Cryptographic Sovereignty Foundations
The architecture of Zero Knowledge Identity represents a tectonic shift in the management of sensitive metadata within decentralized financial systems. This framework allows a prover to demonstrate the validity of a specific claim ⎊ such as solvency, jurisdictional eligibility, or accredited investor status ⎊ without exposing the underlying data that supports the assertion. In an environment where transparency is often weaponized by predatory actors, Zero Knowledge Identity serves as the necessary shield for institutional-grade liquidity.
The systemic requirement for privacy in large-scale derivatives trading is absolute; without it, market participants face the constant risk of front-running and regulatory overreach.
- Data Minimization ensures that only the binary result of a verification process is shared with the counterparty.
- Sovereign Attestation empowers the individual to hold the keys to their own reputational and financial history.
- Computational Integrity guarantees that the proof provided is mathematically bound to the original dataset.
- Selective Disclosure permits the granular release of information based on specific protocol requirements.
Zero Knowledge Identity enables the verification of complex financial credentials while maintaining the absolute privacy of the underlying data.
The integration of Zero Knowledge Identity into the fabric of decentralized markets resolves the tension between regulatory compliance and the cypherpunk ideal of anonymity. By utilizing Zero Knowledge Proofs, protocols can enforce Know Your Customer (KYC) and Anti-Money Laundering (AML) standards without creating centralized honey pots of personal information. This architectural choice mitigates the systemic risk of identity theft and data breaches, which have plagued traditional finance for decades.
The move toward Zero Knowledge Identity is a transition from “trusting” a third party to “verifying” a mathematical proof.
Historical Convergence of Privacy and Math
The lineage of Zero Knowledge Identity traces back to the 1985 seminal work of Goldwasser, Micali, and Rackoff, which introduced the concept of interactive proof systems. These early mathematical frameworks demonstrated that it was possible to convey the truth of a statement without revealing any information beyond the statement’s validity. This discovery remained largely theoretical until the emergence of blockchain technology necessitated a way to scale transactions and preserve user privacy on public ledgers.
The development of ZK-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) provided the technical breakthrough required to implement these concepts in a non-interactive, highly efficient manner.
| Milestone | Technological Impact | Financial Relevance |
|---|---|---|
| GMR Paper 1985 | Foundational ZKP Theory | Conceptual Privacy Framework |
| Zcash Launch 2016 | First Large Scale Implementation | Private Asset Transfer |
| Tornado Cash 2019 | On-chain Privacy Pools | Liquidity Obfuscation |
| ZK-Rollups 2021 | Scalability and Proof Batching | High Frequency Trading Privacy |
The evolution of Zero Knowledge Identity was accelerated by the realization that pseudonymity is insufficient for institutional capital. Early adopters of Bitcoin and Ethereum discovered that the public nature of the ledger allowed for sophisticated chain analysis, making it possible to deanonymize large traders and expose their strategies. This vulnerability led to the creation of Privacy Preserving Identity layers that could wrap traditional identity documents into cryptographic hashes.
The objective shifted from hiding transactions to proving the legality of transactions while keeping the participants’ identities hidden from the public gaze.

Mathematical Mechanics and Circuit Logic
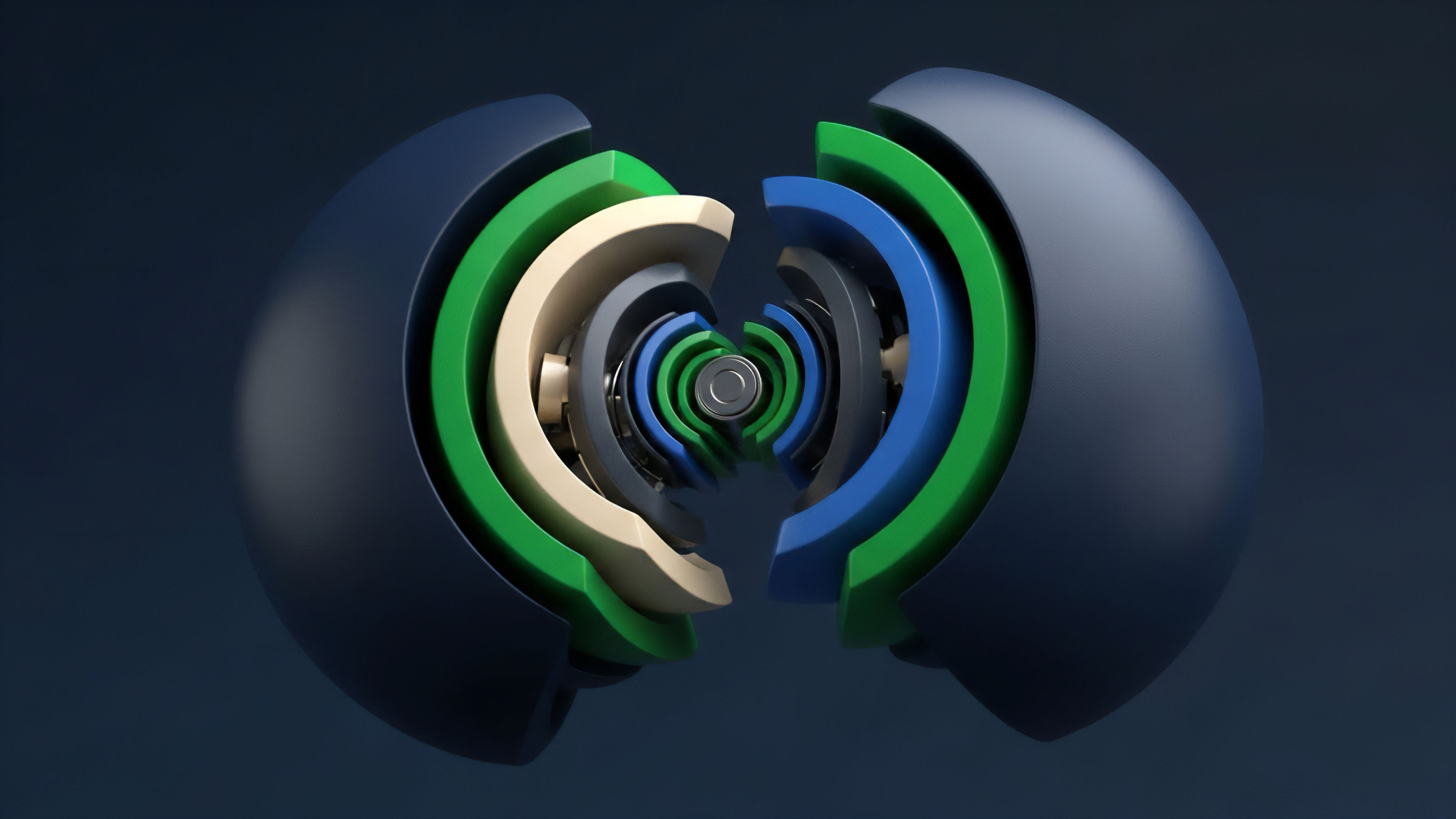
At the quantitative core of Zero Knowledge Identity lies the construction of arithmetic circuits that represent the logic of an identity claim. These circuits translate high-level statements ⎊ such as “the user is over 18 years old and resides in a permitted jurisdiction” ⎊ into a series of polynomial equations. The prover generates a witness, which is the private data that satisfies the circuit, and produces a proof that the witness exists without revealing it.
The verifier then checks this proof against a public key, a process that is computationally inexpensive and can be executed on-chain. This efficiency is vital for Options and Derivatives markets where latency and gas costs directly impact the profitability of hedging strategies.
The mathematical soundness of Zero Knowledge Identity ensures that false claims are statistically impossible to verify within the system.
The robustness of Zero Knowledge Identity is defined by three primary properties: completeness, soundness, and zero-knowledge. Completeness ensures that a true statement will always be accepted by the verifier. Soundness ensures that a false statement will be rejected with overwhelming probability.
Zero-knowledge ensures that the verifier learns nothing other than the fact that the statement is true. In the context of Derivative Liquidity, these properties allow for the creation of Undercollateralized Loans and Credit Default Swaps based on proven but private credit scores. The use of Polynomial Commitments and Fiat-Shamir Heuristics further refines the proof generation process, reducing the size of the proofs and making them more suitable for cross-chain interoperability.
The complexity of these systems often reminds me of the intricate clockwork of 18th-century horology ⎊ where every gear must align perfectly to produce a single, reliable output. This level of precision is required because a single flaw in the circuit logic can lead to total system failure or the leakage of private keys. Zero Knowledge Identity relies on Elliptic Curve Cryptography and Pairing-Based Cryptography to secure the communication between the prover and the verifier.
The security of the system is often tied to a Trusted Setup, although newer iterations like ZK-STARKs (Zero-Knowledge Scalable Transparent Argument of Knowledge) eliminate this requirement by using collision-resistant hash functions.
Implementation in Decentralized Markets
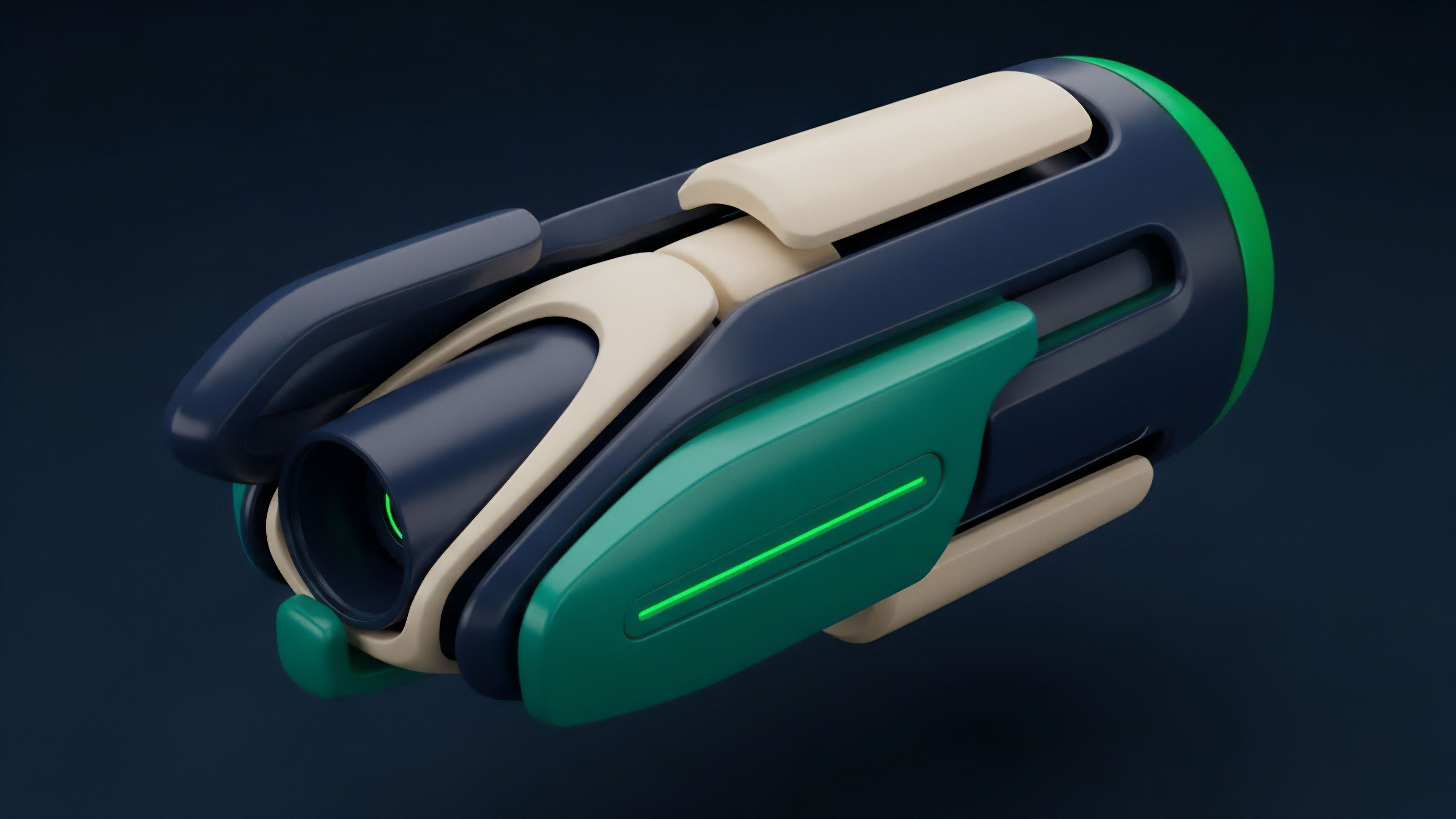
Current applications of Zero Knowledge Identity focus on the integration of Verifiable Credentials into the decentralized finance stack. Protocols utilize ZK-KYC modules to onboard users while maintaining a privacy-first approach. This is achieved by having a trusted issuer ⎊ such as a government agency or a regulated bank ⎊ sign a digital attestation.
The user then stores this attestation in a private wallet and generates a Zero Knowledge Proof whenever a protocol requires verification. This method eliminates the need for the protocol to store sensitive personal data, significantly reducing the surface area for regulatory liability and data breaches.
| Feature | Traditional Identity | Zero Knowledge Identity |
|---|---|---|
| Data Storage | Centralized Databases | User-Controlled Wallets |
| Verification Speed | Manual and Slow | Automated and Instant |
| Privacy Level | High Exposure Risk | Mathematically Guaranteed |
| Compliance | Rigid and Invasive | Flexible and Private |
The deployment of Zero Knowledge Identity in Options Trading venues allows for the creation of permissioned liquidity pools. These pools are restricted to participants who have proven their status as Sophisticated Investors or Market Makers. By ensuring that all participants are verified, these venues can offer higher leverage and lower margin requirements.
The Margin Engine of a decentralized exchange can query the Zero Knowledge Identity layer to confirm that a trader has the necessary risk profile to take on a specific position. This creates a more resilient market structure by filtering out participants who do not meet the requisite capital or expertise thresholds.
- Proof Generation occurs on the client side, ensuring that private data never leaves the user’s device.
- Recursive SNARKs allow for the compression of multiple identity proofs into a single, compact proof.
- On-chain Verification provides a trustless and immutable record that the identity check was performed.
- Revocation Registries enable issuers to invalidate credentials without compromising the user’s privacy.
Regulatory Adaptation and Technical Refinement
The trajectory of Zero Knowledge Identity has moved from experimental privacy tools to essential compliance infrastructure. Initially, the focus was on absolute anonymity, which often put protocols at odds with global financial regulators. However, the development of View Keys and Selective Auditability has allowed for a middle ground.
Regulators can now be granted access to specific transaction data under predefined conditions, such as a court order, while the general public remains unable to track the user’s activity. This evolution reflects a pragmatic approach to the reality of Global Financial Oversight.
The evolution of Zero Knowledge Identity shifts the focus from hiding information to providing verifiable evidence of compliance.
Technical refinements in Prover Efficiency have made Zero Knowledge Identity more accessible to mobile users. Early implementations required significant computational power, often taking minutes to generate a single proof. Modern Proof Systems, such as PlonK and Halo2, have drastically reduced these requirements, enabling near-instant proof generation on standard hardware.
This democratization of privacy is a critical factor in the widespread adoption of Decentralized Identity. The shift toward Multi-Party Computation (MPC) also provides an additional layer of security, ensuring that the private keys used for identity management are never stored in a single location.

Future Paradigms of Autonomous Identity
The next phase of Zero Knowledge Identity involves the rise of Autonomous Agentic Identity. As AI agents begin to participate in Crypto Options markets, they will require their own identity layers to prove their origin, their underlying capital reserves, and their compliance with trading mandates.
Zero Knowledge Identity will provide the framework for these agents to interact with human-led protocols without revealing their proprietary algorithms or strategic biases. This creates a future where the distinction between human and machine participants becomes secondary to the validity of the cryptographic proofs they present. The convergence of Zero Knowledge Identity and Cross-Chain Messaging will enable a universal identity layer that spans the entire blockchain ecosystem.
A user will be able to prove their identity on one network and have that proof accepted on another without needing to re-verify. This interoperability is the key to unlocking Global Liquidity and creating a truly seamless decentralized financial system. The Derivative Systems Architect must view Zero Knowledge Identity not as a static tool, but as a dynamic foundation for a new era of Permissionless Finance.
The ultimate goal is a world where trust is redundant because verification is ubiquitous and private.
- Hyper-Scalable Proofs will allow for millions of identity verifications per second, matching the speed of traditional payment processors.
- Biometric ZK-Proofs will link physical identity to digital wallets without storing biometric data on-chain.
- Social Recovery Layers will use Zero Knowledge Identity to allow users to regain access to their funds through their social graph.
- Dynamic Compliance will enable real-time adjustment of trading permissions based on changing regulatory environments.
Glossary

Smart Contract Security
Options Trading
Zk-Starks

Know Your Customer

Privacy First Finance
Completeness Property

Sybil Resistance

Order Flow Privacy

Zk-Kyc