Essence
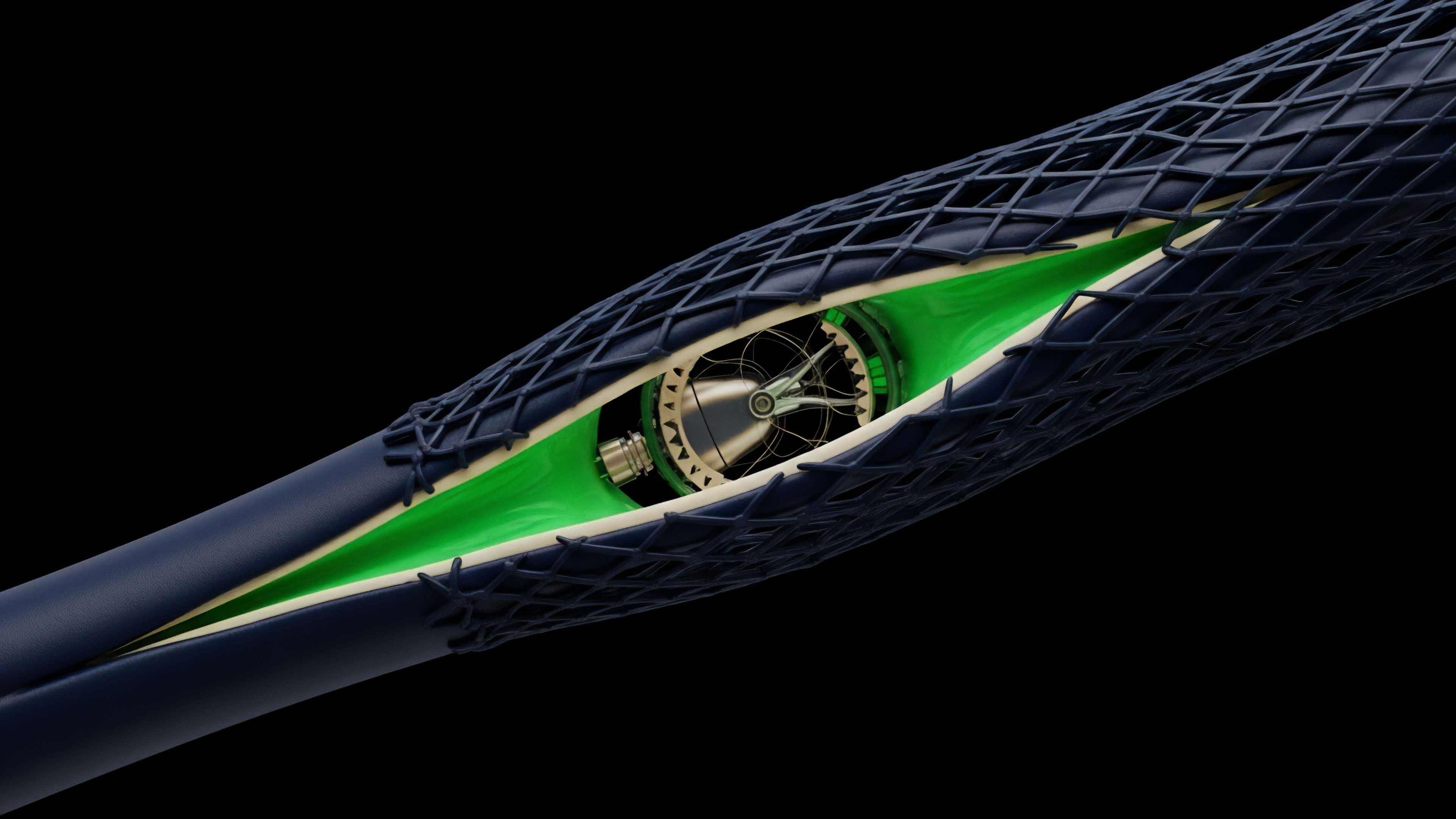
The core function of ZK-Encrypted Valuation Oracles is to provide verifiable proof of a derivative’s fair market value without revealing the proprietary input parameters used in the calculation ⎊ specifically, the implied volatility, the exact spot price used for settlement, or the counterparty’s position size. This technology resolves the fundamental tension in decentralized options markets between transparency and privacy. In traditional finance, valuation models are black boxes, trusted only by reputation.
In decentralized finance (DeFi), the valuation model must be transparent (the smart contract logic), yet the inputs ⎊ particularly volatility surfaces derived from private market maker data ⎊ are competitive secrets.
The oracle uses a Zero-Knowledge Proof (ZKP) system, typically a ZK-SNARK variant, to generate a cryptographic proof (the ‘witness’) that a specific output price P was correctly computed using a public function F (e.g. Black-Scholes or a Binomial Tree model) and a set of private inputs Iprivate. The proof is published on-chain, allowing any observer to cryptographically verify P’s correctness against F and public inputs Ipublic (like time to expiry, strike price) without ever learning Iprivate.
This mechanism transforms a trust assumption into a mathematical certainty.
ZK-Encrypted Valuation Oracles establish cryptographic truth for options pricing, ensuring a calculated value is correct without disclosing the volatility or proprietary market inputs used to obtain it.
This capability is not solely about masking trade secrets; it is a critical infrastructure component for building robust, high-leverage decentralized options protocols. Without input privacy, market makers are immediately susceptible to sophisticated front-running, as their intended volatility adjustments ⎊ the most sensitive data point in options pricing ⎊ would be instantly revealed on-chain before the trade is executed. This system design protects the market maker’s alpha, thereby encouraging deeper liquidity and more accurate pricing surfaces, which are prerequisites for any system aspiring to compete with centralized derivatives exchanges.

Origin
The genesis of ZK-Encrypted Valuation Oracles stems from two converging research domains: the development of ZK-SNARKs in academic cryptography and the practical necessity of mitigating Miner Extractable Value (MEV) in DeFi. ZKPs were initially conceived as a purely theoretical concept in the 1980s, but their computational viability for complex functions only materialized with the advent of efficient constructions like Groth16 and PLONK. The application to financial derivatives became urgent as early decentralized options protocols failed to attract serious institutional liquidity.

The Black-Scholes Circuit Problem
The core challenge, which necessitated the ZK solution, lies in the nature of options pricing models. The Black-Scholes formula, the canonical benchmark, requires calculating the cumulative distribution function of the standard normal distribution ⎊ which involves the error function, erf(x). Expressing such non-linear, floating-point operations within the finite field arithmetic of a ZK-SNARK’s R1CS (Rank-1 Constraint System) or PLONK circuit is computationally prohibitive and prone to precision loss.
- Computational Mismatch: Traditional options pricing uses high-precision floating-point arithmetic, while ZK-SNARKs operate on large prime fields, requiring approximations and complex polynomial constraints for non-linear functions.
- The Oracle Design Precedent: Early attempts at price privacy used trusted execution environments (TEEs) like Intel SGX. The shift to ZKPs represents a move away from hardware-based trust to cryptographic certainty ⎊ a philosophical imperative for a decentralized financial system.
- MEV as the Catalyst: The rise of front-running bots exploiting predictable on-chain price updates provided the immediate, economic impetus. A market maker’s calculated fair price, if revealed, becomes a public good for arbitrageurs before the transaction confirms, effectively taxing liquidity providers.
The current ZK oracle architecture is therefore a direct response to the computational physics of the blockchain ⎊ latency, finite field arithmetic, and the adversarial environment of the mempool. It is a cryptographic firewall against the predatory market structure that DeFi’s transparency created.

Theory
The theoretical foundation rests on the mathematical reduction of the option pricing function F into a vast, verifiable arithmetic circuit. This process is where the quantitative and cryptographic domains collide, defining the system’s practical limits.

Arithmetic Circuit Construction and Cost
To price an option, the system must execute the Black-Scholes formula, C = S N(d1) – K e-rτ N(d2), within the circuit. The most expensive operations are the non-linear components: the exponential function e-rτ and the standard normal cumulative distribution function N(d1), N(d2).
- Approximation of Non-Linearity: Since native floating-point operations are unavailable, the system uses high-degree polynomial approximations (e.g. Taylor series or rational function approximations) to compute the necessary non-linear functions. This trade-off between the degree of the polynomial and the required financial precision is the first-order design constraint.
- Constraint Count and Proof Time: The complexity of the circuit is measured by the number of constraints (gates). A single Black-Scholes calculation can require tens of thousands of constraints, which directly dictates the computational cost and time required for the market maker to generate the proof (the ‘prover’s’ work).
- Fixed-Point Arithmetic: All inputs and intermediate calculations must be converted from floating-point numbers to fixed-point integers, a necessary step for ZK-SNARK compatibility. This conversion introduces a quantifiable rounding error, which must be carefully managed to keep the option price within acceptable market tolerances ⎊ our inability to respect this error budget is a major design vulnerability.
The theoretical ideal of perfect privacy is thus bounded by the practical cost of the circuit. A faster, cheaper proof generation sacrifices financial precision, while higher precision incurs significant latency, making the resulting price stale by the time the proof is verified.
The fundamental constraint in ZK options pricing is the cryptographic cost of proving non-linear financial functions, which forces a trade-off between computational speed and financial precision.

Greeks Sensitivity and ZK-Proof Scope
The true power of the ZK oracle extends beyond the price P itself. The prover can simultaneously generate a proof for the correctness of the option’s first- and second-order risk sensitivities (the Greeks: Delta, Gamma, Vega, Theta). This allows a decentralized margin engine to verify the correctness of a counterparty’s risk profile without revealing the actual price or the portfolio composition.
| Metric Verified | Private Input | System Implication |
|---|---|---|
| Option Price (P) | Implied Volatility (σ) | Front-Running Mitigation |
| Delta (δ) | Spot Price (S) | Margin Call Correctness |
| Vega (mathcalV) | Portfolio Exposure | Systemic Risk Assessment |
The ability to verify Delta and Vega privately is paramount. It means that an options clearing house can confirm a market maker has sufficient capital to cover their portfolio’s risk exposure to a change in spot price or volatility, yet no competitor can observe the specific parameters of their hedge. This transforms risk management into a cryptographically enforced, private-but-verifiable process.

Approach
The current implementation approach for ZK-Encrypted Valuation Oracles is a two-stage hybrid system that prioritizes prover efficiency over pure on-chain verification, a pragmatic concession to the computational burden of complex circuits.

Off-Chain Proof Generation
The market maker’s private server, the ‘prover,’ executes the following steps:
- Input Sanitization: The private inputs (e.g. proprietary volatility surface data) are converted to fixed-point integers compatible with the chosen prime field.
- Circuit Execution: The Black-Scholes or a custom volatility-adjusted pricing model is executed within the ZK-SNARK circuit. This is the computationally heaviest part, where millions of constraints are solved.
- Proof Output: A concise cryptographic proof, typically a few hundred bytes, is generated, asserting the correctness of the final price P and the associated Greeks δ, mathcalV.
This off-chain process is essential; generating the proof on a decentralized virtual machine would be prohibitively slow and expensive. The system delegates the intensive computational work to the market maker’s hardware, demanding only that they submit the final, small, verifiable proof.

On-Chain Verification and Settlement
The decentralized options protocol’s smart contract acts as the ‘verifier.’
- Proof Submission: The market maker submits the calculated price P and the cryptographic proof to the options protocol.
- Verifier Execution: The smart contract executes the ZK-SNARK verifier function. This function takes the public inputs (strike, expiry), the claimed output price P, and the proof itself. Crucially, verification is computationally light ⎊ a constant-time operation ⎊ making it cheap and fast for the blockchain to execute.
- Transaction Finality: If the verification succeeds, the smart contract cryptographically guarantees that the price P was calculated correctly from the hidden inputs, and the trade is executed at that price. This sequence ensures that the market maker’s trade is atomic, verifiable, and protected from front-running.
The current ZK approach relies on delegating the heavy computational burden of proof generation off-chain, while the on-chain verifier performs a computationally light, constant-time check to confirm price integrity.
This hybrid architecture represents a strategic trade-off. We accept a minor increase in the market maker’s hardware and latency costs for proof generation in exchange for a massive gain in market maker privacy, which directly translates to deeper liquidity and a more resilient market structure. The focus is on making the market adversarial only at the point of capital allocation, not at the point of information transmission.
Evolution
The evolution of ZK-Encrypted Valuation Oracles is a story of moving from cumbersome, trusted setups to universal, transparent constructions, paralleled by a relentless pursuit of greater circuit efficiency for complex financial functions.
From Trusted Setup to Universal Composability
The initial ZK-SNARKs (e.g. Groth16) required a Trusted Setup ⎊ a multi-party computation to generate the proving key, which, if compromised, would allow an attacker to forge proofs and prices. The industry’s migration to Universal and Updatable SNARKs (like PLONK and Marlin) was a significant architectural shift.
These systems require a one-time, universally-used setup that can be continually updated, eliminating the single point of failure and significantly lowering the barrier to adoption for new options protocols. The removal of the trust assumption is paramount for a financial primitive.
ZK-STARKs and Post-Quantum Futures
The next phase of evolution involves the adoption of ZK-STARKs. While ZK-SNARKs currently dominate due to their smaller proof size, ZK-STARKs offer two critical advantages:
- No Trusted Setup: STARKs are transparent and require no setup ceremony, simplifying the system’s operational physics.
- Post-Quantum Security: STARKs rely on hash functions, making them resistant to attacks from quantum computers ⎊ a long-term existential risk for any financial system built on elliptic curve cryptography.
The trade-off is the larger proof size and slightly longer verification time for STARKs, but as on-chain data costs decrease and computational power increases, the superior security properties of STARKs will likely make them the standard for proving the correctness of high-value, long-lived financial contracts.

The Circuit Compiler Wars
A more recent, crucial development is the emergence of high-level programming languages and compilers (e.g. Circom, Leo, Cairo) that simplify the conversion of complex financial logic into ZK-friendly arithmetic circuits. This has democratized circuit design, shifting the bottleneck from specialized cryptographic engineering to optimizing the underlying fixed-point approximations.
The ongoing competition between these compilers to produce the smallest, most efficient circuit for the Black-Scholes and volatility smile functions will determine which options protocol can offer the most precise and lowest-latency pricing.

Horizon
The future trajectory of ZK-Encrypted Valuation Oracles extends far beyond simple options pricing; it is the foundation for a fully private, verifiable Decentralized Dark Pool for derivatives. This system will alter market microstructure by eliminating the information leakage that defines current on-chain trading.

Private Order Matching and Auction Design
The current oracle verifies the price of a single option. The horizon is to use ZKPs to verify the correctness of an entire order matching process. This would involve a ZK circuit that takes private bids and asks from market makers, executes a pre-defined auction mechanism (e.g. a batch auction or a continuous double auction), and proves the final, clearing price and matched quantities ⎊ all without revealing the order book depth or individual participant intentions.
This capability would fundamentally address the adversarial nature of the public mempool. Market participants could submit their full, true intentions, secure in the knowledge that only the provably fair execution result will be published on-chain. The system transitions from a transparent-but-predatory market to a private-but-verifiable market.

Systemic Risk Aggregation
A powerful, second-order effect is the ability to use ZKPs for regulatory reporting and systemic risk management. Regulators or a decentralized stability fund could be granted a specific ZK-verifier key that allows them to audit the aggregated risk of all open positions in a protocol (e.g. the sum of all δ and mathcalV exposures) without ever learning the underlying individual positions or proprietary pricing data. This offers a path to regulatory compliance and contagion mitigation ⎊ the system can prove it is solvent and not over-leveraged without sacrificing the privacy of its users.
| Current System (Transparent) | ZK Horizon (Private Verifiable) |
|---|---|
| Public Order Book | ZK-Verified Matching Engine |
| MEV/Front-Running Risk | Cryptographically Enforced Privacy |
| Revealed Volatility Surface | ZK-Encrypted Volatility Inputs |
| Regulation by Disclosure | Regulation by ZK-Proof Audit |
The systemic implications are clear. The ZK oracle, when scaled, transforms a decentralized exchange from a transparent, vulnerable mechanism into a resilient, computationally protected institution. It is the necessary architectural upgrade to handle the leverage and complexity of a multi-trillion dollar derivatives market.
Glossary

Fixed-Point Conversion Errors

Dynamic Pricing Mechanisms in Amms

Blockchain Data Security
Private Order Execution
Zero-Knowledge Architecture
Circuit Complexity

Zero Knowledge Succinct Non Interactive Argument of Knowledge

Systemic Risk Audit

Systemic Stability in Defi