
Essence
Cryptographic verification serves as the foundational trust primitive for decentralized financial systems, replacing reliance on centralized intermediaries with mathematical proof. In the context of derivatives, this mechanism ensures the integrity of a contract’s state transitions, collateral requirements, and settlement logic without requiring a trusted third party to audit or enforce. The core challenge in traditional finance involves counterparty risk and information asymmetry; verification in a decentralized environment addresses this by making all relevant computations publicly verifiable.
A system where every state change must be cryptographically proven shifts the risk from counterparty failure to code execution failure, creating a new set of architectural trade-offs.
Cryptographic verification replaces traditional counterparty trust with verifiable mathematical proof, ensuring the integrity of derivative contracts in decentralized systems.
The goal is to move beyond simple digital signatures to complex, verifiable computation. This allows for the execution of sophisticated financial logic ⎊ such as calculating margin requirements or determining option pricing ⎊ in a permissionless environment. The system’s robustness depends entirely on the strength of the underlying cryptographic proofs and the integrity of the data inputs.
When applied to options, verification guarantees that the conditions for exercise and settlement are met exactly as specified in the smart contract, eliminating disputes over pricing or collateral availability at expiration.

Origin
The concept of cryptographic verification originates from early computer science research in secure computation and verifiable systems, long before the advent of blockchain technology. The foundational elements, such as digital signatures and hash functions, were developed to ensure data integrity and authenticity in digital communications.
Bitcoin first applied these primitives to financial transactions, creating a verifiable ledger of value transfer where every transaction is validated by network participants. The evolution into decentralized derivatives required extending this verification beyond simple value transfer to complex financial instruments. Early decentralized finance protocols initially relied on straightforward on-chain calculations, where all logic was executed directly on the blockchain.
However, this approach proved computationally expensive and limited the complexity of financial products that could be offered. The next phase involved the introduction of off-chain computation with on-chain verification, enabling protocols to scale by proving the integrity of calculations without executing every step on the main chain. This shift allowed for the creation of more complex options products, as the computational cost of pricing models and margin calculations could be optimized.

Theory
The theoretical framework for cryptographic verification in derivatives rests on two core pillars: proof systems and oracle integrity. Proof systems, specifically zero-knowledge proofs (ZKPs), allow a protocol to prove a statement about its state without revealing the state itself. This is particularly relevant for derivatives, where a market maker or collateral provider may want to prove solvency without exposing their full portfolio or proprietary trading strategies.
The theoretical underpinnings allow for a system where counterparty risk is managed through verifiable solvency proofs rather than reliance on a central clearing house. The second pillar involves the verification of external data, known as the oracle problem. Options contracts require accurate pricing data at expiration to determine settlement value.
A verifiable oracle system ensures that the price feed used by the contract is reliable and tamper-proof. This involves cryptographic signatures from multiple data providers and aggregation methods that prevent manipulation.

Proof System Mechanisms
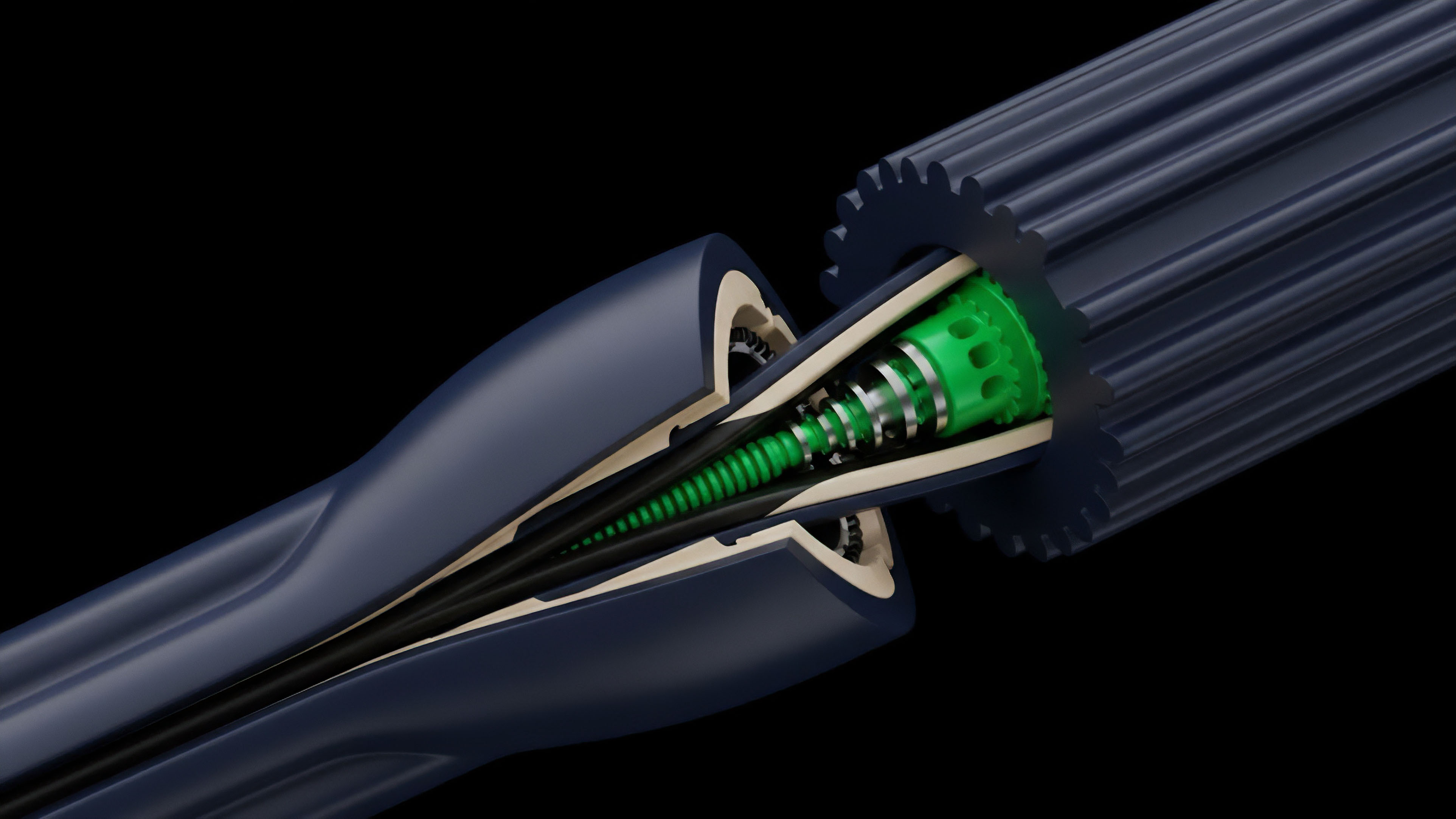
The implementation of verification relies on specific cryptographic techniques.
- Zero-Knowledge Proofs (ZKPs): These allow a party to prove knowledge of a secret (like having sufficient collateral) without revealing the secret itself. In derivatives, ZKPs enable privacy-preserving solvency proofs, where a clearing house or market maker can demonstrate financial health to the network without disclosing their full balance sheet.
- Verifiable Computation (VC): This mechanism ensures that a complex off-chain calculation, such as the Black-Scholes-Merton option pricing model, was performed correctly. The off-chain computation generates a proof that is then verified on-chain, reducing gas costs significantly.
- Digital Signatures (ECDSA): Used to verify the authenticity of transactions and data inputs. Every state change in a smart contract, from collateral deposits to option exercises, requires a valid signature from the initiating party.

Verification Vs Traditional Auditing
A comparison between traditional financial auditing and cryptographic verification highlights the fundamental shift in trust models.
| Feature | Traditional Financial Auditing | Cryptographic Verification |
|---|---|---|
| Trust Model | Reliance on trusted third-party auditors and legal frameworks. | Reliance on mathematical proofs and code execution. |
| Transparency | Limited; requires manual review of private records and data. | Full verifiability of all relevant data and computations. |
| Counterparty Risk | Managed by clearing houses and regulatory oversight. | Managed by verifiable collateral and solvency proofs. |
| Cost Structure | High operational overhead for auditing firms and legal fees. | High computational cost for proof generation; low verification cost. |

Approach
The practical application of cryptographic verification in decentralized options protocols follows a structured approach that prioritizes security and capital efficiency. The process typically begins with the verification of collateral, where a user’s assets are locked into a smart contract. The verification mechanism ensures that the collateral meets the minimum requirements based on the risk parameters of the option being written.

Collateral and Margin Verification
When a user writes an option, the protocol calculates the required margin using a risk engine. This calculation is verified against the user’s available collateral. In many advanced protocols, this verification is performed using off-chain computation to reduce gas costs.
The off-chain computation generates a proof of margin sufficiency, which is then verified on-chain. This allows protocols to offer more capital-efficient margin models without compromising security.

Oracle Verification and Settlement
The settlement process for options relies heavily on external data verification. The smart contract must verify the price of the underlying asset at expiration to determine if the option is in-the-money. This verification relies on a decentralized oracle network.
- Data Source Aggregation: Oracles aggregate data from multiple independent sources to prevent single points of failure. The protocol verifies the signatures of these data providers to ensure data integrity.
- Price Verification Logic: The smart contract’s verification logic checks if the aggregated price falls within an acceptable range. If a discrepancy occurs, the contract may halt settlement or trigger a dispute resolution mechanism.
- Exercise Verification: When a user exercises an option, the protocol verifies that the exercise conditions (e.g. expiration date, strike price) are met. This verification process ensures that the settlement calculation is accurate based on the verifiable on-chain data.
A robust options protocol architecture requires verification at every stage, from initial collateral posting to final settlement, ensuring the integrity of both on-chain and off-chain computations.

Evolution
The evolution of cryptographic verification in options markets has progressed from simple on-chain logic to sophisticated off-chain proving systems. Early protocols, such as those built on Ethereum’s mainnet, struggled with high gas costs associated with complex calculations. The high cost of on-chain verification limited the types of options offered, favoring European options with simple settlement logic.
The next significant development was the adoption of layer 2 solutions and rollups. ZK-rollups, specifically, provide a pathway for verifiable computation at scale. By moving complex option pricing and margin calculations off-chain, protocols can significantly increase throughput and reduce transaction costs.
The key innovation here is that a single proof can verify thousands of off-chain transactions, allowing for more capital-efficient and liquid markets. This evolution is leading to the emergence of verifiable delay functions (VDFs) for specific derivative designs. VDFs introduce a time-lock mechanism, where a computation takes a certain amount of time to complete, regardless of the computing power applied.
This can be used to prevent front-running in option settlement or to create new types of time-locked financial products where the verification itself is time-dependent.
Horizon
Looking ahead, cryptographic verification is poised to redefine the architecture of global finance. The integration of advanced ZK-proofs into derivative systems suggests a future where entire financial institutions can prove their solvency and risk exposure without revealing proprietary information.
This verifiable solvency model could replace current regulatory requirements for periodic audits, offering real-time, transparent oversight while preserving privacy. The future of verification also extends beyond the contract itself to the underlying data feeds. The next generation of oracle networks will likely move toward verifiable computation of market data.
Instead of simply aggregating price feeds, these systems will generate proofs that verify the source data’s integrity and the calculation of metrics like implied volatility. This verifiable data layer creates the potential for truly trustless derivative markets where every input and output is mathematically guaranteed.

Verifiable Systemic Risk Management
The ultimate goal of cryptographic verification is to create a fully verifiable global financial ledger. This system would allow regulators and participants to analyze systemic risk in real-time by verifying the total leverage and interconnectedness of protocols without needing access to private user data. This shifts the focus from managing individual counterparty risk to managing systemic protocol risk.
New Derivative Instruments
The advancement of verification techniques enables the creation of novel derivative instruments previously deemed too complex or computationally expensive for decentralized systems.
- Exotic Options with Verifiable Paths: Options whose payoff depends on the price path of the underlying asset can be verified off-chain, allowing for more complex strategies than standard European or American options.
- Synthetic Asset Creation: Verifiable computation allows for the creation of synthetic assets that precisely mirror traditional financial instruments, backed by verifiable collateral and pricing models.
- Verifiable Prediction Markets: Verification of outcomes and payouts in prediction markets for real-world events.
The integration of advanced cryptographic proofs in derivatives will lead to a verifiable global financial ledger where systemic risk can be assessed in real-time without compromising individual privacy.

Glossary

Cryptographic Security in Financial Systems

Cryptographic Warrants
Cryptographic Proof Systems For

Cryptographic Mechanism

Inter-Chain State Verification

Smart Contract

Data Verification Services

Data Feed Verification

Cryptographic Solvency Check






