Essence
Front-running in crypto options represents a specific form of market microstructure exploitation where an adversarial actor gains prior knowledge of a pending options trade and executes a transaction to profit from the resulting price movement. This is fundamentally different from traditional finance front-running due to the transparency of decentralized exchange mempools. In a public mempool, pending transactions are visible to all network participants before they are confirmed by validators.
An options trade, particularly a large one, contains significant information about market direction and volatility expectations. The front-runner can observe this impending order, calculate its likely impact on the option premium, and execute a trade ahead of it. The profit comes from capturing the price change caused by the original order’s execution.
This activity, often referred to as Miner Extractable Value (MEV), introduces systemic risk and a hidden cost to market participants. The impact of front-running on options markets is magnified by the non-linear nature of derivatives pricing. The price of an option is highly sensitive to changes in the underlying asset price, volatility, and time to expiration.
A front-runner observing a large buy order for a call option can anticipate a corresponding increase in the underlying asset price, leading to a higher call option premium. By executing a buy order immediately before the large order, the front-runner captures the spread. This exploitation undermines the integrity of options pricing and creates an environment where large traders are penalized for providing liquidity or expressing market views.
Front-running in options markets exploits information asymmetry by allowing actors to profit from a pending transaction’s predictable price impact, creating a hidden cost for legitimate traders.

Origin
The concept of front-running originates in traditional financial markets where high-frequency trading (HFT) firms utilized co-location and high-speed data feeds to gain microsecond advantages over slower participants. In this context, front-running involved proprietary traders acting on non-public information about customer orders before they were executed on an exchange. The transition to decentralized finance (DeFi) fundamentally altered the mechanism of front-running.
Instead of relying on non-public information, DeFi front-running relies on public information ⎊ the mempool. The emergence of MEV as a distinct concept formalized this problem. When a user broadcasts a transaction, it enters a public waiting area (the mempool) before being included in a block by a validator.
Validators, or searchers who pay validators, can reorder, insert, or censor transactions within a block to extract value. For options, this value extraction is particularly potent because options trades are often executed against automated market makers (AMMs) where pricing relies on formulas that can be exploited by carefully timed transactions. The origin of front-running defenses stems directly from this realization: the transparent and sequential nature of blockchain transaction processing creates an open-source attack vector.
Early solutions were simple, attempting to mitigate the problem at the protocol level by changing how orders were processed, while later solutions moved to infrastructure-level changes to obscure the order flow entirely.

Theory
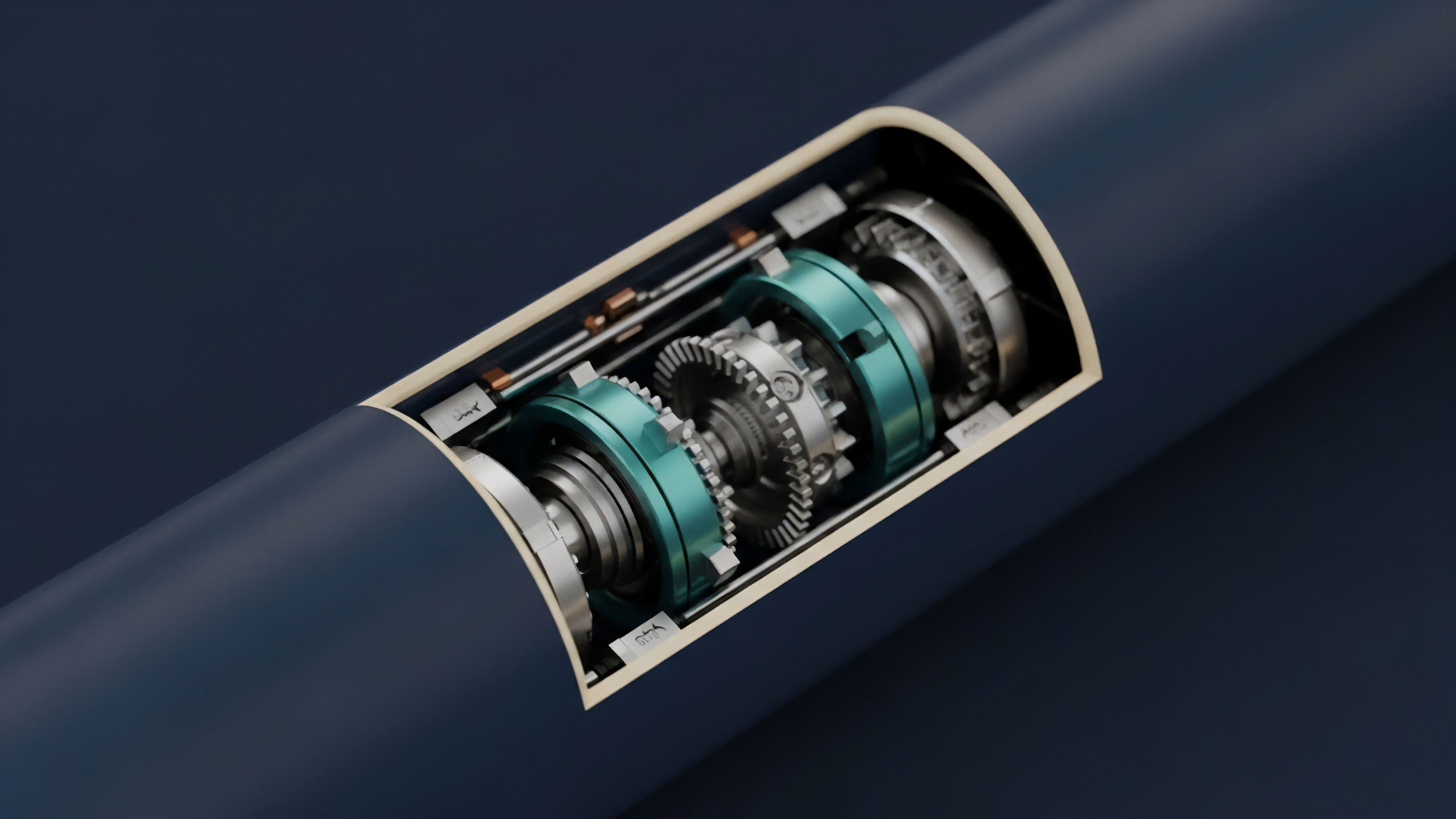
The theoretical basis for options front-running relies on the exploitation of price discovery mechanisms within decentralized options AMMs. The core principle is that a large options order, by changing the AMM’s internal state (e.g. the pool’s ratio of assets), will necessarily change the implied volatility and thus the option premium.
The front-runner calculates this price change and acts upon it. Consider the Black-Scholes model and its Greeks. When a large order for a call option is submitted, it signals a demand that will likely increase the option’s premium.
The front-runner, observing this order, calculates the expected change in Delta (sensitivity to underlying price changes) and Gamma (sensitivity of Delta to underlying price changes). By executing a trade that captures this expected change, the front-runner extracts value. The defense mechanisms must therefore disrupt this calculation by obfuscating the information or eliminating the time advantage.
The challenge in options front-running is the high complexity of the calculations required. A front-runner needs to predict the exact price impact of a large order, which depends on the AMM’s specific pricing curve, current liquidity, and volatility parameters. The defense mechanisms attempt to break the front-runner’s ability to execute this calculation profitably.
| Options Greek | Sensitivity | Front-Running Vector |
|---|---|---|
| Delta | Option price change per $1 change in underlying asset price. | Large order execution causes underlying price movement; front-runner captures pre-move option premium. |
| Gamma | Rate of change of Delta. | Front-runner anticipates rapid Delta changes from large orders, making quick profits from volatility spikes. |
| Vega | Option price change per 1% change in implied volatility. | Large orders signal high demand, increasing implied volatility; front-runner profits from this anticipated volatility increase. |

Approach
Front-running defense mechanisms in crypto options protocols are designed to eliminate the time priority advantage and information leakage inherent in public mempools. These approaches fall into several categories, each with its own trade-offs regarding latency, capital efficiency, and security.
- Batch Auctions: This mechanism groups all orders received within a fixed time window and settles them simultaneously at a single clearing price. This approach removes the time priority advantage by ensuring all participants within the window receive the same execution price.
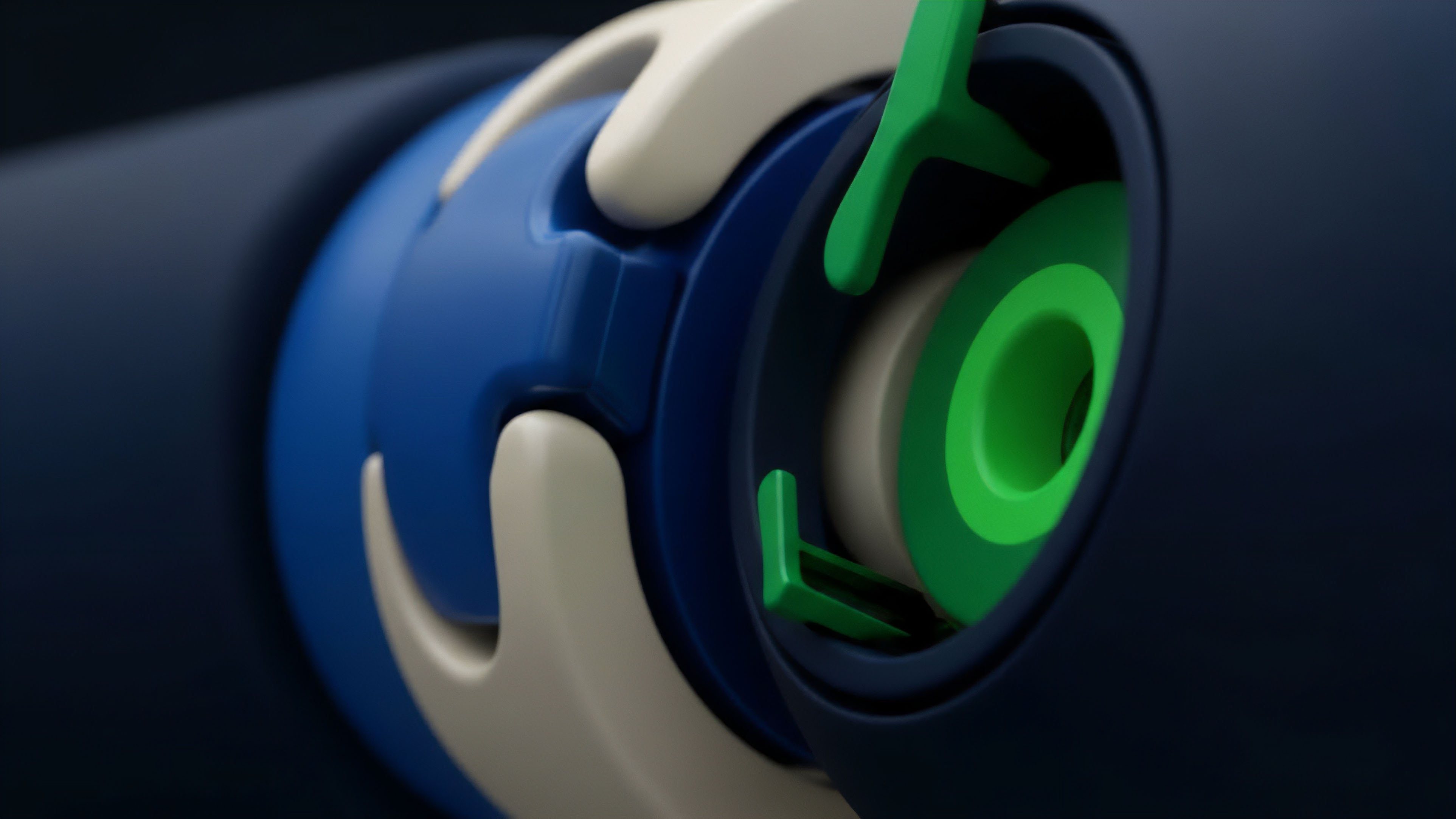
- Commit-Reveal Schemes: Users first submit a cryptographic commitment to their order details without revealing the content. Once a sufficient number of commitments are received, users reveal their full order details. This prevents front-runners from seeing the order before execution, as they only see a hash of the order, not the content itself.
- Encrypted Mempools and Private Order Flow: This involves routing transactions through specialized relayers that keep the transaction content encrypted until it is processed by a validator. The validator processes the encrypted transaction in a trusted execution environment (TEE) or through other cryptographic methods, preventing the validator from reading the order content.
A comparison of these approaches reveals a trade-off between simplicity and effectiveness. Batch auctions are relatively simple to implement but introduce latency and potentially suboptimal execution prices for some traders. Encrypted mempools offer stronger protection by addressing the information leakage directly at the infrastructure level, but they introduce new dependencies on centralized relayers or complex cryptographic overhead.
The fundamental design challenge for options front-running defenses lies in balancing the need for information privacy with the requirement for transparent, verifiable on-chain settlement.

Evolution
The evolution of front-running defenses has moved from basic protocol-level fixes to sophisticated infrastructure solutions. Early DeFi protocols attempted to mitigate front-running through simple methods like delaying order execution or using fixed-interval auctions. However, these methods often led to poor user experience due to increased latency and a lack of real-time price discovery.
The emergence of MEV-specific infrastructure, particularly through solutions like Flashbots, changed the landscape significantly. Flashbots, for example, introduced a private communication channel between users and validators. Users send their transactions directly to validators, bypassing the public mempool.
This prevents front-runners from observing pending orders. This approach, however, shifts the problem from public front-running to private front-running, where validators themselves can still extract MEV by collaborating with searchers in a closed environment. The options market, with its specific need for accurate pricing and liquidity provision, has driven further innovation.
We see a current trend toward order flow auctions where the right to execute a batch of transactions is sold to the highest bidder. This mechanism aims to return a portion of the MEV to the users themselves. For options, this means a large order can be routed through an auction where different market makers compete to provide the best price, effectively internalizing the front-running opportunity and passing the value back to the user.
This approach acknowledges that MEV cannot be eliminated entirely, but its value can be redirected to benefit the user rather than the adversarial actor.
| Defense Mechanism Type | Primary Goal | Impact on Options Trading |
|---|---|---|
| Batch Auctions | Eliminate time priority advantage. | Reduces front-running but increases execution latency and potentially price slippage. |
| Private Mempools | Obscure order information from public view. | Protects against public front-running but creates new challenges regarding validator collusion and transparency. |
| Order Flow Auctions | Redirect MEV profit to users. | Improves execution price for users by internalizing front-running competition. |

Horizon
Looking ahead, the next generation of front-running defenses will likely involve more fundamental shifts in protocol architecture and hardware integration. The current approach of managing MEV through private order flow and auctions is an intermediary step. The ultimate solution involves making the transaction content unreadable to the validator while still allowing for verifiable execution.
This future state relies on advancements in cryptographic techniques like Fully Homomorphic Encryption (FHE) and Trusted Execution Environments (TEEs). FHE allows computations to be performed on encrypted data without decrypting it first. If a user’s options trade can be processed in an FHE environment, the validator can execute the trade and update the state without ever knowing the specifics of the order.
This removes the information asymmetry at its root. Similarly, TEEs provide a hardware-level guarantee that code execution is private and untampered with. A validator could process transactions within a TEE, ensuring that they cannot read the transaction content or reorder transactions maliciously.
The future of options front-running defenses will likely transition from economic-based solutions to cryptographic and hardware-based solutions, aiming to eliminate the information asymmetry entirely rather than simply managing its symptoms.
The challenge here lies in performance and implementation complexity. FHE computations are significantly slower than traditional computations, creating scalability hurdles. TEEs introduce new trust assumptions on hardware manufacturers. The architectural decision for future options protocols will be whether to accept the latency costs of cryptographic solutions for absolute privacy, or to continue to optimize economic-based solutions that attempt to redistribute the extracted value. The direction of development suggests a preference for privacy-preserving solutions that eliminate the attack vector entirely, creating a more robust foundation for options markets.

Glossary

Options Premium Calculation

Front-Running Risk
Quantitative Finance
Arbitrage Exploitation Defense

Price Discovery

Hardware Integration
Inflationary Risk Defense

Protocol-Level Fixes

Economic Manipulation Defense