Architectural Certainty
Trust in decentralized financial systems currently rests on the fragile hope that human auditors caught every edge case within a sea of code. Formal Verification Security replaces this social reliance with mathematical certainty, providing a rigorous method to prove that a smart contract adheres to its intended logic under every possible state. Within the domain of crypto options, where complex margin engines and liquidation thresholds dictate the solvency of millions in capital, the ability to mathematically guarantee that a protocol cannot enter an insolvent state remains the highest tier of technical assurance.
Mathematical certainty replaces social trust in the architecture of decentralized options.
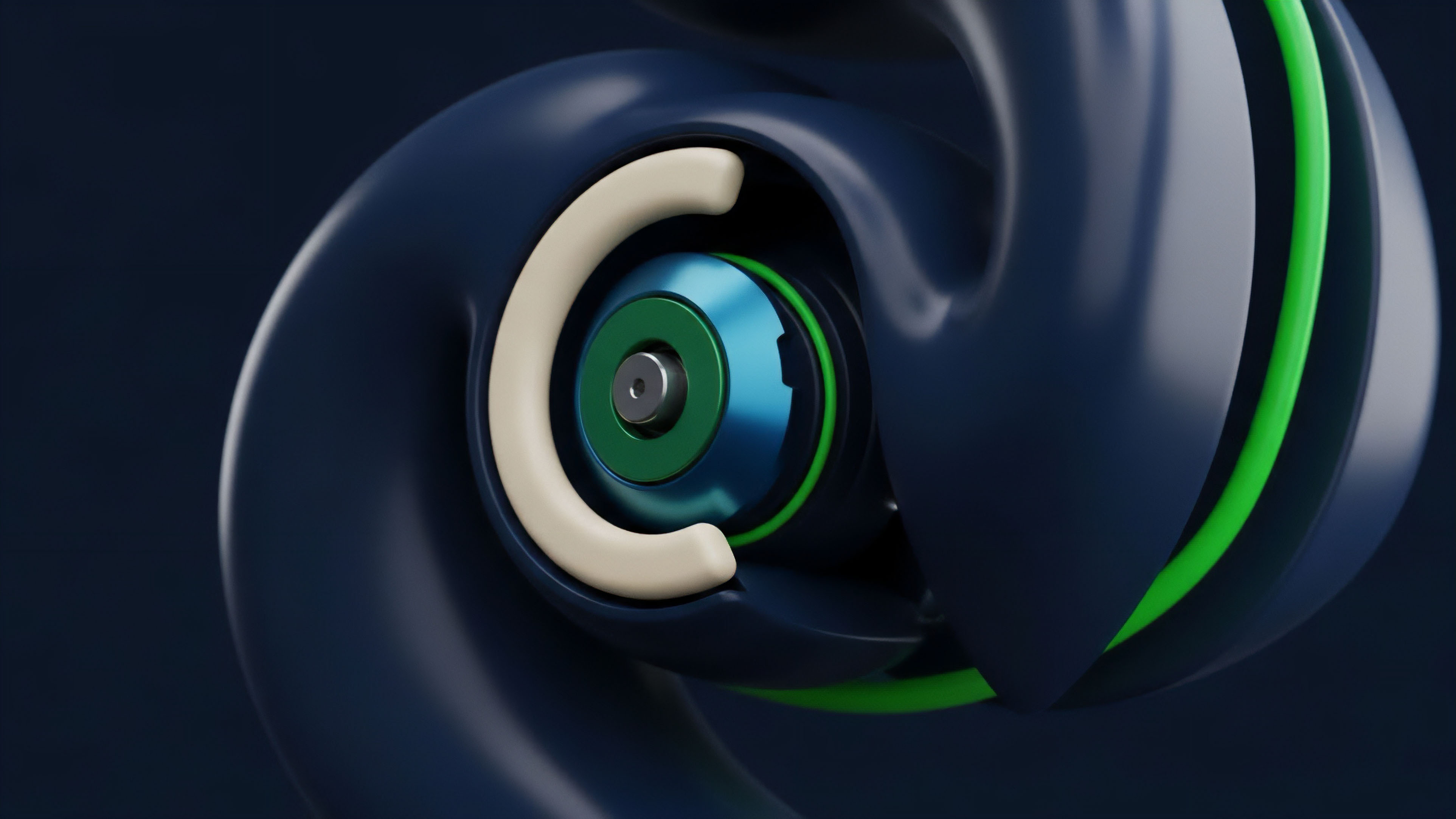
This shift represents a move toward high-assurance software engineering, where the code itself becomes a mathematical theorem. By defining the desired behavior of an options vault ⎊ such as the requirement that collateral must always exceed debt ⎊ developers use automated tools to search for any sequence of transactions that could violate this rule. If no such sequence exists, the protocol is proven secure against the specified vulnerabilities.
This level of rigor is vital for institutional participants who require deterministic risk profiles before committing significant liquidity to permissionless venues. The adoption of Formal Verification Security signals the professionalization of the decentralized finance terrain. It moves the industry away from the experimental ethos of early protocol development toward a future where financial primitives are as reliable as the avionics software in a commercial aircraft.
This transition is imperative for the scaling of on-chain derivatives, as it provides a robust defense against the logic errors that have historically led to catastrophic contagion events.

Historical Roots of High Assurance
The lineage of Formal Verification Security traces back to the mid-20th century, emerging from the necessity to secure critical infrastructure where software failure resulted in loss of life or massive economic destruction. Early computer scientists like Tony Hoare and Edsger Dijkstra pioneered the concept of formal methods, arguing that programming should be treated as a branch of mathematics. These principles were first applied in sectors like aerospace, nuclear energy, and medical device manufacturing, where the cost of a bug was infinite.
Formal verification translates legal intent into immutable logic through symbolic execution.
As the digital asset environment matured, the 2016 DAO hack served as a catalyst, revealing that traditional testing and manual audits were insufficient for the adversarial nature of public blockchains. The high density of value within smart contracts made them prime targets for sophisticated exploits. Consequently, the research community began adapting tools like SMT solvers and Coq proof assistants to the specific constraints of the Ethereum Virtual Machine.
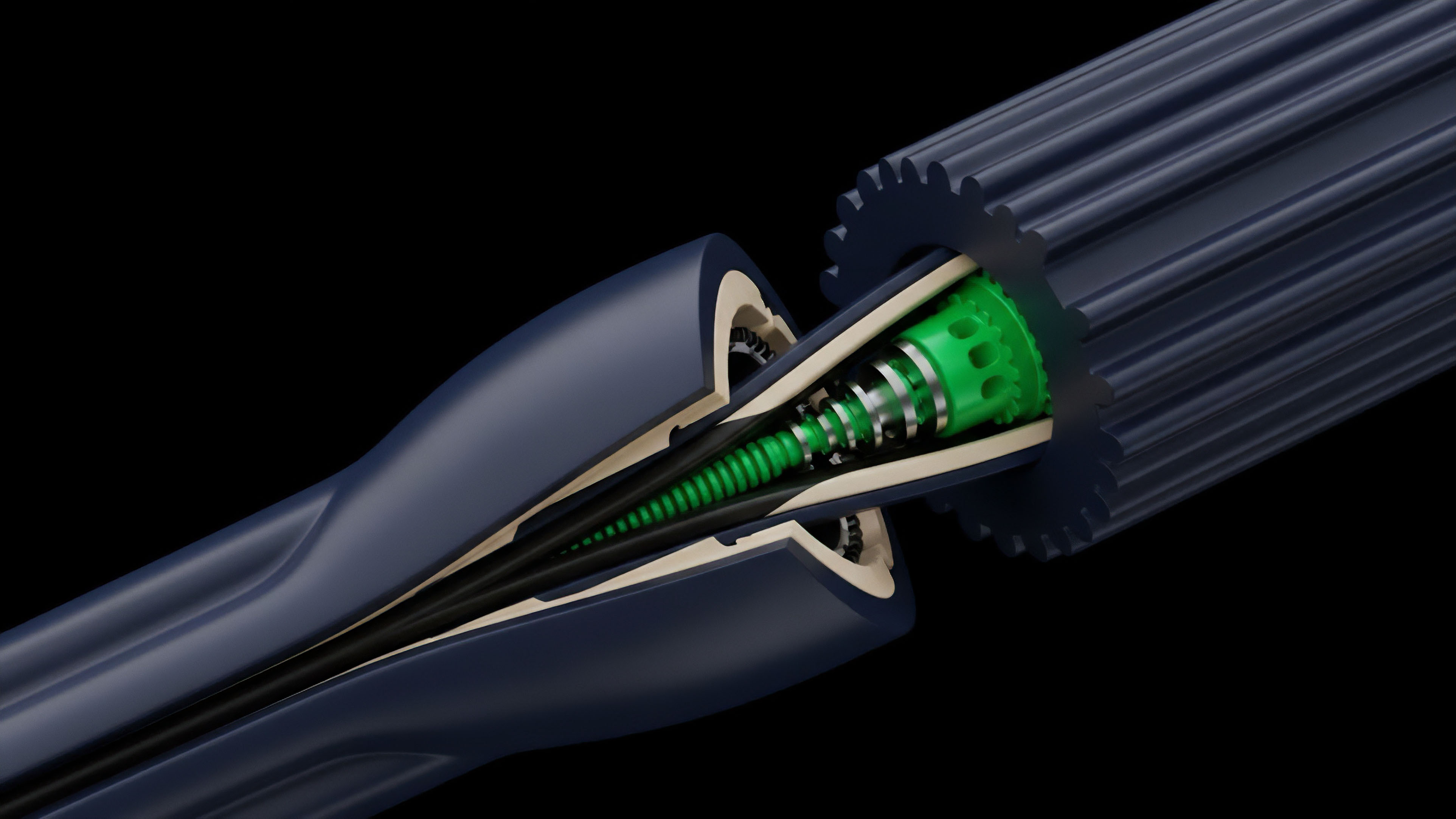
This adaptation allowed for the verification of Formal Verification Security properties directly at the bytecode level, ensuring that the compiled logic matched the developer’s intent. The migration of these academic methods into the crypto options market was driven by the complexity of derivative settlement logic. Unlike simple token transfers, options involve multi-stage state transitions, including strike price calculations, expiration checks, and collateral rebalancing.
The need to ensure these processes remain robust under extreme market volatility led to the integration of formal methods as a standard requirement for top-tier protocol launches.
Logic Verification Architecture
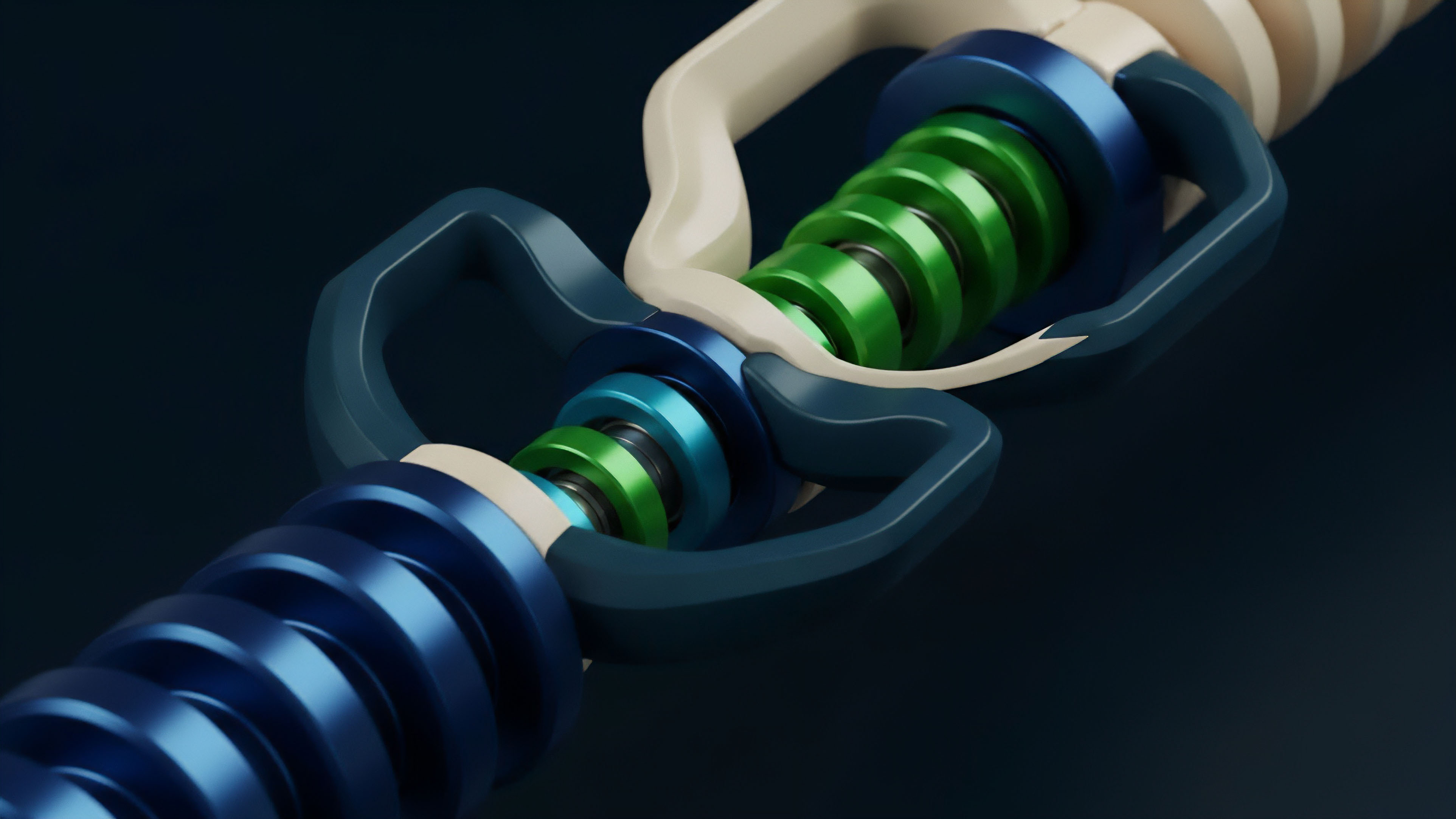
At the center of Formal Verification Security lies the concept of the invariant ⎊ a property that must remain true regardless of the actions taken by users or the passage of time. In an options protocol, an invariant might state that the total supply of vault shares multiplied by the share price must equal the total assets held. To prove this, the system uses symbolic execution, treating variables not as specific numbers but as algebraic symbols.
This allows the verification engine to explore every possible path through the code simultaneously, identifying edge cases that human testers would never conceive. The relationship between contract state and mathematical proof mirrors the conservation laws found in classical thermodynamics. Just as energy cannot be created or destroyed in a closed system, the value within a verified options vault must be accounted for across every state transition.
This physical-logic mapping ensures that no “leakage” of value can occur through rounding errors or reentrancy attacks. The verification process creates a formal specification ⎊ a mathematical description of what the code is supposed to do ⎊ and then checks the implementation against this specification using automated theorem provers.
Verification Methodology Comparison
| Method | Scope of Analysis | Assurance Level | Computational Cost |
|---|---|---|---|
| Unit Testing | Individual Functions | Low | Minimal |
| Fuzzing | Random State Space | Medium | Moderate |
| Formal Verification | Exhaustive State Space | Absolute | High |
The cost of verification remains a capital investment in the long-term solvency of the protocol.
Proof development requires a deep understanding of both the financial logic and the underlying virtual machine. Developers must define Formal Verification Security properties that cover all critical operations, including deposit, withdrawal, and liquidation. This involves writing specifications in specialized languages like the Certora Verification Language (CVL) or the K-Framework.
These specifications are then fed into a solver, such as Z3, which attempts to find a counterexample. If the solver fails to find a counterexample, the property is considered proven within the bounds of the specification.

Implementation Standards
Modern Formal Verification Security workflows are integrated directly into the continuous development pipeline. Rather than a one-time check, verification occurs every time the code is modified, ensuring that new features do not introduce regressions into the proven logic.
This iterative approach is vital for the fast-paced evolution of crypto derivatives, where protocols frequently update their pricing models or collateral types to remain competitive.

Property Verification Categories
- Arithmetic Integrity: Proving that mathematical operations like interest rate compounding or option premium calculations cannot result in overflows, underflows, or precision loss.
- Access Control: Ensuring that only authorized addresses can execute sensitive functions, such as pausing the protocol or adjusting risk parameters.
- State Consistency: Verifying that internal accounting always reflects the actual balance of assets held in the contract, preventing double-spending or unauthorized withdrawals.
- Liveness and Termination: Guaranteeing that transactions will always complete and that users can always exit their positions, even under extreme congestion.
Economic Impact Parameters
| Metric | Unverified Protocol | Verified Protocol |
|---|---|---|
| Capital Efficiency | Conservative / Over-collateralized | Aggressive / Optimized |
| Insurance Premium | High Risk Adjusted | Low Risk Adjusted |
| Institutional Allocation | Restricted | Permitted |
The execution of these proofs requires significant computational resources and expertise. Developers often focus on the most critical components ⎊ the margin engine and the settlement logic ⎊ where a failure would be most damaging. By prioritizing these areas, Formal Verification Security provides the highest return on security spend, protecting the nucleus of the protocol’s value.

Market Adaptation Trends
The role of Formal Verification Security has shifted from a niche academic luxury to a requisite for protocol survival. In the early stages of DeFi, a simple audit was sufficient to attract capital. Contrarily, the current market environment demands a multi-layered security stack where formal methods sit at the top. Large-scale liquidity providers now view a lack of formal proofs as a red flag, representing an unquantified tail risk that could wipe out their entire position. This evolution is reflected in the emergence of specialized security firms that focus exclusively on formal methods. These entities do not just look for bugs; they build mathematical models of the protocol’s economic and technical behavior. This provides a level of transparency that goes beyond open-source code, offering a verifiable guarantee of the protocol’s safety properties. For crypto options, this means that the complex interactions between greeks, volatility smiles, and liquidation engines are scrutinized with a level of precision that was previously impossible. The industry is also seeing a move toward runtime verification, where the Formal Verification Security properties are checked in real-time as transactions are processed. This adds a layer of defense-in-depth, allowing the protocol to pause itself if an invariant is violated, even if the vulnerability was not caught during the initial proof development. This proactive security model is essential for maintaining trust in an environment where the stakes are constantly increasing.

Future Verification Terrain
The next phase of Formal Verification Security involves the integration of zero-knowledge proofs and AI-assisted proof generation. As protocols become more complex, the manual effort required to write formal specifications becomes a bottleneck. Artificial intelligence models are being trained to automatically derive invariants from code and generate the necessary proofs, significantly reducing the time and cost of verification. This will democratize access to high-assurance security, allowing even smaller protocols to benefit from mathematical guarantees. Simultaneously, the rise of modular blockchain architectures creates new challenges for Formal Verification Security. Verifying a single contract is no longer enough; developers must now prove the safety of interactions across multiple chains and layers. This requires a shift toward compositional verification, where the proofs for individual components can be combined to prove the security of the entire system. For the crypto options market, this will enable the creation of cross-chain derivative products with the same level of certainty as local transactions. The ultimate goal is a world where financial risk is purely economic, not technical. By eliminating code risk through Formal Verification Security, participants can focus entirely on managing market volatility and strategic positioning. This will lead to a more efficient and resilient financial system, where the rules of the game are written in math and enforced by logic. Will the complexity of automated proof generation eventually outpace the capacity of human developers to define the very specifications they seek to verify?

Glossary

Reentrancy Prevention

Liquidation Logic

Temporal Logic

Formal Methods
Property-Based Testing

K Framework

Collateralization Ratio Verification
Isabelle/hol

Invariant Preservation