
Essence
The public mempool, a core component of decentralized market infrastructure, acts as a transparent staging ground where transactions await inclusion in a block. For crypto options, this transparency introduces a fundamental vulnerability ⎊ information asymmetry. The exposure of an order to purchase or sell an option before execution allows sophisticated actors, often referred to as searchers, to anticipate market movements and execute front-running strategies.
This process, a form of Maximal Extractable Value (MEV) extraction, compromises execution quality and increases slippage for the end user. Private transactions, in this context, represent a design choice where order intent bypasses the public mempool entirely. Instead, orders are submitted directly to a trusted party, typically a block builder or a specialized relay, which then incorporates the transaction into a block without public pre-disclosure.
This architectural shift moves beyond simple privacy and addresses the core problem of price discovery in an adversarial environment. The value of an options contract is highly sensitive to the underlying asset’s price dynamics. When an actor places a large options order, they are essentially signaling a strong conviction about future price direction.
In a public mempool, this signal becomes a liability, as other actors can trade against this knowledge, forcing the original user to pay a premium for execution. The private transaction model attempts to re-align incentives by creating a secure channel where users can submit orders without broadcasting their intent to the broader market. This creates a more robust execution environment for complex derivatives strategies where information leakage is highly detrimental to the trade’s profitability.
Private transactions for options markets function as a critical layer of defense against information asymmetry, ensuring that order intent remains confidential during the execution process.

Origin
The concept of private order flow originates from traditional financial markets, where high-frequency trading firms utilize dark pools and internalization strategies to execute large orders away from public exchanges. This allows institutional investors to trade large blocks of securities without immediately impacting market prices. The transition to decentralized finance introduced the concept of MEV, which quickly became the digital equivalent of front-running.
The initial iterations of MEV extraction focused on simple arbitrage between decentralized exchanges (DEXs) and liquidations. However, as the ecosystem matured, searchers began targeting more complex instruments, including options and structured products. The specific vulnerability for options stems from the nature of their pricing models.
Options pricing is non-linear and relies heavily on volatility and time decay. The presence of a large options order in the mempool provides an opportunity for an attacker to manipulate the underlying asset price or to execute a sandwich attack on the options trade itself. The need for private transactions became apparent as protocols observed significant value leakage from their options vaults and trading venues.
The origin story of private transactions in crypto options is a direct response to this systemic flaw in public market microstructure ⎊ a necessary evolution to protect sophisticated strategies from automated value extraction.

Theory
The theoretical underpinnings of private transactions in options markets are rooted in game theory and information economics. The core issue is that public mempools create a zero-sum game between the user and the searcher.
The user’s order flow contains informational value that the searcher extracts, resulting in a negative expected value for the user. Private order flow mechanisms attempt to shift this dynamic toward a cooperative game by allowing users to sell their order flow to searchers/builders in a private auction, rather than having it stolen by public observation. The mechanism design for private transactions in options involves several key theoretical considerations:
- Information Asymmetry and Price Impact: A large options order, especially for exotic options or specific strike prices, can signal significant information. If a user wants to execute a complex options spread, a searcher observing the individual legs of the spread in the mempool can anticipate the user’s overall strategy. Private transactions prevent this leakage, allowing the user to execute the entire strategy at fair market value without being exploited by front-running.
- Auction Mechanisms and Value Capture: Private transaction systems often employ a sealed-bid auction model where searchers compete for the right to execute the order. The user receives a portion of the MEV extracted by the winning searcher, transforming a loss into a profit share. This mechanism re-aligns incentives by ensuring the value of the order flow is captured by the user, rather than dissipated to opportunistic searchers.
- Slippage Reduction and Liquidity Provision: By bypassing the public mempool, private transactions can significantly reduce slippage. In a public setting, a large order can move the price of the underlying asset, causing the options trade to execute at a less favorable price. Private order flow, especially when aggregated by large liquidity providers, allows for execution against a deeper pool of liquidity without the risk of public price impact.

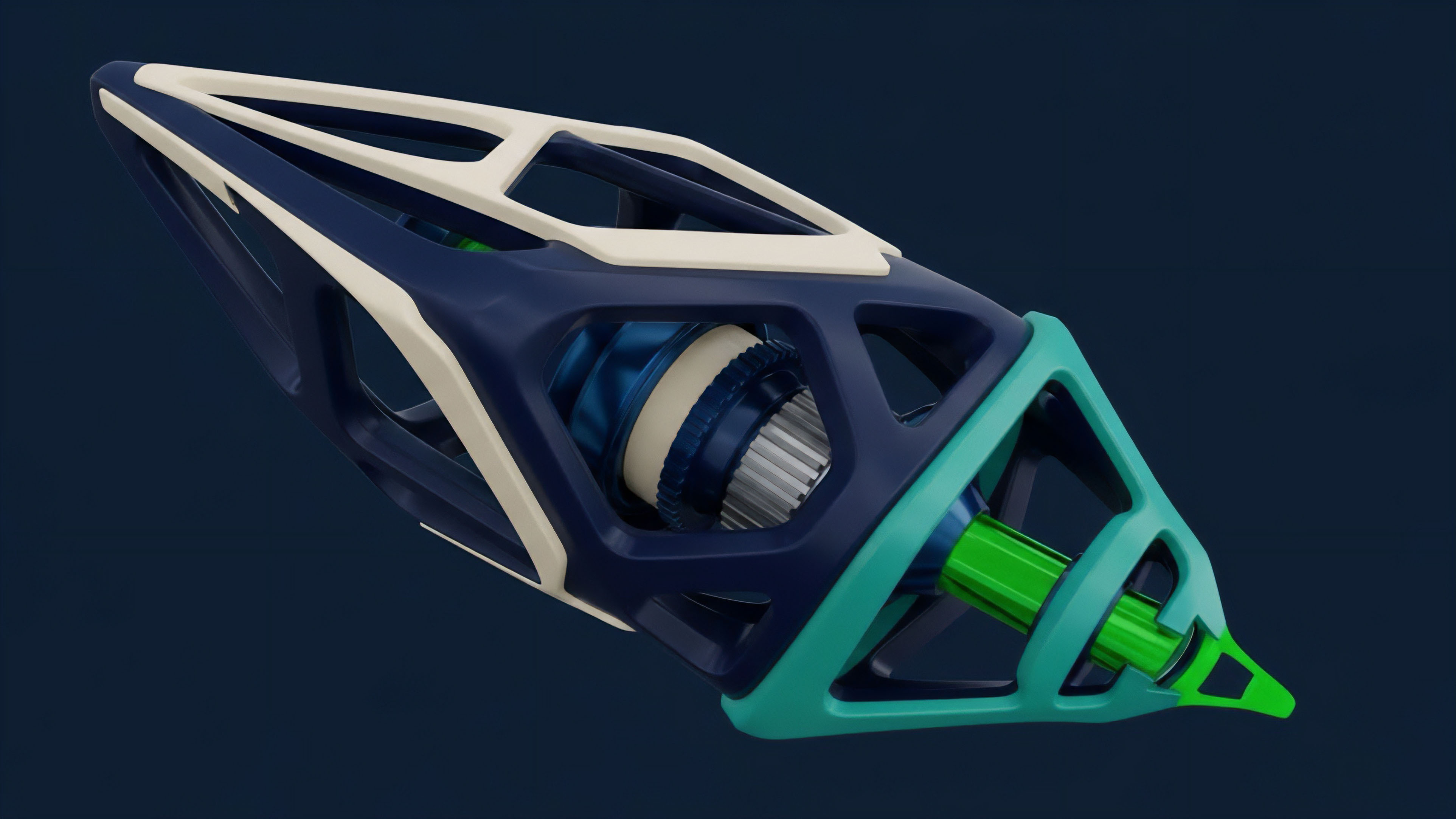
Technical Architecture and MEV Mitigation
The implementation of private transactions requires a fundamental re-architecture of order flow. Instead of broadcasting orders to the network, users submit them to specialized relays. These relays forward the order directly to block builders.
The builder then selects transactions to include in the next block, ensuring the order is executed privately and atomically. This process eliminates the time window between order broadcast and block inclusion, where MEV extraction occurs.
| Feature | Public Mempool Order Flow | Private Order Flow (MEV-Resistant) |
|---|---|---|
| Order Visibility | Publicly viewable by all network participants before confirmation. | Encrypted or directly submitted to block builder/searcher. |
| Execution Risk | High risk of front-running, sandwich attacks, and information leakage. | Reduced risk; execution guaranteed by a trusted builder or TEE. |
| Slippage Profile | Variable slippage due to public price impact and MEV extraction. | Lower slippage; execution against private liquidity pools or aggregated flow. |
| User Value Capture | Negative value capture (MEV extracted by searchers). | Positive value capture (MEV returned to user as rebate). |

Approach
The implementation of private transactions for crypto options requires a careful balancing act between privacy, trust, and decentralization. The current approach involves several distinct methods, each with its own trade-offs regarding security and efficiency. The core challenge lies in guaranteeing that the order remains private while still ensuring timely and accurate execution by the block builder.
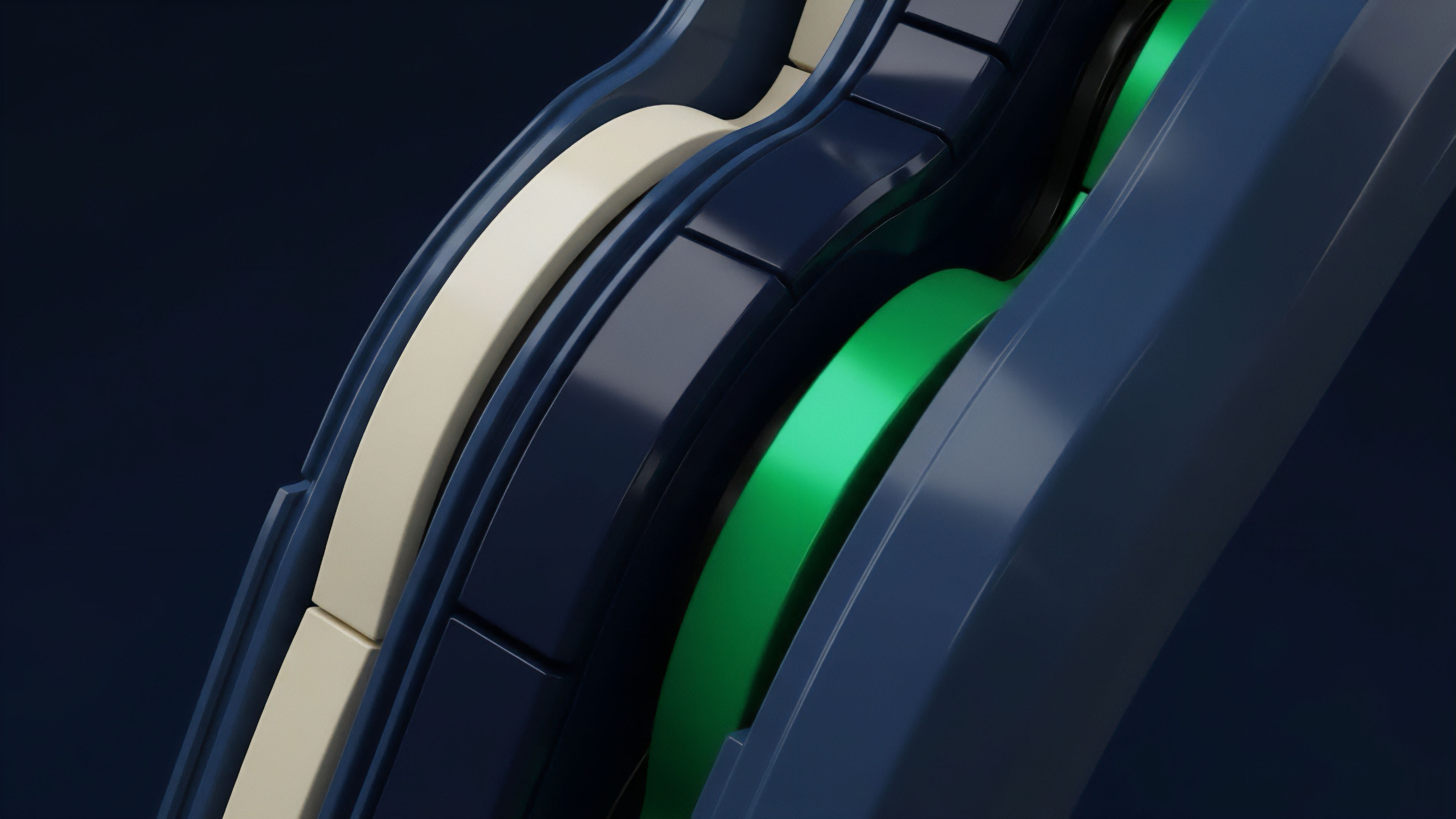
One prevalent approach utilizes Trusted Execution Environments (TEEs). A TEE is a secure area of a processor that guarantees code and data loaded inside are protected with respect to confidentiality and integrity. Orders submitted to a TEE-enabled sequencer or builder are processed within this secure enclave, ensuring that even the operator of the TEE cannot view the unencrypted order details.
This offers a high degree of privacy and prevents MEV extraction at the builder level itself. However, TEEs introduce a dependency on specific hardware and carry the risk of side-channel attacks or hardware vulnerabilities. Another approach involves the use of private order flow auctions.
In this model, users submit their orders to a dedicated auction mechanism where searchers compete to execute the trade. The searcher who offers the best execution price (often by returning a portion of the MEV to the user) wins the right to include the transaction in a block. This approach, exemplified by protocols like SUAVE, transforms MEV from a predatory extraction mechanism into a source of user value capture.
The user receives a rebate for their order flow, effectively reducing the cost of the options trade.
The implementation of private transactions in options markets involves a strategic trade-off between maximizing privacy through technologies like TEEs and maximizing value capture through auction-based mechanisms.

The Role of Encrypted Mempools
While full encryption of all mempool data is still a long-term goal due to performance constraints, certain protocols employ partial encryption for specific order types. This involves encrypting sensitive order parameters, such as strike prices or quantities, to obscure the user’s intent. The transaction details are only revealed to the block builder or searcher at the point of inclusion, preventing other searchers from front-running the trade.
This method is often combined with a commitment scheme, where users commit to an order before revealing its details, preventing them from backing out if the price moves favorably.

Evolution
The evolution of private transactions in crypto options reflects a continuous arms race between market participants. Initially, options trading on decentralized exchanges was highly vulnerable to MEV.
The early solutions focused on simple batching of transactions or utilizing trusted relays that operated with a degree of centralization. However, as MEV strategies became more sophisticated, these early solutions proved insufficient. The next phase involved the development of dedicated private order flow networks.
These networks, such as those associated with protocols like Flashbots, offered a more robust solution by creating a direct channel between users and block builders. This allowed for the execution of complex options strategies without fear of mempool-based front-running. The current evolution is focused on integrating these private order flow mechanisms directly into options protocols, creating a seamless user experience where private execution is the default for derivatives trading.
The challenge in this evolution lies in the centralization risk inherent in private order flow. By submitting orders to a small group of block builders or searchers, users consolidate power in the hands of a few entities. This creates a potential for collusion and censorship, where builders might prioritize certain transactions over others based on criteria beyond economic efficiency.
The current state of private transactions for options therefore presents a paradox ⎊ we trade one form of market inefficiency (MEV) for another (centralization risk).

Horizon
Looking ahead, the future of private transactions in crypto options will likely be defined by advancements in fully homomorphic encryption (FHE) and secure multi-party computation (MPC). Current private transaction models, while effective, still rely on a degree of trust in a specific block builder or TEE.
FHE offers a potential solution by allowing computations to be performed on encrypted data without ever decrypting it. This means an options protocol could calculate a trade’s outcome without ever revealing the underlying asset price or the user’s order details in plain text. The integration of FHE into options protocols would fundamentally alter market microstructure.
It would eliminate information asymmetry at the protocol level, making MEV extraction significantly more difficult. However, FHE remains computationally expensive and slow for real-time market operations. The next generation of options protocols will need to balance the computational cost of FHE with the speed required for efficient derivatives trading.
The long-term horizon for private transactions involves a complete re-thinking of market structure. Instead of a single, public mempool, we may see a fragmented landscape of specialized, private order flow networks for different asset classes. Options trading, with its specific need for confidentiality, will likely be one of the first to adopt these fully encrypted, trustless execution environments.
The goal is to create a market where execution quality is determined by a user’s skill in pricing, rather than their ability to outmaneuver MEV bots in a transparent, adversarial environment.
The future trajectory of private options transactions points toward fully encrypted execution environments, potentially eliminating MEV by making order details unreadable during computation.

Glossary
Verification of Transactions

Pre-Signed Transactions

Private Mev Relays

Private Transaction Relayers

Private Composability

Private Options Settlement
Time-Bound Transactions

Private Order Flow Benefits

Private Price Discovery






