Essence
Mathematical Verification represents the transition from probabilistic security to deterministic certainty within decentralized financial architectures. It functions as the rigorous application of formal logic to verify that the execution of smart contracts aligns perfectly with their intended specifications. While traditional software testing relies on sampling potential inputs to observe outcomes, this methodology utilizes mathematical proofs to exhaustively confirm that every possible state transition remains within safe, predefined parameters.
Mathematical Verification provides the absolute certainty required for trustless financial settlement.
In the context of crypto options and derivatives, Mathematical Verification ensures that margin requirements, liquidation thresholds, and payout structures operate without logic errors. This precision is vital because digital assets move at the speed of block finality, leaving zero room for human intervention or manual reversal. By transforming contract code into a series of logical equations, developers can prove the absence of reentrancy vulnerabilities, integer overflows, and unauthorized state changes.
The adoption of these formal methods signals a shift toward institutional-grade reliability. As capital flows into sophisticated derivative protocols, the demand for verifiable security outweighs the speed of rapid deployment. Protocols that prioritize Mathematical Verification build a foundation of resilience, allowing for the creation of complex financial instruments that can withstand adversarial market conditions and sophisticated exploit attempts.

Origin
The roots of Mathematical Verification lie in the field of formal methods, a discipline developed decades ago for mission-critical systems in aerospace, nuclear energy, and medical hardware.
These industries required a level of assurance that exceeded the capabilities of standard debugging. The emergence of blockchain technology reintroduced the necessity for this level of rigor, as smart contracts are essentially immutable financial hardware once deployed to a public ledger. Early decentralized finance experiments often suffered from catastrophic failures due to simple logic oversights.
These events demonstrated that empirical testing is insufficient for protecting billions of dollars in locked value. Consequently, the industry began adopting tools like Hoare Logic and Temporal Logic to define the properties of secure code. This transition was accelerated by the realization that in an environment where code is law, any ambiguity in that law becomes a vector for total capital loss.
The maturation of Mathematical Verification within crypto was driven by the need for trustless settlement. Unlike traditional finance, where legal recourse can mitigate contract failure, decentralized systems require the code itself to be the final arbiter. This reality forced a return to first principles, where the security of a derivative protocol is not a matter of reputation or insurance, but a mathematical theorem that has been proven true across all possible execution paths.

Theory
The theoretical framework of Mathematical Verification relies on Formal Specification and Model Checking.
A specification is a precise description of what the contract must do, written in a mathematical language. The verification process then uses Satisfiability Modulo Theories (SMT) solvers to check if the implementation of the contract can ever violate these specifications. If the solver finds a set of inputs that leads to a violation, it provides a counterexample, revealing a hidden vulnerability.
Formal Invariants
At the heart of this theory are Invariants ⎊ properties that must remain true throughout the entire lifecycle of a contract. In a decentralized option protocol, a principal invariant might state that the total value of collateral must always exceed the total value of outstanding liabilities. Mathematical Verification proves that no combination of trades, liquidations, or price updates can ever break this rule.
| Feature | Empirical Testing | Mathematical Verification |
|---|---|---|
| Coverage | Partial (Input Samples) | Exhaustive (All States) |
| Certainty | Probabilistic | Deterministic |
| Error Detection | Finds known bugs | Proves absence of bugs |
| Complexity | Low to Medium | High (Formal Logic) |

Symbolic Execution
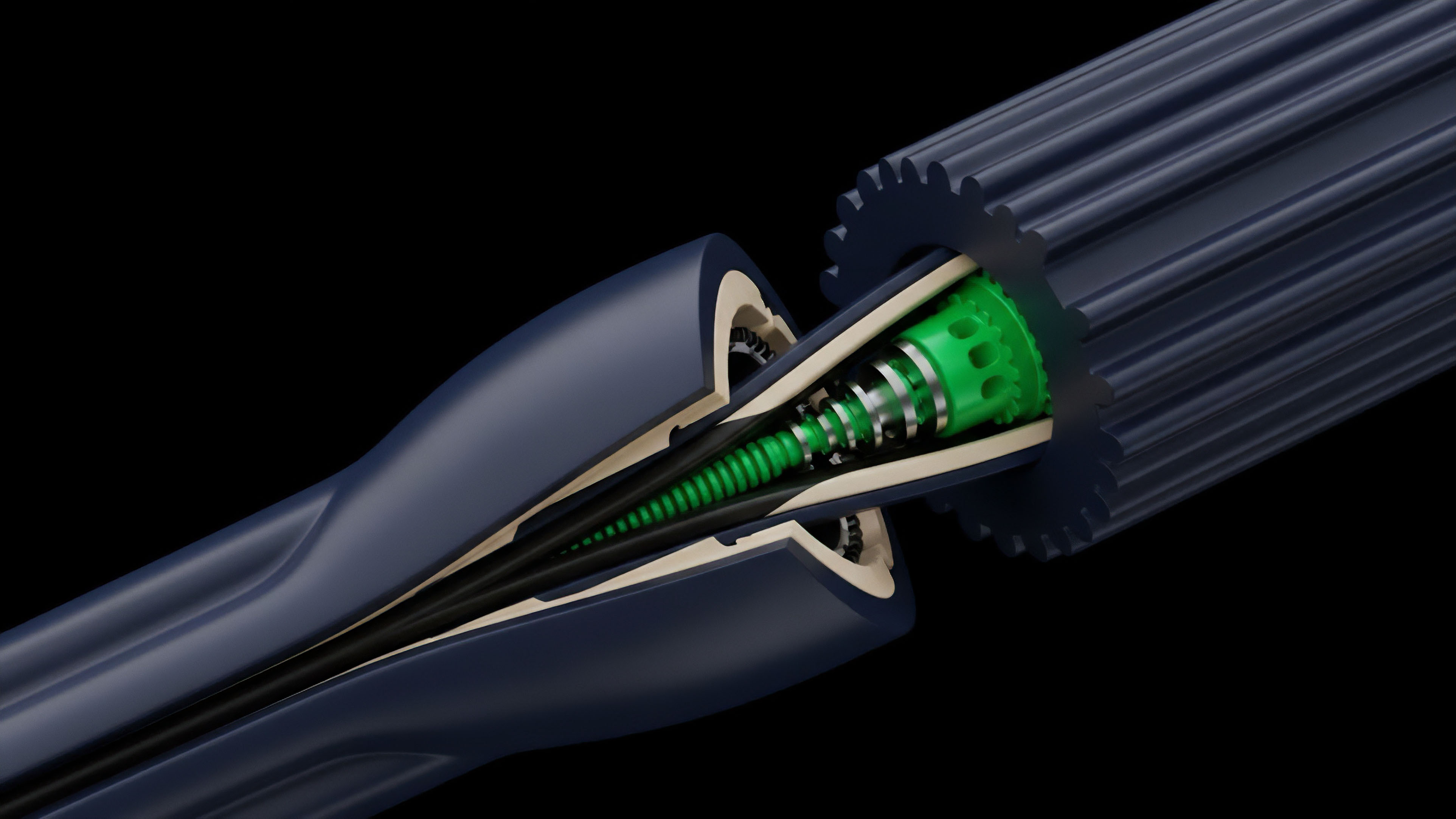
Another vital component is Symbolic Execution, which evaluates a program using symbolic values instead of concrete data. This allows the verifier to traverse multiple execution paths simultaneously. By representing variables as symbols, the system can determine the conditions under which a specific branch of code is triggered, ensuring that every edge case in a derivative’s pricing or settlement logic is accounted for and secured.
Formal proofs replace human oversight with immutable logical constraints.

Approach
Executing Mathematical Verification requires a structured integration of automated tools and manual logic definition. Developers begin by defining the high-level properties of the protocol, such as solvency and permissioning. These properties are then translated into formal languages that can be interpreted by verification engines.
This process is iterative, often revealing flaws in the initial design before a single line of production code is finalized.
Verification Methodologies
- Bounded Model Checking: This technique explores the state space of a contract up to a certain number of steps, identifying vulnerabilities that occur within specific transaction sequences.
- Static Analysis: Automated tools scan the source code for common patterns associated with vulnerabilities, providing a baseline level of security before deeper formal methods are applied.
- Theorem Proving: Engineers use interactive provers to construct step-by-step mathematical proofs that the contract satisfies its most complex requirements.
The current implementation of these methods often involves third-party security firms that specialize in formal verification. These firms use proprietary solvers to stress-test the contract against a library of known attack vectors. For a crypto options platform, this includes verifying the accuracy of Black-Scholes implementations and the robustness of the Margin Engine under extreme volatility.
| Verification Tool | Primary Function | Target Language |
|---|---|---|
| Certora Prover | Formal Property Checking | Solidity, Vyper |
| K-Framework | Semantic Verification | Multiple Bytecodes |
| Z3 Solver | SMT Logic Solving | Mathematical Logic |

Evolution
The trajectory of Mathematical Verification has moved from a niche academic pursuit to a mandatory requirement for high-stakes DeFi protocols. In the early years of Ethereum, security was largely reactive, with developers patching bugs after they were exploited. The shift toward a proactive stance was driven by the increasing complexity of Composable Finance, where the interaction between different protocols creates unforeseen systemic risks.

Structural Changes in Security
The industry has transitioned from one-time audits to continuous verification. Modern protocols now incorporate formal checks into their development pipelines, ensuring that every code update is mathematically verified before it reaches the mainnet. This evolution has also seen the rise of Zero-Knowledge Proofs (ZKP), which utilize mathematical verification to provide privacy and scalability without sacrificing security.
Systemic resilience depends on the rigorous elimination of edge-case vulnerabilities.
The integration of Mathematical Verification into the compiler level is another significant advancement. New programming languages are being designed with built-in support for formal methods, making it easier for developers to write provably secure code from the start. This reduces the reliance on external auditors and moves the responsibility for security directly into the development lifecycle.
Horizon
The future of Mathematical Verification lies in the democratization of formal methods through artificial intelligence and automated proof generation.
Currently, writing formal specifications is a labor-intensive task that requires specialized expertise. Emerging AI models are being trained to assist in this process, translating natural language requirements into formal mathematical properties that can be automatically verified.

Automated Security Environments
We are moving toward a state where Real-Time Verification becomes possible. In this future, the network itself could verify the mathematical correctness of a transaction before it is included in a block. This would create an environment where logic errors are physically impossible to execute, providing a level of security that exceeds anything currently available in traditional or decentralized finance.
- AI-Assisted Specification: Using machine learning to generate formal properties from documentation and code comments.
- On-Chain Verifiers: Implementing lightweight verification engines directly into blockchain virtual machines.
- Formal Verification as a Service: Cloud-based platforms that provide continuous, automated formal analysis for all deployed contracts.
As the derivative market continues to expand, the systemic implications of Mathematical Verification will become even more pronounced. It will be the primary differentiator between protocols that survive market turbulence and those that succumb to technical failure. The ultimate goal is the creation of a global financial system that is not only transparent and permissionless but also mathematically guaranteed to be secure.

Glossary

Mathematical Certainty

Continuous Verification

Real-Time Verification

Automated Theorem Proving

Protocol Resilience

Systemic Stability

Formal Specification

Formal Methods

Mathematical Verification