Essence
Data Integrity Risk represents the foundational vulnerability in decentralized finance where the accuracy and trustworthiness of external data feeds, known as oracles, cannot be guaranteed. In the context of crypto options, this risk specifically manifests when the underlying asset’s price, volatility data, or settlement information is manipulated or inaccurate. The deterministic nature of smart contracts means they execute based on the data provided, without independent judgment.
If the input data is flawed, the contract’s output ⎊ whether it is an options settlement, margin call, or liquidation ⎊ will also be flawed. This creates a systemic point of failure where a single corrupted data feed can lead to significant financial loss for participants and destabilize the entire protocol.
Data Integrity Risk in crypto options protocols arises from the reliance on external oracles for price feeds, creating a critical vulnerability where manipulated or inaccurate data can lead to incorrect settlements and systemic instability.
The core challenge of Data Integrity Risk is the “oracle problem.” Smart contracts are isolated computational environments; they cannot natively access real-world information like market prices or asset values. An oracle serves as the bridge, relaying this off-chain data to the on-chain environment. For options, this data includes not only the spot price of the underlying asset but also volatility metrics and interest rates, all necessary inputs for accurate pricing and risk management.
The integrity of these inputs determines the financial solvency of the options protocol. A malicious actor exploiting this vulnerability can profit from incorrect pricing or trigger liquidations at manipulated prices, leading to a cascade of failures.

Origin
The origin of Data Integrity Risk in crypto derivatives stems directly from the transition from traditional, centralized exchanges (TradFi) to decentralized protocols (DeFi). In TradFi, data integrity is maintained through centralized, regulated entities like Bloomberg or Refinitiv, which act as trusted data providers. These providers operate within legal frameworks and are subject to regulatory oversight, making data manipulation difficult and costly.
The assumption of trust in these centralized entities is foundational to TradFi market microstructure.
When derivatives moved onto decentralized ledgers, this trust model was discarded. Early DeFi protocols attempted to solve the oracle problem in simplistic ways, often by relying on single-source or small-set multisig feeds. These early solutions proved brittle.
The most prominent early examples of data integrity failures occurred in lending protocols where flash loan attacks were used to manipulate the price of a collateral asset on a specific decentralized exchange (DEX). The protocol’s oracle, which pulled data from that single DEX, would then register the manipulated price. This allowed the attacker to borrow significantly more value than their collateral was worth, draining the protocol’s liquidity.
The vulnerability was not in the smart contract code itself, but in the trust assumptions embedded in the data source.
Theory
From a quantitative finance perspective, Data Integrity Risk directly compromises the assumptions underlying options pricing models. The Black-Scholes model and its derivatives require five inputs: spot price, strike price, time to expiration, risk-free rate, and volatility. Data Integrity Risk primarily affects the accuracy of the spot price and the volatility inputs.
A manipulated spot price immediately invalidates the calculated options premium and associated Greeks. This creates a critical vulnerability for market makers and liquidity providers.

Impact on Options Greeks
The Greeks ⎊ delta, gamma, theta, vega ⎊ measure an option’s sensitivity to changes in underlying variables. The calculation of these sensitivities relies heavily on accurate real-time data. When data integrity fails, the implications are profound:
- Delta Risk: Delta measures the rate of change of an option’s price relative to a change in the underlying asset’s price. If the oracle provides a stale or manipulated spot price, a market maker’s delta hedge will be fundamentally incorrect. They might be under-hedged or over-hedged, leading to significant losses as the actual market price diverges from the oracle’s price.
- Vega Risk: Vega measures an option’s sensitivity to changes in implied volatility. For many crypto options protocols, implied volatility is calculated based on recent price movements or derived from on-chain data. If the spot price data is manipulated, the calculation of historical volatility and the implied volatility surface will be distorted, leading to mispricing of options and incorrect risk exposure.
- Liquidation Cascades: Data integrity failures are most dangerous during periods of high market volatility. If a price feed stalls or provides an incorrect value, it can trigger liquidations for positions that are not actually undercollateralized. This can create a positive feedback loop where forced liquidations further destabilize the market, leading to systemic contagion.

Oracle Attack Vectors
Data Integrity Risk can be categorized by specific attack vectors that exploit the oracle mechanism:
- Flash Loan Manipulation: A short-term, uncollateralized loan is used to manipulate the price of an asset on a low-liquidity DEX. The oracle reads this manipulated price, and the attacker executes a transaction against the protocol based on the false price before repaying the loan.
- Stale Data Attack: The oracle fails to update in a timely manner during a period of high market volatility. The on-chain price does not reflect the actual market price, allowing arbitrageurs to exploit the difference at the expense of liquidity providers.
- Data Source Compromise: A centralized data source used by a decentralized oracle network is compromised, either by an external hack or by internal collusion. The compromised data feed then propagates across the network, leading to widespread protocol failure.
Approach
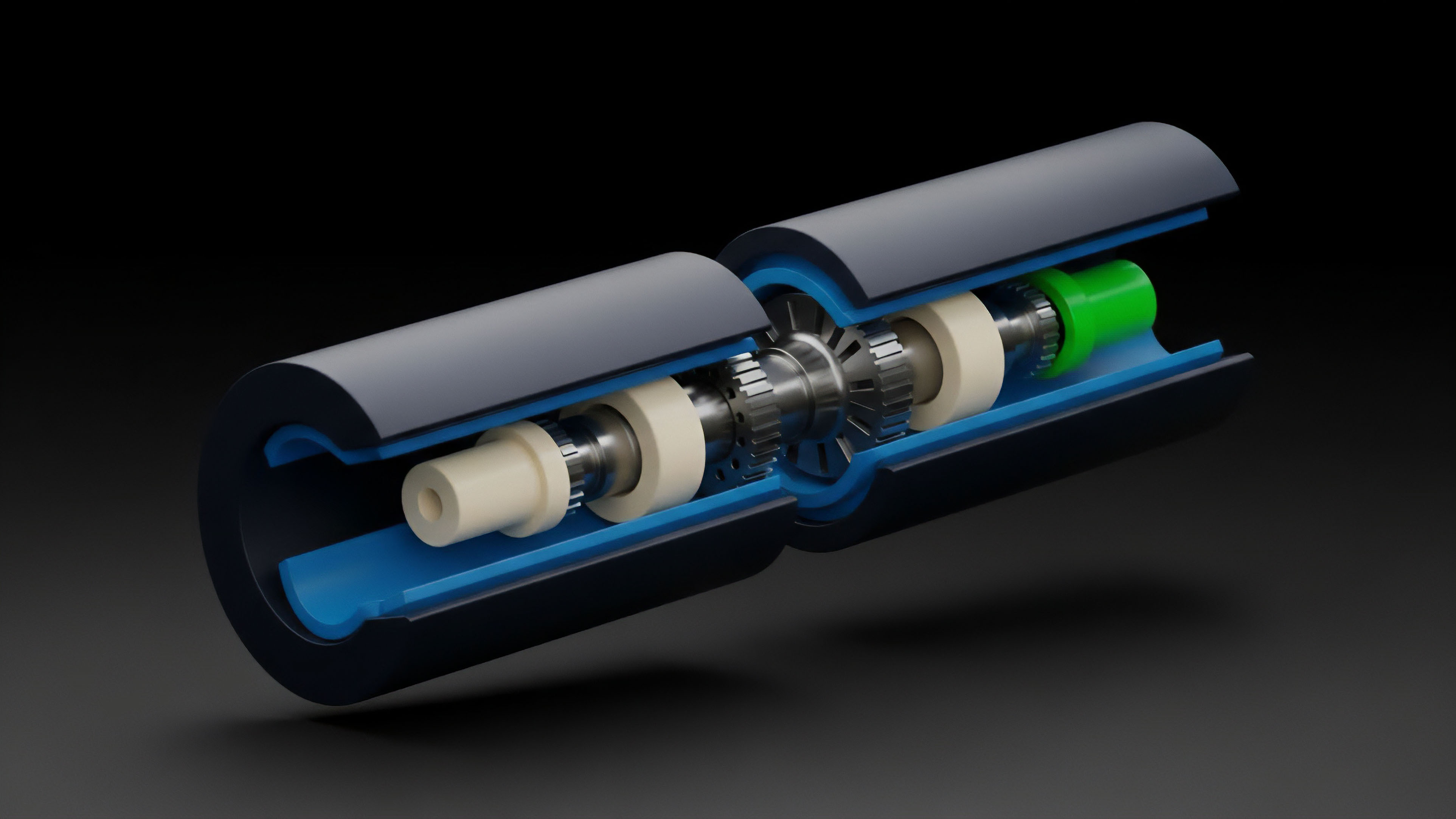
The current approach to mitigating Data Integrity Risk involves building decentralized oracle networks that aggregate data from multiple sources. These networks attempt to replace the trust in a single centralized entity with a consensus mechanism among multiple data providers. The goal is to make the cost of manipulating the data feed prohibitively high by requiring an attacker to compromise numerous independent sources simultaneously.

Oracle Network Architectures
Two primary architectural approaches are currently employed to address data integrity:
- Decentralized Aggregation: Oracles like Chainlink utilize a network of independent node operators that source data from various off-chain exchanges and data aggregators. These nodes submit their price data to a smart contract, which then calculates a median or weighted average price. This method assumes that the majority of nodes are honest and that the cost of compromising a significant portion of the network exceeds the potential profit from the attack.
- Pull vs. Push Models: Data delivery models present a trade-off between latency and security. In a push model, data is constantly updated on-chain by the oracle network. This provides low latency but can be expensive due to transaction fees. In a pull model, a protocol requests data from the oracle only when needed. This reduces cost but introduces potential for stale data, as the protocol may not receive an update during a sudden price change.
For options protocols, the choice between these models dictates the type of risk exposure. High-frequency options trading requires low latency, favoring push models despite their higher cost and potential for manipulation. Longer-term options can tolerate pull models, but face a different set of risks associated with data staleness.
Effective mitigation of Data Integrity Risk requires a multi-faceted approach, balancing the cost of data updates with the need for low latency and high security through decentralized aggregation.

Risk Mitigation Strategies
Protocols employ several strategies to manage Data Integrity Risk beyond basic oracle design:
- Time-Weighted Average Price (TWAP): Instead of relying on a single, instantaneous price, protocols use a TWAP over a specified period. This makes flash loan attacks less effective, as the manipulated price must be sustained for a longer duration, increasing the attacker’s cost and risk.
- Circuit Breakers: Protocols implement circuit breakers that pause trading or liquidations if the price change exceeds a predefined threshold within a short timeframe. This provides a manual or automated mechanism to halt operations during suspected data integrity failures, allowing time for investigation and resolution.
- Insurance and Backstops: Protocols establish insurance funds or utilize backstop mechanisms where capital providers step in to cover losses resulting from oracle failures. This transfers the financial risk from individual users to a pool of risk-takers, but requires careful economic modeling to ensure the fund remains solvent.

Evolution
The evolution of Data Integrity Risk in crypto options is driven by the increasing complexity of derivatives and the shift from simple spot prices to more complex volatility data. Early oracle solutions focused primarily on providing a reliable spot price for collateral valuation in lending protocols. However, options pricing requires a different set of data inputs, specifically reliable volatility surfaces and implied volatility indices.

Volatility Oracles and Exotic Data Feeds
As decentralized options protocols mature, they move beyond simple European options to offer exotic options, perpetual options, and volatility products. These instruments require oracles capable of providing data on implied volatility (IV) and historical volatility (HV). The integrity of a volatility oracle is significantly more complex to verify than a spot price oracle.
A spot price can be cross-referenced across multiple exchanges. Volatility, however, is often derived from a calculation specific to a particular options protocol’s market data. This introduces a new layer of risk where the data integrity vulnerability is not just external manipulation, but internal calculation errors or inconsistencies across protocols.

Data Integrity Risk in Synthetic Assets
The concept of data integrity extends to synthetic assets, which mimic the price of off-chain assets. These assets rely on oracles to maintain their peg. If a synthetic asset’s oracle is compromised, the entire system of options built on top of it collapses.
This creates a chain reaction where a data integrity failure in one protocol can propagate across multiple protocols that utilize the same synthetic asset as collateral or underlying value.

The Data Integrity Risk Vs. Latency Trade-off
The core tension in the evolution of data integrity solutions remains the trade-off between latency and security. High-frequency options trading demands near-instantaneous data feeds to facilitate accurate pricing and hedging. However, achieving this speed often necessitates compromises in decentralization, as data aggregation takes time.
The market’s demand for faster execution pushes protocols toward solutions that increase latency, potentially reintroducing centralization risks. The market must determine whether it prioritizes low latency for efficiency or high security for resilience.

Horizon
Looking ahead, the future of Data Integrity Risk mitigation in crypto options points toward two distinct, yet potentially converging, pathways: cryptographic verification and market-based incentives.

Zero-Knowledge Proofs for Data Integrity
The most promising technological solution lies in leveraging zero-knowledge proofs (ZKPs). ZKPs allow for the verification of data without revealing the data itself. In the context of oracles, a ZKP could be used to prove that an off-chain calculation (such as a volatility index or a spot price average) was performed correctly using a specific set of inputs, without requiring the smart contract to re-calculate everything on-chain.
This could enable high-frequency data feeds with strong cryptographic guarantees, effectively eliminating the trust assumption in the oracle provider.

Market-Based Incentive Structures
Another pathway involves designing robust incentive structures where data providers are financially rewarded for accuracy and penalized for providing incorrect data. This approach relies on game theory to align incentives. Data providers stake collateral, which can be slashed if they submit inaccurate information.
This economic mechanism creates a high cost for malicious behavior. The design of these incentive structures must be carefully calibrated to avoid scenarios where a collective of data providers colludes to manipulate prices for mutual gain.

The Convergence of On-Chain and Off-Chain Data
The long-term horizon for Data Integrity Risk in options involves a shift toward fully on-chain synthetic assets. If an asset’s price discovery can be conducted entirely on-chain through decentralized exchanges and liquidity pools, the need for external oracles decreases. However, this creates a new challenge: ensuring the on-chain liquidity pools are sufficiently deep and resilient to manipulation.
The ultimate solution will likely involve a hybrid model where off-chain data feeds are used for broad market context, while on-chain data is prioritized for settlement and liquidation logic.
| Risk Mitigation Approach | Mechanism | Pros | Cons |
|---|---|---|---|
| Decentralized Aggregation | Median calculation from multiple nodes | Resilient to single-node failure; high cost to manipulate | Higher latency; requires robust incentive design |
| Time-Weighted Average Price (TWAP) | Averages price over a time window | Mitigates flash loan attacks | Stale data risk during rapid market movements |
| Zero-Knowledge Proofs (ZKPs) | Cryptographic verification of off-chain data calculation | Strongest security guarantees; potential for low latency | High computational cost; early stage development |

Glossary

Consensus Layer Integrity

Data Integrity Assurance and Verification

Staked Capital Data Integrity
Market Microstructure

Oracle Data Integrity

Statistical Integrity

Collateral Value Integrity
Permissionless Ledger Integrity

Options Settlement Integrity