
Essence
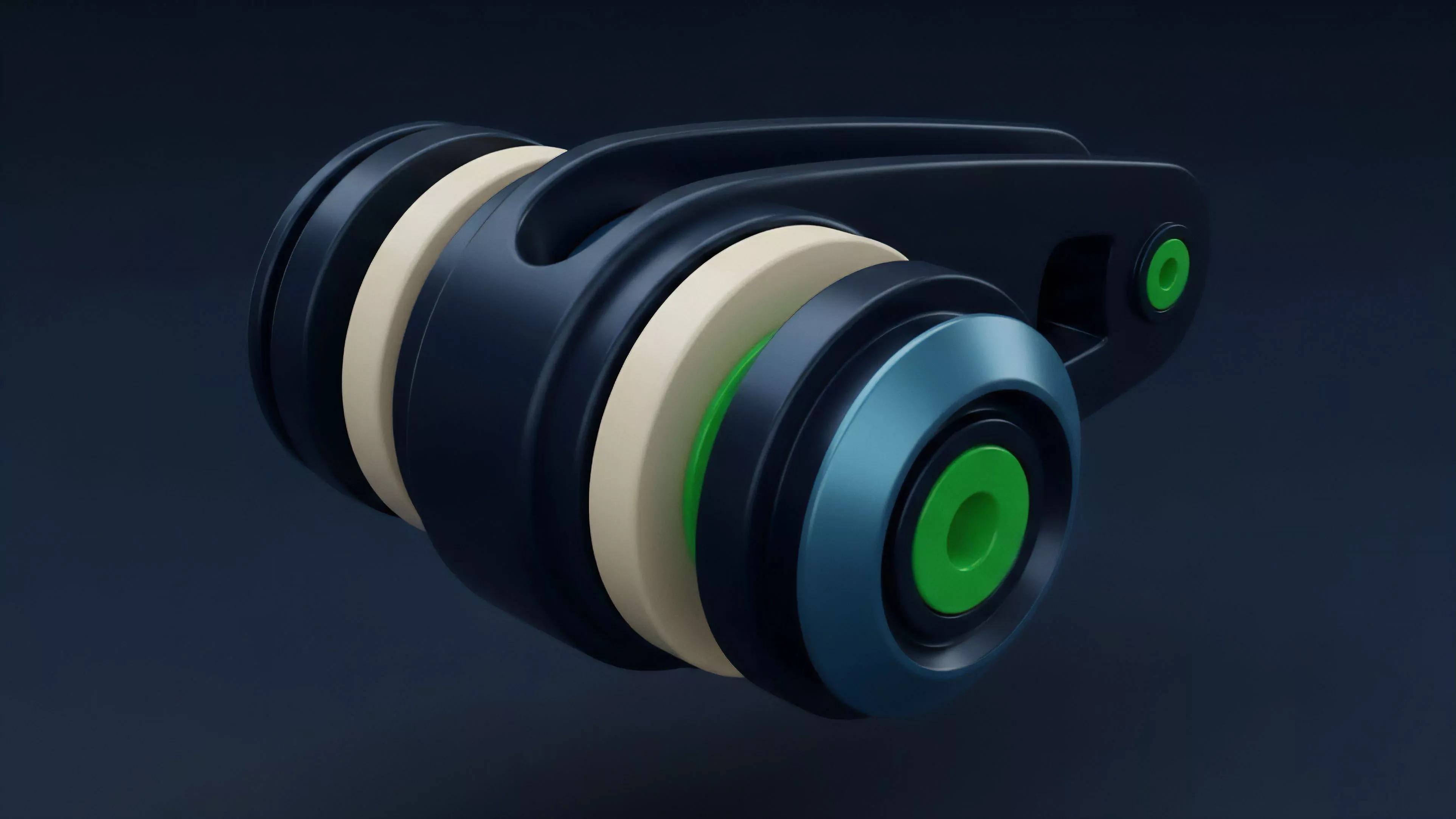
MPC-HSM Hybrid architecture represents the convergence of distributed cryptographic computation and hardened physical security modules to manage digital asset keys. This framework decentralizes the signing process while maintaining the integrity of hardware-backed root secrets, effectively addressing the vulnerability of centralized custodial systems. By splitting private keys into mathematical shares across disparate nodes, the system ensures no single entity holds a complete secret.
The integration of Hardware Security Modules at each node adds a layer of tamper-resistant execution, enforcing strict policy controls and identity verification before any partial signature generation occurs.
MPC-HSM Hybrid architecture synthesizes decentralized cryptographic key management with hardware-enforced policy execution to eliminate single points of failure in digital asset custody.
The operational utility of this structure lies in its ability to facilitate institutional-grade transaction throughput without compromising on security. It transforms the signing event from a monolithic operation into a coordinated, multi-party consensus process, where each participant relies on their internal HSM to validate the legitimacy of the request.

Origin
The genesis of this model stems from the inherent tension between the transparency of blockchain protocols and the opacity required for secure institutional capital management. Early attempts at securing digital assets relied heavily on cold storage, which offered security but introduced significant friction for liquidity management and high-frequency trading.
The evolution toward Multi-Party Computation emerged as a solution to remove the need for a single, centralized authority. However, purely software-based MPC implementations often faced scrutiny regarding their vulnerability to malware or unauthorized code execution within the server environment. The subsequent introduction of Hardware Security Modules as a foundational layer provided the necessary physical isolation.
This synthesis creates a defense-in-depth strategy, combining the mathematical guarantees of Threshold Cryptography with the physical tamper-resistance of dedicated hardware, addressing the primary concerns of institutional risk managers and auditors.

Theory
The mathematical foundation of MPC-HSM Hybrid relies on Threshold Signature Schemes where the secret key is never reconstructed in its entirety. The signing process involves nodes generating partial signatures that are combined off-chain to form a valid blockchain transaction.
- Secret Sharing: The master key is partitioned using schemes such as Shamir or Gennaro-Goldfeder, ensuring security against colluding subsets of participants.
- Policy Enforcement: The HSM acts as a gatekeeper, verifying transaction parameters against pre-defined rules before permitting the release of a partial signature.
- Adversarial Resilience: The system maintains functionality even if a portion of the nodes are compromised or offline, assuming the threshold for signature generation is met.
The security of the hybrid model is predicated on the impossibility of compromising both the cryptographic threshold and the physical isolation of the hardware modules simultaneously.
This architecture shifts the threat model from protecting a single repository to securing a distributed network. The complexity of orchestrating an attack increases exponentially as the number of independent nodes and distinct hardware vendors rises.
| Metric | Centralized Custody | MPC-HSM Hybrid |
| Failure Mode | Single point of compromise | Threshold compromise required |
| Latency | Low | Medium |
| Auditability | Opaque | High transparency |

Approach
Current implementations prioritize operational agility while maintaining strict compliance with financial regulations. Organizations deploy nodes across geographically distributed environments to mitigate jurisdictional and physical risks. The workflow involves a rigorous validation pipeline:
- An initiator proposes a transaction request.
- The request passes through an automated risk engine.
- Each participating HSM validates the transaction against stored policy sets.
- Nodes produce partial signatures only if all internal checks pass.
- The aggregator assembles the final transaction for broadcast.
This structured approach allows for programmable governance, where multisig requirements are enforced at the hardware level. It removes the human element from the immediate signing process, significantly reducing the surface area for social engineering or insider threats.
Evolution
The transition from early, monolithic cold storage to distributed, hardware-backed architectures reflects the maturing requirements of the crypto derivatives market. Early iterations struggled with performance bottlenecks, as the overhead of MPC coordination often hindered high-frequency trading strategies.
Technological advancements in Zero-Knowledge Proofs and optimized cryptographic primitives have drastically reduced the computational cost of generating signatures. Modern systems now support complex, conditional transaction types, enabling advanced strategies like automated liquidation or rebalancing without manual intervention.
The shift toward hybrid architectures reflects the industry transition from simple asset storage to complex, automated, and policy-driven financial infrastructure.
Consider the broader context of decentralized systems; the history of human organization often mirrors this movement from centralized power to distributed, trustless cooperation, where the architecture of the system itself dictates the boundaries of possible behavior. We are witnessing the automation of institutional trust, where code and hardware replace the subjective judgment of centralized intermediaries.

Horizon
Future developments in this domain focus on increasing the flexibility of the MPC protocol to handle cross-chain interoperability and complex smart contract interactions. We anticipate a tighter integration with decentralized identity standards, allowing for more granular, identity-aware signing policies.
The next phase will involve the transition to Trusted Execution Environments that offer greater scalability while maintaining the security properties of dedicated hardware. This will likely lower the cost of entry for smaller institutions, potentially leading to a democratization of institutional-grade security.
| Trend | Implication |
| Cross-Chain Signing | Increased liquidity efficiency |
| TEE Integration | Lower operational overhead |
| Policy Automation | Reduced manual intervention |
The ultimate trajectory leads to the seamless embedding of these security primitives into the protocol layer itself. This would make secure, distributed custody the default state for all participants, fundamentally changing the nature of risk in digital asset markets.
