-protocol verification.

Novel Conjecture
The widespread adoption of Zero-Knowledge Voting will lead to a “governance premium” for tokens that offer shielded participation. Investors will value the ability to influence protocol direction without exposing their strategic intent, leading to a decoupling of token price from public voting activity. This will create a more stable long-term holding pattern for governance assets.

Instrument of Agency
A design for a Shielded Liquidity Provision Protocol. This system would allow liquidity providers to vote on dynamic fee adjustments and collateralization ratios using Zero-Knowledge Voting. The results would be executed by an automated market maker only after a randomized delay period.
This delay, combined with the privacy of the vote, ensures that high-frequency trading bots cannot front-run the changes in fee structures, thereby preserving the yield for the liquidity providers and maintaining the stability of the pool during periods of high volatility.
Shielded governance protocols act as a buffer against market manipulation by decoupling the decision-making process from immediate public observation.
Glossary

On-Chain Privacy

Adversarial Environments

Financial Engineering

Succinct Verification

Off-Chain Computation
Information Asymmetry
Systems Risk
Arithmetic Circuits

Decentralized Autonomous Organizations