Essence
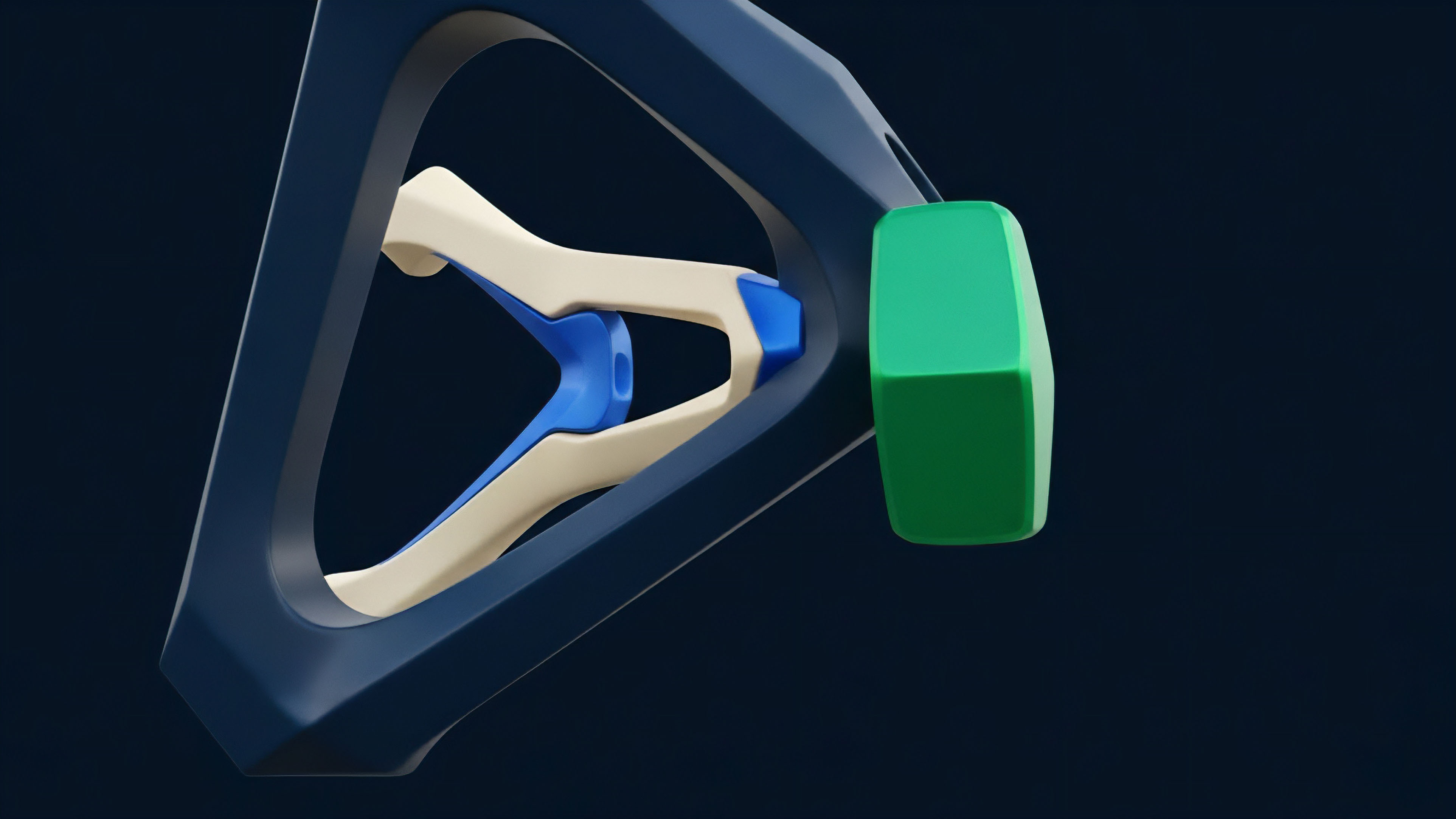
Silicon represents the final frontier of protocol sovereignty. Cryptographic ASIC Design transforms abstract mathematical proofs into physical reality, etching the rules of consensus directly into semiconductor gates. This hardware specialization eliminates the inefficiencies of general-purpose computing, providing a dedicated execution layer where the cost of a computation is minimized and the speed is maximized.
Within the adversarial environment of decentralized markets, these circuits function as the immutable enforcement mechanism for financial settlement.
The physical architecture of a circuit defines the ultimate efficiency limit for any cryptographic protocol.
Fixed-function logic replaces the flexible but slow instruction sets of traditional processors. By stripping away every transistor that does not contribute to the specific cryptographic primitive ⎊ be it SHA-256, Keccak, or Poseidon ⎊ the designer creates a device with a singular purpose. This specialization results in a massive increase in hash rate per watt, a metric that dictates the economic viability of network security.
In the context of derivatives, this hardware ensures that the underlying settlement layer remains resistant to reorganization, providing the finality required for complex options contracts. The relationship between silicon and protocol is symbiotic. A protocol’s security budget is physically manifested in the global fleet of ASICs dedicated to its maintenance.
This hardware layer creates a barrier to entry that is measured in gigawatts and petahashes, moving the security of the network from the digital realm into the physical world of energy and matter. Cryptographic ASIC Design is the process of defining this physical barrier, ensuring that the cost to subvert the system remains orders of magnitude higher than the potential gain.

Origin
The transition from general-purpose silicon to specialized hardware followed a predictable path of economic necessity. Early participants utilized Central Processing Units for validation, but the competitive nature of proof-of-work soon necessitated the parallel processing power of Graphics Processing Units.
As the difficulty adjusted and the stakes rose, the industry moved toward Field Programmable Gate Arrays, which offered a middle ground between flexibility and efficiency. However, the ultimate destination was always the Cryptographic ASIC Design, where the logic is permanently hard-coded. Historical data shows that the shift to ASICs coincided with the professionalization of the market.
The move from hobbyist hardware to industrial-scale silicon marked the end of the amateur era and the beginning of the institutional phase of digital assets. This transition was driven by the need for capital efficiency; those who could produce more hashes with less electricity secured a larger share of the block reward.
| Hardware Era | Primary Processor | Efficiency Metric | Market Participant |
|---|---|---|---|
| CPU Era | General Purpose Intel/AMD | Low Hash/Watt | Hobbyists |
| GPU Era | NVIDIA/AMD Parallelism | Medium Hash/Watt | Early Pools |
| FPGA Era | Xilinx/Altera Programmable | High Hash/Watt | Specialized Firms |
| ASIC Era | Custom Fixed-Function | Ultra-High Hash/Watt | Industrial Miners |
This hardware lineage reflects a broader trend in financial history where the speed of execution becomes the primary competitive advantage. Just as high-frequency traders moved their servers closer to the exchange to reduce latency, cryptographic participants moved their logic closer to the silicon to reduce energy waste. Cryptographic ASIC Design is the logical conclusion of this race for efficiency, where the software and hardware become one.

Theory
The theoretical framework of Cryptographic ASIC Design rests on the principles of logic gate optimization and thermal dynamics.
At the transistor level, the goal is to minimize the path length of the signal through the circuit. Each additional gate adds latency and consumes power. By designing a circuit that only performs the specific bitwise operations required by a hash function ⎊ such as XOR, AND, and bit rotations ⎊ the designer can pack millions of these units onto a single die.
Efficiency in specialized silicon is achieved by eliminating the overhead of instruction fetching and decoding.

Logic Path Optimization
In a general processor, a significant portion of the silicon area is dedicated to managing the flow of instructions. In an ASIC, this overhead is absent. The data flows through a fixed pipeline of gates, with each stage performing a part of the cryptographic algorithm.
This pipeline allows for massive throughput, as new data can enter the start of the pipeline before the previous data has finished the entire process. This parallelization is the source of the ASIC’s dominance.

Thermal and Power Constraints
Power density is the primary limiting factor in chip performance. As transistors switch, they generate heat. If the heat cannot be dissipated, the chip will fail.
Cryptographic ASIC Design must account for the voltage drop across the die and the thermal gradients that emerge during high-intensity operations. Designers utilize advanced cooling solutions and power delivery networks to maintain stability at high clock speeds. The relationship between voltage, frequency, and power consumption is non-linear, requiring a precise balance to achieve the lowest Joules per Terahash.
| Parameter | General Purpose CPU | Cryptographic ASIC |
|---|---|---|
| Logic Type | Programmable/Flexible | Fixed/Hard-coded |
| Throughput | Sequential/Limited | Massively Pipelined |
| Power Efficiency | Low (High Overhead) | Maximum (Zero Overhead) |
| Development Cost | High (Amortized) | Very High (Niche) |

Approach
The methodology for creating these circuits involves a multi-stage engineering process that begins with high-level algorithmic description and ends with physical manufacturing. Cryptographic ASIC Design requires deep expertise in both cryptography and semiconductor physics. The process is characterized by high upfront capital expenditure and long lead times, making it a high-stakes endeavor for any firm.
- Register Transfer Level Description: The cryptographic algorithm is translated into a hardware description language like Verilog or VHDL.
- Logic Synthesis: The description is converted into a netlist of specific logic gates available in the manufacturer’s library.
- Floorplanning and Placement: The physical location of each gate on the silicon die is determined to minimize signal delay.
- Clock Tree Synthesis: A distribution network is created to ensure the clock signal reaches every transistor simultaneously.
- Routing and Verification: The physical wires connecting the gates are drawn, and the design is tested against the original algorithmic specification.
Once the design is verified, it undergoes a tape-out process where the masks for the lithography machines are produced. Manufacturing typically occurs at advanced foundries like TSMC or Samsung, utilizing the latest process nodes such as 5nm or 3nm. The choice of node size directly impacts the energy efficiency and the number of chips that can be produced per wafer.
A successful Cryptographic ASIC Design must also incorporate robust error correction and thermal throttling mechanisms to ensure longevity in the harsh environment of a data center.

Evolution
The progression of specialized hardware has moved from simple hash-rate maximization to more complex forms of computational acceleration. Initially, the industry focused exclusively on SHA-256 for Bitcoin. However, the rise of alternative consensus mechanisms and privacy-preserving technologies has expanded the scope of Cryptographic ASIC Design.
We are now seeing the emergence of chips designed for Zero-Knowledge proofs and Verifiable Delay Functions.
The shift from hashing to proof-generation represents the next phase of hardware-protocol integration.

Process Node Migration
The rapid advancement of semiconductor manufacturing has forced a continuous cycle of hardware replacement. Older ASICs become economically obsolete as newer, more efficient models enter the market. This creates a high-velocity capital cycle where miners must constantly reinvest in the latest Cryptographic ASIC Design to remain competitive.
This cycle has profound implications for the centralization of the network, as only those with access to cheap capital and the latest hardware can survive.

Algorithmic Hardening
Some protocols have attempted to resist ASIC dominance by utilizing memory-hard algorithms. These algorithms require large amounts of RAM, which is expensive to include on an ASIC die. However, the history of Cryptographic ASIC Design shows that hardware engineers eventually find ways to optimize even the most resistant algorithms.
The result is a perpetual arms race between protocol designers and hardware manufacturers.
- Phase One: Simple bitwise operations (SHA-256).
- Phase Two: Memory-intensive operations (Scrypt, Ethash).
- Phase Three: Complex mathematical proofs (ZK-SNARKs, STARKs).
- Phase Four: Fully Homomorphic Encryption acceleration.

Horizon
The future of specialized silicon lies in the democratization of design and the expansion of use cases. As open-source hardware initiatives gain traction, we may see a shift away from the current oligopoly of ASIC manufacturers. This could lead to more transparent and auditable hardware, reducing the risk of hidden backdoors or kill-switches.
Cryptographic ASIC Design will likely become more accessible, allowing smaller players to produce custom silicon for specific niche applications. Furthermore, the integration of ASICs into the broader financial infrastructure will continue. We can expect to see specialized hardware embedded in high-frequency trading servers and exchange matching engines to provide real-time cryptographic verification.
This will reduce the latency of decentralized derivatives, bringing them closer to the performance levels of centralized venues. The ultimate goal is a world where the physical layer of the internet is natively cryptographic.
Zero Knowledge Acceleration
The most significant area of growth is in ZK-ASICs. These chips are designed to accelerate the generation of complex proofs, a process that is currently too slow for many real-world applications. By moving proof generation from software to Cryptographic ASIC Design, we can achieve massive gains in scalability and privacy.
This will enable a new generation of decentralized applications that are both private and high-performance.

Systemic Resilience
As the world becomes more dependent on digital assets, the resilience of the hardware layer becomes a matter of systemic importance. Cryptographic ASIC Design must evolve to resist physical attacks and supply chain disruptions. This may involve the development of decentralized foundries or the use of novel materials that are less dependent on rare-earth elements. The security of the global financial system will increasingly depend on the integrity of the silicon it runs on.

Glossary

High Frequency Trading Hardware

Hardware Root of Trust

Hardware Security Module

Specialized Hardware

Latency Optimization

Zero-Knowledge Acceleration
Specialized Silicon

Gate Array

Application-Specific Integrated Circuit