Essence
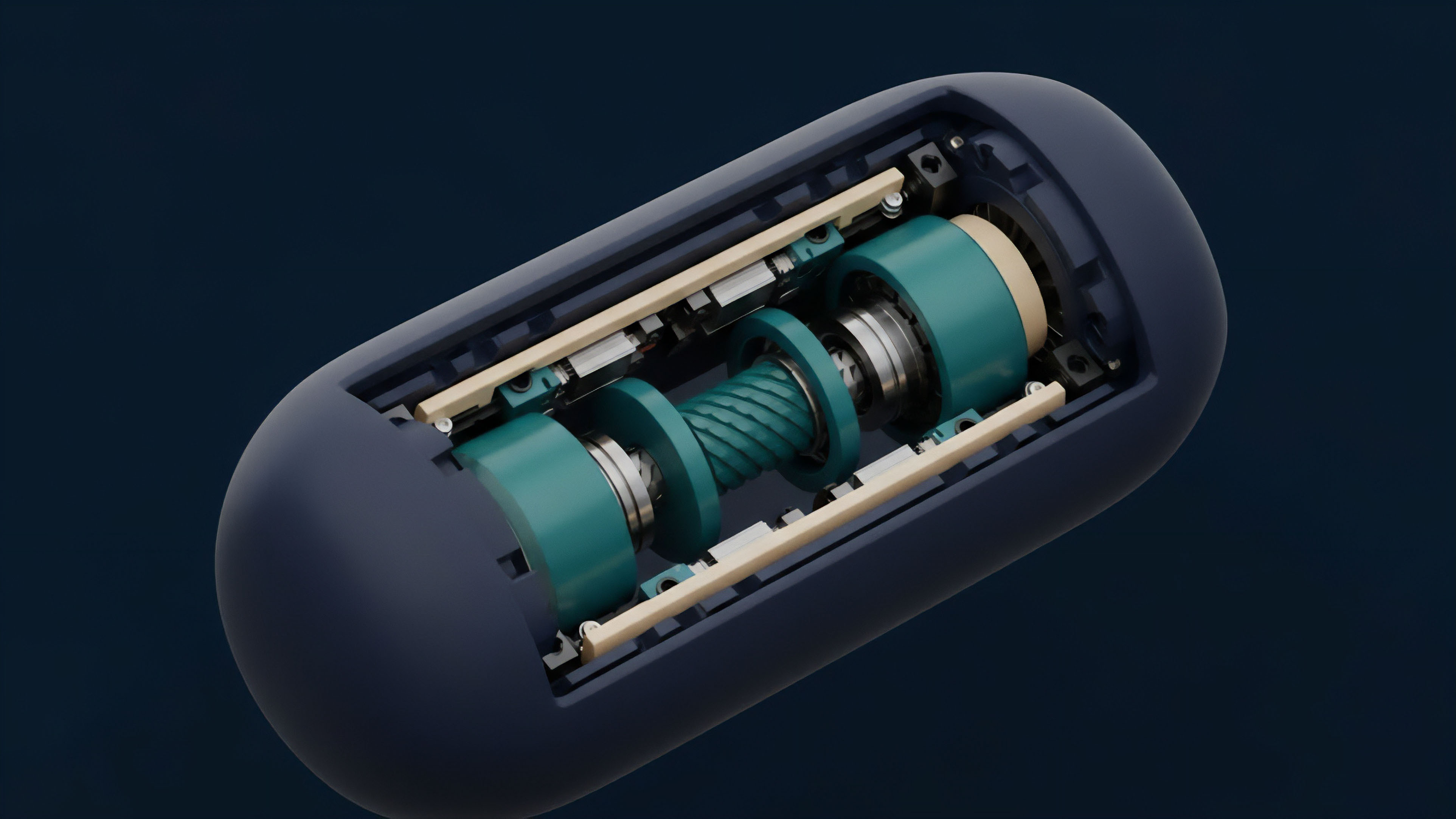
Verification costs dictate the boundaries of decentralized liquidity. Cryptographic Proof Complexity Tradeoffs represent the deliberate calibration between the computational resources required to generate a proof and the resources required to verify it. In the high-stakes environment of crypto derivatives, these tradeoffs determine whether a margin engine can operate on-chain or if it must rely on slower, off-chain settlement.
Cryptographic Proof Complexity Tradeoffs function as the governing physics of zero-knowledge systems, balancing prover overhead against verifier efficiency.
The primary tension exists between Prover Time, Proof Size, and Verification Gas Costs. A system optimized for small proof sizes often demands massive computational power from the prover, which can lead to centralization of the proving infrastructure. Conversely, reducing the prover’s burden frequently results in larger proofs that are expensive to verify on a public ledger like Ethereum.
This balance is a strategic choice rather than a technical limitation, as different financial instruments require different levels of latency and security.
- Prover Complexity determines the hardware requirements for generating valid state transitions.
- Proof Succinctness influences the bandwidth needed for data availability and cross-chain communication.
- Verification Scalability ensures that the cost of checking a proof remains constant or grows logarithmically relative to the number of transactions.
These technical decisions directly impact the Capital Efficiency of a protocol. If verification is too slow, liquidation events cannot happen in real-time, increasing the risk of systemic insolvency. The choice of a specific proving system is a commitment to a particular risk profile and operational cost structure.

Origin
The quest for verifiable computation began with the introduction of Zero-Knowledge Proofs in the mid-1980s.
Early researchers sought ways to prove the validity of a statement without revealing the underlying data. While theoretically sound, these early constructions were computationally prohibitive for practical applications. The shift toward decentralized finance necessitated a transformation of these academic concepts into production-ready systems.
The transition from interactive proofs to non-interactive succinct arguments enabled the settlement of complex financial state changes on constrained ledgers.
The emergence of SNARKs (Succinct Non-Interactive Arguments of Knowledge) provided the first viable path for scaling blockchains. These systems required a Trusted Setup, a one-time ceremony to generate parameters. While SNARKs offered incredibly small proofs, the reliance on a trusted setup introduced a point of failure that many in the decentralized community found unacceptable.
This led to the development of STARKs (Scalable Transparent Arguments of Knowledge), which eliminated the trusted setup but increased proof sizes significantly.
| Proof System | Setup Type | Proof Size | Verification Speed |
|---|---|---|---|
| SNARKs (Groth16) | Trusted | Very Small | Constant |
| STARKs | Transparent | Large | Logarithmic |
| Bulletproofs | Transparent | Medium | Linear |
This historical progression reflects a move toward Transparency and Quantum Resistance. As the value secured by these proofs grew, the industry moved away from systems with hidden parameters toward those based on hash functions, which are easier to audit and harder to compromise.

Theory
Mathematical constraints define the efficiency of any cryptographic system. Cryptographic Proof Complexity Tradeoffs are rooted in the relationship between the complexity of the circuit being proven and the resulting proof metrics.
A circuit represents the financial logic ⎊ such as an option’s Black-Scholes calculation or a Perpetual Swap funding rate adjustment ⎊ translated into a series of polynomial constraints.
Arithmetic Circuit Complexity
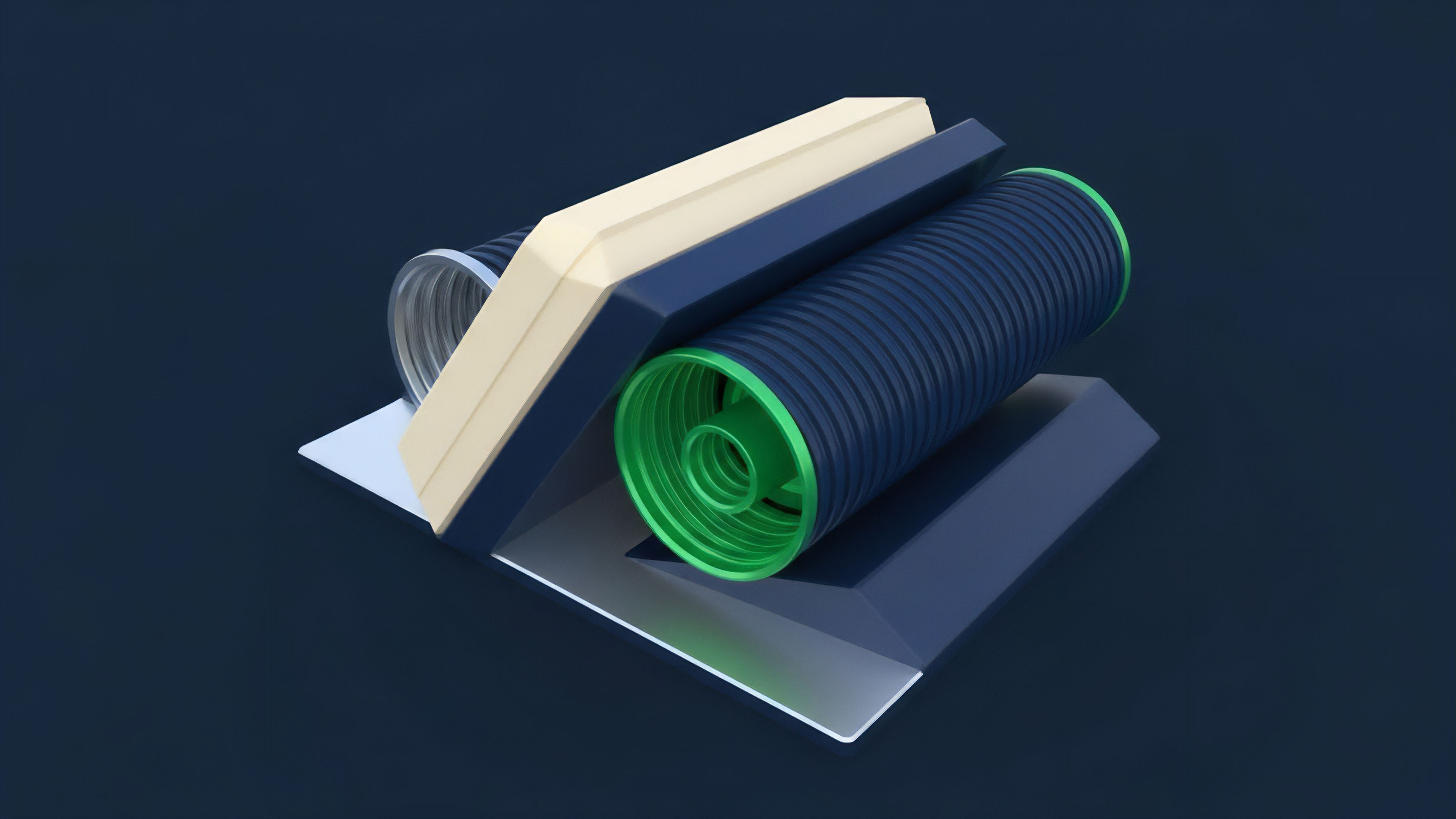
The size of the circuit, measured in Gates, directly scales the prover’s workload. For complex derivatives, the number of constraints can reach into the millions. Provers must perform Large Number Theory operations, specifically Multi-Scalar Multiplications (MSM) and Fast Fourier Transforms (FFT).
These operations are the primary bottlenecks in the proving pipeline.

Polynomial Commitments
Different proving systems utilize different Polynomial Commitment Schemes (PCS) to anchor the circuit’s logic. This choice is the most significant driver of the tradeoff. KZG Commitments, used in many SNARKs, offer the smallest proofs but require pairing-friendly elliptic curves.
FRI (Fast Reed-Solomon Interactive Oracle Proof of Proximity), used in STARKs, relies on hash functions, providing transparency at the cost of larger data footprints.
Financial settlement integrity relies on the mathematical impossibility of generating a valid proof for an invalid state transition.
The second law of thermodynamics suggests that entropy always increases; similarly, in proof systems, computational work cannot be destroyed, only shifted. If the verifier’s job is made easier, the prover’s job must become harder. This is the Conservation of Computational Work.
In a decentralized market, shifting this work to the prover allows the verifier (the blockchain) to scale, but it creates a market for Proving Power where only those with specialized hardware can participate.
| Metric | SNARK Optimization | STARK Optimization |
|---|---|---|
| Security Assumption | Elliptic Curves | Hash Functions |
| Prover Memory | High | Moderate |
| Verifier Gas | ~200k-300k | ~1M-5M |
| Quantum Security | No | Yes |
Approach
Current implementations of Cryptographic Proof Complexity Tradeoffs focus on Recursive Proof Composition. Instead of proving a thousand transactions individually, a system can prove the validity of a proof that proves those transactions. This “proof of proofs” approach allows for nearly infinite scaling by compressing massive amounts of financial activity into a single, verifiable constant.

Hardware Acceleration
To mitigate the high prover costs, protocols are increasingly turning to FPGA and ASIC hardware. This mirrors the evolution of Bitcoin mining. By offloading MSM and FFT operations to specialized silicon, provers can reduce latency, making ZK-based derivatives competitive with centralized exchanges in terms of execution speed.
- Custom Gates allow for the optimization of specific financial functions like Sigmoid or Logarithm within the circuit.
- Look-up Tables replace complex calculations with pre-computed values, significantly reducing the gate count for operations like range checks.
- Batch Verification enables the network to process multiple proofs in a single transaction, spreading the gas cost across many users.

Data Availability Modes
Protocols also experiment with Validiums and Volitions. A Validium keeps the transaction data off-chain while posting only the proof to the mainnet. This maximizes privacy and minimizes cost but introduces a dependency on an external data provider.
A Volition allows users to choose between on-chain and off-chain data on a per-transaction basis, providing a granular way to manage the Cost-Security Tradeoff.

Evolution
The transition from Monolithic to Modular architectures has redefined how we view these tradeoffs. Initially, a single blockchain handled execution, settlement, and data availability. Now, specialized layers use cryptographic proofs to communicate state changes between disparate environments.
This modularity allows for the “outsourcing” of complexity.
The Shift to PlonKish Arithmetization
Modern systems have largely converged on PlonK and its variants. This approach uses a flexible “alphabet” for building circuits, allowing developers to define Custom Gates that are specifically tailored for financial logic. This has drastically reduced the prover overhead compared to the older R1CS (Rank-1 Constraint System) standard.
The evolution toward universal and updateable setups has removed the primary barrier to entry for secure SNARK deployments.
We have seen the rise of Halo2 and other “setup-less” SNARKs that use recursive techniques to achieve transparency without the proof size explosion seen in STARKs. This represents a middle ground that satisfies both the need for Low Gas Costs and the desire for Decentralized Trust. The competitive pressure between these technologies has forced a rapid optimization of the entire stack, from the underlying math to the high-level programming languages used to write the circuits.

Horizon
The future of Cryptographic Proof Complexity Tradeoffs lies in Fully Homomorphic Encryption (FHE) and Multi-Party Computation (MPC) integration.
While ZK proofs verify the validity of a computation, FHE allows for computation on encrypted data itself. Combining these will enable a new class of Private Derivatives where the entire order book and margin state remain hidden even from the validators, yet their integrity is mathematically guaranteed.

Proof as a Service
A specialized market for Decentralized Prover Networks will likely emerge. Instead of every protocol running its own proving infrastructure, they will outsource this to a global pool of hardware. This will commoditize proving power, further reducing the costs for end-users and enabling Micro-Options and other high-frequency instruments that are currently too expensive to secure with proofs.
| Future Milestone | Impact on Options | Technical Requirement |
|---|---|---|
| Real-time ZK-Greeks | Instant Risk Updates | ASIC Provers |
| Cross-Chain Atomic Settlement | Unified Liquidity | Shared Sequencers |
| Privacy-Preserving Liquidations | Reduced MEV Front-running | FHE + ZK Hybrid |
The risk of Quantum Computing remains a distant but significant factor. Protocols that have opted for STARKs or other hash-based systems are already positioned for this future. Those relying on elliptic curves will eventually face a Migration Event, requiring them to upgrade their underlying cryptographic primitives. This looming shift will drive the next decade of research into Post-Quantum Proof Complexity.

Glossary

Application Specific Integrated Circuits

Range Checks

Fast Reed-Solomon Interactive Oracle Proofs

Arithmetic Constraints

Decentralized Liquidity

Capital Efficiency

Verifier Efficiency
Prover Time Complexity
Kzg Commitments