
Essence
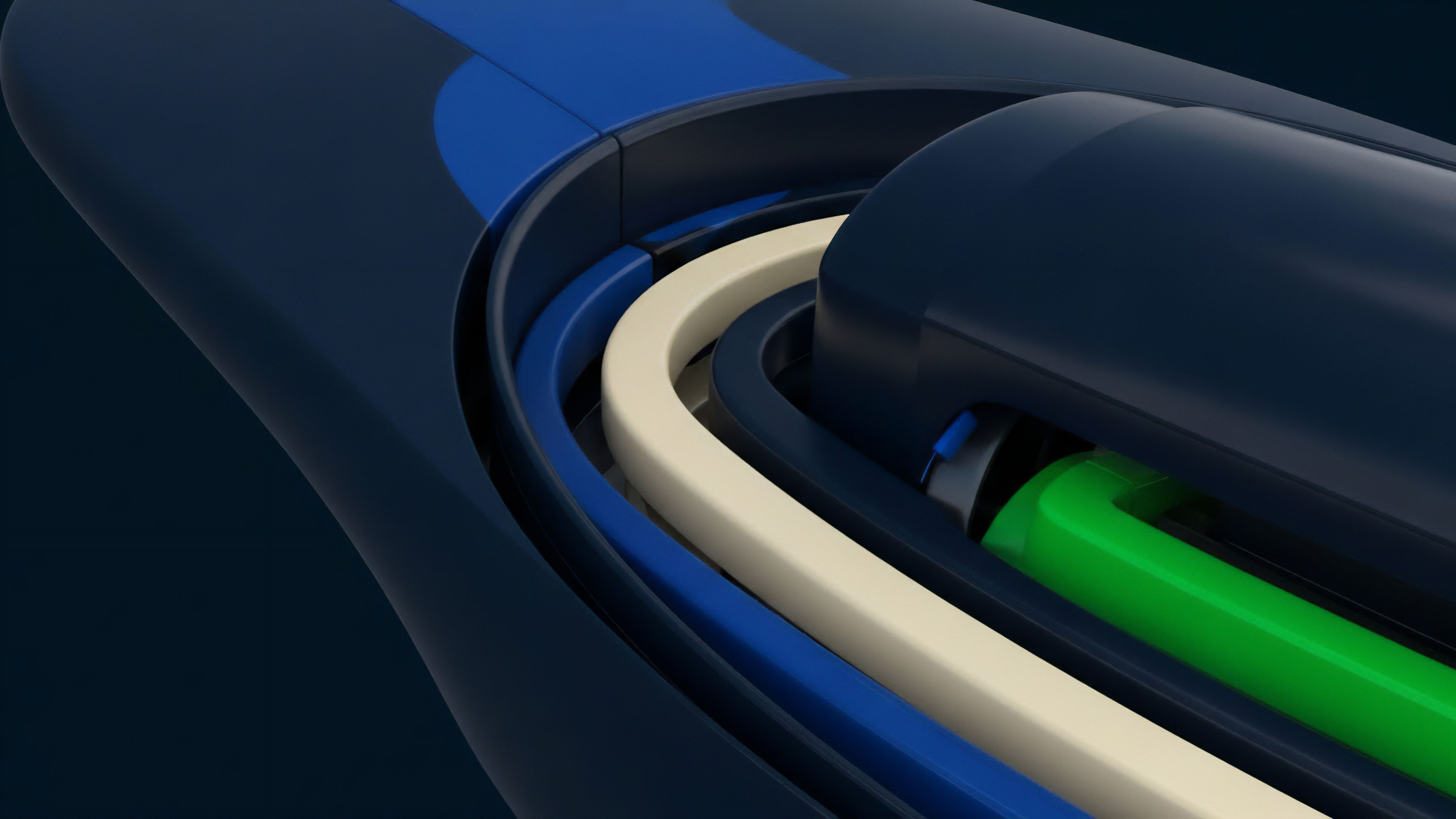
The visibility of order flow in public ledgers acts as a structural tax on liquidity providers. Zero-Knowledge LOBs function as a cryptographic shield, enabling the execution of limit orders without broadcasting intent to the entire network before a trade occurs. This architecture separates the matching logic from the settlement layer, ensuring that trade details remain confidential while the validity of the transaction remains verifiable by the blockchain.
By decoupling order matching from public data availability, Zero-Knowledge LOBs resolve the tension between transparency and front-running protection. Traders submit encrypted orders to an off-chain matching engine which then generates a validity proof. This proof confirms that the engine followed the prescribed matching rules and that all participants possess sufficient collateral without revealing individual positions or price levels.
Zero-Knowledge LOBs utilize cryptographic proofs to validate order matching and margin solvency without exposing sensitive trade data to the public ledger.
The primary utility of this system lies in its ability to offer the performance of a centralized exchange with the non-custodial security of a decentralized protocol. Professional participants can deploy complex strategies ⎊ including high-frequency market making and large-scale delta hedging ⎊ without fear of predatory actors observing their movements in the mempool. This cryptographic sovereignty is the foundation for a more resilient and efficient derivative market.

Origin
The inception of private order books stems from the inherent limitations of transparent automated market makers and public central limit order books.
Early decentralized exchanges faced persistent threats from front-running and sandwich attacks, where predatory actors exploited the latency between order broadcast and block inclusion. Professional market makers found the exposure of their proprietary strategies to be an unacceptable cost of participation in decentralized finance. As the demand for complex instruments like options and perpetuals grew, the need for high-performance matching engines became undeniable.
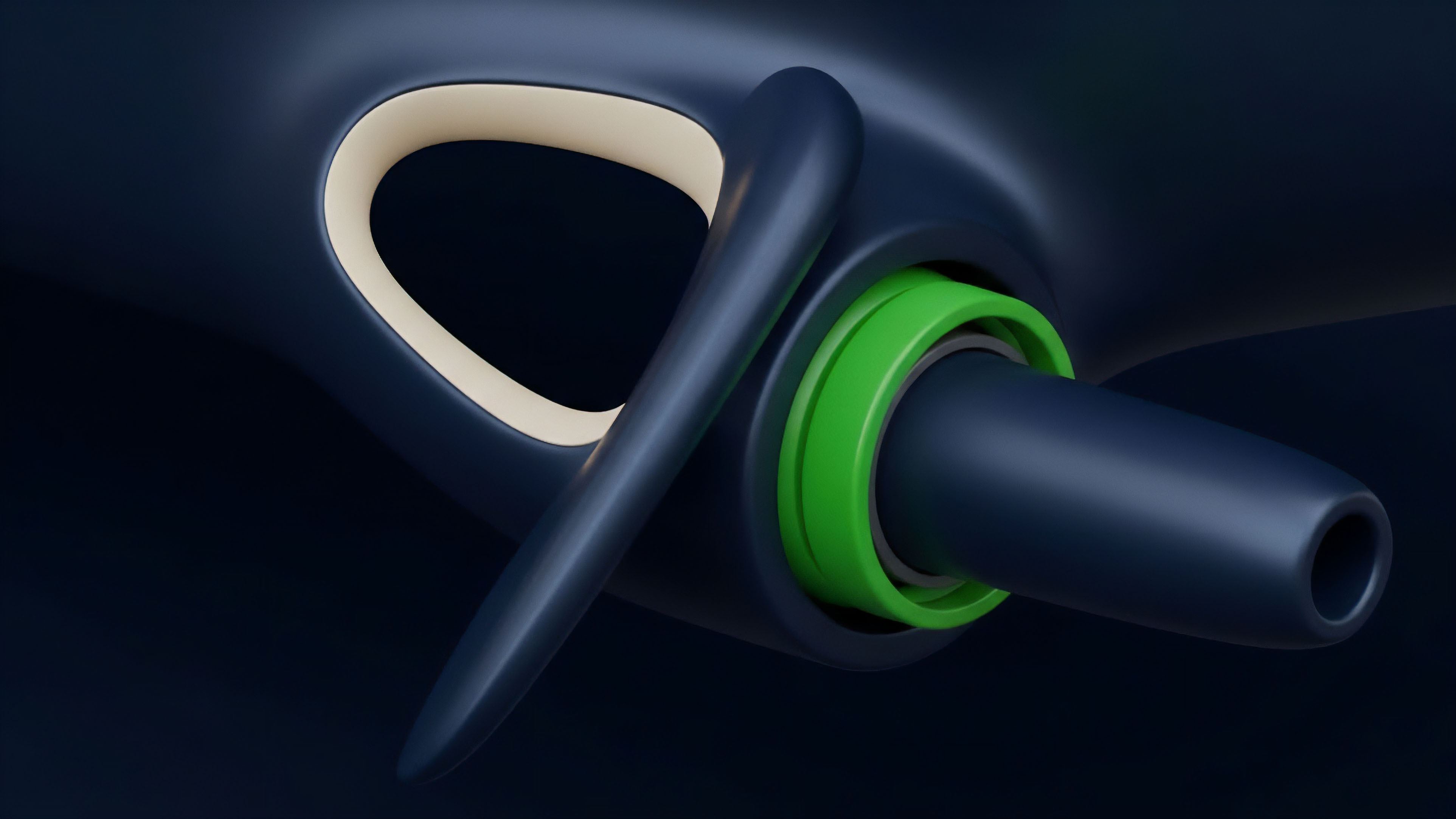
Public blockchains, constrained by block times and gas costs, could not support the throughput required for active derivative trading. This led to the development of off-chain matching solutions, yet these early iterations required users to trust a centralized operator. The convergence of zero-knowledge cryptography and layer 2 scaling provided the technical path to remove this trust requirement.
The transition from transparent liquidity pools to shielded order books represents a maturation of the digital asset environment. It reflects a shift toward institutional-grade infrastructure where privacy is not an elective feature but a requirement for market stability. By adopting proofs of validity, the industry moved away from the “don’t be evil” mantra of centralized entities toward a “can’t be evil” mathematical certainty.

Theory
Mathematical proofs ensure that every trade within Zero-Knowledge LOBs adheres to the rules of the matching engine.
The system utilizes zero-knowledge succinct non-interactive arguments of knowledge to prove that the state transition ⎊ from an open order to a matched trade ⎊ was executed correctly according to the price-time priority of the book. This allows the blockchain to verify the integrity of the entire exchange without processing every individual transaction. Information entropy in physics mirrors the leakage of alpha in transparent markets; just as a system loses energy to its surroundings, a trader loses edge to the observing network.
Zero-Knowledge LOBs minimize this entropy by keeping the order book state private. Only the updated state root and the corresponding proof are submitted to the settlement layer. This ensures that the information content of the public ledger remains low, preserving the strategic value of participant data.

Risk Management and Margin Engines
The margin engine within a Zero-Knowledge LOBs structure must operate on encrypted data. It uses range proofs to verify that a user’s collateral remains above the maintenance margin threshold. This is vital for options trading, where the non-linear nature of Greeks ⎊ specifically Gamma and Vega ⎊ requires frequent re-evaluation of account health.
- Prover Node: This component generates the cryptographic evidence that the matching engine followed the protocol rules and that all margin requirements were met.
- State Root: A cryptographic commitment representing the current balances and open orders of all participants in the system.
- Verifier Contract: A smart contract on the base layer that checks the validity of the submitted proofs before updating the global state.
- Price Feed Oracle: Provides external market data to the margin engine to calculate real-time solvency without revealing user positions.
The integration of zero-knowledge proofs into limit order books enables the verification of complex financial state transitions while maintaining complete data confidentiality for all participants.
Adversarial game theory suggests that in a transparent environment, the dominant strategy for well-capitalized actors is to exploit the information revealed by smaller participants. By introducing privacy, Zero-Knowledge LOBs alter the incentive structure, favoring participants who provide genuine liquidity over those who seek to extract value through informational advantages. This leads to tighter spreads and deeper order books, benefiting the entire network.

Approach
Current implementations utilize off-chain matching engines that generate validity proofs for on-chain verification.
This hybrid model allows for the high-frequency execution required for complex derivatives while maintaining the security guarantees of the underlying settlement layer. The methodology focuses on maximizing throughput and minimizing the latency of proof generation, which is the primary bottleneck for real-time trading.
| Feature | Automated Market Maker | Centralized LOB | Zero-Knowledge LOBs |
|---|---|---|---|
| Execution Privacy | None | Partial (to Operator) | Full (Cryptographic) |
| Throughput | Low | High | High |
| Settlement | On-chain | Off-chain | On-chain (via Proof) |
| Front-running Risk | High | Medium | Low |
The deployment of Zero-Knowledge LOBs often involves dedicated app-chains or layer 2 environments optimized for cryptographic operations. These venues provide the necessary computational resources for the prover nodes to function efficiently. Traders interact with these systems through standard APIs, but their signatures are used to authorize encrypted state changes rather than public transactions.
By separating the matching logic from the verification layer, Zero-Knowledge LOBs achieve a balance between the speed of centralized systems and the trustless nature of decentralized protocols.
Tactical execution in these environments requires a shift in how liquidity is managed. Market makers must ensure their local state remains synchronized with the off-chain engine while monitoring the settlement finality on the base layer. The use of recursive proofs allows for multiple batches of trades to be compressed into a single verification, significantly reducing the gas cost per trade and enabling the scaling of complex option strategies.
Evolution
The progression of these systems moved from simple private swaps to complex margin engines capable of handling cross-margined options and perpetuals.
Initial designs were limited by the computational overhead of proof generation, but advancements in recursive proof systems have significantly reduced latency. This transition has enabled the support of multi-asset collateral and sophisticated risk models that were previously impossible in a private decentralized setting.

Scaling and Efficiency Gains
The shift from SNARKs to STARKs in some protocols has improved scalability by removing the need for a trusted setup and offering faster proving times for large batches of data. This has been a significant development for high-volume derivative venues where thousands of orders must be processed per second. The ability to generate proofs in parallel has further decreased the time between execution and settlement finality.
- Phase One: Introduction of private settlement for simple spot trades on layer 2.
- Phase Two: Development of zero-knowledge margin engines for perpetual contracts with basic leverage.
- Phase Three: Implementation of full-scale Zero-Knowledge LOBs for options with multi-dimensional risk proofs.
- Phase Four: Integration of cross-chain liquidity via shared sequencers and unified proof verification.
Early iterations often struggled with data availability, as the cost of posting enough data to reconstruct the state was prohibitive. The transition toward Validium and Volition models allowed users to choose between on-chain data availability for maximum security or off-chain data for lower costs. This flexibility has been a principal driver in the adoption of Zero-Knowledge LOBs by institutional participants who require high-volume execution.

Horizon
The future of these protocols lies in the integration of selective disclosure mechanisms for regulatory compliance.
This will allow institutions to prove they are meeting anti-money laundering requirements without revealing their entire trading history to the public. Such a system would enable a “compliant privacy” model, where the cryptographic proof includes an attestation from a verified identity provider.

Technological Convergence
The integration of hardware acceleration ⎊ specifically ASICs and FPGAs designed for zero-knowledge proof generation ⎊ will likely reduce latency to levels comparable with centralized exchanges. This will enable the growth of sub-millisecond private trading on-chain. Additionally, the development of cross-chain proof verification will allow Zero-Knowledge LOBs to aggregate liquidity from multiple networks, creating a unified and private global market for derivatives.
| Metric | Current State | Future Projection |
|---|---|---|
| Proof Generation Time | Seconds | Milliseconds |
| Cross-Chain Liquidity | Fragmented | Unified via Shared Proofs |
| Regulatory Interface | Manual/External | Native Selective Disclosure |
| Hardware Optimization | General Purpose CPU/GPU | Dedicated ZK-ASICs |
The transition toward sovereign order books will likely redefine the role of the exchange. Instead of acting as a custodian, the exchange becomes a service provider that facilitates matching and proof generation. This model minimizes systemic risk by ensuring that even if the exchange operator fails, the users retain control over their assets through the cryptographic proofs held on the base layer. The long-term trajectory points toward a fully private, high-performance, and compliant financial layer that operates independently of centralized intermediaries.

Glossary

Cryptographic Margin Requirements

Margin Solvency Proofs

Cryptographic Auditing

Polynomial Commitments

Adversarial Game Theory

Sandwich Attack Prevention

Prover Efficiency

Off-Chain Matching
Systemic Risk Mitigation






