Essence
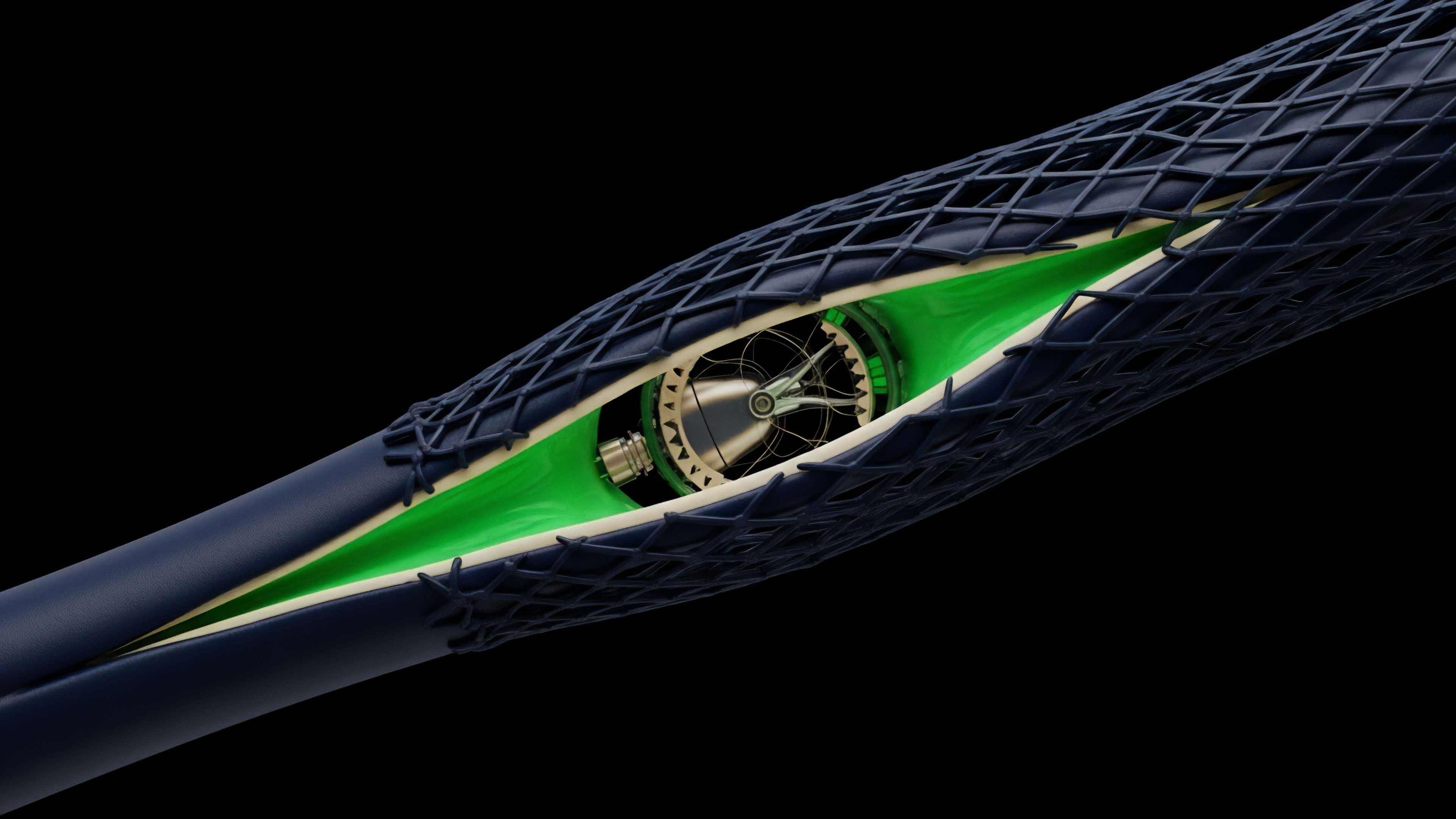
Trustless financial settlement requires verification mechanisms that scale faster than the transactions themselves. High-density options trading on-chain remains a theoretical exercise without the ability to compress vast state changes into a single, verifiable hash. This compression, achieved through Recursive Proof Composition, allows a single proof to verify the validity of multiple prior proofs.
The result is a logarithmic reduction in the computational burden placed on the settlement layer.
Recursive proof composition enables the verification of an entire chain of transactions by checking only the final proof in the sequence.
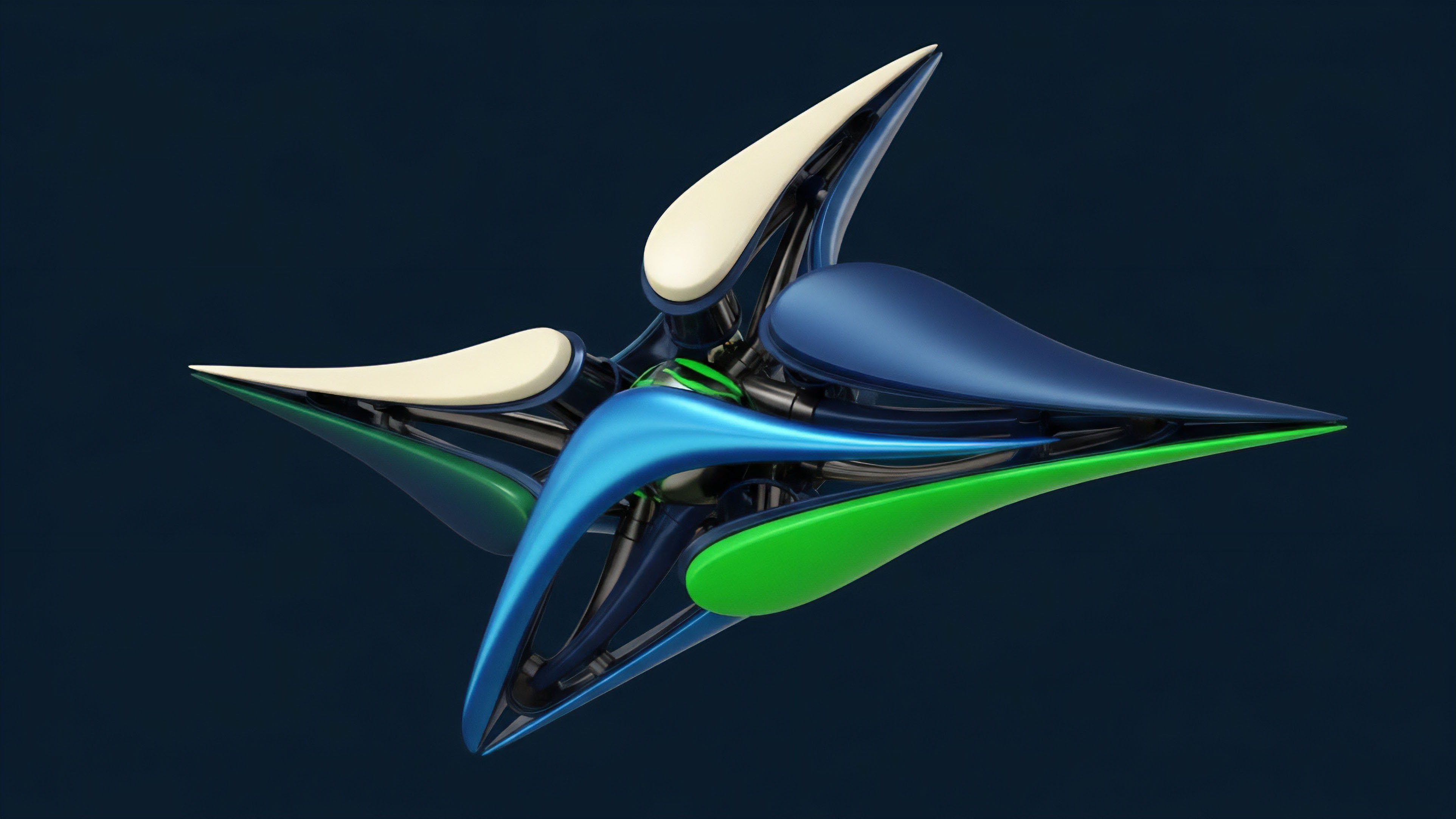
The architectural shift toward Succinctness ensures that even the most complex volatility strategies ⎊ involving multi-leg Greeks and dynamic hedging ⎊ can be settled with minimal on-chain footprints. By offloading the proving work to specialized hardware and only submitting the proof to the mainnet, protocols achieve a level of capital efficiency previously reserved for centralized matching engines. This is the transition from optimistic assumptions to cryptographic certainty.
The inability to respect the verification bottleneck is the failure point of early decentralized finance. Systems that rely on re-executing every trade on every node are doomed to high latency and prohibitive costs. Proof Aggregation solves this by batching thousands of derivative settlements into a single proof, ensuring that the cost per transaction approaches zero as volume increases.
This is the mathematical prerequisite for a truly global, permissionless options market.

Origin
The early days of zero-knowledge proofs were defined by massive proof sizes and high verification costs. Early protocols like Groth16 required a trusted setup for every single circuit, a process that introduced systemic risk and limited flexibility for complex derivative instruments. The shift toward Universal Structured Reference Strings and eventually Transparent Setup protocols removed the need for these fragile ceremonies.
Transparent setup protocols eliminate the systemic risk associated with the destruction of initial cryptographic secrets.
As the demand for privacy-preserving finance grew, the limitations of first-generation proofs became apparent. The birth of STARKs (Scalable Transparent Arguments of Knowledge) introduced a path to scalability that did not rely on elliptic curve pairings, instead using hash-based cryptography. This provided post-quantum security and significantly faster proving times for large-scale computations.
The transition from monolithic proving to Modular Proving Systems allowed developers to swap out different components of the proof stack. This flexibility led to the creation of Halo and Plonky2, which utilized recursion without a trusted setup. These advancements were driven by the need for light-client verification, where a mobile device could verify the entire state of an options exchange without downloading the full blockchain.
Theory
Mathematical efficiency in proof systems relies on the arithmetization of logic.
By converting financial operations into polynomial constraints, we can verify the correctness of a margin call or an option exercise without re-executing the trade. Polynomial Commitment Schemes (PCS) provide the mechanism for this verification. The efficiency of these schemes determines the proof size and the time required for the verifier to reach a conclusion.
Polynomial commitments allow a prover to convince a verifier of a mathematical statement without revealing the underlying data.
The choice of proof system involves a trade-off between prover time, verifier time, and proof size. For high-frequency options, verifier time is the most vital metric, as it directly impacts the gas cost on the settlement layer. Look-up Tables have emerged as a vital tool for optimizing these circuits, allowing the prover to pre-calculate repetitive operations like range checks or hash functions.
| System Type | Proof Size | Verification Time | Setup Type |
|---|---|---|---|
| Groth16 | Constant | Very Fast | Per-Circuit Trusted |
| PLONK | Constant | Fast | Universal Trusted |
| STARK | Polylogarithmic | Moderate | Transparent |
| Halo2 | Logarithmic | Fast | Transparent |
This is where the pricing model becomes truly elegant ⎊ and dangerous if ignored. If the proof system cannot keep up with the rate of market state changes, the system enters a state of Information Asymmetry. Traders with faster access to the proving hardware can front-run the settlement of others, creating a new form of MEV that exists at the cryptographic layer.
Approach
Modern derivative architectures utilize Custom Gates and Look-up Tables to optimize the proving process.
These tools allow the circuit to handle repetitive operations ⎊ such as Keccak hashing or ECDSA signature verification ⎊ with significantly fewer constraints. This specialization is what allows a decentralized exchange to process thousands of orders per second.
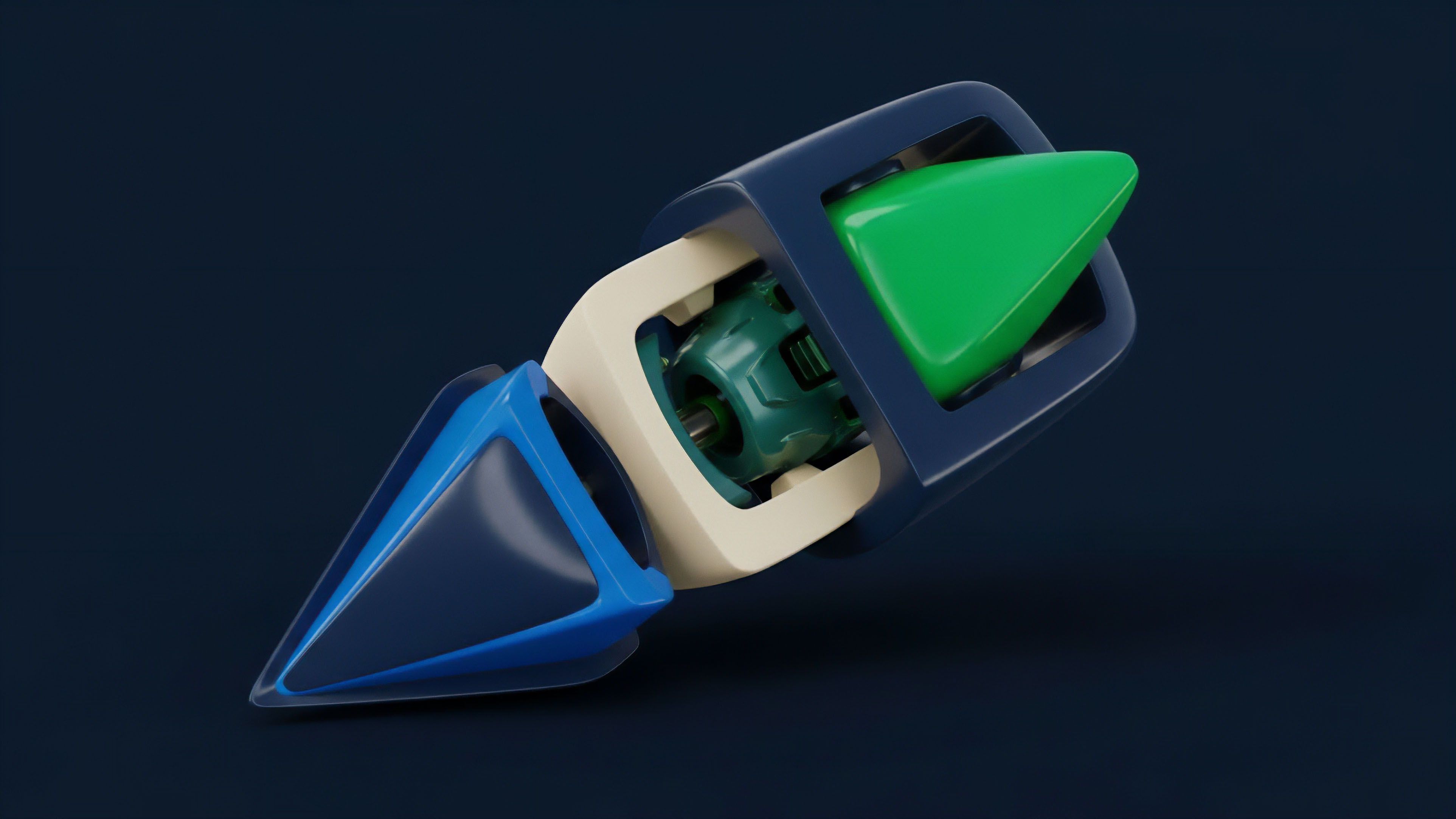
- Arithmetization converts the derivative logic into a system of equations over a finite field.
- Commitment generates a succinct representation of the trace of execution.
- Recursion enables the proofer to wrap multiple transaction proofs into a single meta-proof.
- Aggregation combines proofs from different users into a single submission to the blockchain.
The use of ZK-VMs (Zero-Knowledge Virtual Machines) has simplified the development of complex options logic. Instead of writing custom circuits for every new instrument, developers can write in high-level languages like Rust or C++, which are then compiled into a provable format. While this adds some overhead, the efficiency gains from Recursive SNARKs often offset the cost, making the development cycle much faster.
Evolution
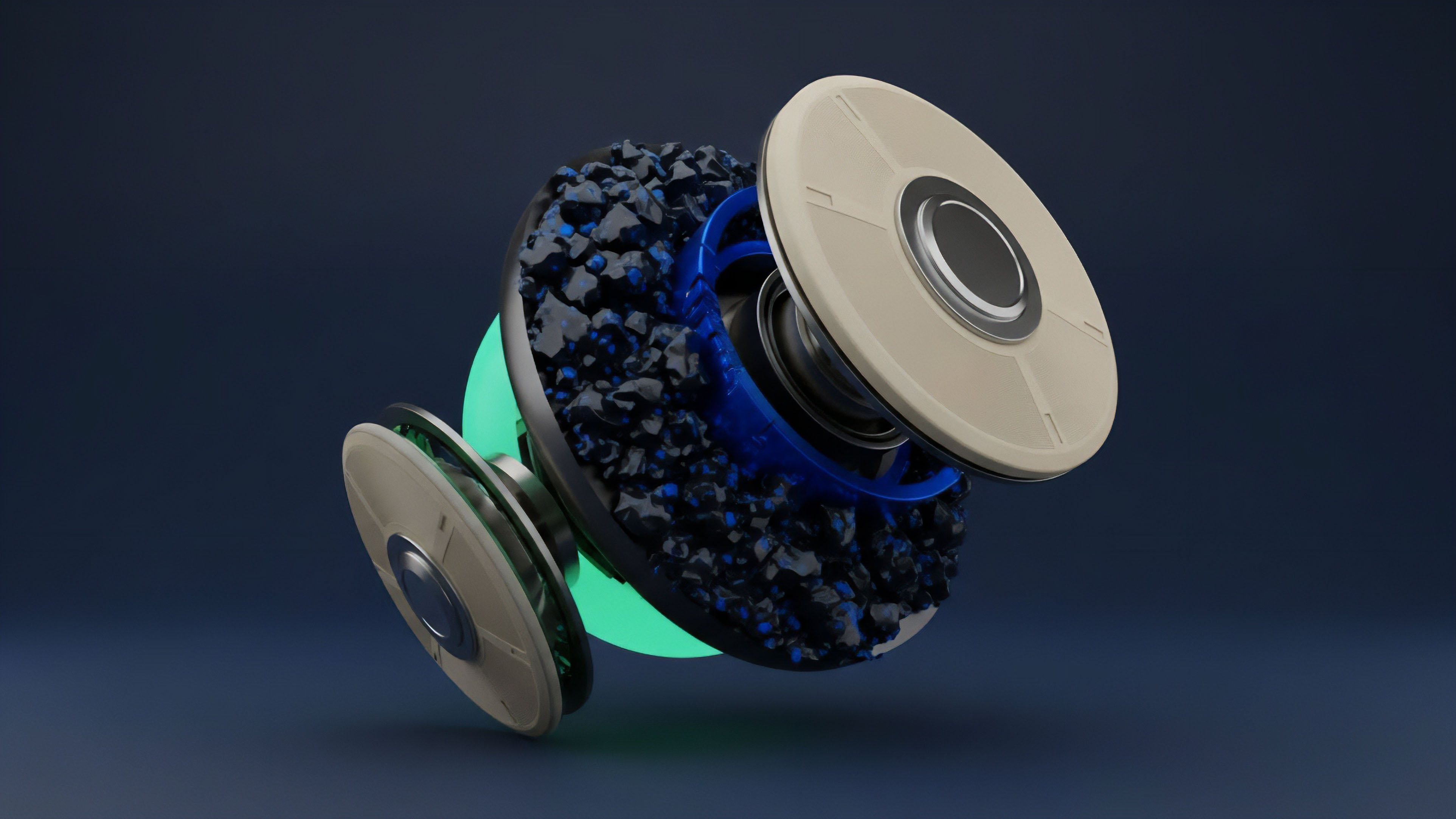
The transition from monolithic proving to Distributed Proving Markets represents a shift in how we view computational security.
Prover networks now compete to generate proofs for decentralized option vaults, driving down latency. This competition ensures that the time-to-finality for a complex volatility strategy matches the speed of centralized exchanges.
| Era | Primary Bottleneck | Efficiency Solution |
|---|---|---|
| Static Circuits | Circuit Flexibility | Universal Setups (PLONK) |
| High Gas Costs | On-chain Footprint | Recursive Aggregation |
| Latency Wars | Prover Speed | Hardware Acceleration (ASICs) |
The adversarial reality of crypto finance means that any efficiency gain is immediately used to increase leverage. As proving becomes cheaper, the frequency of margin rebalancing increases, which in turn requires even more efficient proofs. This feedback loop drives the constant search for Field-Agnostic Proving and faster Fast Fourier Transforms (FFTs).

Horizon
We are moving toward a world where Hardware-Accelerated Proving becomes the standard for derivative settlement.
The risk of a Proof Gap ⎊ where the time to generate a proof exceeds the market’s volatility window ⎊ is the new frontier of systemic failure. If a prover cannot generate a proof of solvency during a market crash, the entire margin engine stalls, leading to potential contagion across the network.
The Proof Gap represents the temporal risk between a market event and its cryptographic verification on the settlement layer.
The next phase involves Fully Private Liquidity Pools where the entire order book is hidden behind a zero-knowledge shield. Only the proof of execution is public, ensuring that market makers can provide liquidity without being picked off by toxic flow. This requires a level of efficiency that can only be achieved through Folding Schemes like Nova or Sangria, which bypass the need for expensive FFTs entirely. Ultimately, the goal is Instant Finality. When the cost and time of proving become negligible, the distinction between on-chain and off-chain disappears. We will see the emergence of Self-Proving Assets, where the instrument itself carries the proof of its own value and risk parameters, updated in real-time as the market moves. This is the endgame for decentralized derivatives.
Glossary
Margin Solvency Proofs

Fpga Proving

Confidential Options Trading

Fri Protocol

Zk-Rollups

Plonky2

Zero Knowledge Proofs

Gkr Protocol

Number Theoretic Transform