Essence
Privacy-Preserving Order Books, or PPOBs, are a critical architectural response to the information leakage inherent in public blockchain market designs. In a standard decentralized exchange, every order placed is broadcast to the network before execution, creating a public record of intent that can be exploited by adversarial actors. This transparent order flow allows for sophisticated front-running strategies, often categorized under the umbrella of Maximal Extractable Value (MEV), where miners or sequencers reorder transactions to profit from a user’s anticipated price movement.
The core function of a PPOB is to conceal the details of an order ⎊ specifically its price and size ⎊ from all parties, including network validators, until the order is matched and executed. This cryptographic concealment shifts the market from a transparent race condition to a more deterministic, private matching process. PPOBs are essential for fostering institutional participation and enabling robust options markets where large-volume orders cannot be easily manipulated or exploited by predatory algorithms.
PPOBs mitigate information asymmetry in decentralized markets by concealing order details from public view until execution.
Origin
The concept of privacy in trading originates from traditional financial markets with the advent of “dark pools.” These off-exchange venues allow large institutional traders to execute significant orders without revealing their intentions to the broader market, thereby avoiding negative price impact. The challenge in decentralized finance was replicating this function without relying on a centralized, trusted intermediary. Early attempts at privacy in crypto focused on transaction value and address obfuscation, exemplified by protocols like Zcash.
The application of privacy specifically to market microstructure evolved from these foundations. The realization that transparent order books create a fundamental vulnerability for high-value derivatives trading drove the development of specialized solutions. The origin of PPOBs lies in the synthesis of advanced cryptography, specifically zero-knowledge proofs, with market design principles, seeking to create a truly fair and level playing field for market participants by eliminating information-based arbitrage.
Theory
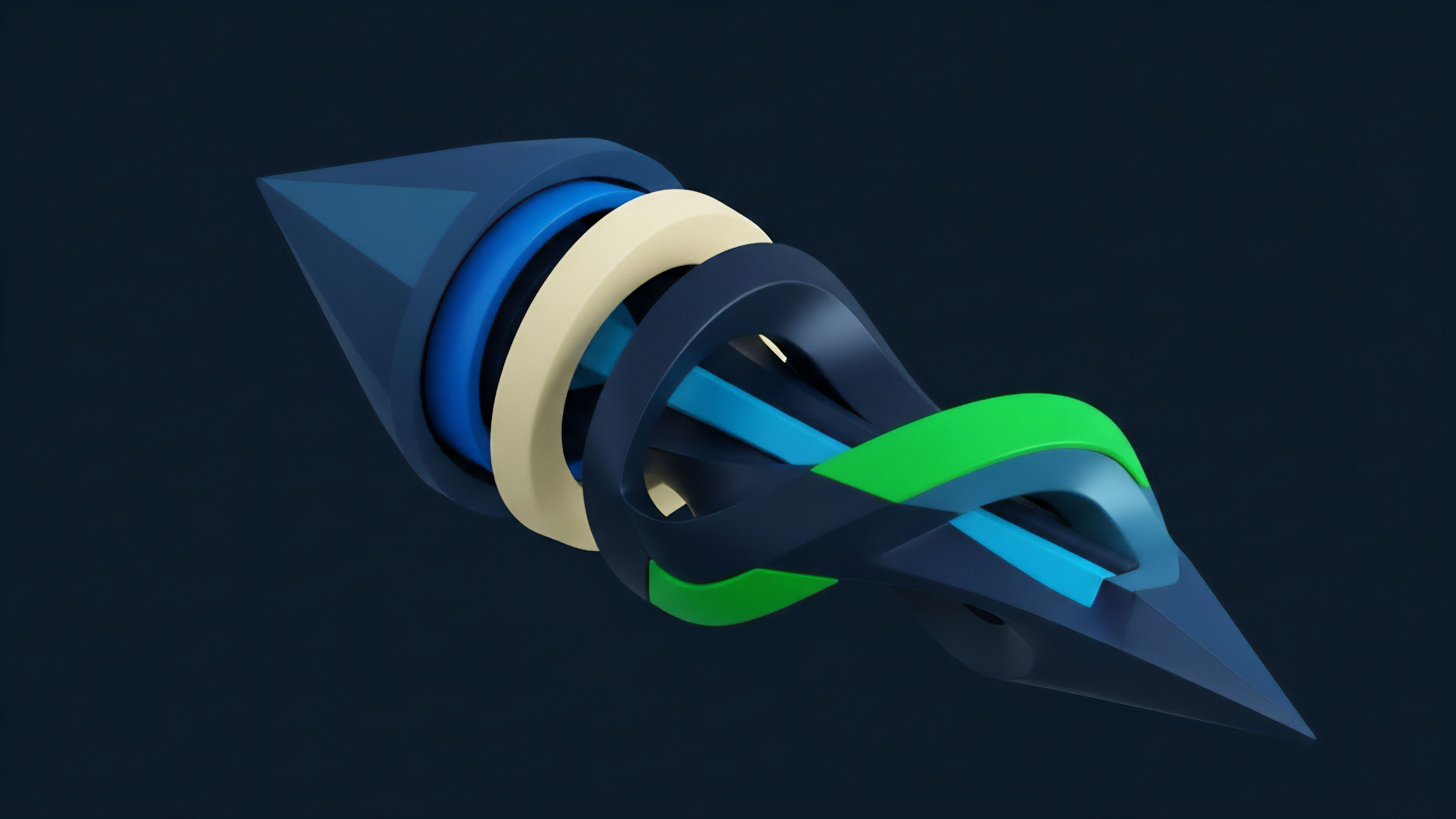
PPOBs operate by changing the fundamental game theory of market execution. The traditional model presents a simultaneous-move game where participants act based on public knowledge of other participants’ intentions. PPOBs introduce cryptographic barriers to this knowledge, forcing participants to act based on probabilistic assumptions rather than certain knowledge.
This reduces the profitability of predatory strategies like front-running. The underlying protocol physics rely on advanced cryptographic primitives.

Cryptographic Primitives and Verifiability
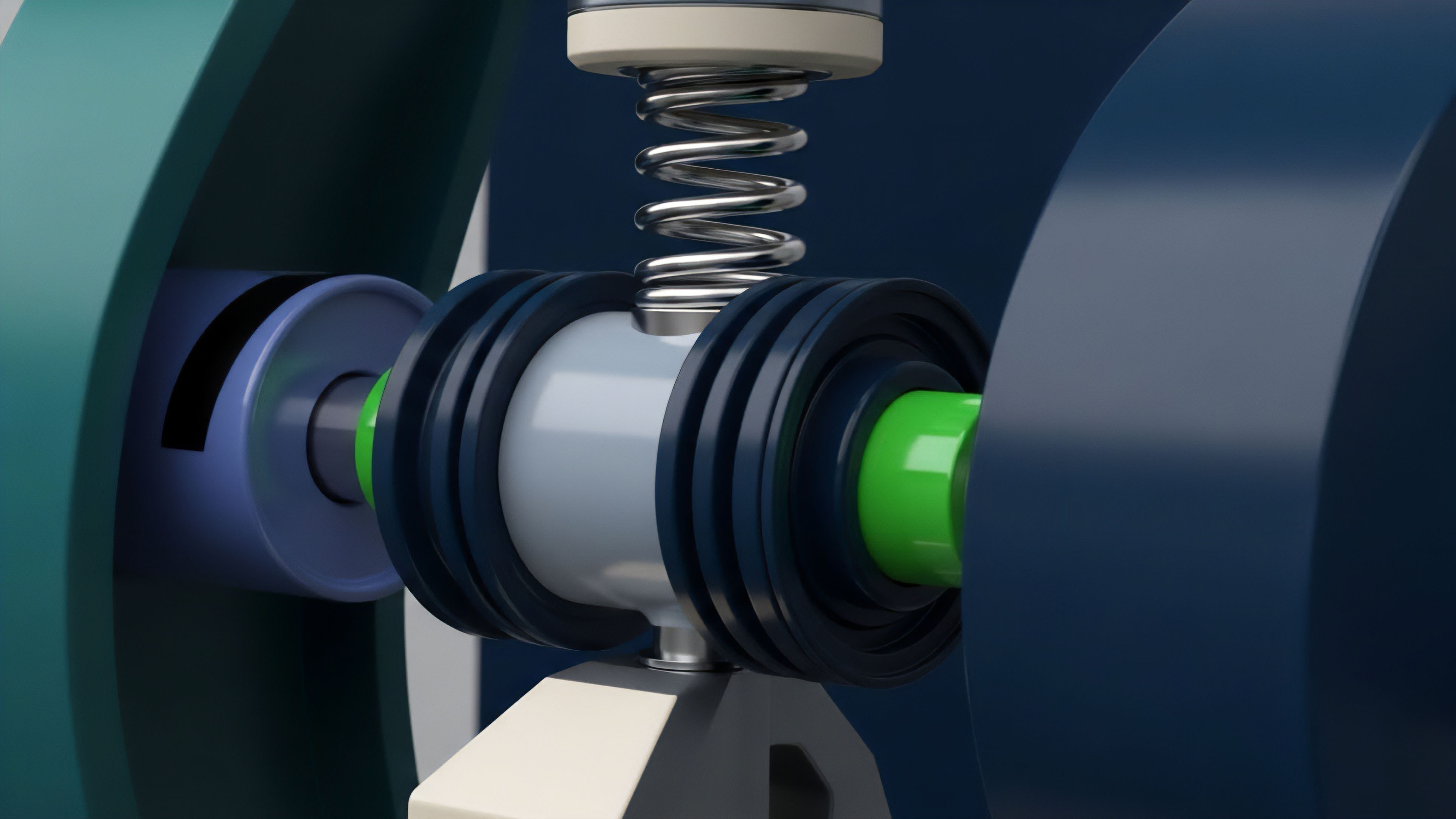
The primary challenge in designing a PPOB is ensuring that an order can be verified as valid without revealing its specific content. This is achieved through several mechanisms:
- Zero-Knowledge Proofs (ZKPs): A user submits an order along with a ZKP that proves the order satisfies certain constraints ⎊ for example, that the order price is within a valid range or that the user has sufficient collateral ⎊ without revealing the specific price or size. The sequencer can verify the proof without learning the sensitive information.
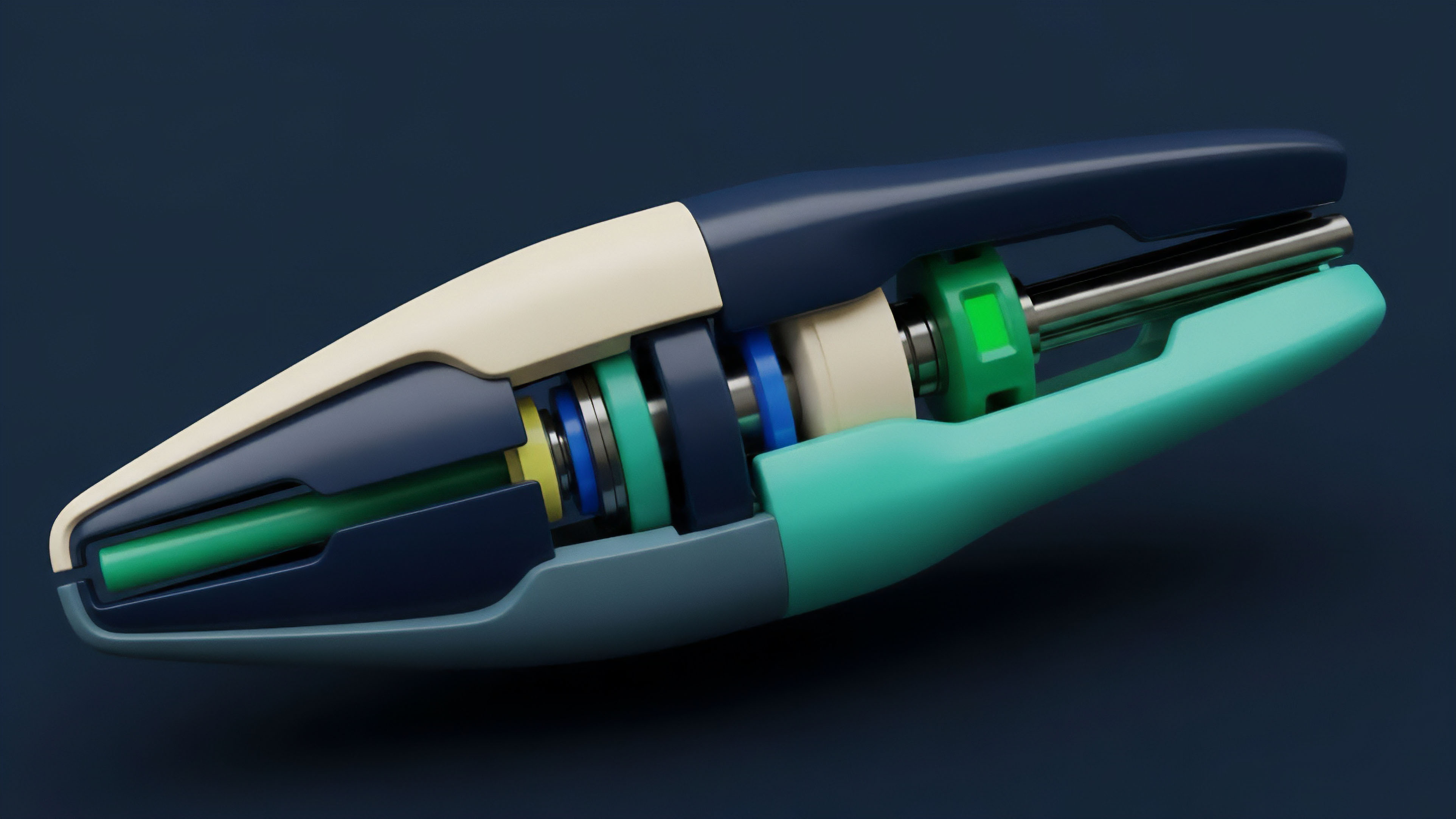
- Secure Multi-Party Computation (MPC): This approach distributes the computation of the matching engine across several independent parties. No single party sees the full set of orders; instead, the parties collectively compute the match results. This creates a distributed trust model where collusion among all parties is required to compromise privacy.
- Trusted Execution Environments (TEEs): TEEs offer a hardware-based solution. Orders are submitted to a secure enclave on a physical server. The code running within the TEE is isolated from the operating system and network. While efficient, this model introduces a reliance on specific hardware and its manufacturer, creating a different trust assumption.

Market Microstructure and MEV Mitigation
The primary theoretical advantage of PPOBs is the mitigation of MEV. In a transparent system, MEV arises from the ability to observe and reorder transactions within a block. PPOBs render this observation useless by encrypting order details.
The matching process itself is executed privately, ensuring that a sequencer or validator cannot use knowledge of pending orders to profit. This shifts the focus from predatory information-based strategies to genuine price discovery based on supply and demand dynamics.

Approach
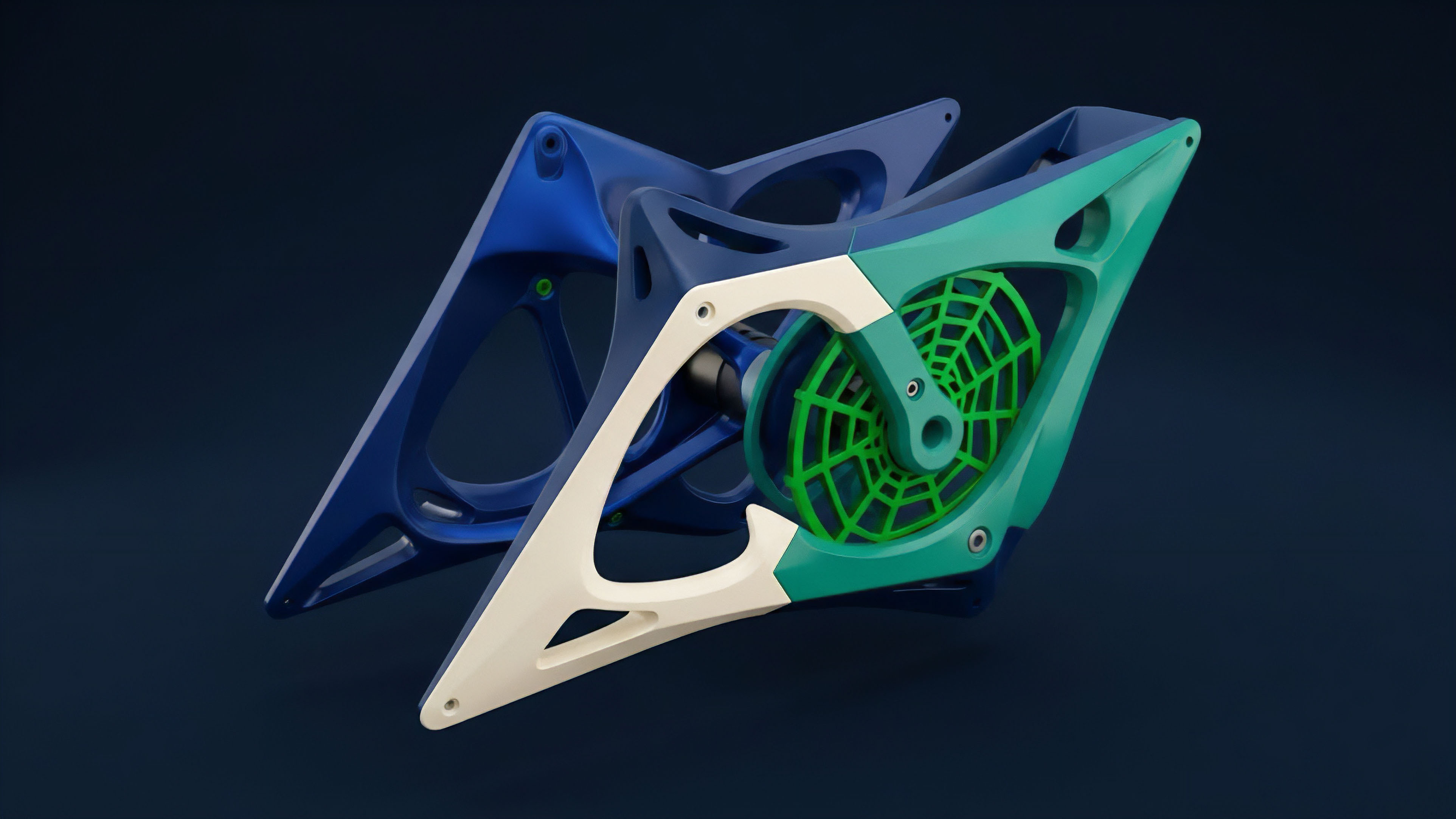
The implementation of PPOBs in decentralized options markets typically follows one of two primary architectural patterns, each presenting distinct trade-offs in performance, security, and trust assumptions.
The choice of approach dictates the final characteristics of the derivative market, specifically its latency and resistance to various forms of attack.

ZKP-Based Architectures
Protocols like dYdX utilize ZK-rollups, where orders are batched off-chain and then settled on-chain via a validity proof. The matching engine operates in a private environment, and a proof of the match result is generated. This approach offers strong cryptographic guarantees, as the privacy is enforced mathematically.
However, ZKP generation can introduce latency, making high-frequency trading challenging.

TEE-Based Architectures
Protocols like Oasis or derivatives exchanges built on Sui leverage Trusted Execution Environments. Orders are sent to a TEE, which acts as a black box. The TEE matches orders and then broadcasts the results to the blockchain.
This method offers significantly lower latency compared to ZKP generation. The trust model shifts from mathematics to hardware; participants must trust the TEE’s integrity and that the hardware manufacturer has not introduced backdoors.

Comparison of PPOB Approaches
| Feature | ZKP-Based PPOBs | TEE-Based PPOBs |
|---|---|---|
| Trust Assumption | Cryptographic Proofs (Mathematical) | Hardware Integrity (Physical/Manufacturer) |
| Latency | Higher (due to proof generation) | Lower (hardware-accelerated matching) |
| Security Model | Strong mathematical guarantees | Relies on external hardware and code integrity |
| Scalability | High throughput through batching | High throughput through hardware efficiency |
The selection between ZKP and TEE approaches for PPOBs balances the fundamental trade-off between mathematical trust and hardware performance.

Evolution
The evolution of PPOBs tracks directly with the increasing sophistication of market participants and the escalating threat of MEV. Early DeFi protocols were designed around a simple, transparent model. The initial wave of MEV extraction, primarily through simple front-running and sandwich attacks, demonstrated the fragility of this model for complex financial instruments like options.
The response has been a progression from simple order flow auctions to fully encrypted order books. The development of PPOBs represents a shift in market design philosophy. Instead of accepting MEV as an inherent cost of transparency, PPOBs attempt to engineer it out of existence by removing the information advantage.
This evolution is driven by the demand from professional market makers and institutional players who cannot operate efficiently in a high-MEV environment. The current iteration of PPOBs is focused on optimizing the balance between privacy and performance. The goal is to provide a trading experience that matches the speed of centralized exchanges while maintaining the decentralized and non-custodial nature of a public blockchain.
- Phase 1: Transparent Order Books (Early DeFi): All orders are public; high MEV risk.
- Phase 2: Order Flow Auctions (OFA): Users sell their order flow to specialized searchers who execute the trade. This centralizes MEV extraction but potentially offers better execution to users.
- Phase 3: Encrypted Order Books (PPOBs): Orders are hidden from all parties, including searchers and sequencers, until execution. This eliminates MEV at the source.
The current challenge in this evolution is ensuring sufficient liquidity in these private pools. If liquidity fragments across too many PPOBs, the overall market efficiency decreases. The design must therefore incentivize liquidity provision while maintaining privacy guarantees.

Horizon
Looking ahead, PPOBs are positioned to become the default market structure for high-value derivatives in decentralized finance. The next generation of options protocols will not be able to compete effectively without offering a solution to information asymmetry. The horizon for PPOBs involves several key areas of development:

Composability and Interoperability
The current PPOB implementations often exist in isolated silos to maintain privacy guarantees. The next step in their evolution is to enable composability with other DeFi protocols without compromising the privacy of the order book. This involves developing new standards for “private composability,” allowing protocols to interact with the PPOB (e.g. for collateral checking or settlement) while ensuring the order flow remains hidden.

The Role of ZK Hardware Acceleration
The latency issue associated with ZKPs is a significant barrier to high-frequency options trading. The future depends on the development of specialized hardware accelerators for ZK proofs. If proof generation time can be reduced from seconds to milliseconds, ZKP-based PPOBs will offer a superior combination of security and speed compared to TEE-based models.

Risk Management and Market Structure
The implementation of PPOBs introduces new forms of systemic risk. A PPOB that fails to execute correctly could lead to cascading liquidations in an options market. The focus must shift from preventing front-running to ensuring the integrity of the private matching process itself.
This requires rigorous auditing and formal verification of the underlying cryptographic and matching algorithms.
The future of PPOBs will define the market structure for institutional-grade decentralized derivatives, shifting competition from information arbitrage to genuine liquidity provision.
The critical question for the next phase of development centers on the trade-off between privacy and network effects. If a PPOB achieves perfect privacy but cannot easily share state with other protocols, does it create a new form of market fragmentation that hinders overall capital efficiency?

Glossary

Privacy-First Liquidity

Selective Privacy

Atomic Privacy Swaps
Auditable Privacy Framework
Delta Neutrality Privacy

User Privacy

Order Flow Transparency

Privacy Preserving Risk Management
Privacy-Preserving Order Matching Algorithms