Essence
Zero-Knowledge Security refers to the application of cryptographic primitives that allow one party to prove the validity of a statement to another party without revealing any underlying information about that statement. In the context of decentralized finance, this capability directly addresses the fundamental tension between transparency and privacy inherent in public blockchain architectures. While the public ledger offers unprecedented auditability, it simultaneously exposes market participants to front-running, price manipulation, and the exploitation of order flow ⎊ a critical issue for derivatives markets where information asymmetry is highly valuable.
The core function of Zero-Knowledge Security in crypto derivatives is to enable private computations on public data. For an options protocol, this means a user can prove they meet the necessary collateral requirements for a position, or that their trade execution follows the rules of the protocol, without revealing the size of their collateral, their specific trading strategy, or the precise details of their order. This allows for the creation of sophisticated financial products that require a degree of confidentiality to function efficiently, mimicking the private nature of traditional financial markets while retaining the trustless verifiability of a decentralized system.
Zero-Knowledge Security enables verifiable privacy, allowing market participants to prove the integrity of their financial actions without revealing the sensitive data that underpins them.
This approach moves beyond simple data encryption. It creates a new form of digital trust where the integrity of the system is secured not by obfuscation, but by mathematical proof. The financial implication is profound: it allows for the development of complex derivatives, such as options with dynamic margin requirements or exotic products, that would otherwise be impractical on a public ledger due to the high risk of Maximal Extractable Value (MEV) extraction and strategic front-running.
The architectural goal is to shift from a system where “everything must be public” to one where “everything must be verifiable,” creating a more robust and efficient market microstructure for complex financial instruments.

Origin
The conceptual foundation of zero-knowledge proofs originates from the academic work of Shafi Goldwasser, Silvio Micali, and Charles Rackoff in their 1985 paper, “The Knowledge Complexity of Interactive Proof Systems.” This paper introduced the concept of an interactive proof system where a prover convinces a verifier of a statement’s truth without conveying additional information. The core properties defined were completeness (a true statement can be proven), soundness (a false statement cannot be proven), and zero-knowledge (the verifier learns nothing beyond the statement’s truth).
The application of these concepts to practical computation required significant technical evolution. The initial interactive proofs were complex and resource-intensive. The breakthrough for modern blockchain application came with the development of non-interactive zero-knowledge proofs (NIZKPs), specifically zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) and zk-STARKs (Zero-Knowledge Scalable Transparent Argument of Knowledge).
These advancements allowed a single, compact proof to be generated without requiring real-time interaction between the prover and verifier, making them suitable for on-chain verification.
While early applications of zero-knowledge technology in crypto focused primarily on privacy-preserving cryptocurrencies, the application to derivatives markets emerged as a response to the inherent vulnerabilities of public order books. The high-stakes nature of options trading, where information about positions and liquidations can be exploited for significant profit, highlighted the need for a solution that could secure order flow. The shift in focus from privacy coins to privacy-preserving financial infrastructure marked the transition of ZK technology from a niche application to a foundational element for building a mature decentralized financial system.

Theory
The theoretical application of Zero-Knowledge Security in options markets is rooted in the conflict between market efficiency and information leakage. In a transparent, public ledger environment, every pending order and every collateral adjustment is visible. This allows sophisticated actors to predict price movements and execute front-running strategies, which extracts value from other market participants and reduces overall market liquidity.
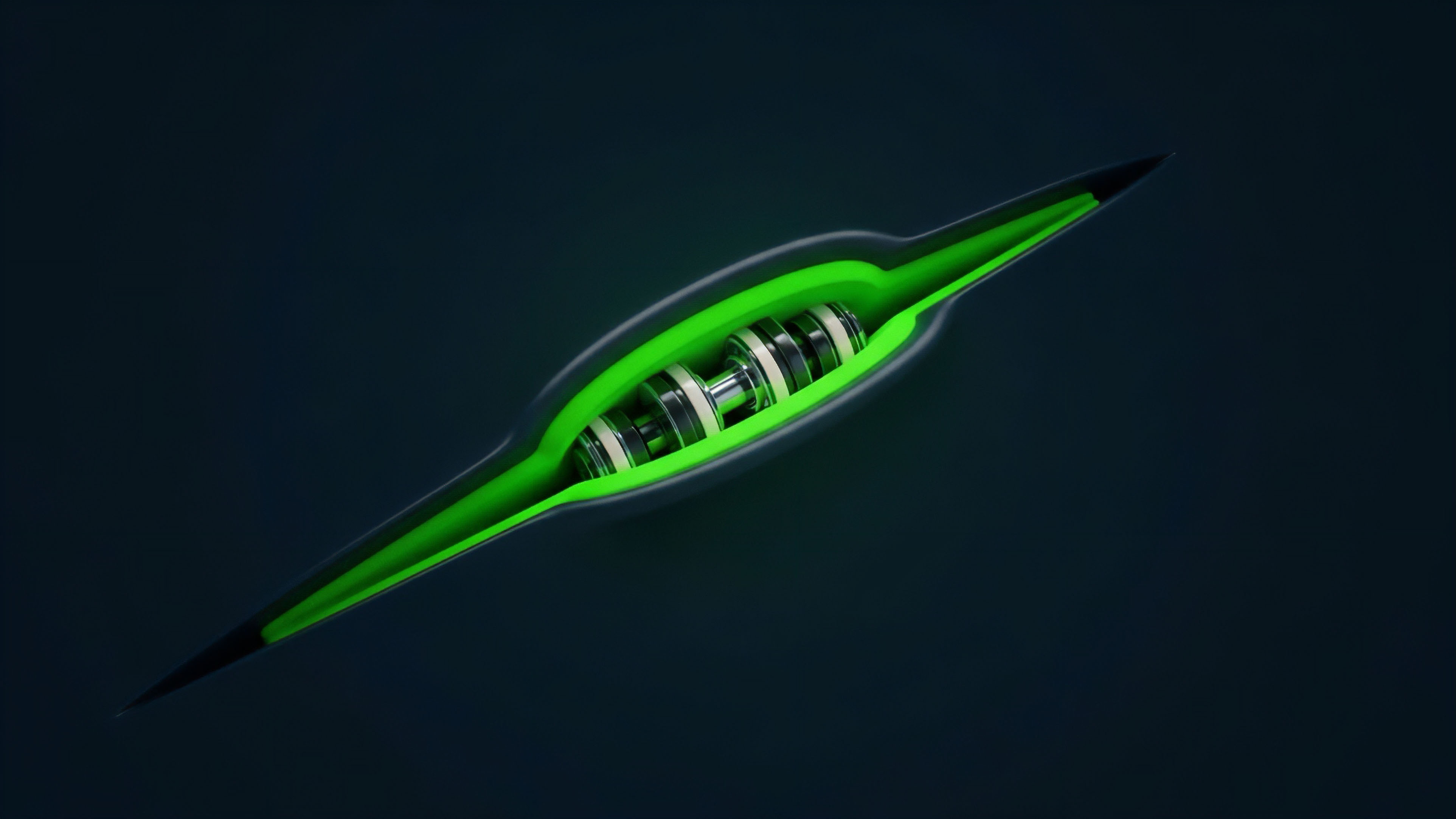
Zero-knowledge proofs mitigate this by decoupling verifiability from visibility.
Consider a decentralized options exchange (DEX). A user submits an order to buy or sell an option. Instead of broadcasting the order details publicly, the user generates a ZK-proof that demonstrates two things: first, that they have sufficient collateral to cover the margin requirements of the trade; and second, that the order adheres to the protocol’s rules (e.g. within a valid price range, correct option type).
This proof is submitted to the settlement layer, where validators can verify its validity without ever seeing the specifics of the trade. The order details are only revealed to the counterparty at the point of execution.
The implementation of zero-knowledge proofs transforms market microstructure by moving from public order books to verifiable private order flow, directly combating MEV extraction.
This approach changes the dynamics of market making and risk management. Market makers can operate with less fear of being exploited, leading to tighter spreads and greater liquidity. From a risk perspective, ZK-proofs enable more efficient capital management.
A user’s collateral and position details can remain private, yet the protocol can verify in real-time that the user’s risk profile remains within acceptable parameters. This allows for more dynamic margin requirements, where collateral checks are performed cryptographically rather than through public, on-chain data analysis. The key theoretical trade-off lies in balancing the computational cost of generating proofs against the financial value gained from preventing information leakage.
Proof System Comparison
Different zero-knowledge systems offer distinct trade-offs in terms of performance and trust assumptions. The choice of system impacts the protocol’s overall architecture and user experience.
| Proof System | Key Feature | Trust Assumption | Proof Size | Computational Cost |
|---|---|---|---|---|
| zk-SNARKs | Succinct, fast verification | Requires a trusted setup phase | Small, constant size | High prover computation cost |
| zk-STARKs | Transparent setup, post-quantum resistance | No trusted setup needed | Larger proof size (linear to computation) | High prover computation cost |
| Bulletproofs | Logarithmic proof size, no trusted setup | No trusted setup needed | Logarithmic size | High prover computation cost |
The choice between these systems for a derivatives platform often hinges on the specific needs of the application ⎊ whether a small proof size is prioritized for lower L1 transaction costs (SNARKs) or a trustless setup is prioritized for enhanced security (STARKs).

Approach
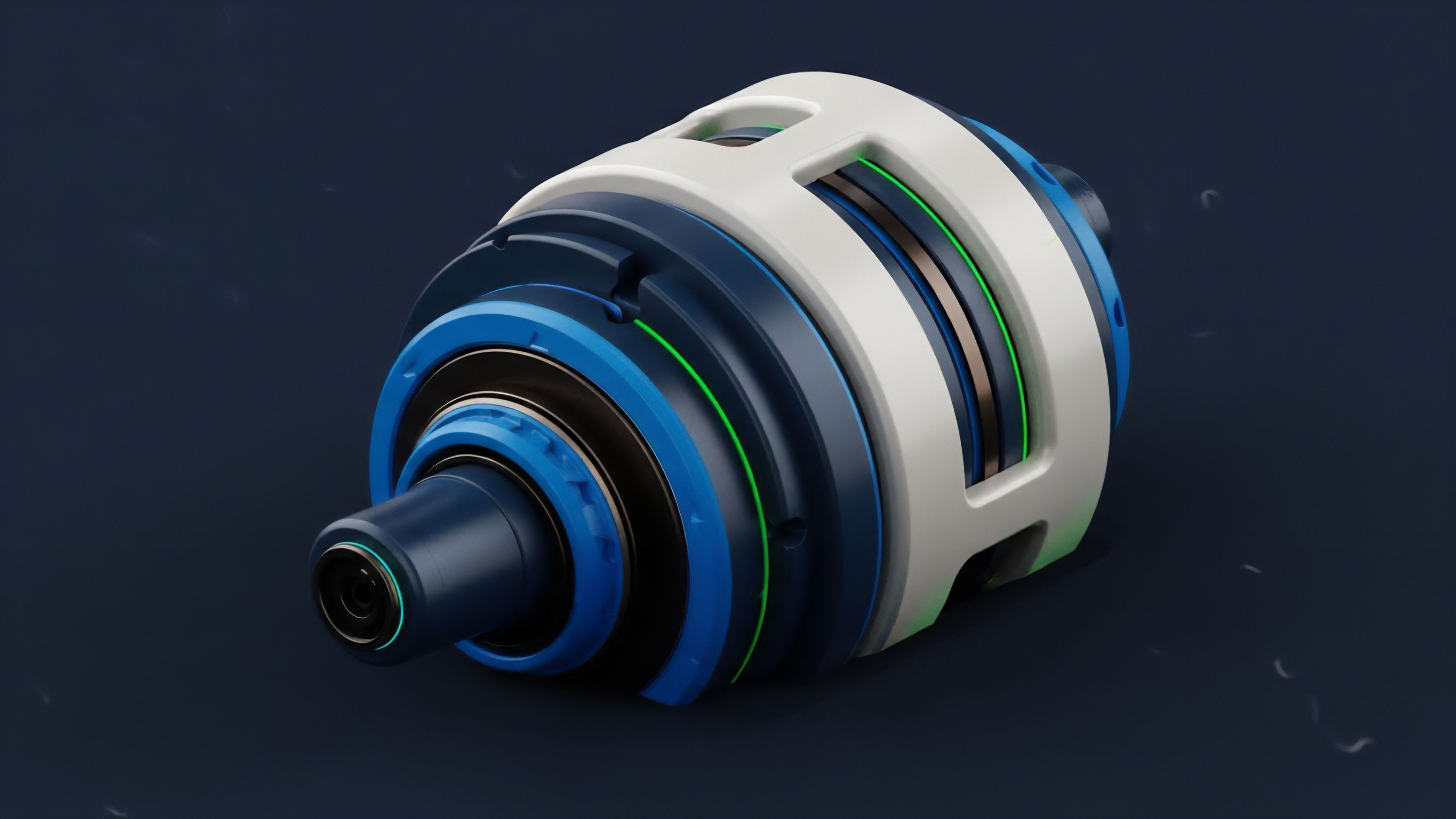
The practical implementation of Zero-Knowledge Security in crypto derivatives follows a layered architectural approach, primarily utilizing Zero-Knowledge Rollups (zk-Rollups). The core challenge is to offload complex computations from the main blockchain (Layer 1) while retaining its security guarantees. In this model, the execution of trades and calculation of margin requirements occur on a Layer 2 network, which periodically bundles transactions and submits a single cryptographic proof of their validity back to Layer 1.
For an options protocol, this approach enables high-frequency trading and complex financial calculations without incurring the high gas fees associated with on-chain computation. The critical component is the ZK-proof itself, which cryptographically guarantees that all state transitions on Layer 2 ⎊ such as changes in collateral, position sizes, or liquidations ⎊ are valid according to the protocol rules. This allows for a massive increase in throughput while maintaining the security properties of the underlying blockchain.
Systemic Risks and Trade-Offs
Implementing Zero-Knowledge Security introduces a new set of systems risks and engineering trade-offs. The high computational cost of generating proofs creates a significant technical hurdle. While verification on Layer 1 is fast, the prover itself requires substantial resources, which can create latency issues for high-speed trading applications.
Furthermore, the reliance on a trusted setup for certain ZK-proof systems introduces a single point of failure where the initial parameters could be compromised, potentially allowing a malicious actor to create invalid proofs.
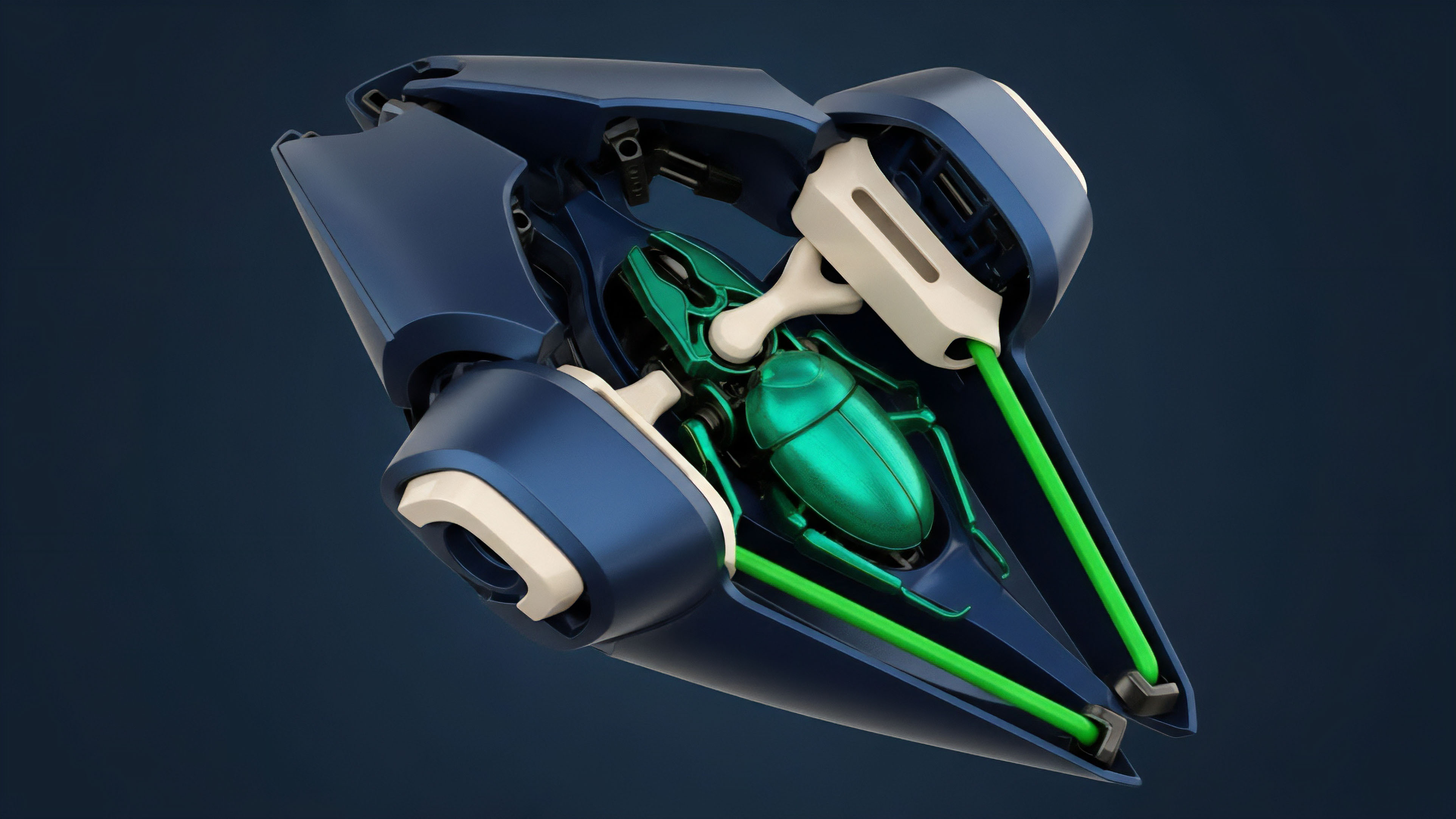
Another significant challenge is the design of the liquidation engine. In a private system, a liquidator cannot see the exact position details of a user. The protocol must be designed to allow liquidators to submit a ZK-proof that demonstrates a specific position has fallen below its margin threshold without revealing the position’s identity or full details.
This requires careful design to prevent front-running by liquidators themselves, ensuring that the liquidation process remains fair and efficient. The design of a private liquidation engine is a critical area of ongoing research.
- Latency vs. Privacy: The time required to generate complex proofs can add latency to trade execution, which is detrimental to options markets where pricing changes rapidly.
- Computational Cost: The high computational resources needed for proof generation can centralize the role of provers, potentially creating a new form of centralization risk.
- Trusted Setup: For zk-SNARKs, the initial setup requires trust in the participants to destroy certain cryptographic parameters, a potential vulnerability if not executed properly.
Evolution
The evolution of Zero-Knowledge Security in derivatives markets reflects a shift from a focus on privacy as a feature to privacy as a foundational layer for market efficiency. Initially, ZK-proofs were viewed as a mechanism to hide transaction details from public view. The current thinking re-frames ZK-proofs as a tool to improve market microstructure by eliminating information asymmetry.
The public ledger creates an adversarial environment where information is extracted as value; ZK-proofs create a neutral environment where information cannot be extracted.
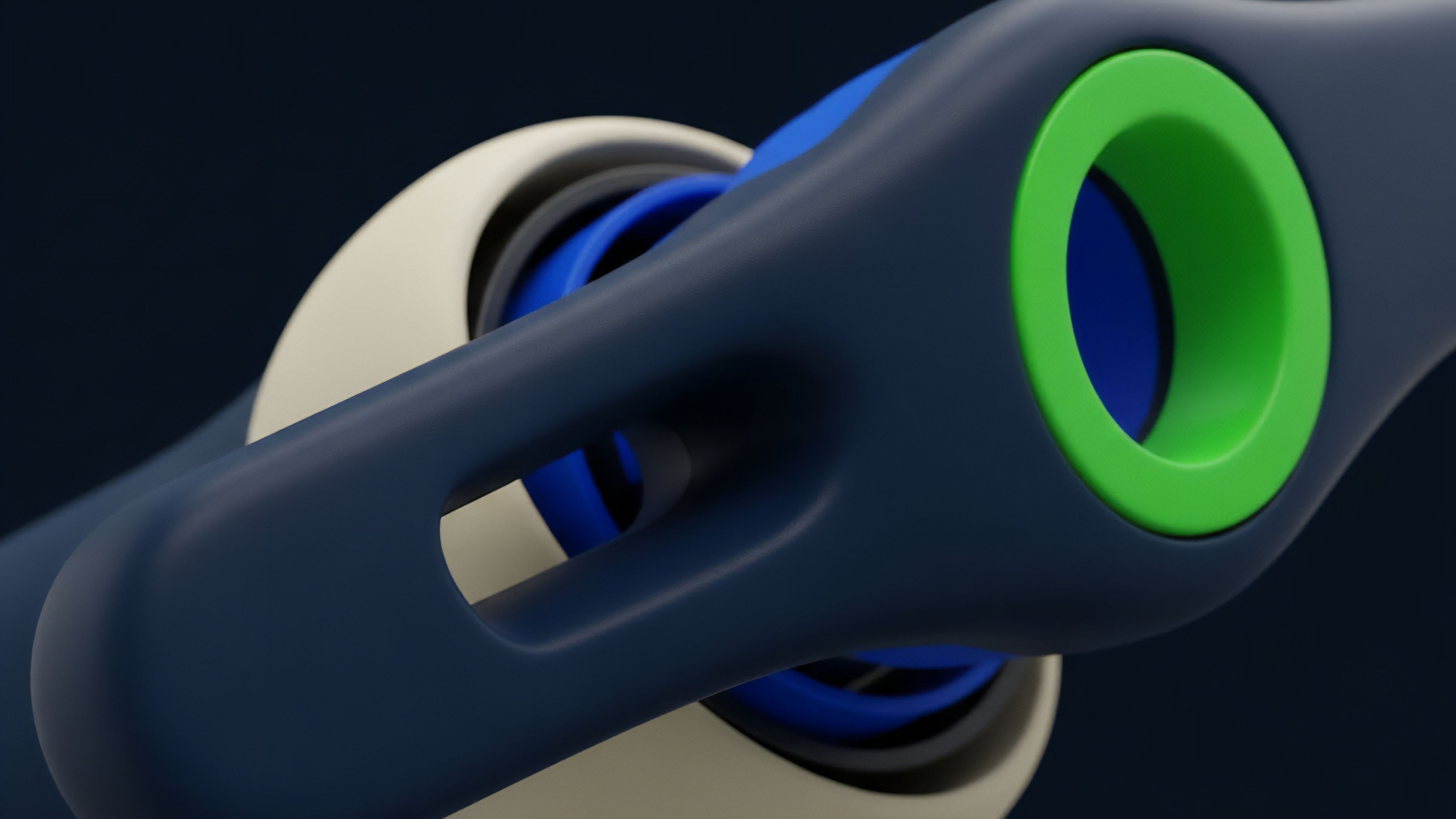
This evolution is driving a change in the design of decentralized exchanges. We are moving from “transparent DEXs” to “verifiable DEXs.” In a transparent DEX, the public nature of the order book allows anyone to see pending orders, leading to front-running and MEV. In a verifiable DEX using ZK-proofs, orders are submitted privately, and the protocol only reveals the execution details.
This fundamental change in market design reduces systemic risk and increases capital efficiency. The progression from simple privacy-preserving transactions to complex, privacy-preserving state changes represents a critical step toward a truly resilient decentralized financial ecosystem.
The shift from transparent public ledgers to verifiable private computations redefines the core assumptions of decentralized market microstructure.
A key aspect of this evolution is the transition from ZK-proofs as a scaling tool to a security primitive. While zk-Rollups are effective scaling solutions, their true impact lies in enabling complex financial logic to run securely off-chain. This allows protocols to offer more complex options products that require dynamic pricing models and sophisticated risk management, which were previously infeasible on Layer 1 due to computational limitations and information leakage.
The next stage of this evolution involves integrating ZK-proofs directly into the core logic of financial protocols, rather than treating them as an external scaling layer.

Horizon
Looking forward, the integration of Zero-Knowledge Security will lead to the emergence of truly permissionless and capital-efficient options markets. The next generation of protocols will leverage ZK-proofs to create fully private collateral management systems where a user’s entire portfolio and risk profile remain confidential, yet verifiable by the protocol’s risk engine. This enables sophisticated risk-weighted margin requirements that are currently only feasible in traditional finance.
The most significant long-term impact lies in the potential for regulatory arbitrage and new compliance models. If a user can prove they meet certain regulatory criteria (e.g. being an accredited investor, residing outside a sanctioned jurisdiction) without revealing their identity, it creates a new paradigm for compliance. This concept of zk-KYC allows for a separation between identity verification and data privacy, offering a pathway for protocols to adhere to global regulations without compromising user anonymity.
This approach could significantly reshape how decentralized finance interacts with traditional financial systems.
However, this path is not without its challenges. The primary risk on the horizon is the potential for hidden leverage. If positions and collateral are fully private, it becomes difficult for external auditors or regulators to assess systemic risk and contagion.
A hidden buildup of leverage across multiple protocols could lead to cascading liquidations that are invisible until they occur. The solution to this lies in a new class of ZK-proofs that allow for aggregate risk analysis without revealing individual position details. This requires a shift in thinking from individual privacy to systemic verifiability.
The future of ZK-enabled options markets requires a new set of tools for risk analysis and financial oversight. The industry must develop methods to calculate total value locked (TVL) and market risk without direct access to individual account data. This necessitates the creation of new mathematical frameworks for calculating aggregate risk in a private environment.
The transition from public, transparent markets to private, verifiable markets will redefine the financial operating system, creating both immense opportunities for efficiency and significant new challenges for risk management.

Glossary

Security Token Offering
Consensus Mechanism Security

Proactive Security Posture

Options Protocol Security

Security Considerations for Defi Applications
Collateral Security in Defi Protocols

1-of-N Security Model
Protocol Security Best Practices Guide

Protocol Security Audit Standards