Essence
Bridge Integrity Testing constitutes the systematic verification of the cryptographic and economic links connecting disparate blockchain environments. This process confirms that the value locked on a source ledger remains equivalent to the synthetic assets minted on a destination ledger. In a financial system characterized by fragmented liquidity, this testing serves as the primary defense against the creation of unbacked debt.
It ensures that the underlyings for options and other complex instruments maintain their intended value through rigorous, continuous attestation of vault solvency.
Bridge Integrity Testing functions as the definitive validation of cross-chain collateralization to prevent the propagation of unbacked synthetic assets.
The nature of this verification extends to the validation of state transitions and the security of the messaging layer. When a protocol facilitates the movement of assets across chains, it introduces a unique vector of systemic hazard. Bridge Integrity Testing addresses this by examining the mathematical proofs that govern asset locking and unlocking.
By establishing a high-fidelity audit trail, it allows market participants to trade with the certainty that the underlying collateral is both present and accessible. This verification is the prerequisite for the expansion of decentralized finance into a multi-chain reality where trust is replaced by verifiable code.

Origin
The necessity for Bridge Integrity Testing arose from a series of catastrophic failures within early cross-chain architectures. Initial attempts at asset bridging relied on centralized custodians or small sets of trusted validators, creating massive honey pots for adversarial actors.
The exploitation of these vulnerabilities resulted in billions of dollars in lost capital, revealing the fragility of trust-based models in a permissionless environment. These events forced a shift toward cryptographic verification and decentralized surveillance as the only viable methods for securing inter-chain value transfer. As the sophistication of the digital asset market grew, the demand for more robust verification techniques became apparent.
Early adopters realized that a derivative contract is only as secure as the bridge supporting its underlying asset. This realization led to the development of Bridge Integrity Testing as a formal discipline. It moved the industry away from periodic, manual reviews toward a model of continuous, programmatic attestation.
This transition was driven by the need to mitigate the contagion hazards that occur when a bridge failure devalues the assets used as collateral in broader financial markets.

Theory
The logic of Bridge Integrity Testing is rooted in the synchronization of state roots across asynchronous networks. It utilizes Merkle proofs to verify that a specific transaction occurred on the source chain without requiring the destination chain to store the entire history of the source ledger. This mathematical abstraction allows for efficient verification while maintaining a high level of security.
The testing protocol focuses on the parity between the locked supply and the circulating supply of wrapped tokens, identifying any discrepancies that could signal a breach or a failure in the minting logic.
State Synchronization Logic
At the technical level, Bridge Integrity Testing examines the latency and accuracy of state relays. These relays are responsible for carrying the proof of a state change from one network to another. If the relay is compromised or delayed, the integrity of the bridge is at hazard.
The testing process involves simulating various failure modes, such as chain reorganizations or validator collusion, to determine the resilience of the bridge under stress. This quantitative analysis provides a measure of the “economic security” of the bridge, which is the cost required to successfully execute a fraudulent transaction.
The mathematical synchronization of state roots provides the foundation for trustless asset transfers across heterogeneous blockchain networks.

Contagion Risk Parameters
The systemic implications of bridge failure are analyzed through the lens of interconnectedness. When Bridge Integrity Testing identifies a weakness, it assesses how that weakness might propagate through the ecosystem. This involves mapping the dependencies of various protocols on the bridged assets.
If a major lending platform or an options exchange relies on a specific bridge, a failure in that bridge could trigger a cascade of liquidations. The testing seeks to quantify this hazard by measuring the concentration of bridged assets within the total value locked of the system.

Approach
Current execution of Bridge Integrity Testing involves a combination of real-time on-chain monitoring and periodic deep-dive audits of the smart contract logic. Automated systems track the balances of bridge vaults and compare them to the total supply of the corresponding synthetic assets.
Any deviation triggers an immediate alert or an automated circuit breaker to prevent further losses. This proactive stance is required to maintain market stability in an environment where exploits can occur in seconds.
| Verification Method | Mechanism | Primary Benefit |
|---|---|---|
| Proof of Reserve | On-chain balance attestation | Real-time solvency visibility |
| Zero Knowledge Proofs | Cryptographic state validation | Trustless verification without data exposure |
| Optimistic Verification | Fraud-proof window | Lower computational cost on-chain |
| Multi-Sig Surveillance | Distributed validator set | Redundancy in decision-making |

Operational Execution
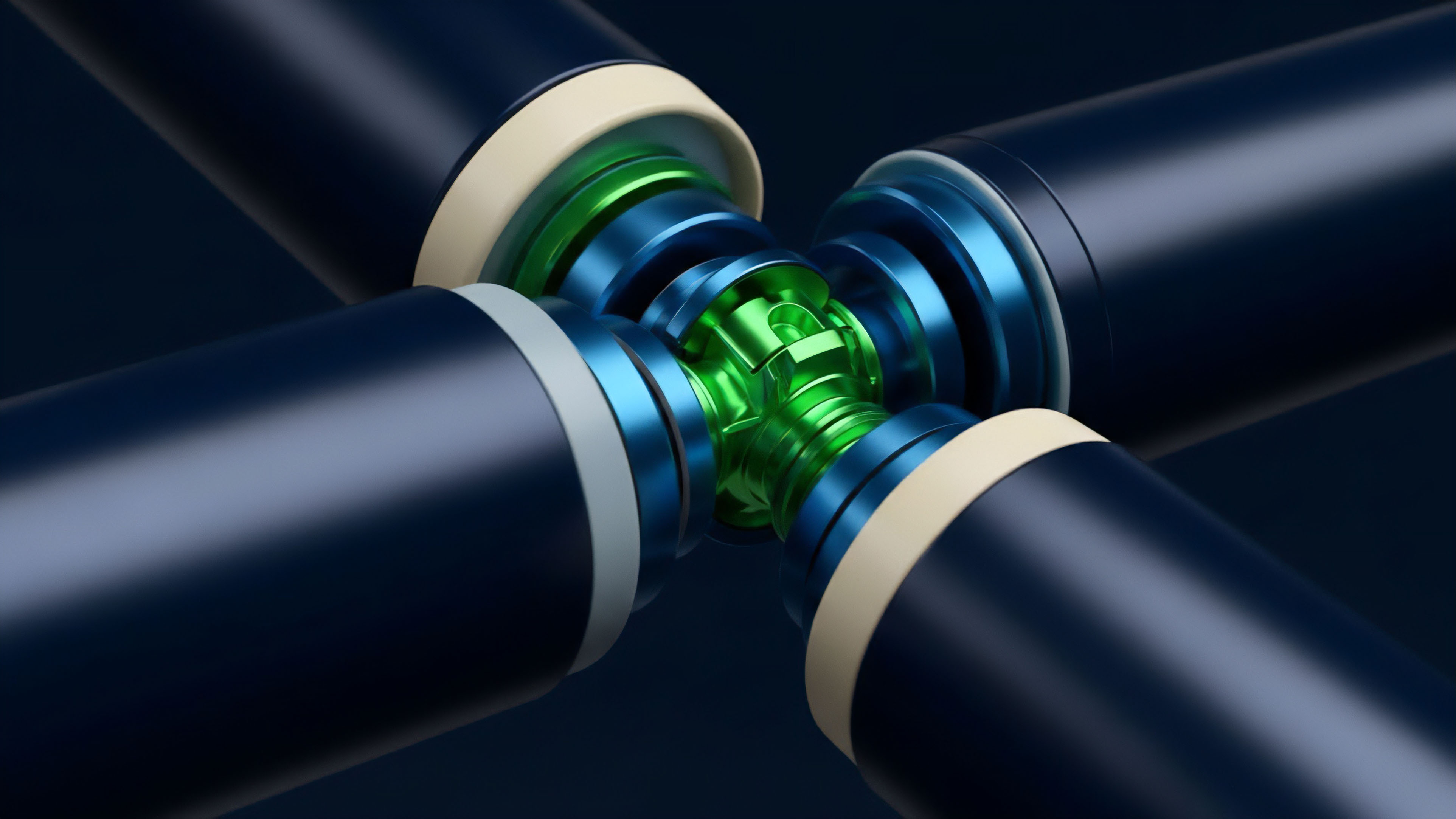
The procedure for Bridge Integrity Testing includes the use of decentralized oracle networks to provide independent data points regarding the state of different chains. These oracles act as a neutral third party, confirming that the assets on the source chain are indeed locked before the destination chain allows the minting of new tokens. This multi-layered defense ensures that even if one part of the system is compromised, the integrity of the overall bridge remains intact.
Furthermore, developers utilize formal verification to prove the correctness of the bridge’s smart contracts, eliminating entire classes of coding errors.
- Vault Balance Tracking: Continuous monitoring of the collateral held in escrow on the source chain.
- Supply Parity Verification: Matching the circulating supply of wrapped assets with the locked collateral.
- Messaging Layer Stress Testing: Simulating high-traffic and adversarial conditions to test the reliability of cross-chain communication.
- Circuit Breaker Activation: Implementing automated pauses in bridge activity when anomalies are detected.

Evolution
The progression of Bridge Integrity Testing has seen a shift from reactive measures to predictive modeling. In the early stages, testing was often an afterthought, conducted only after a major security incident. Today, it is an integral part of the development lifecycle for any cross-chain protocol.
This change reflects a maturing industry that recognizes the existential importance of security. The move toward “ZK-bridges” represents the latest stage in this progression, where zero-knowledge proofs are used to provide mathematical certainty of bridge integrity without relying on external validators.
The shift from manual audits to autonomous cryptographic verification marks the maturation of cross-chain security standards.

Architectural Shifts
The transition from optimistic models to validity-proof models has transformed the landscape of Bridge Integrity Testing. Optimistic bridges rely on the assumption that at least one honest actor will challenge a fraudulent transaction within a specific timeframe. Testing these systems requires analyzing the economic incentives for challengers and the liveness of the challenge network.
In contrast, validity-proof bridges use ZK-SNARKs or ZK-STARKs to prove the correctness of every state transition. Testing for these systems focuses on the soundness of the cryptographic circuits and the integrity of the prover software.
| Era | Dominant Model | Testing Focus |
|---|---|---|
| Foundational | Centralized Custody | Manual balance checks |
| Intermediate | Multi-Sig / Optimistic | Validator reputation and fraud proofs |
| Modern | Zero Knowledge Proofs | Circuit soundness and prover integrity |

Horizon
The trajectory of Bridge Integrity Testing points toward the total automation of solvency verification. We are moving toward a future where the risk of a bridge is priced directly into the premiums of cross-chain options. Market makers will utilize real-time integrity data to adjust their spreads, effectively creating a market for bridge security.
This will incentivize bridge operators to maintain the highest standards of integrity, as any perceived weakness will immediately result in higher costs for their users. The integration of Bridge Integrity Testing with decentralized insurance protocols will further stabilize the market. Insurance pools will use the data generated by these tests to set their underwriting fees.
This creates a feedback loop where the most secure bridges attract the most liquidity and the lowest insurance costs. Ultimately, the goal is to create a seamless, multi-chain financial system where the underlying infrastructure is so robust that the hazard of bridge failure becomes negligible. This will enable the creation of complex, cross-chain derivatives that are as secure as their single-chain counterparts.
- Real-Time Risk Pricing: Integrating bridge integrity metrics into the valuation of multi-chain derivatives.
- Autonomous Self-Healing: Protocols that can automatically re-collateralize or switch providers based on integrity data.
- Standardized Security Ratings: The emergence of independent agencies that provide standardized integrity scores for all major bridges.
- Cross-Chain Governance Integration: Using integrity data to inform the governance decisions of decentralized organizations.

Glossary

Bridge Security Monitoring
Trading Protocol Integrity

Protocol Architecture Integrity

Bridge Vulnerabilities

Protocol Operational Integrity

Cross Chain Messaging Security

Trustless Bridge

Bridge Tax
State Transitions