Essence
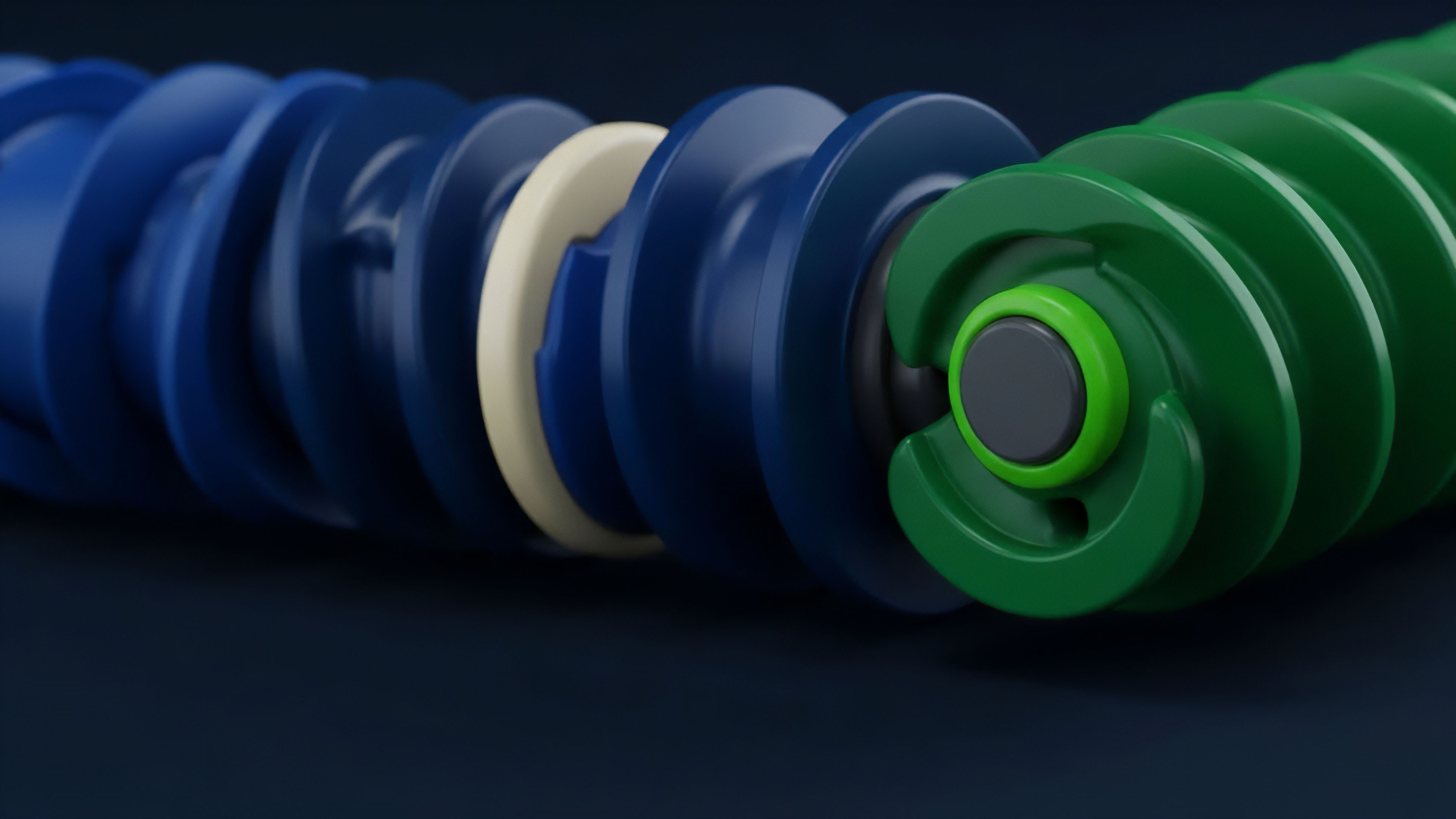
Liquidity fragmentation across the digital asset landscape necessitates a mechanism that prioritizes internal capital efficiency over external execution latency. Internal Order Matching Systems function as autonomous liquidity reservoirs within a single financial entity ⎊ orchestrating the immediate settlement of trades without external market interaction. These architectures prioritize the netting of offsetting risks between participants ⎊ minimizing the slippage and fee leakage that characterize public order book execution.
Internalizers reduce market impact by absorbing large orders within private liquidity pools.
The primary objective remains the maximization of internal fill rates ⎊ a metric that dictates the success of any closed-loop financial environment. By isolating order flow, these systems eliminate the information leakage that often plagues traders on transparent chains. This internal settlement layer acts as a buffer ⎊ protecting sensitive trade data from predatory algorithms that scan public mempools or order books for directional signals.

Origin
The transition of these mechanisms into the digital asset space mirrors the rise of dark pools in traditional equities.
Early centralized exchanges operated on rudimentary matching logic ⎊ broadcasting every intent to the public. As sophisticated market makers entered the crypto ecosystem, the demand for stealth and capital efficiency birthed internal crossing engines. These early iterations allowed large institutions to offset risk without alerting the broader market ⎊ preventing front-running.
The evolution from simple bid-ask matching to sophisticated risk-offsetting engines reflects the professionalization of crypto market microstructure. This shift was driven by the realization that broadcasting every order to a public ledger is often counterproductive for large-scale capital deployment.
Theory
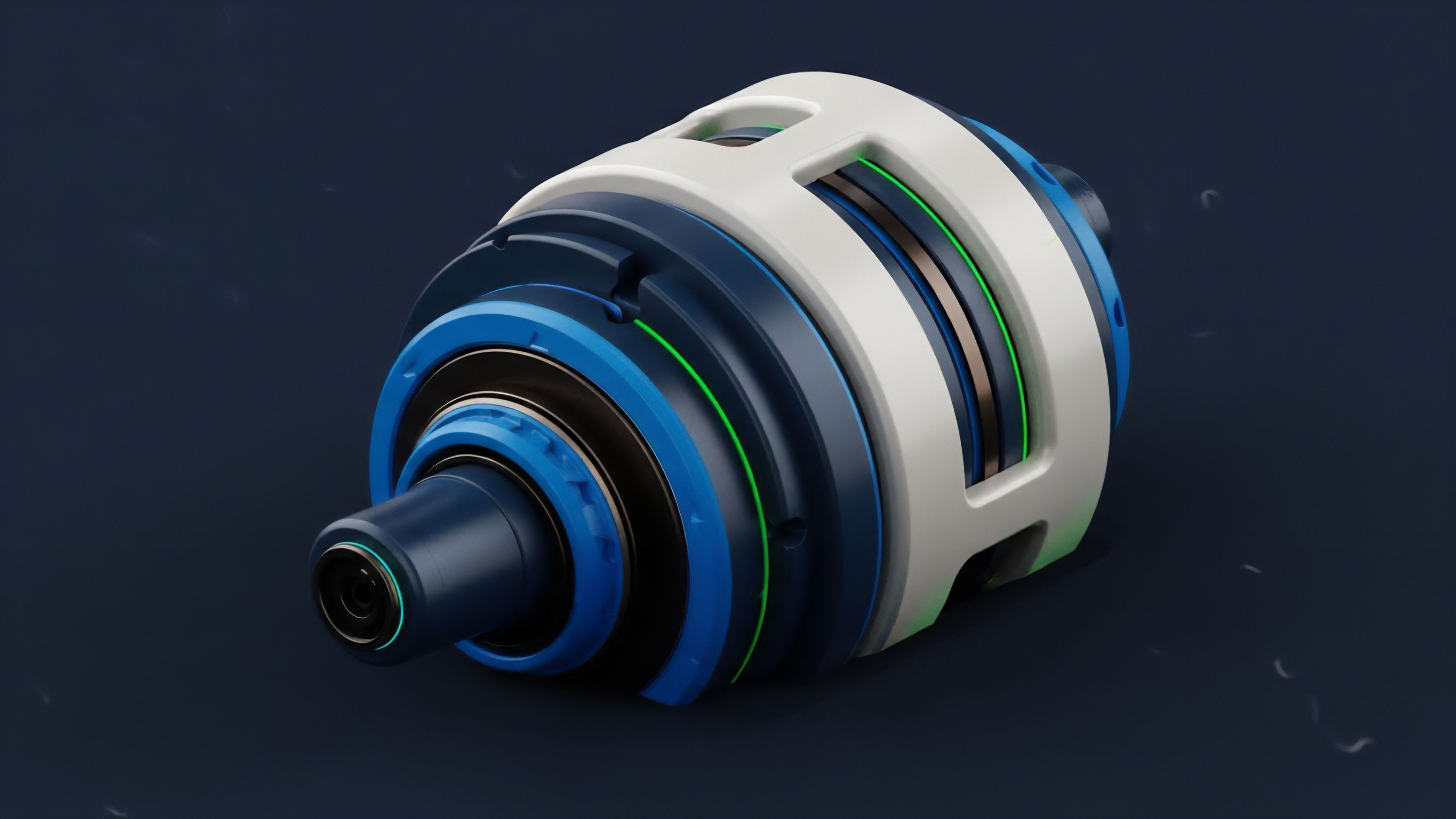
The mathematical architecture of an internalizer centers on the netting efficiency ratio. This calculation determines the volume of trades resolved without external hedging.
A high ratio suggests that the system successfully pairs opposing risks ⎊ reducing the reliance on external liquidity providers. Internal matching of liquidity mirrors the physical principle of local entropy reduction ⎊ where order is maintained within a closed system at the expense of external noise.

Matching Priority Frameworks
Execution logic within these systems follows a rigorous hierarchy to ensure fairness and efficiency. The following table outlines the primary logic structures used to govern internal flow.
| Logic Type | Execution Priority | Primary Benefit |
|---|---|---|
| Price-Time | Best price followed by earliest arrival | Rewards speed and competitive pricing |
| Pro-Rata | Volume-weighted distribution across participants | Encourages large-scale liquidity provision |
| Inventory-Weighted | Prioritizes orders that balance the internal book | Reduces the need for external hedging |
The efficiency of a matching engine is measured by its ability to minimize external hedging costs.
Technical Requirements for Internalization
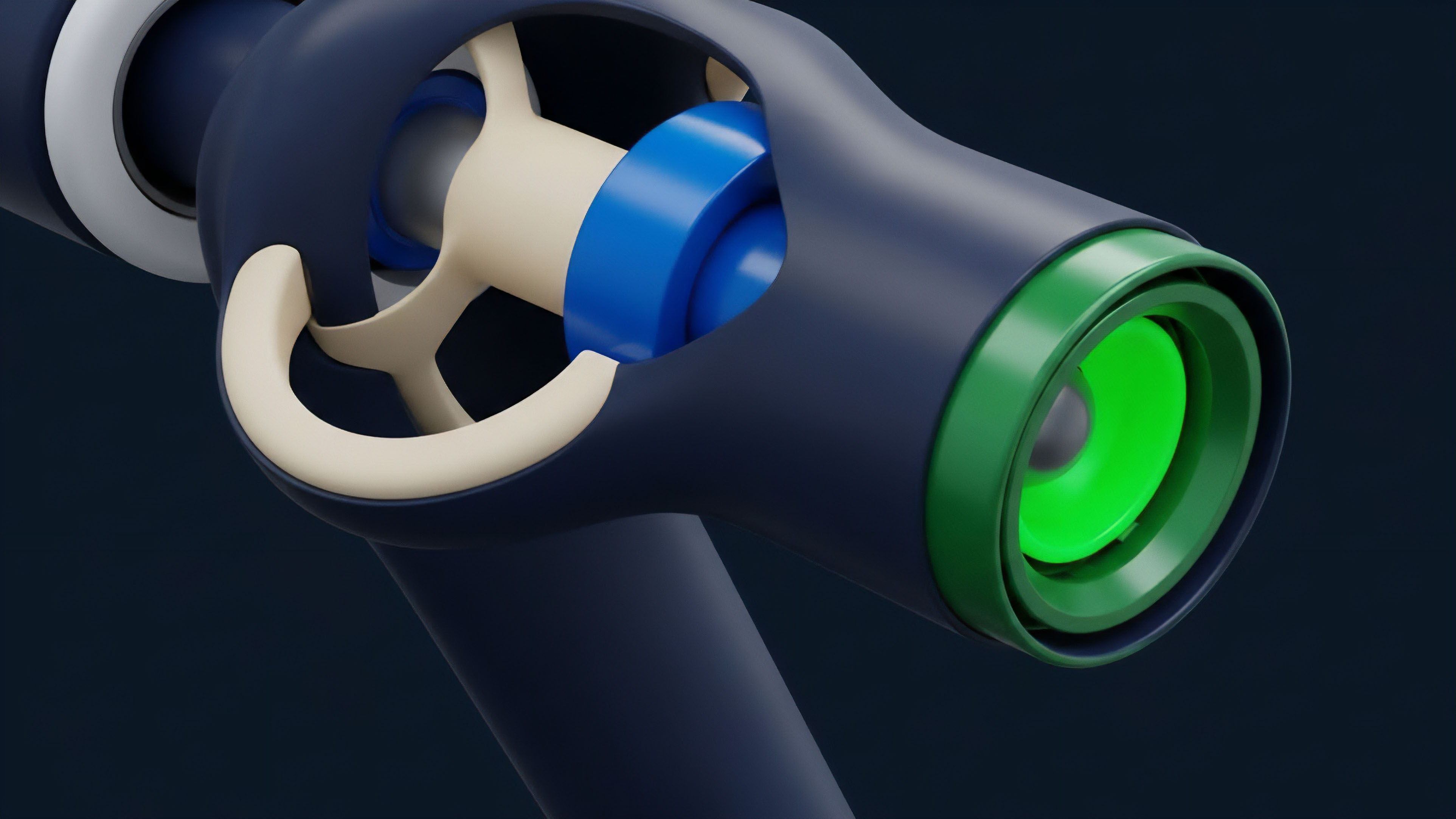
- Low-latency order processing engines are required to scan internal books before external routing occurs.
- Robust internal ledger systems must maintain absolute accuracy for sub-millisecond settlement.
- Real-time risk assessment modules evaluate the impact of every internal match on the overall treasury balance.
- External venue routing logic determines when internal liquidity is insufficient and external execution is required.

Approach
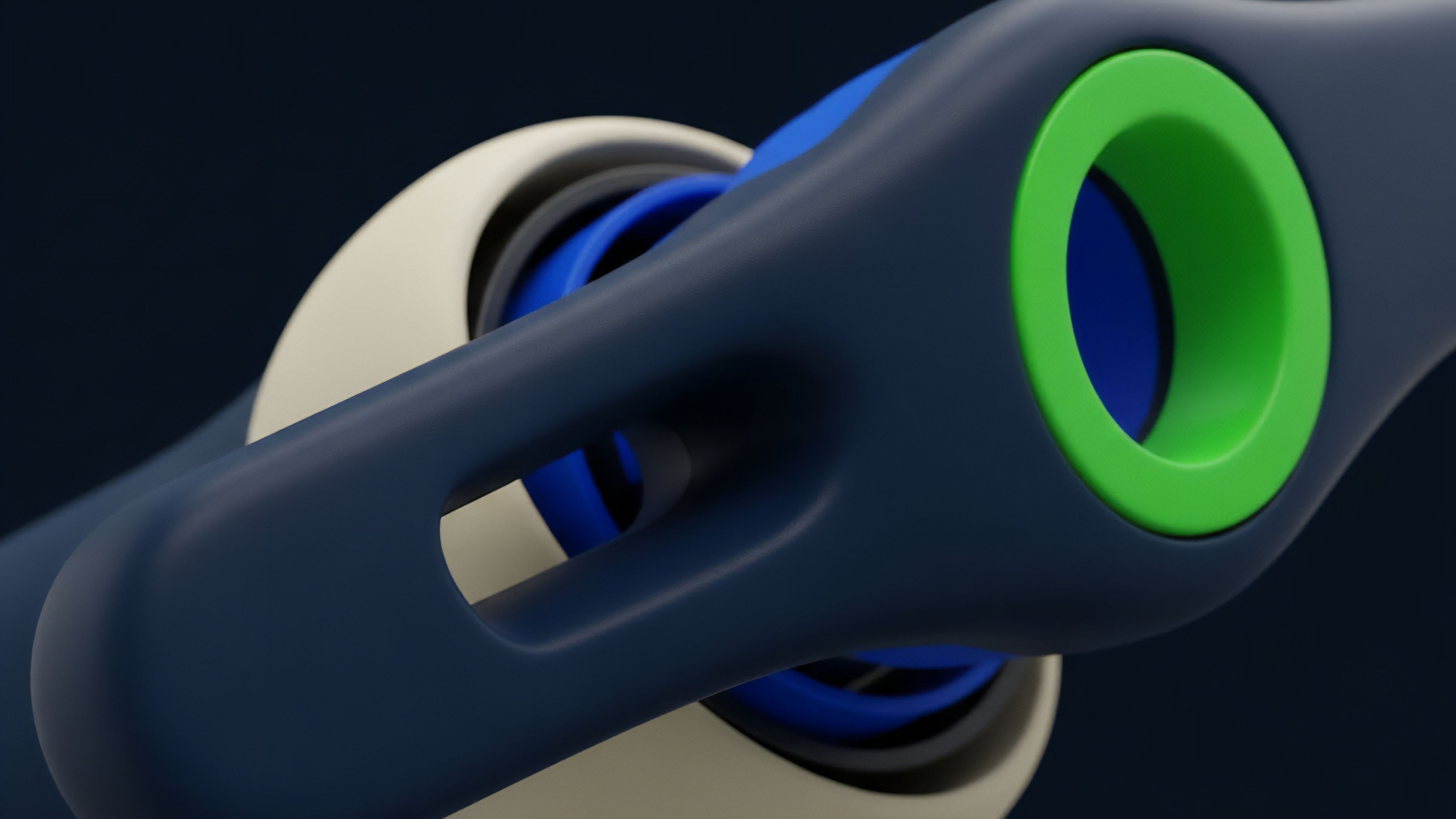
Execution within these systems relies on high-speed crossing engines. These engines analyze incoming orders against a private order book ⎊ seeking immediate matches. If no internal match exists, the system may route the order to an external venue or hold it for a brief window to await offsetting flow.
This method prioritizes execution speed and cost reduction over total transparency.
| Feature | Centralized Internalizer | Decentralized PMM |
|---|---|---|
| Transparency | Low (Private Ledger) | Medium (On-chain Settlement) |
| Execution Speed | Sub-millisecond | Block-time Dependent |
| Cost Structure | Zero or Low Fee | Gas + Spread |
Current execution models utilize high-frequency crossing engines. These engines scan internal inventories ⎊ identifying matches before the latency of a public broadcast occurs. This methodology allows for a significant reduction in the bid-ask spread offered to the end-user ⎊ as the internalizer captures the spread that would otherwise be paid to an external market maker.
Evolution
Initial systems were simple crossing desks.
Today, they have evolved into complex risk-management engines that incorporate predictive modeling. These modern internalizers anticipate order flow patterns ⎊ adjusting internal spreads to attract the necessary side of a trade. This progression has moved the industry away from static order books toward fluid, intent-based execution environments.
Risk Mitigation Protocols
- Strict capital adequacy requirements ensure the internalizer can settle all matched trades even during high volatility.
- Automated circuit breakers pause internal matching if the directional imbalance exceeds predefined thresholds.
- Regular audits of matching logic verify that the system remains unbiased and compliant with internal mandates.
- Separation of internal and external order books prevents the contamination of private liquidity with public market noise.
Regulatory compliance requires strict separation between proprietary trading desks and internal matching logic.

Horizon
The future of internal matching lies in privacy-preserving technologies that bridge the gap between efficiency and trustlessness. Zero-knowledge proofs will allow protocols to prove the validity of an internal match without revealing the size or price to the public ⎊ creating a state where liquidity is both global and private simultaneously. We are moving toward a reality where Internal Order Matching Systems are no longer confined to centralized silos but are instead integrated into the very fabric of cross-chain communication. These next-generation engines will utilize multi-party computation to match orders across disparate networks without requiring a central intermediary to hold the assets. This shift will effectively decentralize the dark pool ⎊ offering the privacy and efficiency of institutional-grade internalizers to the broader decentralized finance world. As capital continues to migrate toward these more efficient structures, the traditional public order book may eventually become a venue of last resort ⎊ reserved only for the residual flow that cannot be netted within these private, high-velocity matching environments. The ultimate destination is a seamless, invisible layer of global liquidity that prioritizes the trader’s intent while maintaining the systemic stability of the underlying networks through rigorous, automated risk management.
Glossary

Bid-Ask Spread

Market Making
Decentralized Finance

Internal Order Matching Systems

Sor

Price Discovery
Decentralization
Privacy Preserving

High Frequency Trading