Essence
Fully Homomorphic Encryption, or FHE, represents a cryptographic primitive that enables computation on encrypted data without first decrypting it. This capability directly addresses a fundamental conflict within decentralized finance: the tension between public verifiability and private data integrity. In traditional finance, proprietary algorithms, trading strategies, and user positions are kept confidential.
In contrast, most decentralized protocols operate on a public ledger where all data, including user balances, collateral levels, and order flow, are visible to all participants. This transparency creates a systemic vulnerability, particularly in derivatives markets, where information asymmetry allows for front-running and manipulation. FHE provides a cryptographic solution to this problem, allowing smart contracts to process sensitive financial data ⎊ such as calculating option prices, managing collateral ratios, or executing complex trading strategies ⎊ while keeping the inputs and intermediate computations hidden from all parties, including the protocol operators themselves.
FHE allows smart contracts to process sensitive financial data, such as calculating option prices and managing collateral ratios, while keeping the inputs and intermediate computations hidden.
This technology fundamentally changes the design space for decentralized derivatives. It shifts the security model from reliance on economic incentives and transparent verification to a model based on mathematical proof. By ensuring that only the outcome of a computation is revealed, and not the underlying data, FHE creates a new foundation for privacy-preserving financial applications.
This allows for the construction of sophisticated financial instruments that would otherwise be impractical in a fully transparent environment.

Origin
The theoretical groundwork for FHE began decades ago, long before the advent of blockchain technology. The concept was first proposed in 1978 by Rivest, Adleman, and Dertouzos, who recognized the potential for performing computations on encrypted data.
However, for many years, FHE remained a theoretical construct, primarily due to the immense computational cost and performance overhead associated with the proposed methods. The major breakthrough arrived in 2009 with Craig Gentry’s thesis, which presented the first construction of a fully homomorphic encryption scheme. Gentry introduced the concept of “bootstrapping,” a technique that allows for the refreshing of encrypted data (ciphertext) to remove accumulated noise, thereby enabling an unlimited number of operations.
The initial implementations of Gentry’s scheme were prohibitively slow, requiring several orders of magnitude more time for a single operation compared to unencrypted computation. This limitation meant FHE was largely confined to academic research. The subsequent decade saw significant advancements in FHE schemes, leading to different approaches optimized for specific types of calculations.
These advancements, driven by research in lattice-based cryptography, have focused on improving efficiency and reducing the size of the ciphertexts. The emergence of blockchain and decentralized finance has provided a compelling use case and renewed motivation for making FHE practical, moving it from theoretical computer science to applied cryptography.

Theory
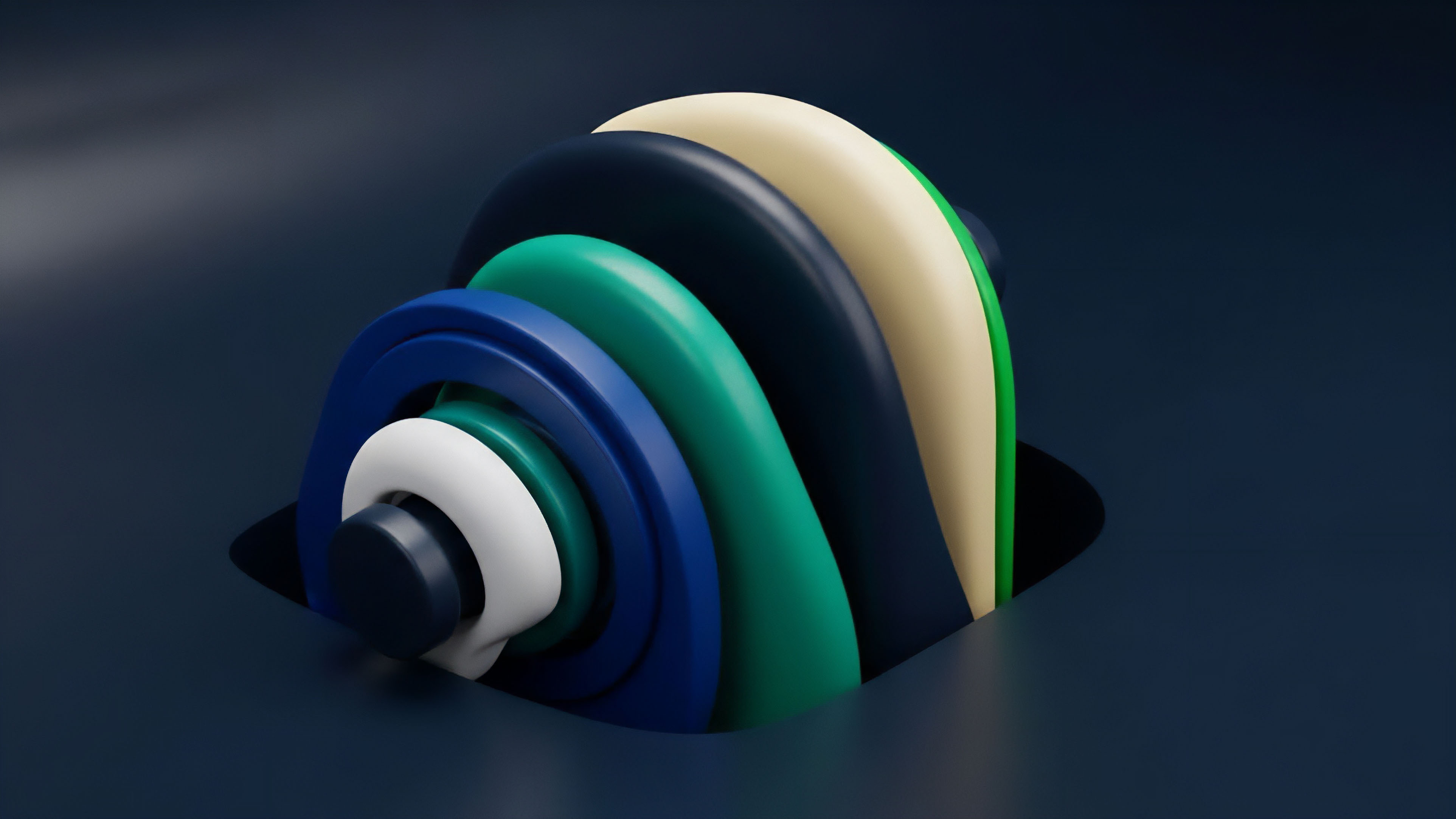
FHE’s theoretical foundation rests on the concept of noise management within lattice-based cryptography.
When an operation (addition or multiplication) is performed on encrypted data, a small amount of “noise” is introduced into the ciphertext. If too many operations are performed, this noise accumulates to a point where the ciphertext cannot be correctly decrypted, effectively corrupting the calculation. The primary challenge of FHE is managing this noise.
There are two main types of FHE schemes, each with a different approach to noise management and computation:
- Level-Based Schemes: These schemes limit the number of operations that can be performed on a ciphertext before the noise becomes too high. The “level” corresponds to the depth of the circuit (number of multiplications) that can be evaluated.
- Bootstrapping Schemes: These schemes introduce a technique to refresh the ciphertext. Bootstrapping essentially evaluates the decryption circuit homomorphically on the noisy ciphertext, producing a new ciphertext that encrypts the same value but with reduced noise. This allows for an infinite number of operations, enabling true “fully homomorphic” computation.
For financial applications, the choice of scheme depends on the required precision and type of calculation. For example, calculating option Greeks often requires high precision floating-point arithmetic, which is better suited for schemes like CKKS (Cheon-Kim-Kim-Song). However, if the calculation involves simple integer arithmetic or Boolean logic, schemes like BFV (Brakerski-Fan-Vercauteren) or TFHE (Toroidal FHE) might be more appropriate.
The complexity of the FHE circuit for calculating something like the Black-Scholes model is substantial, involving multiple multiplications and additions, which requires careful optimization to remain computationally viable.
| FHE Scheme | Best Suited For | Key Feature | Noise Management |
|---|---|---|---|
| CKKS | Floating-point arithmetic (e.g. option pricing) | Approximate calculation | Bootstrapping |
| BFV | Integer arithmetic (e.g. collateral checks) | Exact calculation | Bootstrapping |
| TFHE | Boolean circuits (e.g. access control) | Gate-by-gate evaluation | Bootstrapping |

Approach
The implementation of FHE in decentralized finance requires specialized tooling and a different approach to smart contract architecture. Current decentralized options protocols typically rely on off-chain computation oracles for pricing and risk management, which introduces a trusted third party and centralizes a key function. FHE offers a path to move these complex calculations on-chain, but the performance cost remains significant.
The primary application for FHE in derivatives markets centers on preserving privacy in key areas:
- Order Book Confidentiality: FHE can encrypt limit orders and other trading intentions. A decentralized exchange could use FHE to process encrypted orders, match them based on price, and execute the trade without revealing the full order book or specific order details to other market participants. This eliminates front-running based on order flow observation.
- Collateral and Position Privacy: In a decentralized options vault, FHE allows a user’s collateral to be managed and checked against margin requirements without revealing the exact amount of collateral or the specific option positions held by that user. The protocol only receives a boolean (true/false) result indicating whether the user meets the margin call.
- Proprietary Model Protection: Market makers often use complex, proprietary pricing models to calculate volatility skew and manage risk. FHE allows these models to be executed on-chain without revealing the intellectual property within the algorithm itself.
A significant challenge in implementing FHE for options pricing is the computational overhead. A single Black-Scholes calculation, which is trivial on a standard computer, can take seconds or even minutes when performed homomorphically, even with optimized schemes. This overhead must be carefully managed in a real-time trading environment.
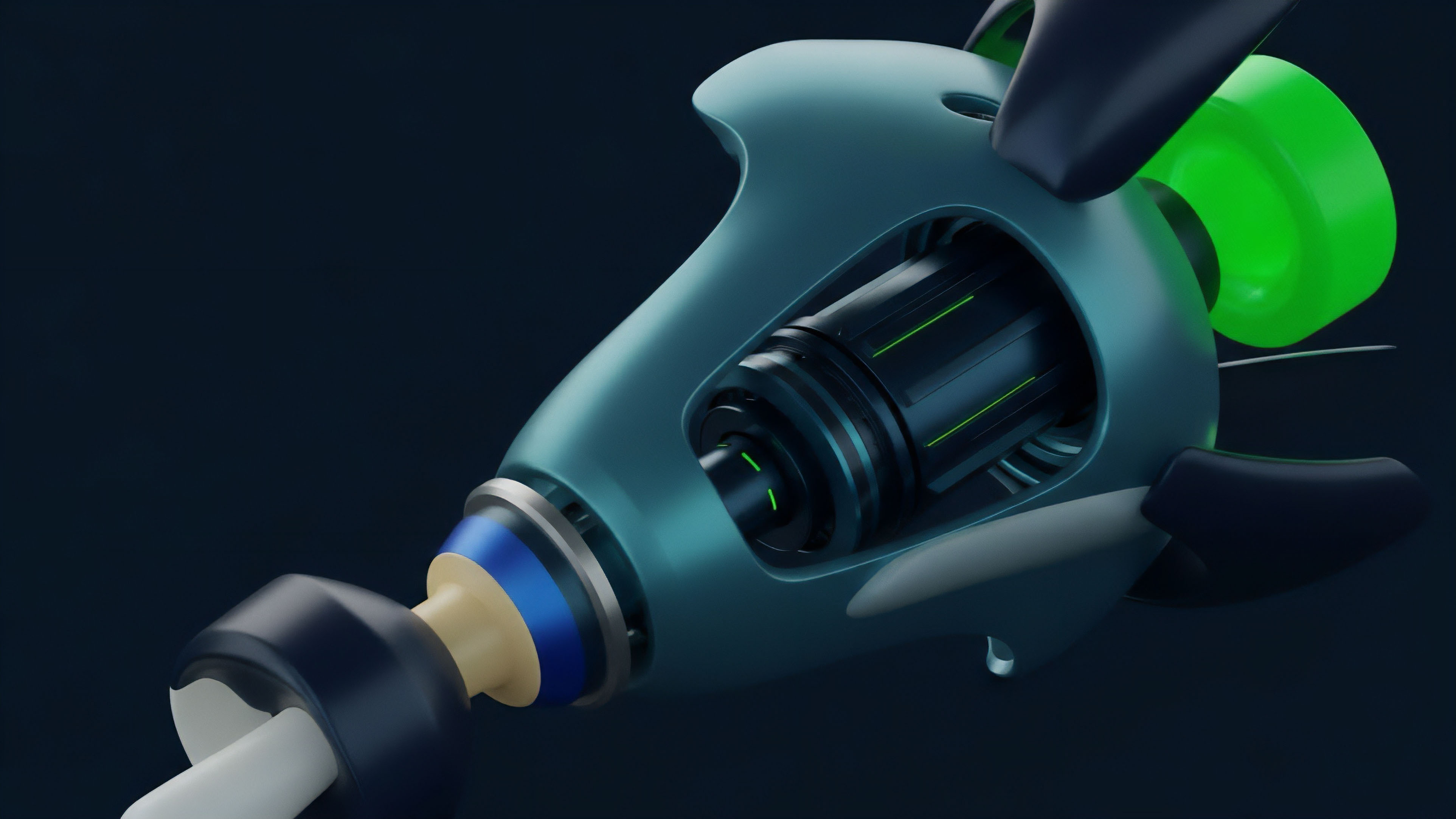
Furthermore, the FHE-enabled smart contracts require a different execution environment. The recent development of FHE-enabled virtual machines (fhEVMs) aims to standardize this process, allowing developers to write FHE-compatible code in languages like Solidity and execute it in a secure, privacy-preserving manner.

Evolution
The evolution of FHE from a theoretical curiosity to a practical tool for financial systems has been marked by a transition from general-purpose schemes to specialized, application-specific optimizations.
Early FHE research focused on proving the possibility of homomorphic computation. The next phase involved creating more efficient schemes that were still computationally intensive. The current phase focuses on optimizing these schemes for specific use cases, such as secure machine learning and decentralized finance.
In the context of decentralized derivatives, the development of FHE has moved from simple, additive-only schemes (like Paillier encryption, which is technically homomorphic but limited) to full bootstrapping schemes that support complex financial calculations. The development of fhEVMs (fully homomorphic encryption virtual machines) represents a significant leap forward in making this technology accessible to developers. These virtual machines abstract away the low-level cryptographic details, allowing developers to focus on the business logic of their smart contracts.
This shift reduces the barrier to entry for building privacy-preserving financial applications. However, the adoption of FHE introduces new systems risk. The performance overhead of FHE computations creates latency.
In a high-speed trading environment, this latency can lead to significant execution risk and slippage. The trade-off between privacy and performance is a critical design choice for any FHE-enabled protocol. Furthermore, while FHE protects data from observation, it does not prevent a user from submitting a valid, but potentially manipulative, encrypted transaction.
The game theory of FHE-enabled markets remains a subject of active research, as the ability to hide intentions changes how rational agents behave in adversarial environments.

Horizon
The future of FHE in decentralized finance is closely tied to advancements in hardware acceleration and regulatory clarity. The current computational cost of FHE means that high-frequency trading applications remain impractical on existing general-purpose hardware.
The development of specialized FHE accelerators, similar to ASICs used for Bitcoin mining, could dramatically reduce the latency and cost of homomorphic computations. These accelerators would make FHE viable for high-volume, real-time derivatives trading. From a strategic perspective, FHE opens the door to financial instruments that require confidentiality.
We could see the emergence of fully decentralized, non-custodial structured products where the underlying assets and risk parameters are hidden from the public ledger, protecting proprietary strategies. The ability to perform private calculations also extends to complex risk management frameworks. A decentralized credit protocol, for example, could calculate a user’s creditworthiness based on their encrypted financial history without ever revealing the specific data points to the protocol or other users.
- Specialized Hardware: The widespread adoption of FHE depends on the development of dedicated hardware accelerators. Without these, FHE remains too slow for most high-frequency financial applications.
- Regulatory Implications: The ability to conduct private financial transactions on a public ledger presents a challenge for regulators. The technology’s adoption will be shaped by how jurisdictions balance financial privacy with anti-money laundering and know-your-customer requirements.
- Interoperability with ZK-proofs: The combination of FHE (for computation on encrypted data) and zero-knowledge proofs (for verifying computation integrity) could create a powerful new standard for decentralized financial applications. FHE would handle the privacy, while ZK-proofs would handle the verification of correct execution.
FHE is not a panacea for all financial privacy problems, but it provides a necessary building block for creating a truly robust, censorship-resistant, and confidential financial system. The technology’s impact on decentralized derivatives will be to enable new market structures where information asymmetry is reduced by design, rather than by relying on economic incentives that can fail under stress.

Glossary
Trustless Protocols

Regulatory Clarity

Zero Knowledge Proofs

Fhevm

Fully Homomorphic Encryption Trading
Fhe Accelerators

Crypto Architecture

Verifiable Computation
State Transition Logic Encryption