Essence
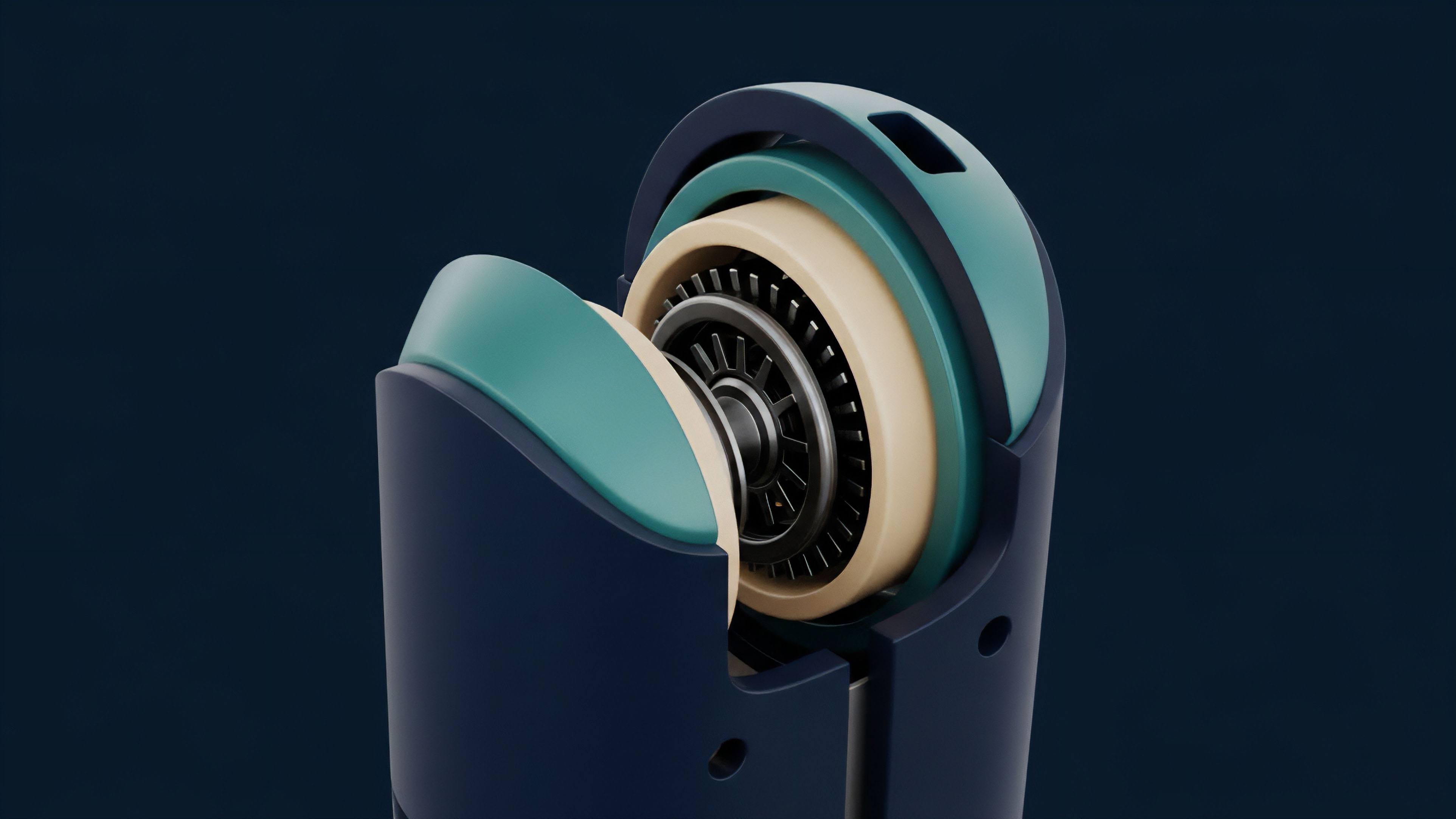
The Hardware Security Module represents the physical anchor of digital sovereignty. It functions as a hardened perimeter where private keys exist in total isolation from general-purpose operating systems. Within the architecture of crypto derivatives, the Hardware Security Module acts as the final arbiter of transaction validity.
It ensures the signing of complex option contracts or liquidation events occurs within a tamper-proof environment. This physical isolation provides the certainty required for institutional participants to deploy capital into decentralized markets.
Physical isolation remains the only verifiable method for securing cryptographic primitives against remote extraction.
Trust in digital asset markets relies on the mathematical certainty of private key ownership. The Hardware Security Module secures this ownership by preventing the exposure of the key to the external network. Even during the signing process, the private key remains within the internal circuitry of the device.
This architecture eliminates the risk of memory scraping or remote code execution attacks that plague software-based custody solutions.
Physical Trust Anchors
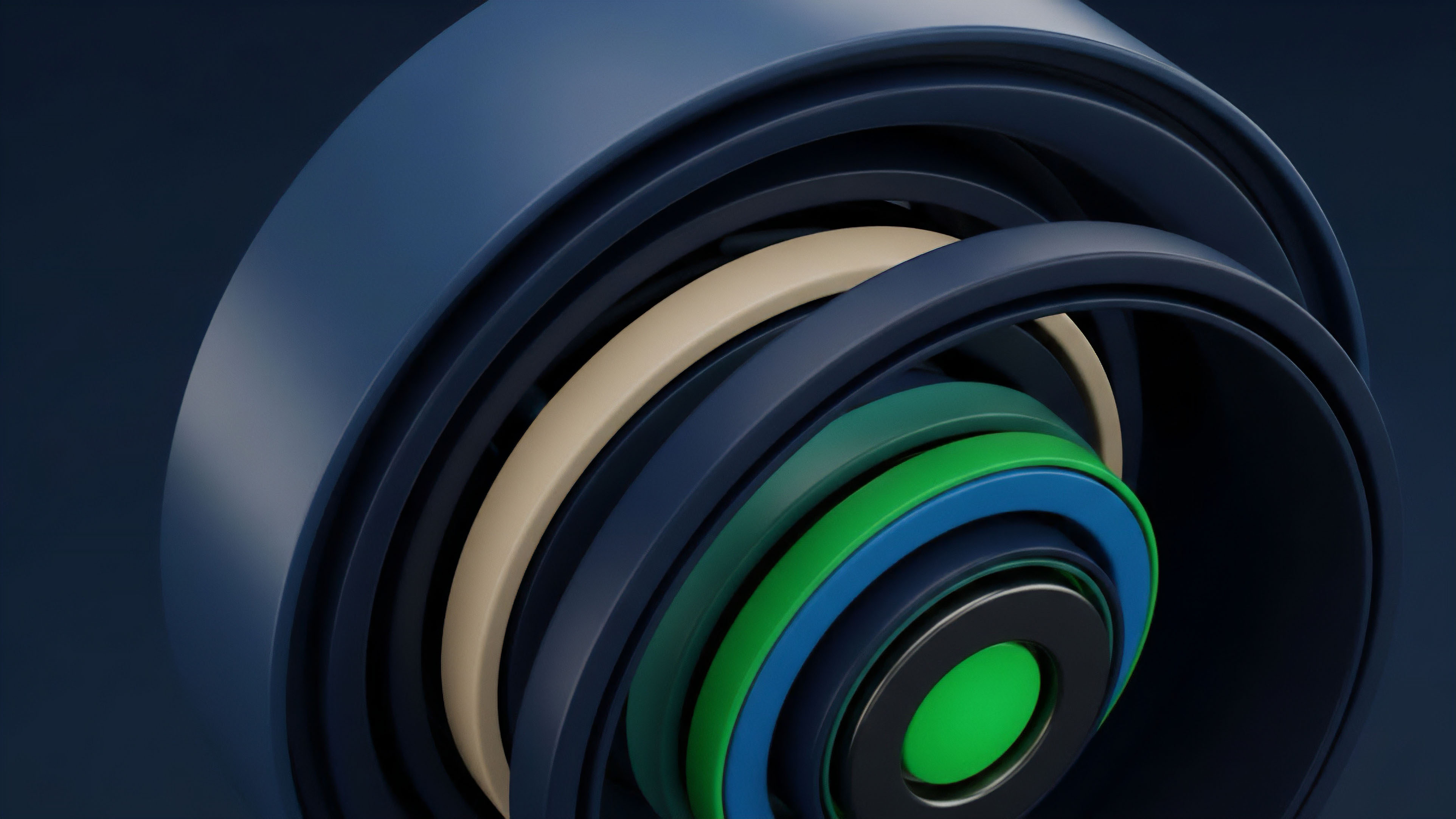
The Hardware Security Module utilizes specialized processors designed for high-performance cryptographic operations. These processors handle the heavy mathematical load of elliptic curve digital signature algorithms (ECDSA) and Edwards-curve digital signature algorithms (EdDSA). By offloading these tasks to dedicated hardware, systems maintain high throughput while keeping sensitive material behind a physical barrier.
- Tamper Detection: Physical sensors monitor the integrity of the module and trigger data erasure upon intrusion.
- Entropy Generation: Hardware-based random number generators provide non-deterministic seeds for key creation.
- Access Control: Role-based authentication restricts administrative functions to authorized personnel only.

Origin
The lineage of the Hardware Security Module traces back to the high-stakes requirements of national security and global finance. Early iterations appeared to protect the integrity of the SWIFT network and the security of credit card transactions. As digital assets moved from experimental scripts to multi-billion dollar option markets, the requirement for a physical root of trust became apparent.
The transition from software-based wallets to institutional-grade Hardware Security Module deployment marked the professionalization of the industry.
The transition from software-defined security to hardware-anchored trust defines the institutionalization of digital asset markets.
Financial history shows that systemic failures often stem from the compromise of centralized trust points. Traditional banking solved this through vault-based security and physical ledgers. In the digital era, the Hardware Security Module serves as the modern vault.
It translates physical security into cryptographic assurance. The adoption of FIPS 140-2 standards by crypto custodians reflects the convergence of legacy financial security and decentralized technology.

Standards Evolution
Regulatory bodies and industry groups established rigorous testing protocols to certify the efficacy of these devices. These standards define the levels of physical and logical protection required for various use cases.
| FIPS 140-2 Level | Security Requirements | Primary Application |
|---|---|---|
| Level 1 | Standard cryptographic software without physical security. | Personal desktop applications. |
| Level 2 | Tamper-evident coatings or seals to show physical access. | Low-risk corporate environments. |
| Level 3 | Tamper resistance and response to physical intrusion. | Institutional crypto custody and clearing. |
| Level 4 | Physical envelope protection against environmental attacks. | National security and high-value settlements. |

Theory
The technical architecture of a Hardware Security Module centers on the principle of cryptographic isolation. These devices utilize specialized hardware to generate high-entropy random numbers, which are vital for creating secure private keys. Unlike standard servers, an Hardware Security Module features physical security measures like epoxy potting and sensors that detect temperature fluctuations or physical intrusion.
These sensors trigger an immediate erasure of sensitive data upon detection of an attack.
Entropy generation within a hardened boundary prevents the predictability of private key derivation.
Mathematical modeling of Hardware Security Module performance focuses on the trade-off between signing latency and cryptographic strength. In derivatives markets, where price discovery happens in milliseconds, the signing speed of an Hardware Security Module determines the efficiency of a margin engine. If the module cannot sign liquidation orders fast enough, the system faces insolvency risk during periods of high volatility.
Cryptographic Primitives
The Hardware Security Module manages the lifecycle of keys, from generation to destruction. This lifecycle occurs entirely within the secure boundary. The device exposes only a limited API, such as PKCS#11, which allows external applications to request signatures without ever seeing the underlying key material.

Side Channel Mitigation
Attackers often attempt to deduce private keys by measuring the physical properties of a device during operation. An Hardware Security Module includes countermeasures against these side-channel attacks.
- Power Analysis Defense: Internal voltage regulators mask power consumption fluctuations during signing.
- Timing Attack Defense: Constant-time algorithms ensure that the duration of a calculation does not reveal information about the key.
- Electromagnetic Shielding: Metal enclosures prevent the leakage of signals that could be captured by external sensors.
Approach
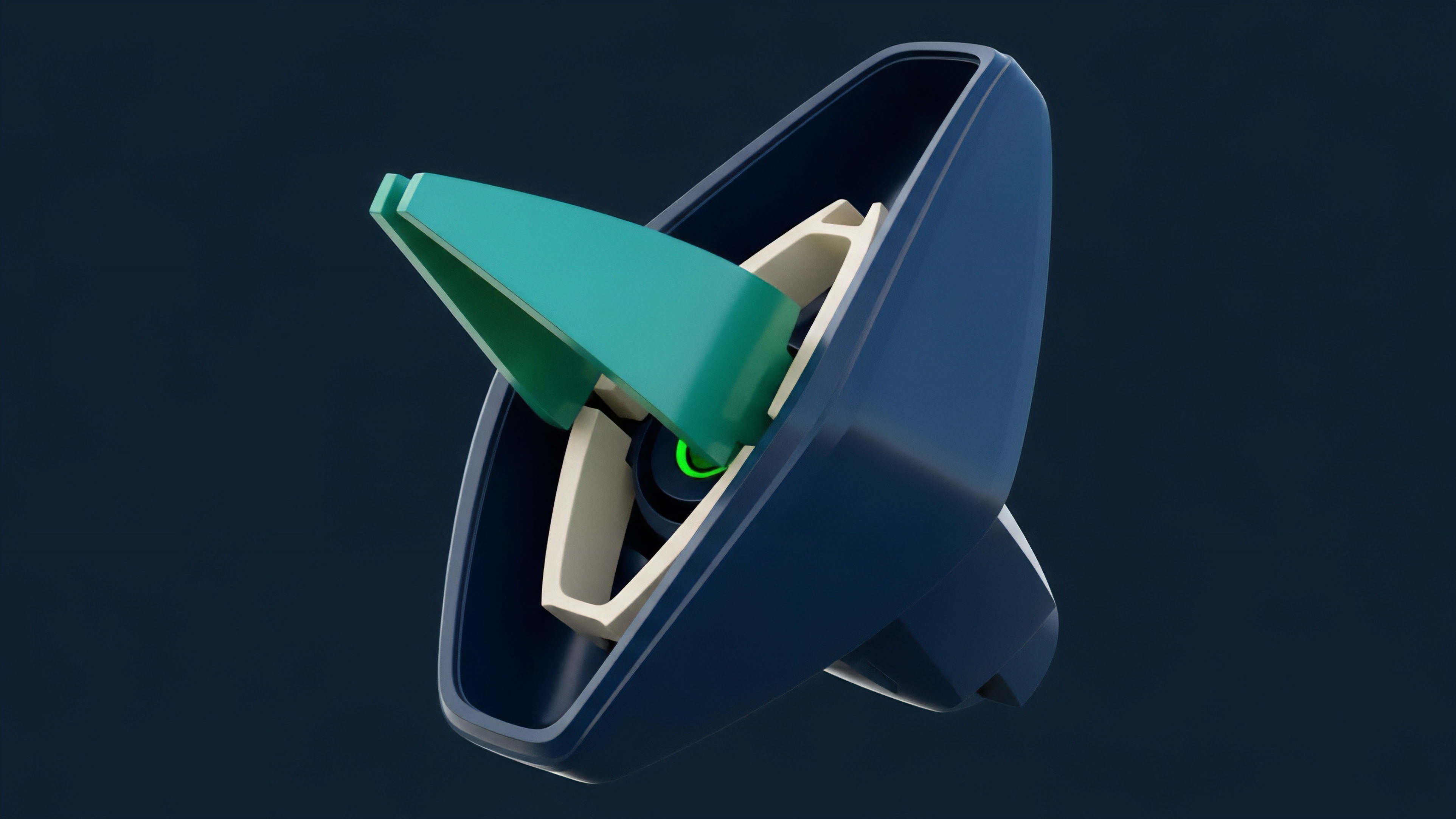
Modern derivatives platforms utilize the Hardware Security Module in various configurations to balance security with execution speed. High-frequency trading environments require low-latency signing, often necessitating the use of specialized network-attached modules. These devices reside in the same data centers as the exchange matching engines to minimize round-trip time.
Operational Configurations
The choice of deployment affects the capital efficiency and risk profile of a trading desk. Custodians often combine Hardware Security Module technology with multi-party computation (MPC) to create hybrid security models.
| Security Model | Signing Speed | Physical Requirement | Primary Risk |
|---|---|---|---|
| Cold HSM | Very Low | High | Operational Delay |
| Warm HSM | Medium | Medium | Network Exposure |
| MPC-HSM Hybrid | High | Low | Protocol Logic Error |

Key Management Policies
Administrators define strict policies for how the Hardware Security Module interacts with the broader network. These policies are often hardcoded into the firmware to prevent unauthorized changes.
- Quorum Approval: Multiple administrators must authorize the generation or export of keys.
- Whitelisting: The module only signs transactions destined for pre-approved addresses.
- Velocity Limits: The system restricts the total value signed within a specific timeframe.

Evolution
The transition from physical on-premise hardware to cloud-based Hardware Security Module services has altered the risk profile of digital asset custody. Cloud providers now offer dedicated instances that allow for rapid scaling of signing operations without the overhead of maintaining physical data centers. This shift enables smaller market participants to access institutional-grade security that was previously reserved for the largest banks.

Cloud Migration Risks
While cloud-based modules offer flexibility, they introduce new variables into the security equation. The reliance on a third-party provider for physical security requires a high degree of trust in the provider’s operational integrity. Market participants must verify that the cloud Hardware Security Module offers true hardware isolation rather than a virtualized instance sharing resources with other tenants.
Trusted Execution Environments
The rise of Trusted Execution Environments (TEEs) provides an alternative to traditional Hardware Security Module hardware. TEEs utilize secure enclaves within a standard CPU to perform sensitive operations.
- Scalability: TEEs can be deployed across thousands of servers simultaneously.
- Cost Efficiency: Lower hardware costs compared to dedicated modules.
- Attack Surface: Higher risk of software-level vulnerabilities compared to hardened hardware.

Horizon
The future of the Hardware Security Module lies in the integration of post-quantum cryptographic algorithms and the acceleration of zero-knowledge proofs. As quantum computing threats move from theoretical models to physical realities, the ability of these modules to upgrade their underlying mathematical primitives will determine the longevity of current financial architectures. The next generation of Hardware Security Module will likely include specialized ASICs for zero-knowledge proof generation, enabling private and scalable derivative settlements.
Post Quantum Readiness
The Hardware Security Module must adapt to lattice-based cryptography and other quantum-resistant methods. This transition requires significant upgrades to the internal processing power of the modules, as these new algorithms are computationally more demanding than current elliptic curve standards.
| Algorithm Type | Current Standard | Quantum Resistance | Hardware Impact |
|---|---|---|---|
| Elliptic Curve | ECDSA | None | Low Latency |
| Lattice-Based | Dilithium | High | High Memory Usage |
| Hash-Based | SPHINCS+ | High | Large Signature Size |
The convergence of hardware security and decentralized finance will lead to the creation of “DeFi-native” Hardware Security Module instances. These devices will interact directly with on-chain smart contracts, providing a hardware-anchored oracle for off-chain data and private key management. This integration will reduce the friction between institutional custody and permissionless liquidity pools, fostering a more resilient global financial system.
Glossary

Transaction Validity

Quantum-Resistant Algorithms

Derivative Settlement Security
Hardware Security Module

Private Keys

Lattice-Based Cryptography

Institutional-Grade Security
Digital Asset Security

High-Frequency Trading Security