Essence
The process of Black-Scholes Model Verification is the rigorous, quantitative assessment of the model’s ability to accurately price European-style options on crypto assets ⎊ a financial tool designed for an entirely different market structure. This verification is not an academic exercise; it is a critical systems risk check, confirming the stability of collateralization and liquidation engines built atop these pricing primitives. The core issue is the model’s reliance on five input variables, most critically the single, constant volatility parameter, which immediately breaks down in the face of crypto’s non-stationary, jump-discontinuous price processes.
The model’s verification fails at the most fundamental level because the underlying asset’s price distribution is fat-tailed, exhibiting significantly higher kurtosis than the log-normal distribution the Black-Scholes-Merton (BSM) framework assumes.
The functional relevance of verification within decentralized finance (DeFi) protocols is paramount. A mis-verified, and therefore mis-priced, option can lead to systemic insolvency within a decentralized options vault or an automated market maker (AMM) for derivatives. When a protocol’s margin engine calculates a user’s collateral requirement based on a model that severely underprices out-of-the-money options ⎊ a phenomenon known as the volatility skew ⎊ the system is inherently over-leveraged.
Our inability to respect the skew is the critical flaw in our current models.
Black-Scholes Model Verification in crypto is the quantification of pricing error, serving as a direct measure of systemic protocol solvency.
The systemic implications are clear: BSM verification failure is a proxy for model risk, a risk that is socialized across all liquidity providers in a permissionless environment. When the model is verified as accurate ⎊ meaning its implied volatility aligns closely with realized volatility and exhibits a near-flat volatility surface ⎊ the system is deemed robust. When verification reveals a severe mismatch, it signals a structural vulnerability that adversarial game theory dictates will be exploited by informed participants.
Origin
The genesis of the BSM verification challenge lies in the model’s original construction in the 1970s, which provided the first elegant, closed-form solution for option pricing. The original paper and subsequent work by Merton relied on a set of restrictive, foundational assumptions ⎊ assumptions that were plausible approximations in the highly liquid, centrally-cleared markets of the time. The verification process evolved alongside these traditional markets, primarily through the examination of the model’s outputs against observable market prices, leading to the concept of implied volatility.
In crypto derivatives, the BSM framework was initially adopted out of expediency and familiarity, despite the immediate and obvious violations of its underlying assumptions. The model’s original utility was its capacity to reduce the problem to a single, unobservable parameter ⎊ volatility ⎊ by assuming the rest were known or constant. The primary verification methods inherited from traditional finance are therefore centered on analyzing how this implied volatility behaves across different strike prices and maturities.
BSM Foundational Assumptions and Crypto Violations
The model’s core principles, which must be verified against the crypto market’s reality, include:
- Continuous Trading and Hedging: The model assumes hedging can occur frictionlessly and continuously, which is impossible due to network latency, gas fees, and block finality ⎊ these are fundamental violations of protocol physics.
- Constant Risk-Free Rate: While a risk-free rate is often approximated by a DeFi lending rate (e.g. Aave or Compound), this rate is stochastic and volatile, contradicting the model’s static input.
- Lognormal Price Distribution: The geometric Brownian motion (GBM) assumption is incompatible with the observed fat-tailed returns of digital assets, where extreme price movements occur far more frequently than the normal distribution predicts.
- Constant Volatility: The single, constant volatility input is an immediate falsehood, as crypto volatility is demonstrably stochastic, mean-reverting, and highly dependent on price level.
The verification, therefore, is not a check of the model’s validity, but a measurement of the systemic error introduced by using a tool that fundamentally misunderstands the asset class.

Theory
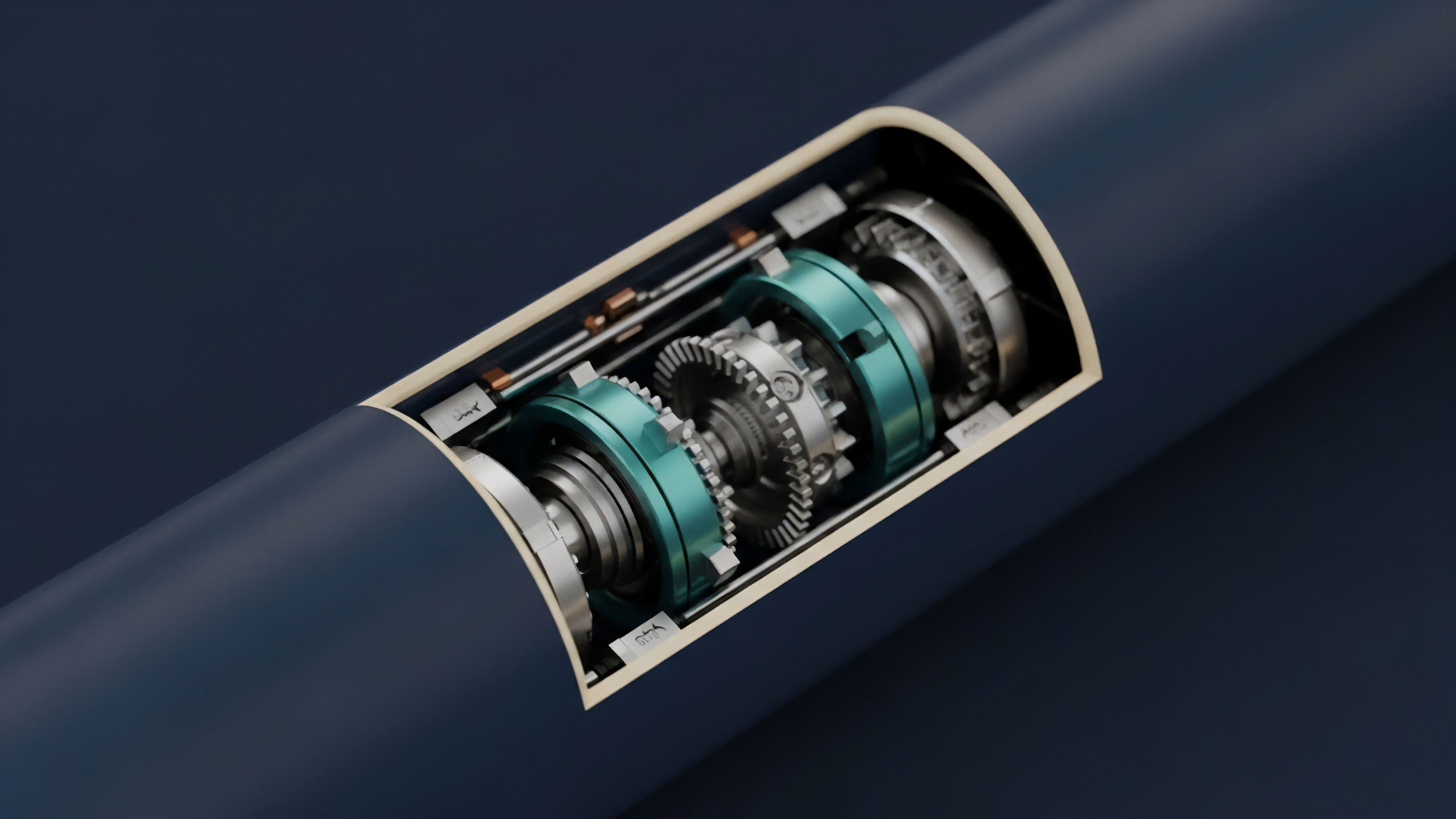
The theoretical core of Black-Scholes Model Verification is the Implied Volatility Surface (IVS). The BSM is verified only if the implied volatility derived from market prices is constant across all strike prices (K) and times to expiration (T). In a theoretically perfect BSM world, the IVS would be a flat plane.
The verification process, then, is a direct measurement of the topography of this surface.

Quantifying Model Failure
In crypto markets, the IVS is a complex, three-dimensional structure defined by a severe volatility skew and smile. This shape is the model’s theoretical rejection ⎊ a direct visualization of the market pricing in the non-GBM risks that the BSM ignores. The skew, where implied volatility for out-of-the-money (OTM) puts is higher than for at-the-money (ATM) options, reflects the market’s collective fear of a sharp, sudden price collapse.
This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored.
The volatility skew is the market’s collective, probabilistic bet against the Black-Scholes-Merton assumption of log-normal returns.
The theoretical divergence is rooted in the absence of a complete market and the reality of jump risk. A complete market allows any payoff to be perfectly replicated through continuous hedging. Crypto markets are incomplete due to transaction costs and illiquidity, making perfect replication impossible and thus invalidating the risk-neutral pricing foundation of BSM.
This failure is compounded by the market’s structural susceptibility to cascading liquidations ⎊ a systems risk that is explicitly priced into OTM options.
(It is interesting to note that this structural divergence between theoretical financial physics and market reality echoes the transition from Newtonian mechanics to quantum field theory, where the classical model fails at the extreme edges of scale and complexity.)
Delta Hedging Error Analysis
Verification can also be conducted by simulating the Delta Hedging performance that BSM implies. The model suggests a riskless portfolio can be constructed by holding the option and a dynamically adjusted position in the underlying asset (Delta). Verification involves measuring the cost and efficacy of this hedging strategy in a high-fee, discrete-time environment.
| Parameter | BSM Assumption | Crypto Reality | Verification Impact |
|---|---|---|---|
| Hedging Frequency | Continuous (Infinite) | Discrete (Limited by Gas/Latency) | High Transaction Cost, Basis Risk |
| Transaction Cost | Zero | Non-Zero (Gas Fees) | Hedging P&L Drag, Model Overvaluation |
| Market Jumps | None (Smooth Path) | Frequent (Fat Tails) | Hedging Failure, Large Model Error |
The resulting P&L from the simulated hedge portfolio is the true verification metric; a large, negative variance signals a profound model failure.
Approach
The practical approach to Black-Scholes Model Verification in crypto involves two primary, interconnected methodologies: Implied Volatility Surface (IVS) Construction and Model-Implied Greeks Calibration. The goal is not to prove the BSM is correct, but to parameterize its incorrectness ⎊ to understand the precise magnitude of the necessary adjustments.

IVS Construction and Volatility Skew Analysis
The primary tool is the IVS. Market makers and sophisticated derivatives protocols use high-frequency order book data and executed trade prices to back out the implied volatility for a matrix of strike and maturity pairs. The resulting surface is then analyzed for its structural features.
- Data Aggregation: Collecting reliable, time-stamped options prices across all decentralized and centralized venues ⎊ a complex task given liquidity fragmentation.
- Volatility Calculation: Inverting the BSM formula for each option price to solve for the implied volatility ().
- Surface Visualization: Mapping the values against the Strike/Maturity axes to observe the skew and term structure.
- Skew Quantification: Measuring the difference between the implied volatility of a 25-Delta put and a 25-Delta call (the Skew Slope ) to quantify the tail risk priced into the market.
A steep, negative skew ⎊ high IV for OTM puts ⎊ indicates a significant failure of the BSM model to account for the market’s perceived crash risk. Verification is passed only when this skew is stable and predictable, allowing for a consistent, model-adjusted pricing methodology.

Greeks Sensitivity Testing
The verification of the model’s risk sensitivities, or Greeks , is paramount for risk management. If the BSM-derived Delta or Vega is inaccurate, a protocol’s liquidation logic will fail to adequately manage its risk exposure.
- Delta Verification: Testing the model’s predicted change in option price for a unit change in the underlying price against empirical market movement. A miscalculated Delta leads to inefficient or insufficient hedging.
- Vega Verification: Checking the model’s sensitivity to changes in volatility. Since crypto volatility is stochastic, BSM’s Vega ⎊ which assumes a static ⎊ is often misleadingly low during volatility spikes, creating immense, hidden exposure for sellers.
| Metric | BSM Output | Verification Target | Systemic Purpose |
|---|---|---|---|
| Delta | Hedge Ratio | Empirical Price Sensitivity | Liquidation Thresholds |
| Vega | Volatility Exposure | Stochastic Volatility Sensitivity | Margin Requirement Buffer |
| Skew Slope | Zero (Implied) | Market-Observed Skew | Tail Risk Pricing Adjustment |

Evolution
The evolution of Black-Scholes Model Verification in crypto is a story of necessary, painful migration away from a closed-form solution toward stochastic and local volatility frameworks. The initial reliance on BSM for its simplicity gave way to a pragmatic acceptance that the model serves only as an interpolation tool for the IVS, not a fundamental pricing truth.

Stochastic Volatility and Jump Diffusion
The market has progressively moved to models that attempt to correct the BSM’s fundamental flaws. Stochastic Volatility (SV) models , such as Heston, treat volatility as a second, random process rather than a constant. This shift is the theoretical acknowledgement that the volatility of volatility ⎊ the Vanna and Volga Greeks ⎊ are real, measurable risk factors in crypto.
Verification of these SV models is more complex, involving the calibration of additional parameters, such as the mean-reversion rate of volatility.
The migration from BSM to Stochastic Volatility models is the architectural response to the reality of volatility as a financial asset itself.
Furthermore, the inclusion of Jump Diffusion models attempts to account for the fat-tailed returns directly by adding a Poisson process to the GBM, simulating the sudden, large price movements common in a low-liquidity, protocol-driven market. Verification of these models involves statistical testing of the jump frequency and magnitude against historical price data.
Decentralized Verification and Governance
The most significant evolution is the shift of the verification function into the protocol itself. Decentralized options protocols cannot rely on external, trusted market data for verification; they must internalize the risk. This has resulted in:
- DAO-Governed Parameter Adjustments: Governance mechanisms vote on the skew parameterization, effectively hard-coding the BSM verification failure into the system’s risk limits.
- Liquidation Engine Sensitivity: Protocols are architected to run multiple pricing models in parallel ⎊ BSM, Heston, and empirical models ⎊ with the highest-risk calculation determining margin requirements, ensuring conservative capital efficiency.
- Implied Volatility Oracles: New oracle designs are being developed to feed a real-time, strike-specific implied volatility surface into the smart contract, moving the system’s pricing mechanism away from BSM’s static sigma and towards the observed market reality.

Horizon
The horizon for Black-Scholes Model Verification is its eventual retirement as a primary pricing tool and its reclassification as a simple benchmark for computational speed. The future of crypto options valuation will be dominated by computationally intensive, model-free or semi-parametric approaches that fully acknowledge the market’s non-stationarity and endogenous risks.

The Challenge of Model Risk Aggregation
The next major challenge is the aggregation of model risk across interconnected DeFi protocols. When an options protocol uses a Heston model, and a lending protocol uses BSM for collateral valuation, the systemic risk is a non-linear function of their combined model errors. The verification challenge moves from confirming a single model’s price accuracy to confirming the resilience of the entire risk graph ⎊ the network of liabilities and collateral across the decentralized ecosystem.
The most critical area of research involves applying techniques from behavioral game theory to the verification process. The model’s failure is often exacerbated by coordinated or strategic behavior around liquidations. Verification must account for the impact of automated agents (bots) executing adversarial strategies based on known model weaknesses, effectively turning model error into exploitable alpha.

Architecting for Systemic Resilience
The ultimate goal is a pricing and risk system that is robust to the failure of any single model. This requires:
- Adversarial Simulation: Running Monte Carlo simulations where the underlying asset path is generated by a heavy-tailed, jump-diffusion process, and then stress-testing the BSM’s Delta and Vega against this path.
- Model-Agnostic Collateral: Structuring collateral requirements not on a model’s point price, but on the Value-at-Risk (VaR) or Expected Shortfall (ES) derived from a range of models, providing a capital buffer against model error.
- Regulatory Arbitrage Defense: Protocols will increasingly need to demonstrate verifiable model robustness to preempt future regulatory oversight, as jurisdictions worldwide begin to standardize capital requirements based on model risk. The capacity to prove the systemic soundness of the pricing mechanism will become a competitive advantage.
Glossary

On-Chain Transaction Verification

Data Verification Architecture

Identity Verification

First-Price Auction Model
Crypto Span Model

Compliance Verification

Verifier Model

Pooled Liquidity Model

Pricing Function Verification