Essence
The structural integrity of decentralized finance relies on a delicate equilibrium between public auditability and strategic confidentiality. Hybrid Privacy Models represent the architectural synthesis designed to resolve the transparency paradox, where the absolute openness of a distributed ledger becomes a systemic liability for institutional participants. In high-stakes environments like crypto options markets, total transparency exposes trade intent, strike price concentrations, and expiration sensitivities to predatory actors.
Hybrid Privacy Models introduce a selective visibility layer, allowing for the cryptographic proof of solvency and compliance while shielding the specific parameters of a position from the broader market.
Hybrid privacy models reconcile the structural requirement for public solvency with the strategic necessity of private execution.
This framework functions as a sophisticated filter for information flow. By utilizing Zero-Knowledge Primitives, a protocol can verify that a market maker maintains sufficient collateral to cover a short volatility position without revealing the exact hedge ratio or the underlying delta-hedging strategy. This preservation of Information Asymmetry is vital for maintaining market depth.
Without it, the cost of liquidity provision increases as participants demand a premium to compensate for the risk of being front-run by automated agents monitoring the mempool. Hybrid Privacy Models transform privacy from a binary state into a programmable variable, enabling a new class of Dark Pool Derivatives that mirror the efficiency of legacy finance within a trustless environment.

Information Decay and Strategic Protection
The value of a proprietary trading strategy decays rapidly when exposed to a public blockchain. Hybrid Privacy Models mitigate this decay by ensuring that the Execution Logic remains encrypted during the matching process. This architectural choice protects the Alpha Generation of sophisticated funds, fostering a more robust and diverse ecosystem of liquidity providers.
The systemic implication is a reduction in Volatility Spikes caused by herd behavior, as the market cannot easily identify and exploit the liquidation thresholds of large-scale participants. Selective Disclosure mechanisms allow these same participants to reveal their positions only to authorized auditors or regulatory bodies, fulfilling the dual mandate of market privacy and legal accountability.
Origin
The genesis of Hybrid Privacy Models lies in the historical failure of extremist privacy and transparency archetypes. Early blockchain iterations offered a choice between the radical transparency of Bitcoin and the total obfuscation of Monero.
Neither extreme supported the complex requirements of Derivative Settlement. Institutional capital avoided transparent chains due to the risk of Strategy Leakage, while regulators viewed total obfuscation as a vehicle for systemic risk and illicit activity. The industry required a middle path that could satisfy the Solvency Verification needs of the market and the Privacy Rights of the individual.

Transition from Obfuscation to Programmable Privacy
The development of ZK-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) provided the mathematical breakthrough necessary for this transition. Originally conceptualized in academic cryptography during the late 20th century, these tools found practical application in the quest for On-Chain Confidentiality. The realization that one could prove the validity of a statement without revealing the statement itself changed the trajectory of Protocol Physics.
Developers began to move away from simple mixers and toward Privacy-Preserving Smart Contracts that could handle complex financial logic, such as the Black-Scholes pricing of an option, within a shielded environment.
The mathematical foundation of selective disclosure allows protocols to prove compliance without exposing sensitive trade parameters to adversarial actors.
This evolutionary shift was accelerated by the rise of Maximal Extractable Value (MEV) on public networks. As traders realized that every transaction was a target for sandwich attacks and censorship, the demand for Shielded Order Flow became a survival imperative. Hybrid Privacy Models emerged as the standard for professional-grade decentralized exchanges, moving beyond the “privacy as a crime” narrative to “privacy as a market efficiency feature.” This shift mirrored the evolution of the traditional Dark Pool, adapted for the cryptographic constraints of a decentralized ledger.

Theory
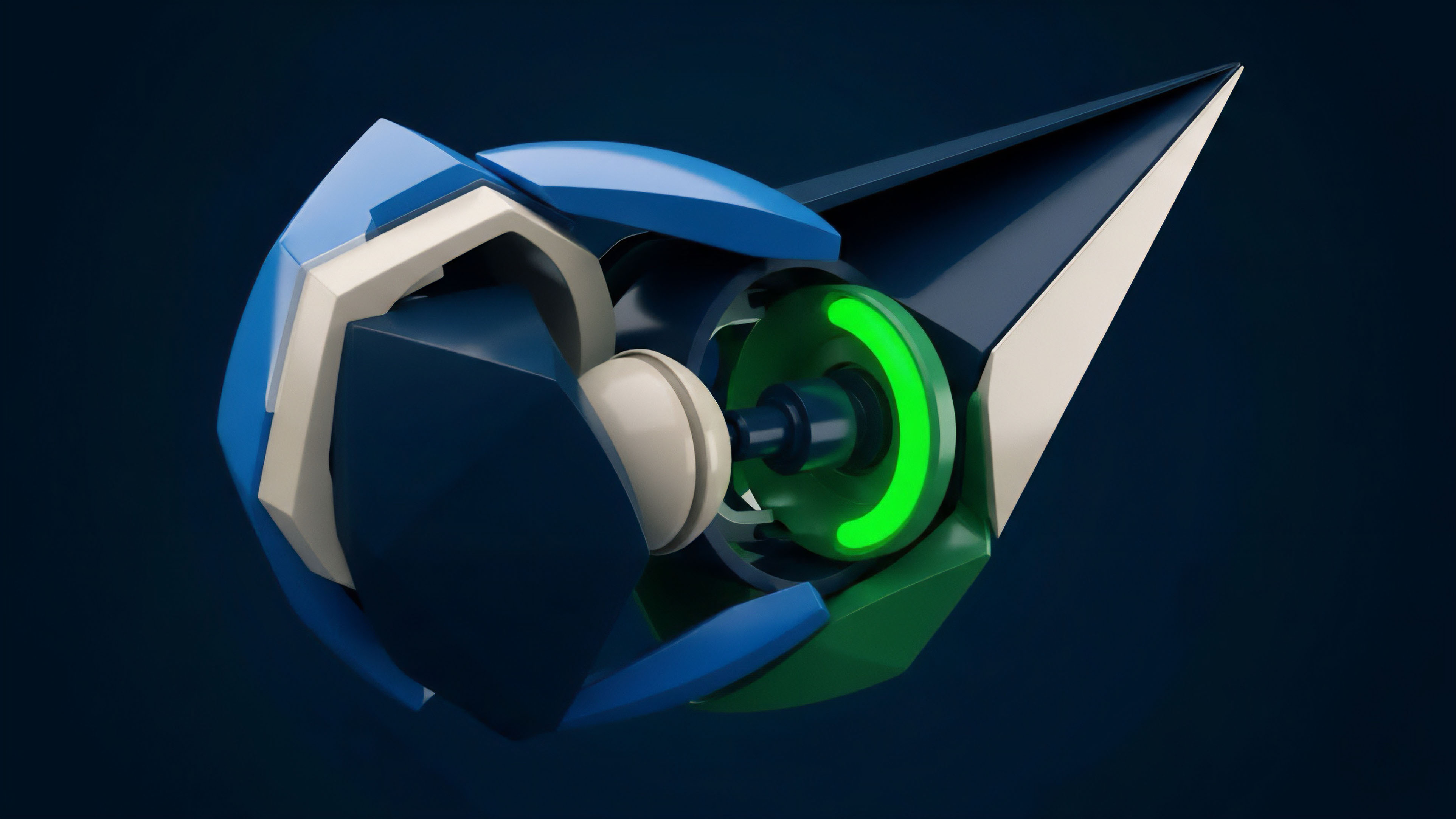
The theoretical framework of Hybrid Privacy Models is built upon the decoupling of State Transition from State Visibility.
In a standard blockchain, the state (account balances, contract data) is visible to all nodes to ensure validity. In a hybrid model, the state is divided into public and private partitions. Cryptographic Commitments are used to link these partitions, ensuring that while the details of a transaction are hidden, the overall integrity of the system remains verifiable.
This is achieved through a combination of Commit-and-Reveal Schemes and Recursive Proofs, which allow for the compression of complex private computations into small, publicly verifiable certificates.

Privacy Primitives and Performance Tradeoffs
The choice of cryptographic primitive determines the Latency Profile and Security Assumptions of the model. Each approach offers a different balance of computational overhead and privacy depth.
| Primitive | Mechanism | Market Impact | Primary Constraint |
|---|---|---|---|
| ZK-SNARKs | Zero-knowledge proofs of transaction validity | Eliminates front-running by shielding order details | High computational cost for proof generation |
| FHE | Computation directly on encrypted data | Enables private automated market makers (AMMs) | Significant latency and throughput limitations |
| MPC | Distributed computation across multiple parties | Secures institutional custody and trade execution | Requires high-bandwidth communication between nodes |
| TEEs | Hardware-based secure execution environments | Fast execution for high-frequency options trading | Reliance on hardware manufacturer security |
Adversarial Game Theory in Shielded Environments
Within a Hybrid Privacy Model, the game theory shifts from public competition to Probabilistic Interaction. Participants must model the market based on Partial Information, which reduces the efficacy of predatory algorithms that rely on perfect visibility. This environment encourages Fundamental Analysis over simple mempool sniping.
The Margin Engine of a hybrid options protocol must be designed to handle Private Liquidations, where the protocol can prove a position is underwater and trigger a close-out without revealing the user’s entire portfolio to the liquidator. This prevents Cascading Liquidations driven by market participants intentionally pushing prices toward known trigger points.
Approach
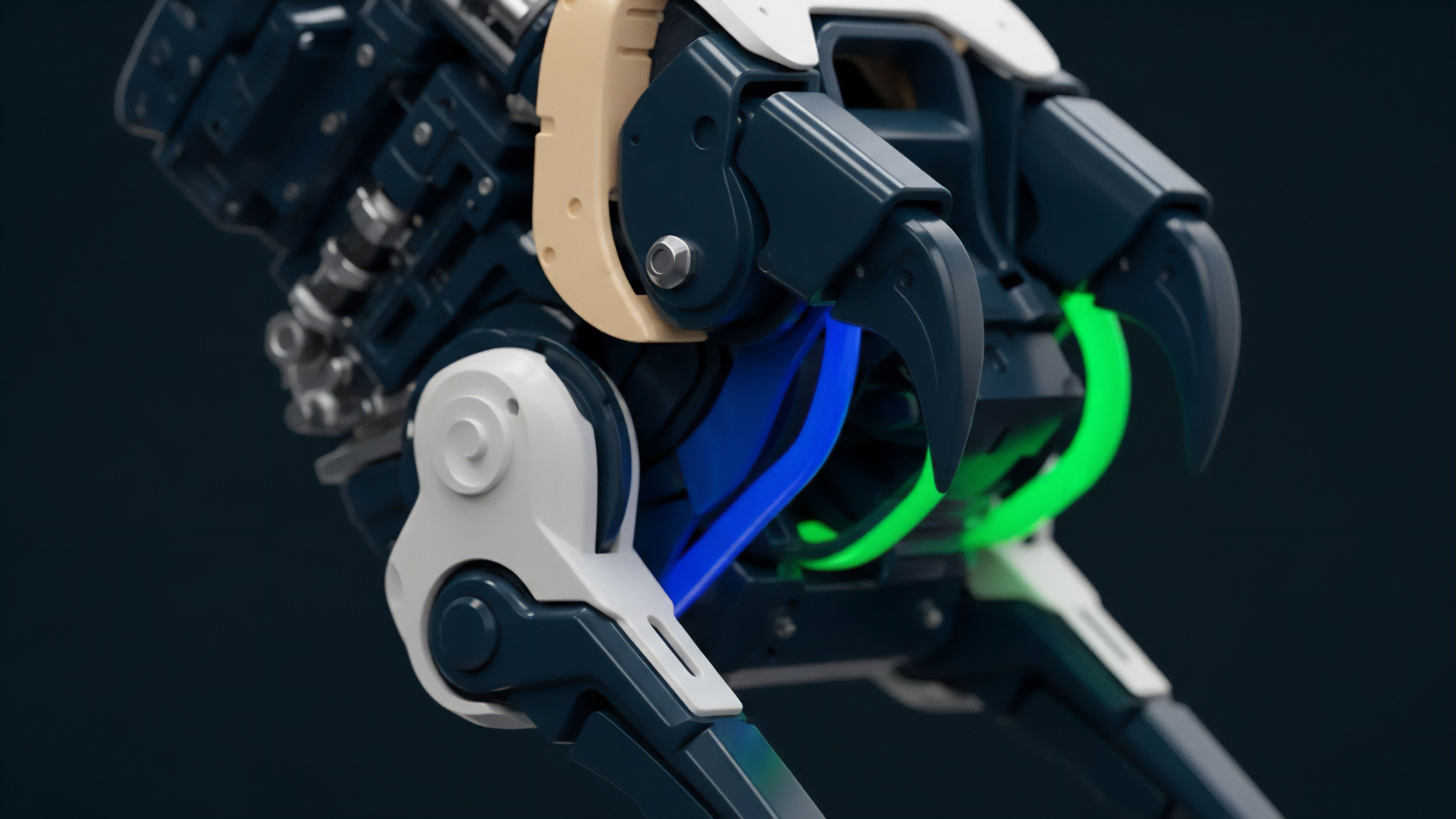
Implementing Hybrid Privacy Models requires a multi-layered technical stack that integrates Shielded Pools with public liquidity. The standard approach involves a Privacy Layer (often a Layer 2 or a specialized sidechain) where users deposit assets to generate Privacy-Preserving Notes.
These notes represent the underlying value but do not reveal the owner’s identity or transaction history. When a user trades an option, the transaction logic is executed within a ZK-Circuit, which outputs a proof that the trade was valid according to the protocol’s rules (e.g. sufficient collateral, valid strike price).
- Shielded Order Books utilize Pedersen Commitments to hide the size and price of limit orders until they are matched.
- Selective Disclosure Key Management allows users to share a viewing key with a specific third party for Regulatory Reporting.
- Private Oracle Integration ensures that price feeds are consumed without leaking the timing or frequency of a trader’s price checks.
- Decentralized Sequencers with Threshold Encryption prevent the operator from seeing or reordering transactions before they are batched.
Information leakage in transparent order books creates a systemic tax on institutional liquidity through predatory front-running and MEV extraction.

Quantitative Risk Management in Private Markets
The Quantitative Analyst must adapt traditional risk metrics to account for Hidden Gamma and Shadow Delta. In a transparent market, the aggregate Option Greeks of all participants can be estimated, providing a roadmap for potential market moves. In a Hybrid Privacy Model, these metrics become obscured.
Risk managers must rely on Statistical Inference and Volatilty Surface Analysis to estimate the positioning of the market. This creates a more resilient system where the “crowded trade” is less visible, reducing the risk of Systemic Contagion during periods of high market stress.
| Risk Metric | Transparent Market State | Hybrid Privacy State |
|---|---|---|
| Delta Exposure | Directly observable via public wallet addresses | Inferred through net price movement and volume |
| Liquidation Risk | Visible at specific price points on-chain | Hidden; triggered by ZK-proofs of insolvency |
| MEV Vulnerability | High; transactions are vulnerable in the mempool | Low; transaction details are encrypted until execution |
| Counterparty Risk | Auditable through public history | Verified via ZK-proofs of historical performance |

Evolution
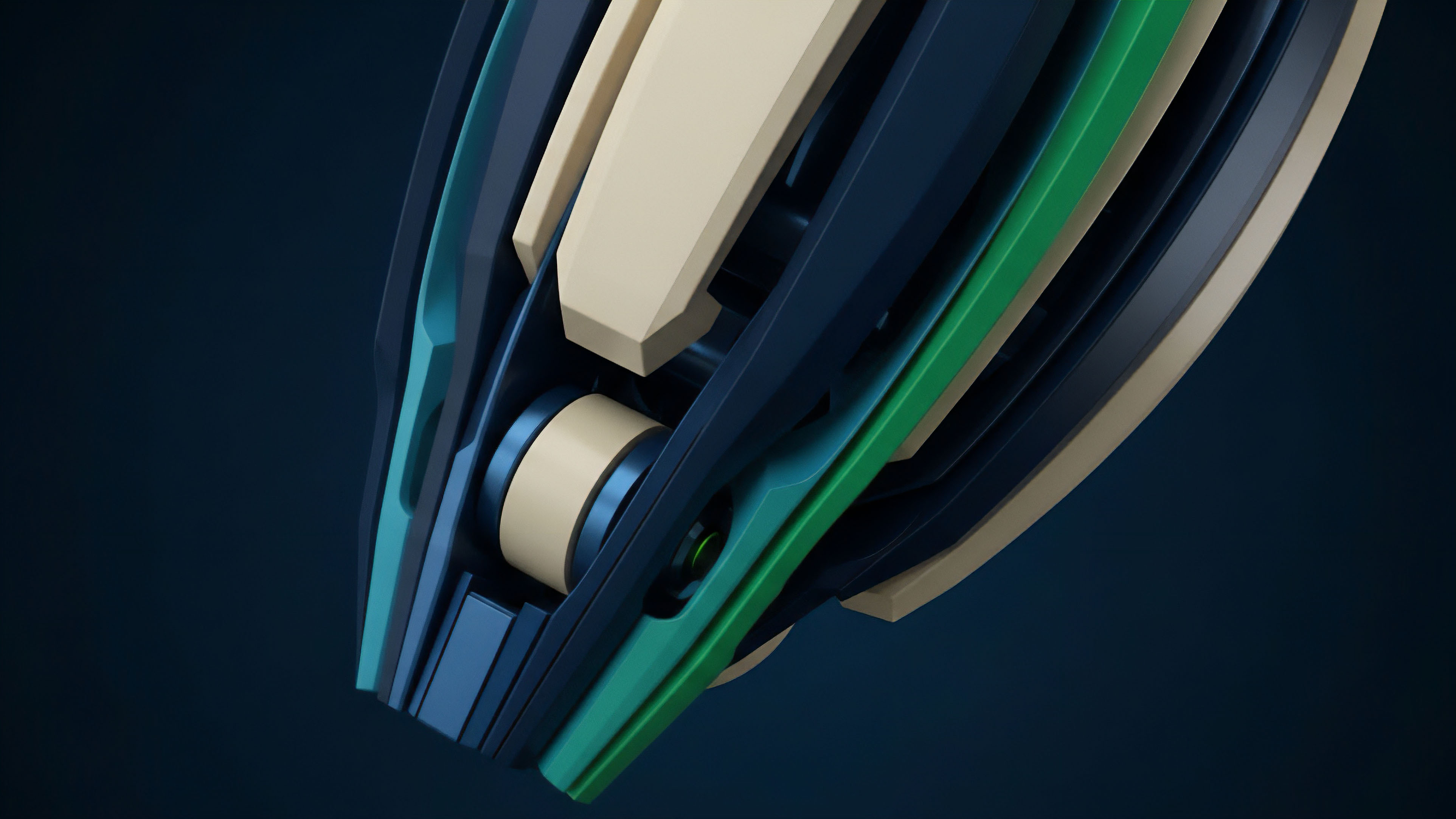
The trajectory of Hybrid Privacy Models has moved from experimental novelties to Institutional Infrastructure. Initially, privacy was viewed as an obstacle to Capital Efficiency because the computational overhead of generating proofs led to slow execution times. However, the development of Hardware Acceleration (ASICs and FPGAs specifically for ZK-proofs) has drastically reduced this friction.
We have transitioned from simple Private Transfers to Confidential Smart Contracts capable of managing complex Derivative Workflows, including automated delta-hedging and multi-leg option strategies.
Regulatory Synthesis and the End of Anonymity
The narrative has shifted from Total Anonymity to Compliant Privacy. The industry has realized that for Hybrid Privacy Models to survive, they must integrate with existing Legal Frameworks. This led to the creation of Identity-Aware Privacy Layers, where users undergo KYC/AML verification to receive a Soulbound Token or a ZK-proof of identity.
This proof allows them to access the shielded pool without revealing their personal data to the public, while still providing the protocol with a mechanism to ban malicious actors or comply with Subpoena Requests. This evolution marks the maturation of the space, moving away from the “wild west” toward a Sovereign Financial System that respects both privacy and the rule of law.
Financial History and the Dark Pool Precedent
The evolution of Hybrid Privacy Models rhymes with the development of Dark Pools in the 1980s and 90s. Traditional markets moved toward Off-Exchange Trading to allow large blocks of shares to be traded without causing massive price swings. Crypto is repeating this history but with Cryptographic Guarantees instead of legal contracts.
The shift from Centralized Dark Pools (which require trust in the operator) to Decentralized Hybrid Models (which require trust in the math) represents a significant leap in Market Microstructure. This transition is dismantling the Information Monopoly held by large centralized exchanges and redistributing it to the protocol level.

Horizon
The future of Hybrid Privacy Models is inextricably linked to the advancement of Fully Homomorphic Encryption (FHE). While currently limited by high latency, FHE will eventually allow for Encrypted State Interaction, where an entire Options Clearinghouse can operate on encrypted data.
This would mean that even the protocol’s smart contracts would not “know” the details of the trades they are processing, yet they would still be able to enforce margin requirements and execute liquidations with mathematical certainty. This is the ultimate destination for Sovereign Finance: a system that is perfectly transparent in its rules but perfectly private in its execution.

Cross-Chain Privacy and Liquidity Aggregation
We are moving toward a Multi-Chain Privacy Fabric where liquidity can flow between different Shielded Environments without losing its privacy properties. Cross-Chain ZK-Proofs will allow a trader to use collateral on one chain to back an option position on another, with the entire transaction remaining confidential. This will solve the current Liquidity Fragmentation problem, as Hybrid Privacy Models become the standard interface for all high-value transactions.
The distinction between “private” and “public” chains will fade, replaced by a unified Privacy-Enabled Infrastructure.

Systemic Implications for Global Markets
The widespread adoption of Hybrid Privacy Models will fundamentally alter Price Discovery. As more order flow moves into shielded environments, the public tape will reflect only the final Settlement Prices, rather than the messy process of Order Matching. This will reduce Market Noise and lead to more stable Volatility Surfaces. Strategically, this empowers the individual and the smaller institution to compete with High-Frequency Trading firms on a more level playing field, as the Speed Advantage of HFT is neutralized by the Information Shield of the hybrid model. The result is a more resilient, efficient, and equitable Global Derivative Market.
Glossary

Selective Disclosure

Range Proofs

Privacy Preserving Compliance

Capital Efficiency

Market Microstructure

Systemic Contagion
Zero Knowledge Settlement

Trusted Execution Environments

Liquidity Fragmentation