Essence
Deterministic execution environments replace the opacity of legacy clearinghouses. Within the architecture of decentralized finance, Cryptographic Systems function as the primary enforcement mechanism for derivative contracts, ensuring that settlement occurs according to mathematical proofs rather than institutional discretion. These structures provide the requisite certainty for high-stakes options trading by anchoring every state transition to a verifiable chain of computation.
The nature of these systems resides in their ability to maintain digital scarcity and transactional integrity in an adversarial environment. By utilizing asymmetric encryption and hash-based commitment schemes, the protocol ensures that collateral remains locked and accessible only through the fulfillment of predefined conditions. This shift from trust-based to verification-based finance removes the need for centralized intermediaries, thereby reducing systemic counterparty risk.
Deterministic execution environments eliminate the discretionary risks associated with legacy financial clearinghouses.
Financial autonomy in this context is a product of cryptographic primitives that secure the order flow and the margin engine. The systemic implication is a transition toward a global, 24/7 market where the rules of engagement are written in code and enforced by consensus. This architectural shift allows for the creation of complex financial instruments that are transparent, composable, and resistant to censorship.

Origin
The lineage of Cryptographic Systems within digital assets began with the quest for electronic cash that did not rely on a central authority.
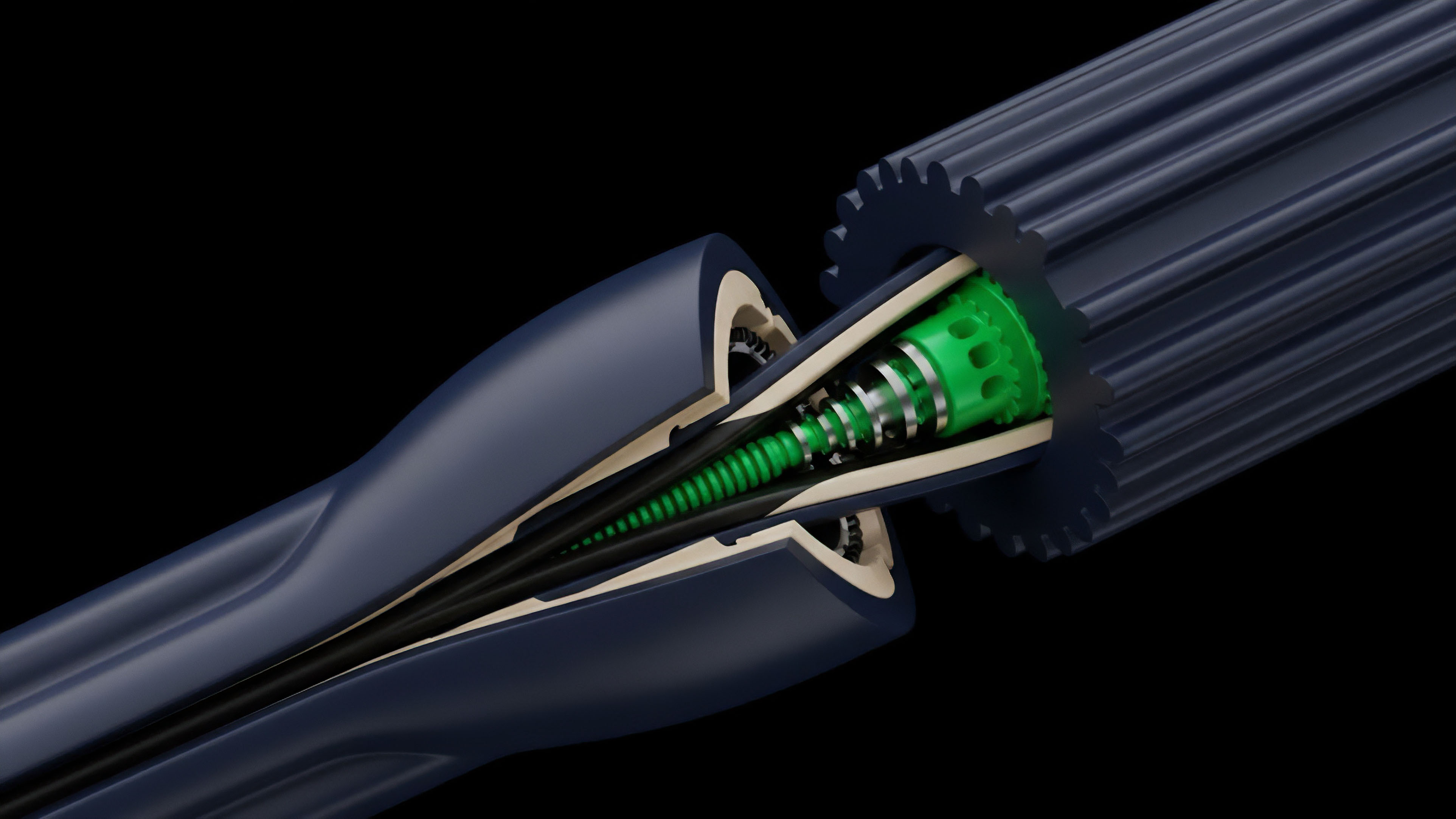
Early explorations into blind signatures and proof-of-work provided the conceptual basis for what would eventually become the blockchain. These initial efforts sought to solve the double-spending problem while preserving the privacy and sovereignty of the participants. As the technology matured, the focus shifted from simple value transfer to the execution of programmable logic.
The introduction of Turing-complete state machines allowed for the development of smart contracts, which are the building blocks of decentralized options. This transition enabled the encoding of complex financial payoffs directly into the ledger, creating a self-executing derivative market.
The shift from centralized trust to verifiable computation reduces systemic contagion risks associated with opaque counterparty exposures.
The evolution of these systems has been driven by the persistent need for scalability and privacy. From the early days of basic multisig escrows to the current state of advanced scaling solutions, the trajectory has always been toward increasing the efficiency and security of the underlying cryptographic rails. This historical progression reflects a broader move toward a more resilient and transparent financial operating system.

Theory
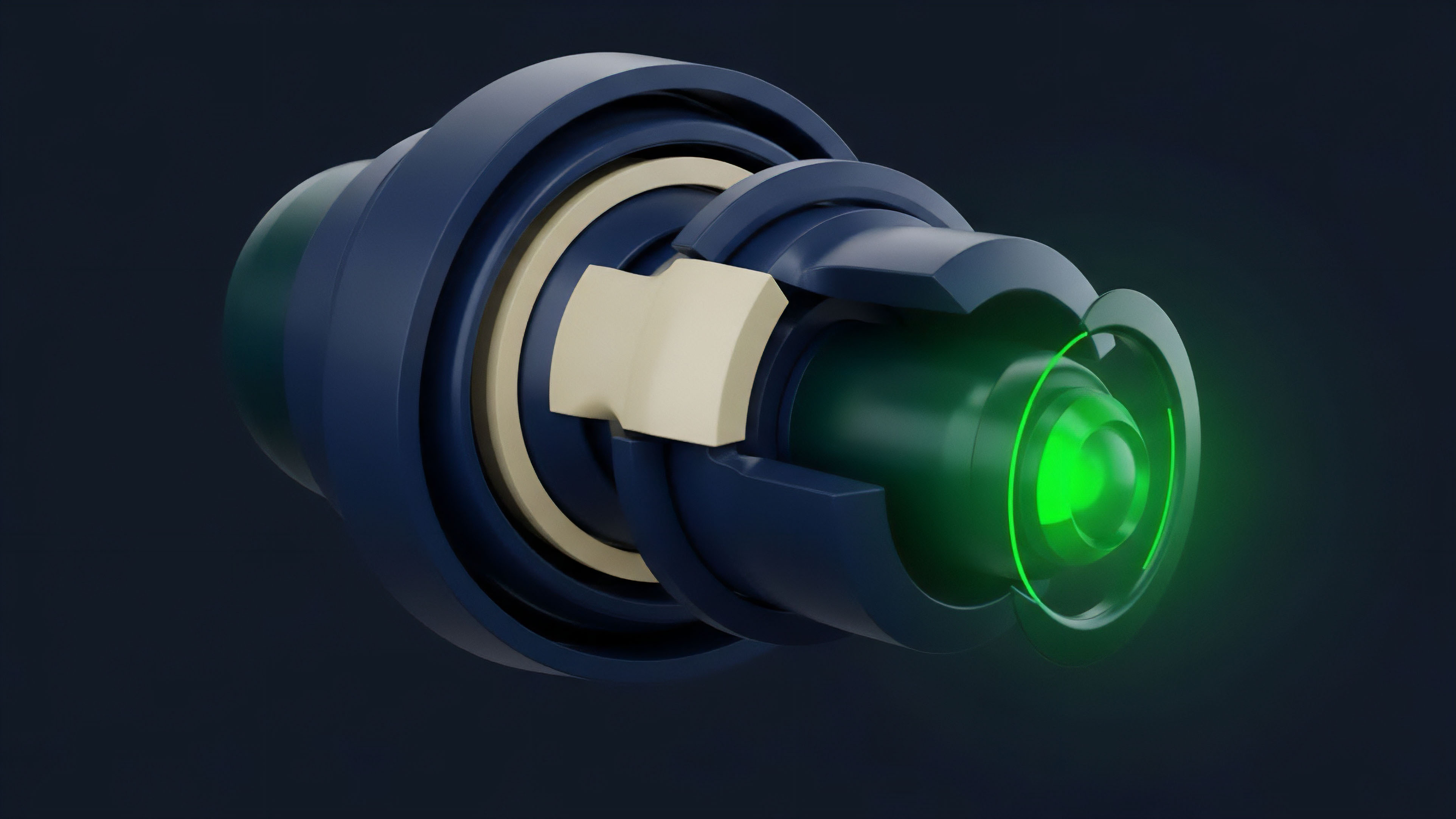
The mathematical integrity of Cryptographic Systems rests on one-way functions and the computational difficulty of certain mathematical problems.
Elliptic Curve Cryptography (ECC) provides the security for transaction authorization, allowing users to prove ownership of assets without revealing their private keys. This is the structural basis for secure collateral management in option protocols.

Primitive Functions
| Primitive | Financial Utility | Mathematical Basis |
|---|---|---|
| Hash Functions | Data Integrity and Linking | SHA-256 / Keccak-256 |
| Asymmetric Encryption | Ownership and Authorization | ECDSA / EdDSA |
| Zero-Knowledge Proofs | Privacy and Scalability | zk-SNARKs / zk-STARKs |
The application of Zero-Knowledge Proofs (ZKP) represents a significant advancement in the theoretical framework of decentralized derivatives. ZKPs allow a prover to convince a verifier that a statement is true without revealing any information beyond the validity of the statement itself. In the context of options, this enables private margin calculations and anonymous trading, which are vital for institutional participation.

System Architectures
| Architecture | Latency | Capital Efficiency |
|---|---|---|
| On-chain AMM | High | Moderate |
| Off-chain CLOB | Low | High |
| ZK-Rollup | Ultra-Low | Maximum |
The interaction between consensus mechanisms and financial settlement creates a unique set of trade-offs. While proof-of-stake provides a secure foundation for the ledger, the latency of block times can introduce challenges for high-frequency delta hedging. This necessitates the use of Layer 2 solutions that can process transactions off-chain while maintaining the security guarantees of the main net.

Approach
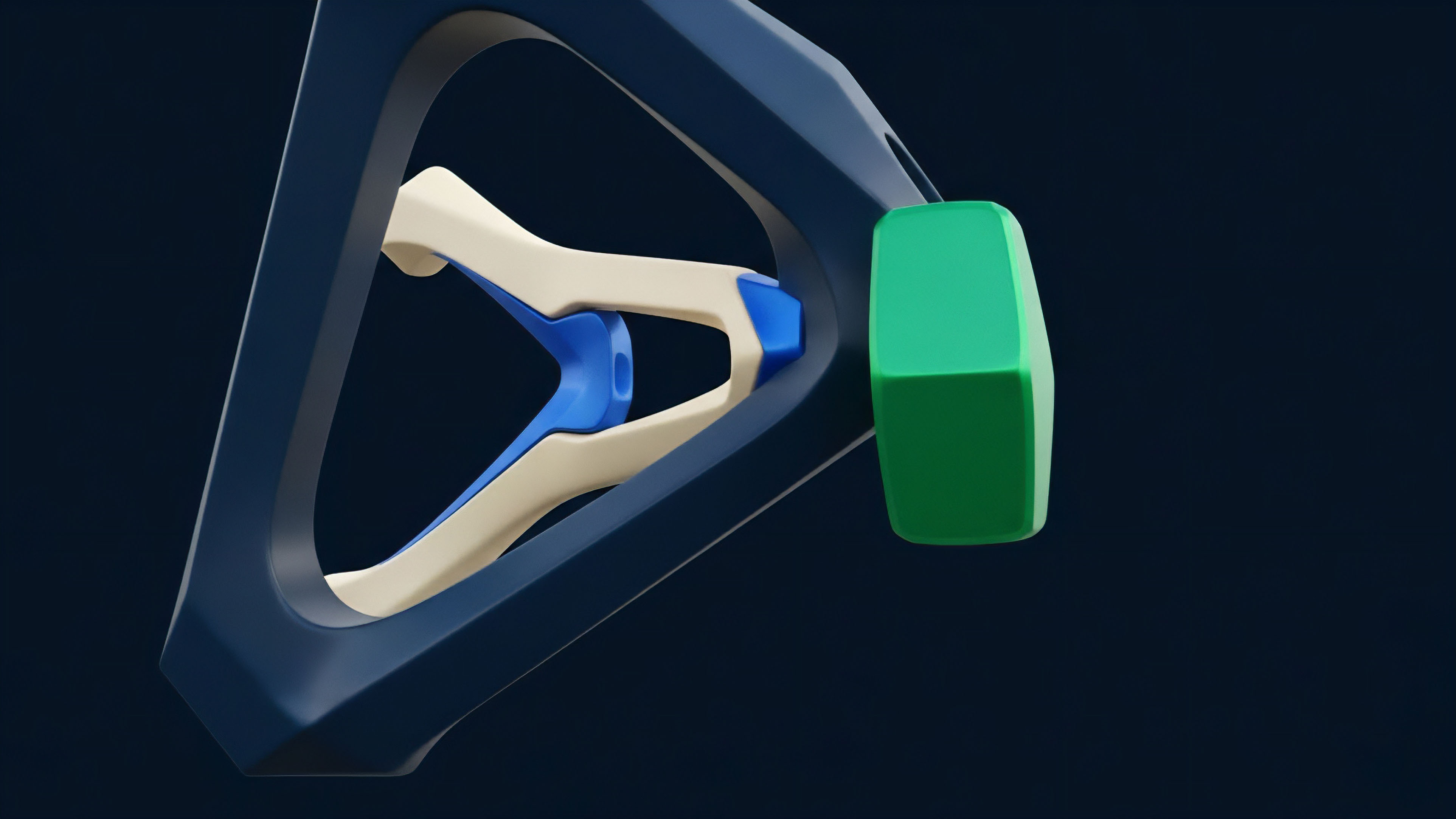
Current methodologies for implementing Cryptographic Systems in option markets focus on non-custodial vaults and automated clearing.
Market participants interact with smart contracts that act as the escrow agent, ensuring that the option seller has sufficient collateral to cover the potential payoff. This process is entirely transparent and can be audited in real-time by any participant.
- Collateralization: Assets are locked in a smart contract at the inception of the trade to ensure settlement.
- Oracle Integration: External price feeds are used to determine the value of the underlying asset at expiry.
- Automated Liquidation: Margin engines monitor positions and trigger liquidations if the collateral value falls below a certain threshold.
- Settlement Logic: The payoff is calculated and distributed automatically based on the final price of the asset.
Mathematical proofs serve as the ultimate arbiter of value transfer in decentralized option markets.
The use of Automated Market Makers (AMMs) has democratized access to option liquidity, allowing anyone to become a liquidity provider. These protocols use mathematical formulas to price options and manage risk, providing a continuous source of liquidity even in volatile markets. Conversely, Central Limit Order Books (CLOBs) are being deployed on high-performance scaling layers to cater to professional traders who require more granular control over their execution.

Evolution
The transition from simple multisig wallets to complex decentralized autonomous organizations (DAOs) has transformed the governance and development of cryptographic protocols.
Early systems were rigid and difficult to upgrade, but modern architectures are designed to be modular and extensible. This allows for the rapid deployment of new financial products and the continuous improvement of the underlying security. The emergence of AppChains and Rollups has addressed the limitations of early blockchain networks.
These specialized environments are optimized for financial transactions, offering higher throughput and lower fees. This has enabled the development of more sophisticated option strategies, such as multi-leg spreads and exotic payoffs, which were previously impractical due to high gas costs.
Capital efficiency in decentralized options depends on the ability to cryptographically verify margin requirements without exposing private user data.
In contrast to the early focus on pure decentralization, the current trend is toward a hybrid model that combines the speed of centralized systems with the security of decentralized settlement. This approach allows for a better user experience while still providing the transparency and auditability that are the hallmarks of Cryptographic Systems. The systemic implication is a more robust and scalable infrastructure for the future of finance.

Horizon
The future state of Cryptographic Systems involves the widespread adoption of Fully Homomorphic Encryption (FHE) and Multi-Party Computation (MPC).
These technologies will allow for the execution of trades and risk management on encrypted data, providing a level of privacy that is currently unavailable in public ledgers. This will be a major driver for the entry of large-scale institutional capital into the decentralized option space.
- Cross-Chain Atomic Swaps: Enabling the seamless exchange of assets across different blockchain networks without intermediaries.
- Privacy-Preserving Compliance: Using ZKPs to prove compliance with regulatory requirements without revealing sensitive user data.
- AI-Driven Risk Management: Integrating machine learning models directly into the cryptographic layer to optimize margin and liquidity.
- Quantum-Resistant Algorithms: Developing new cryptographic primitives that are secure against the threat of quantum computing.
The integration of decentralized identity will also play a significant role in the evolution of these systems. By linking cryptographic addresses to verifiable identities, protocols can offer more personalized financial services and better manage risk. This will lead to a more inclusive and efficient global market where access to sophisticated financial instruments is no longer restricted by geography or status. The path forward is one of increasing complexity and sophistication. As Cryptographic Systems become more integrated into the global financial fabric, the distinction between traditional and decentralized finance will continue to blur. The ultimate goal is a unified, transparent, and resilient financial system that is powered by mathematics and accessible to all.

Glossary
Non-Custodial Vaults

Technical Exploits

Cross-Chain Atomic Swaps

Financial Sovereignty
Counterparty Risk

Adversarial Environments

Zero Knowledge Proofs

Order Flow

Central Limit Order Books