Essence
Financial privacy within decentralized derivatives markets represents a fundamental architectural challenge to the prevailing design ethos of public blockchains. The current paradigm, where every transaction, collateral position, and liquidation threshold is broadcast to a global audience, creates a market structure fundamentally incompatible with institutional-grade trading strategies. This radical transparency, initially conceived as a mechanism for trustless verification, becomes a severe vulnerability when applied to complex financial instruments like options.
A trader’s strategic intent, portfolio composition, and even their risk management decisions are exposed to adversaries, creating an environment ripe for predatory behavior. This vulnerability is particularly acute in options trading, where the visibility of large open positions can allow sophisticated actors to anticipate market movements and execute front-running strategies. The very act of placing a large order or adjusting margin can signal future intent, enabling a “sandwich attack” where an attacker places orders before and after the victim’s transaction to extract value.
The concept of financial privacy in this context extends beyond a simple desire for anonymity; it is a prerequisite for market efficiency and fairness. Without it, the market reverts to a less sophisticated, less resilient state, where only those willing to accept significant information leakage can participate in size.
Financial privacy transforms a market from a transparent, adversarial environment into a robust system where strategic information is protected.
The goal is to move beyond the current state where every participant operates in a high-stakes, open-book game. True financial privacy allows for the separation of a trader’s identity from their actions, enabling strategic decision-making without revealing their hand to the entire market. This architectural shift is essential for attracting large-scale capital, which demands a level of confidentiality to prevent its strategies from being reverse-engineered or exploited.

Origin
The necessity for financial privacy in decentralized finance arose directly from the design constraints of first-generation blockchains. Early protocols prioritized data availability and consensus integrity above all else, making every state transition visible to all participants. The initial focus of privacy research centered on simple value transfer, giving rise to concepts like CoinJoin and later, fully private blockchains like Monero and Zcash.
These solutions addressed basic transaction confidentiality but lacked the expressiveness required for complex financial logic. The problem intensified with the rise of decentralized options and lending protocols. When a user deposits collateral to write an option, the public ledger reveals not only the amount of collateral but also the specific terms of the derivative contract.
This level of exposure created an information asymmetry where sophisticated on-chain analysts could track the entire portfolio of a large trader. This led to the realization that privacy for complex financial instruments requires more than just hiding the transaction; it requires hiding the state changes and calculations associated with the derivative itself. The theoretical foundation for solving this problem emerged from advancements in Zero-Knowledge Proofs (ZKPs).
ZKPs allow a prover to convince a verifier that a statement is true without revealing any information about the statement beyond its truthfulness. While initially computationally expensive, innovations like zk-SNARKs and zk-STARKs began to make these proofs practical for on-chain verification. This technical breakthrough provided the necessary primitive to separate a trader’s strategic information from the verification process required for a trustless system.

Theory
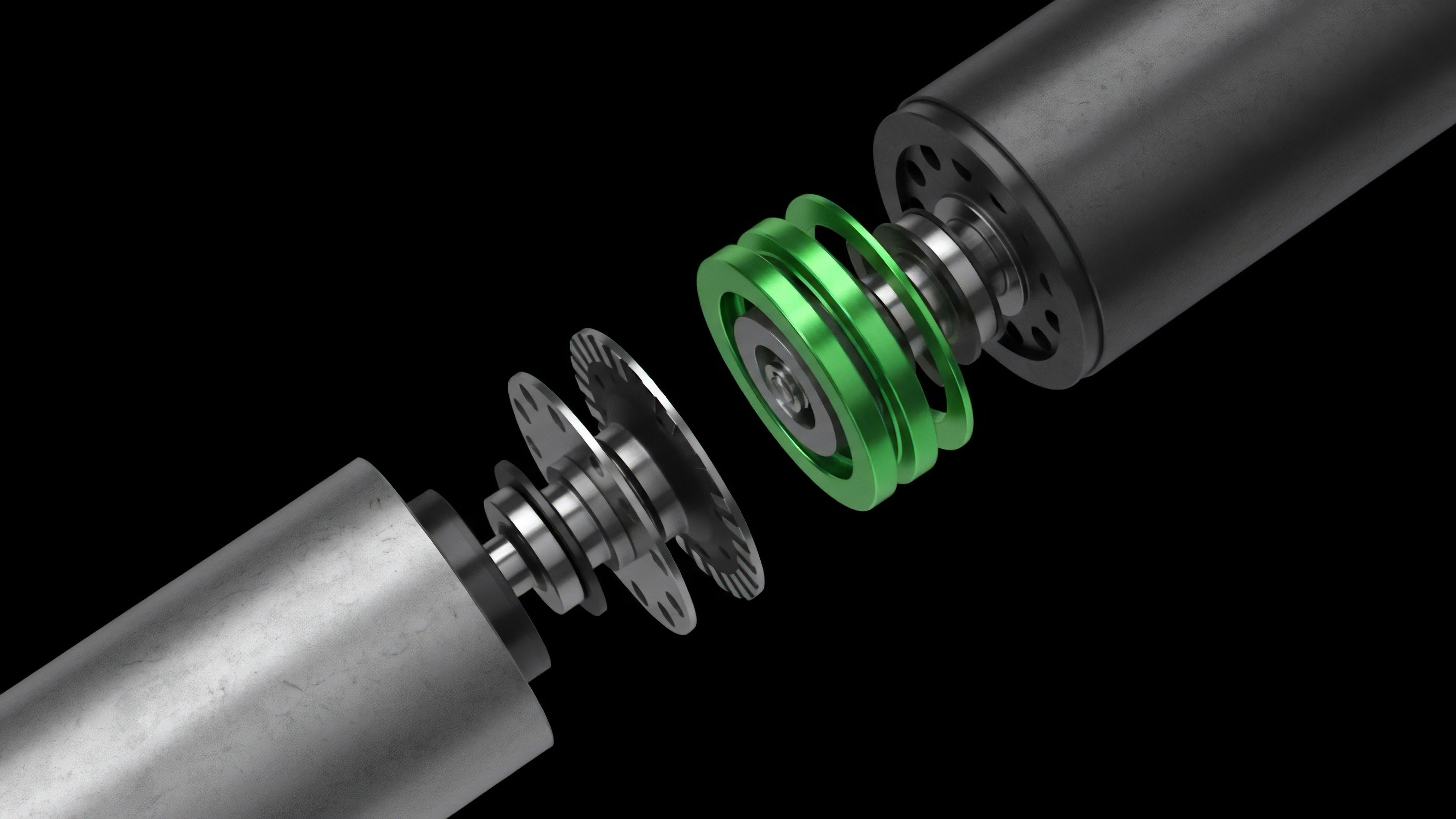
The theoretical underpinnings of financial privacy for options rely heavily on cryptographic primitives that enable computation over encrypted data. The primary goal is to maintain the verifiability required for trustless settlement while simultaneously obscuring the underlying inputs and state changes. This creates a challenging trade-off between computational overhead and the level of confidentiality achieved.

Zero-Knowledge Proofs and Market Integrity
Zero-Knowledge Proofs are the core mechanism for achieving confidential transactions in derivatives. A ZKP allows a participant to prove to a smart contract that they meet a specific condition ⎊ such as having sufficient collateral to cover a written option ⎊ without revealing the exact amount of collateral held. This protects against a critical market vulnerability: the public knowledge of a large trader’s margin health.
If an adversary knows a specific trader is close to liquidation, they can manipulate the underlying asset price to force a margin call, profiting from the liquidation event. The application of ZKPs to options requires a careful design of the circuit. The circuit must verify several conditions simultaneously:
- The participant holds the necessary collateral in a private state.
- The option contract parameters (strike price, expiry) are valid according to the protocol rules.
- The participant’s collateral balance remains above the required margin threshold after writing the option.
The proof generation process for these complex calculations introduces significant computational overhead. This is where the choice between different ZKP types becomes critical.
| Mechanism | Description | Trade-off |
| zk-SNARKs | Zero-knowledge proofs with small proof size and quick verification time, requiring a trusted setup. | High initial setup complexity; lower on-chain cost per verification. |
| zk-STARKs | Zero-knowledge proofs with larger proof size and no trusted setup, relying on collision-resistant hashes. | Higher on-chain verification cost; enhanced security and transparency in setup. |
| Secure Multi-Party Computation (MPC) | Multiple parties jointly compute a function over their inputs without revealing their inputs to each other. | Requires multiple active participants; less efficient for large, open markets. |

The Problem of Information Asymmetry
The core challenge in designing private derivatives markets is not technical alone; it is a problem of behavioral game theory. In traditional finance, information asymmetry is managed by regulation and privileged access. In decentralized finance, the open-book nature of the ledger transforms this asymmetry into a systemic vulnerability.
The public ledger, intended to create a level playing field, paradoxically enables sophisticated actors with automated bots to exploit less informed participants. The privacy solutions must therefore function as a form of “digital regulation,” ensuring that no participant can gain an unfair advantage simply by observing the internal state of another participant’s portfolio. The challenge is in building systems that can prevent this information leakage without sacrificing the trustless nature of the verification process.
Approach
Current approaches to implementing financial privacy in crypto options focus on three primary architectural patterns: Layer 2 rollups, specific privacy-preserving smart contracts, and hybrid approaches utilizing both on-chain and off-chain computation. The design choice dictates the balance between privacy, cost, and liquidity.

Layer 2 Solutions for Confidentiality
The most prominent approach involves building derivatives protocols on top of a zero-knowledge Layer 2 rollup. In this architecture, the state of all derivative positions and collateral is managed within the rollup, where only cryptographic proofs of state transitions are posted to the mainnet. The underlying data remains hidden from the public.
This approach offers significant benefits for market microstructure:
- Order Book Confidentiality: Orders can be submitted to a private order book on the rollup, preventing front-running and allowing market makers to operate with strategic confidence.
- Position Secrecy: A trader’s entire portfolio of option positions, including their specific margin requirements and liquidation levels, is hidden from public view.
- Cost Efficiency: By bundling many transactions into a single proof, the computational cost of privacy is amortized across all participants on the Layer 2.

Hybrid Privacy Models
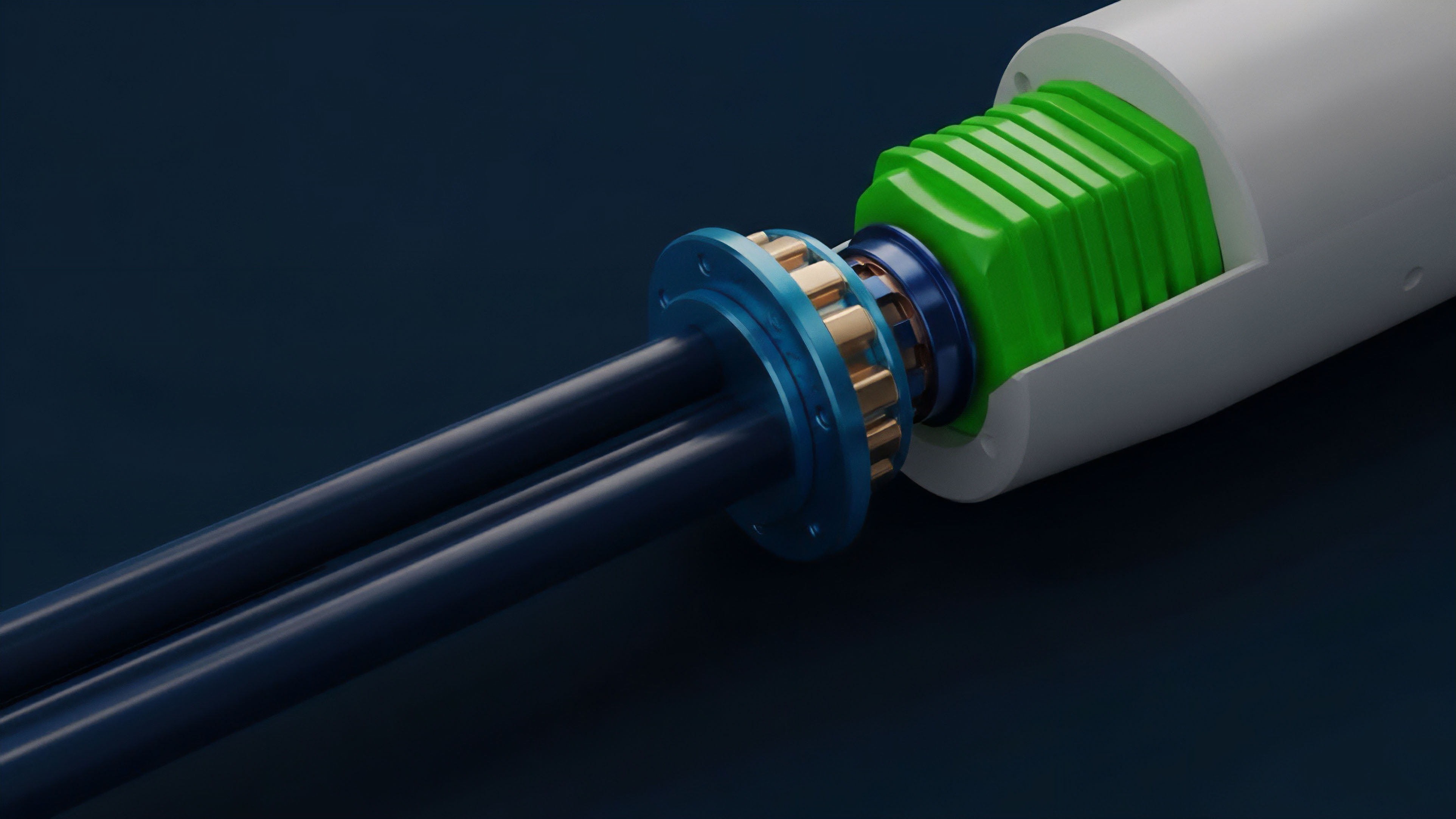
Some protocols adopt a hybrid model, using Homomorphic Encryption or Trusted Execution Environments (TEEs) to handle specific parts of the calculation. Homomorphic encryption allows computations to be performed on encrypted data without decrypting it first. A TEE, such as Intel SGX, creates a secure, isolated environment where data can be processed privately.
| Method | Description | Application in Options |
| Homomorphic Encryption | Allows calculation on encrypted data; result remains encrypted. | Pricing models and risk calculations on private inputs; complex, high overhead. |
| Trusted Execution Environments (TEEs) | Hardware-enforced secure area for code execution; data processed inside remains confidential. | Running private order matching engines; relies on hardware trust assumptions. |
| ZK-Rollups | Bundles transactions and verifies state transitions using ZKPs; data is kept off-chain. | Scalable and comprehensive privacy for an entire options market. |
The strategic choice between these approaches depends on the specific risk model of the derivative protocol. For a protocol that requires frequent, high-speed calculations for margin calls and liquidations, a TEE or ZK-rollup is more suitable. For a protocol focused on long-term, static positions, a less computationally intensive approach might suffice.
Evolution
The evolution of financial privacy in derivatives has moved from basic transaction mixing to complex state-level confidentiality, driven primarily by the need for market efficiency and the looming threat of regulatory scrutiny. The initial focus was on creating a black box where transactions simply disappeared from public view. This model, however, proved insufficient for complex financial instruments, where the interaction between different positions and collateral pools must be verifiable for system health.
The current stage of evolution focuses on selective disclosure and compliance-friendly privacy. Protocols are moving away from absolute anonymity toward a model where privacy is a default setting, but specific data can be disclosed to regulators or auditors under specific, pre-defined conditions. This addresses the significant regulatory friction associated with privacy tools.
Regulators are concerned that private transactions facilitate money laundering and sanctions evasion.
The future of financial privacy in derivatives hinges on balancing the need for market efficiency with the imperative of regulatory compliance.
This evolution requires a shift in technical design. Protocols are exploring mechanisms where a user’s private state can be verified by a third party (a regulator or auditor) without revealing the state to the public. This might involve generating specific, limited-scope proofs for compliance purposes.
The market is also seeing a move toward MEV-resistant designs where privacy is baked into the protocol’s core logic to prevent front-running, rather than being an optional add-on. The challenge is in building systems that can prevent this information leakage without sacrificing the trustless nature of the verification process.

Horizon
The future trajectory for financial privacy in crypto options points toward a world where privacy is not a feature but a fundamental layer of the market’s infrastructure.
This requires the development of new primitives that allow for fully private, yet verifiable, computation. The goal is to create privacy-preserving market design where all aspects of trading ⎊ from order submission to liquidation ⎊ are conducted without revealing strategic information to external observers.

Next Generation Market Architecture
The next phase of development will see the rise of private order books where a matching engine can process orders without revealing the details of individual bids and asks to the public. This requires advancements in fully homomorphic encryption or specialized hardware acceleration for ZKPs. The ideal architecture would allow a market maker to submit a complex options quote, knowing that their strategic pricing model cannot be reverse-engineered by competitors observing the public ledger.
Another critical area is the integration of privacy into cross-chain derivatives. As options markets fragment across multiple blockchains, privacy solutions must be able to verify collateral and positions across different environments without requiring a centralized third party. This involves developing interoperability standards for ZKPs, allowing a proof generated on one chain to be verified on another.
The long-term vision involves a shift in how market participants view risk. In a fully private environment, risk models can move beyond simple, publicly verifiable collateral ratios to more complex, strategic calculations. This enables more sophisticated derivative products and capital efficiency.
The key challenge lies in making these systems computationally efficient enough for real-time market operations.
| Current State | Future State (Horizon) |
| Publicly visible order books and collateral. | Encrypted order books with private matching engines. |
| Privacy as an add-on (e.g. mixers). | Privacy as a core architectural layer (e.g. ZK-rollups). |
| Vulnerability to front-running and MEV. | MEV-resistant market design via confidentiality. |
| Limited institutional participation due to information leakage. | Institutional-grade markets with protected strategic positions. |
This future requires a move away from the current adversarial model to one where the protocol itself acts as a neutral arbiter, protecting all participants from information exploitation. The ultimate goal is to enable a level of financial sophistication currently restricted to traditional, centralized exchanges, but with the added benefits of decentralization and trustless verification.

Glossary

Cryptographic Solutions for Financial Privacy

Decentralized Finance Privacy

Auditable Privacy

Margin Account Privacy

Hybrid Privacy Models

Collateralization Privacy

Volatility Skew Privacy
Privacy Preserving Triggers

Governance Privacy