
Essence
The core challenge in decentralized finance for options trading revolves around data source authenticity. A derivative contract, particularly an options contract, requires a precise, indisputable price at expiration to determine the payoff. In traditional markets, this price is provided by a centralized, regulated exchange or data provider.
The decentralized nature of blockchain protocols means they cannot inherently access external market data. This fundamental limitation creates the “oracle problem,” where a trustless system must rely on a trusted external source for critical information. If this data source is compromised or manipulated, the entire settlement logic of the options contract fails.
The integrity of the data feed is not a secondary consideration; it is the single most important variable for determining a derivative protocol’s systemic risk profile.
The options market structure introduces unique complexities compared to spot trading. An option’s value is highly sensitive to changes in implied volatility, interest rates, and the underlying asset’s price, all of which must be fed into the protocol’s pricing and risk models. A small error in a data feed can lead to significant mispricing, resulting in incorrect liquidations or massive value transfers between counterparties.
This sensitivity makes options protocols particularly vulnerable to data manipulation attacks. The architectural goal is to design a system where the cost of manipulating the data source exceeds the profit gained from exploiting the derivative contract based on that manipulated data.
Data source authenticity is the foundation upon which all trustless options settlement mechanisms are built, directly impacting pricing accuracy and systemic risk.
Origin
The oracle problem originated with the earliest smart contracts, which were designed to execute deterministic logic based on data present on the blockchain. The moment a contract needed information from the external world ⎊ like the price of Bitcoin in USD ⎊ it required an external data feed, or oracle. The first solutions were simplistic, often relying on a single, centralized entity to provide the data.
This created a single point of failure, directly contradicting the core ethos of decentralization. Early attempts to create decentralized derivatives protocols struggled with this vulnerability. If the single oracle feed failed or provided malicious data, the contract would settle incorrectly, leading to immediate financial losses for users.
The evolution of data authenticity in crypto options mirrors the transition from simple price feeds to robust decentralized oracle networks (DONs). Early derivatives protocols, such as those built on platforms like Augur, relied on a prediction market model where participants would vote on outcomes. This proved effective for specific events but was too slow and subjective for high-frequency options settlement.
The development of DONs, pioneered by projects like Chainlink, introduced a new paradigm. Instead of trusting a single source, protocols began aggregating data from multiple independent nodes and data providers. This aggregation model significantly raised the cost of manipulation, creating a more secure foundation for decentralized options protocols.

Theory
From a quantitative finance perspective, data source authenticity directly impacts the accuracy of option pricing models and risk calculations. The most critical data inputs for a Black-Scholes model ⎊ or any derivatives pricing framework ⎊ are the underlying asset price, volatility, and interest rate. If the underlying asset price feed is compromised, the model output becomes invalid.
The integrity of the data feed directly affects the calculation of the Greeks, specifically Delta and Gamma, which measure the sensitivity of the option’s price to changes in the underlying asset. A bad price feed results in inaccurate Delta hedging, exposing market makers to significant, unforeseen risks.
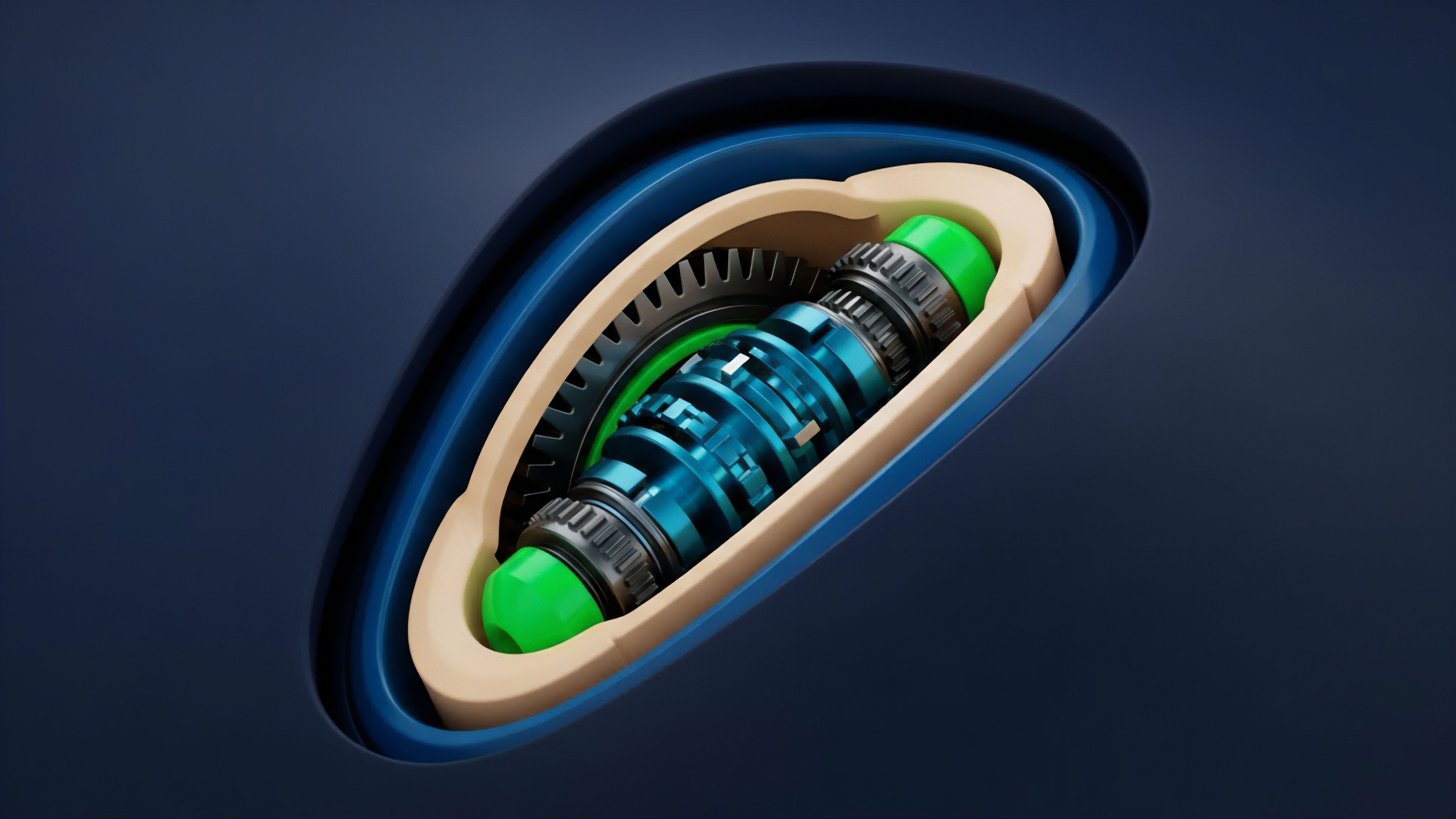
The choice of data aggregation methodology is a key theoretical challenge. A protocol must choose between using a spot price or a time-weighted average price (TWAP) for settlement. A spot price oracle provides the most current price but is highly susceptible to flash loan attacks, where an attacker can temporarily manipulate the price on a decentralized exchange (DEX) to trigger a favorable liquidation or settlement.
A TWAP calculates the average price over a specified time window, mitigating the risk of short-term manipulation. However, a TWAP introduces “oracle lag,” which means the price used for settlement does not reflect the immediate market reality. This lag can be problematic during periods of extreme volatility, where the settlement price may differ significantly from the current market price, leading to potential counterparty risk.
The design choice between these methods represents a fundamental trade-off between speed and security.
The concept of cryptoeconomic security further refines the theoretical approach. The security of the data feed relies on economic incentives rather than absolute trust. The oracle network’s design ensures that it is more profitable for nodes to behave honestly than to collude and manipulate the data.
This is achieved through mechanisms like staking, where nodes must lock up capital that can be slashed if they provide incorrect data. The theoretical model must calculate the precise amount of capital required to deter manipulation, ensuring the cost of attack outweighs the potential profit from exploiting the options protocol.
The integrity of data feeds for options pricing is determined by the trade-off between the speed of spot data and the resilience of time-weighted averages.
| Data Aggregation Method | Description | Risk Profile for Options |
|---|---|---|
| Spot Price Oracle | Provides the most current market price from a single source or instantaneous snapshot of aggregated sources. | High vulnerability to flash loan attacks and rapid price manipulation; immediate pricing accuracy but low security during high volatility. |
| Time-Weighted Average Price (TWAP) | Calculates the average price over a defined time interval (e.g. 10 minutes) to smooth out short-term fluctuations. | High resilience against short-term manipulation; introduces “oracle lag,” which can create counterparty risk during sudden market movements. |
| Decentralized Oracle Network (DON) | Aggregates data from multiple independent nodes and data sources to create a consensus price. | Strong security against single-source failure; cost of manipulation increases with the number of nodes and data sources. |

Approach
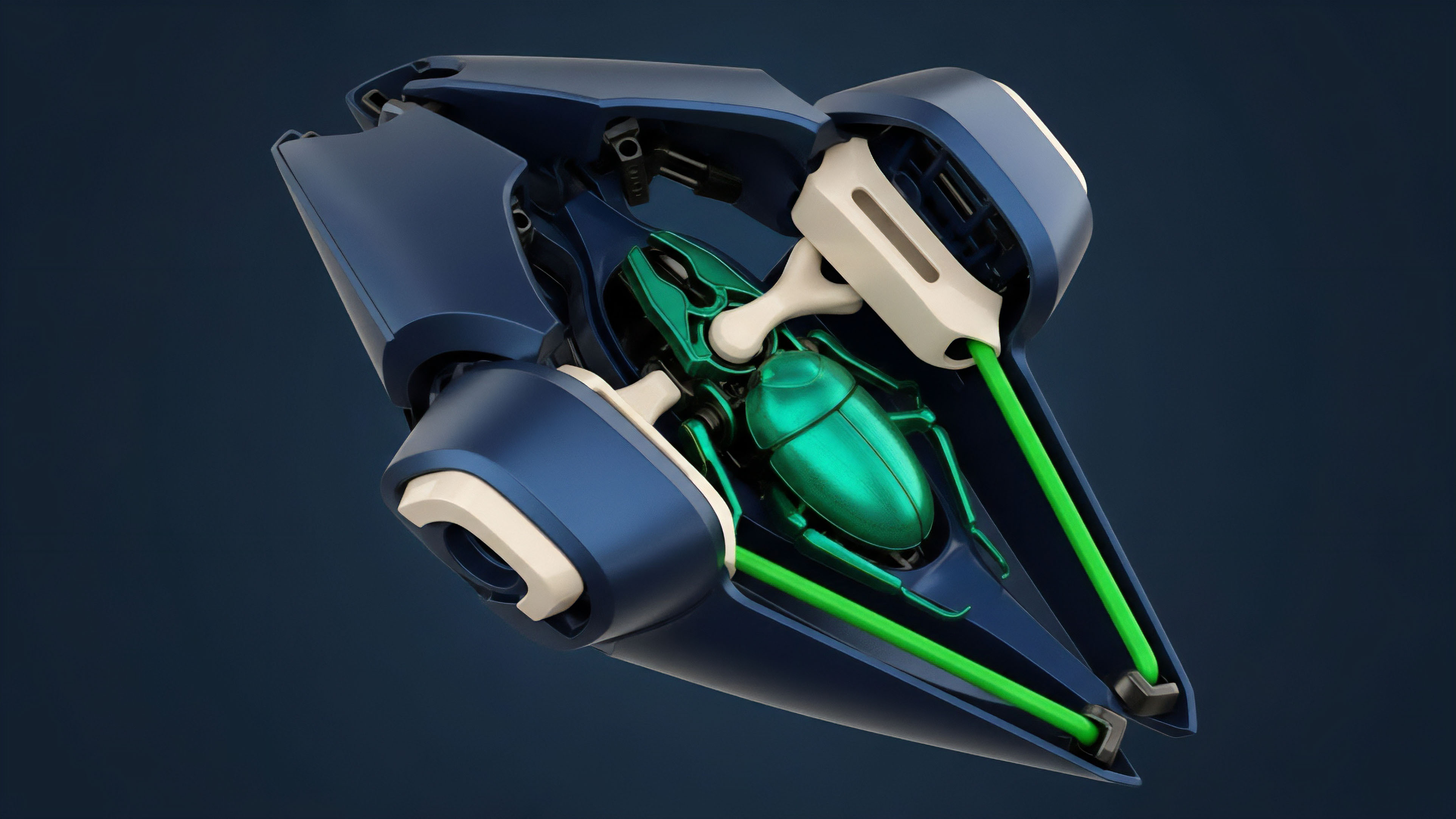
The current approach to achieving data source authenticity for crypto options protocols involves a layered architecture focused on redundancy and economic incentives. The first layer involves data source selection and aggregation. Protocols typically do not rely on a single data provider.
Instead, they aggregate data from a diverse set of sources, including major centralized exchanges and decentralized exchanges, to reduce reliance on any single entity. The data is then processed through aggregation algorithms that filter out outliers and calculate a robust median price. This filtering process is essential for preventing a single malicious data point from corrupting the entire feed.
The second layer is cryptoeconomic security. This layer ensures that data providers are incentivized to provide accurate information. Oracle networks implement staking mechanisms where data providers lock up collateral.
If a data provider submits malicious data that is proven incorrect, their staked collateral is slashed. This mechanism ensures that providing bad data results in a net loss for the attacker. The protocol’s design must calculate the required stake size to make an attack prohibitively expensive.
This cost-of-attack analysis is critical for determining the protocol’s overall security budget.
The third layer involves dispute resolution. No oracle system is infallible. A robust options protocol must have a mechanism for challenging potentially incorrect data.
This often involves a governance-based dispute process where users or data providers can submit evidence that the current oracle price is incorrect. If the challenge is successful, the oracle price is updated, and the malicious data provider is penalized. This process ensures that data authenticity is not a static property but rather a continuously verified state, where the community actively participates in maintaining integrity.
| Oracle Design Principle | Functional Requirement for Options | Security Implications |
|---|---|---|
| Data Source Diversity | Aggregating price data from multiple centralized and decentralized exchanges. | Prevents single-source failure and makes manipulation of a single exchange less effective. |
| Outlier Filtering Algorithms | Algorithms that discard extreme data points that deviate significantly from the median price. | Protects against sudden price spikes caused by low liquidity events or manipulation on specific exchanges. |
| Cryptoeconomic Staking | Requiring data providers to stake collateral that can be slashed upon malicious behavior. | Aligns incentives by making the cost of providing bad data greater than the potential profit from exploitation. |
Evolution
The evolution of data source authenticity has been driven by the increasing complexity of crypto derivatives. Early options protocols required only a single price feed for settlement. However, as protocols expanded to offer more sophisticated instruments ⎊ such as options with different strikes and expirations ⎊ the data requirements grew exponentially.
The market requires accurate implied volatility (IV) surfaces, which represent the market’s expectation of future volatility across different strike prices and maturities. Generating these IV surfaces requires a more complex data input than a simple price feed.
The challenge lies in the trade-off between decentralization and data quality. While a simple price feed can be easily decentralized and verified by multiple nodes, a complex IV surface is harder to generate reliably in a trustless manner. Market makers often calculate these surfaces internally, and protocols must decide whether to rely on a few centralized data providers for this specific data or attempt to decentralize the calculation itself.
The current trend suggests a move toward specialized oracles that provide specific, high-quality data inputs rather than generic price feeds.
This evolution introduces new regulatory arbitrage considerations. As data authenticity becomes more critical, regulators are likely to focus on the provenance and auditability of these data feeds. Protocols seeking to operate within regulated jurisdictions may face pressure to use specific, approved data sources, potentially forcing a centralization of data provision to meet compliance requirements.
This creates a tension between the goal of a truly decentralized financial system and the need for regulatory compliance, which demands auditable data sources.
The complexity of options requires a transition from simple price feeds to specialized data inputs, creating a tension between data quality and decentralization.

Horizon
Looking forward, the future of data source authenticity in crypto options points toward two major developments: verifiable computation and cross-chain interoperability. Verifiable computation, particularly through zero-knowledge proofs (ZKPs), offers a pathway to solve the oracle problem by bringing data verification on-chain. Instead of simply trusting an external oracle, a protocol could receive a ZKP that verifies the data’s integrity without revealing the source or the full dataset.
This approach allows a protocol to prove that the data used for settlement was calculated correctly based on a specific set of rules, creating a truly trustless data pipeline.
Another significant development is the rise of cross-chain oracles. As the crypto landscape fragments into multiple Layer 1 and Layer 2 solutions, options protocols must be able to settle contracts using assets from different chains. This requires data feeds that can reliably communicate across chains without introducing new points of failure.
The design of these cross-chain communication protocols ⎊ and the mechanisms to ensure data integrity during transit ⎊ will define the security of options in a multi-chain environment. The challenge lies in ensuring that the data source remains authentic even as it traverses different consensus mechanisms and network architectures.
The ultimate goal for data source authenticity is to create a data layer that is as secure and decentralized as the underlying settlement layer. This involves moving away from relying on external, off-chain data feeds toward a model where data integrity is mathematically proven on-chain. This transition requires significant advancements in cryptographic research and protocol design, but it offers the only path toward truly resilient, trustless options markets that can scale without sacrificing security.

Glossary

Protocol Physics

Yield Source Aggregation

Open Source Financial Logic

Data Source Centralization

Oracle Design Principles

Oracle Problem

Open Source Matching Protocol

Data Integrity

Data Source Attacks






