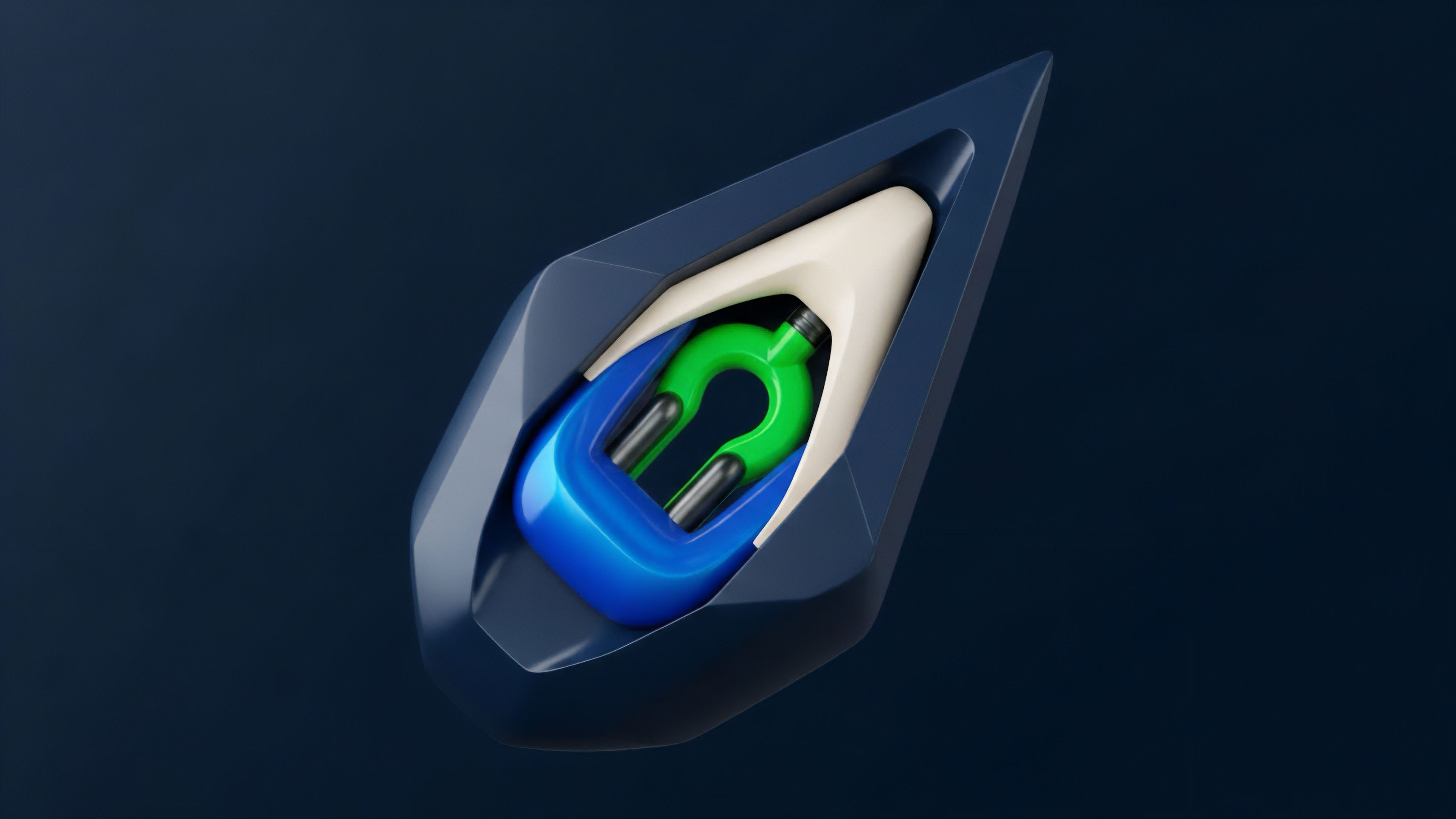
Essence
Economic Security, in the context of decentralized options protocols, refers to the systemic resilience of the protocol itself against financial and technical shocks. This concept extends beyond individual user risk management, focusing instead on the architectural integrity required to ensure the protocol remains solvent and operational under adversarial conditions. The primary challenge in a decentralized environment is that code executes without human intervention, meaning a flaw in the economic design ⎊ the incentive structure or risk parameters ⎊ can lead to catastrophic cascading failures.
A protocol’s economic security is therefore measured by its ability to maintain a positive net asset value across all outstanding positions, even during periods of extreme market volatility or oracle manipulation. This requires a robust design that aligns incentives for participants, ensures accurate pricing, and prevents the insolvency of the protocol’s insurance fund or backstop mechanisms. The core function of Economic Security is to prevent a systemic breakdown where the protocol’s liabilities exceed its assets.
In traditional finance, this role is filled by central clearinghouses, which guarantee trades and manage counterparty risk. In decentralized systems, this guarantee must be built into the code itself through a combination of margin requirements, liquidation logic, and collateralization mechanisms. The protocol must possess a high degree of confidence that it can fulfill all obligations to option holders at expiration, regardless of the underlying asset’s price movement.
Economic Security in crypto options protocols is the architectural design that ensures systemic solvency and prevents cascading failures by aligning incentives and managing risk algorithmically.
The challenge of Economic Security is compounded by the fact that crypto markets operate continuously, without circuit breakers, and often with significantly higher volatility than traditional assets. The protocol must be designed to withstand “black swan” events where prices move dramatically, potentially rendering large numbers of positions underwater simultaneously. This requires a deep understanding of market microstructure and the feedback loops that can amplify small liquidations into larger systemic risks.

Origin
The concept of Economic Security for derivatives protocols originates from the inherent limitations of traditional options pricing models when applied to the unique characteristics of digital assets. The Black-Scholes-Merton model, foundational to traditional options markets, relies on assumptions that do not hold true in crypto. These assumptions include continuous trading, constant volatility, and log-normal distribution of asset prices.
The high volatility, non-normal distributions, and tail risk observed in crypto markets ⎊ often characterized by sudden, sharp price movements ⎊ make traditional models unreliable for accurate risk management. Early decentralized protocols often adapted existing TradFi models without fully accounting for these differences. This led to a series of high-profile failures where protocols became insolvent when faced with extreme market movements.
The term “Economic Security” emerged as a specific design objective to address these failures. The focus shifted from simply pricing options to ensuring the protocol could survive a rapid, large-scale price change. The origin story of Economic Security is therefore a story of iteration and learning from systemic failures, where each failure revealed a new vector of risk that needed to be mitigated by the protocol’s design.
The core design principle that emerged from these early failures was the necessity of dynamic risk adjustment. Protocols realized they could not rely on static margin requirements or simple liquidation thresholds. Instead, they needed mechanisms that could adjust risk parameters in real-time based on current market volatility and open interest.
This led to the development of dynamic collateral requirements and risk-based liquidation systems.

Theory
The theoretical foundation of Economic Security in options protocols centers on a synthesis of quantitative finance, game theory, and smart contract design. The objective is to design a system where rational, self-interested participants are incentivized to act in ways that maintain protocol solvency.
This requires a robust understanding of how different risk parameters interact and how a protocol’s margin engine calculates risk exposure.

Quantitative Risk Parameters
The core challenge in options risk management is quantifying the “Greeks,” which measure the sensitivity of an option’s price to changes in underlying variables.
- Delta: The rate of change of the option price relative to the change in the underlying asset price. A protocol must ensure that its overall portfolio delta is balanced to prevent large losses from small price movements.
- Gamma: The rate of change of Delta. High Gamma exposure means the protocol’s delta changes rapidly as the underlying price moves, making risk management significantly more difficult during volatile periods.
- Vega: The rate of change of the option price relative to changes in implied volatility. Crypto options frequently exhibit high Vega risk, as implied volatility can change drastically in short timeframes, often in response to macro events or network updates.

Game Theory and Adversarial Environments
Economic Security is fundamentally a game theory problem. The protocol operates in an adversarial environment where participants are constantly seeking to maximize their profits, potentially at the expense of other users or the protocol itself. The protocol’s design must account for “griefing” attacks, where a malicious actor intentionally takes actions to exploit a vulnerability for personal gain, even if the direct profit is small.
A crucial element of this theory is the concept of a “liquidation cascade.” If a large number of positions become undercollateralized simultaneously, the resulting liquidations can flood the market, pushing the price of the underlying asset down further. This creates a feedback loop that liquidates even more positions, potentially leading to protocol insolvency. The design of liquidation engines must mitigate this by managing the size and timing of liquidations to prevent market destabilization.

Oracle Dependency and Data Integrity
The accuracy of options pricing and liquidation logic depends entirely on the integrity of the data feeds (oracles) providing the underlying asset’s price. A compromised oracle can lead to a total loss of Economic Security. The protocol must implement mechanisms to prevent oracle manipulation, often through decentralized oracle networks (DONs) that aggregate data from multiple sources.
A common vulnerability arises when a protocol uses a single, low-liquidity source for its oracle price. A large actor can manipulate this price on a decentralized exchange, triggering liquidations at an artificial price, and profiting from the resulting protocol losses. This risk is managed by protocols that use time-weighted average prices (TWAPs) from multiple high-liquidity sources to make manipulation prohibitively expensive.

Approach
The practical approach to implementing Economic Security involves several architectural components that work in concert to manage risk. The core of this approach is a sophisticated margin engine designed to handle the high volatility and non-normal distributions of crypto assets.
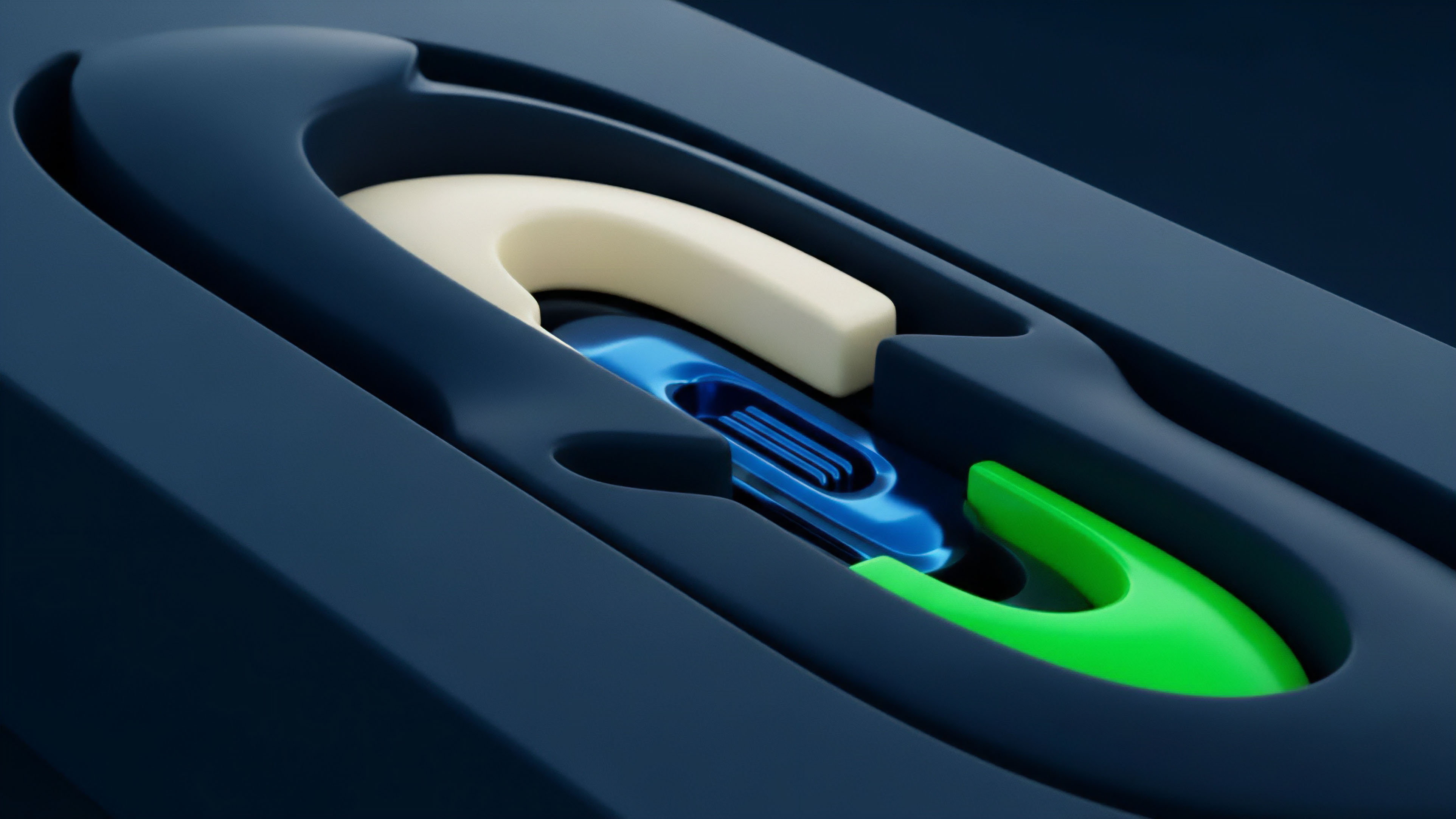
Margin and Collateralization Mechanisms
Options protocols utilize various methods to ensure sufficient collateral is held to cover potential losses. The choice of mechanism directly impacts capital efficiency and systemic risk.
- Isolated Margin: Each position has its own separate collateral pool. This approach limits losses to a single position but can be capital inefficient for users with multiple positions.
- Portfolio Margin: This approach calculates risk across a user’s entire portfolio of positions, allowing for offsets between long and short positions. It significantly increases capital efficiency but requires a more complex risk engine to calculate potential future losses accurately.
- Cross-Collateralization: Allows users to post collateral in assets other than the underlying asset. This introduces additional risk from collateral volatility, requiring the protocol to manage the risk of multiple assets simultaneously.

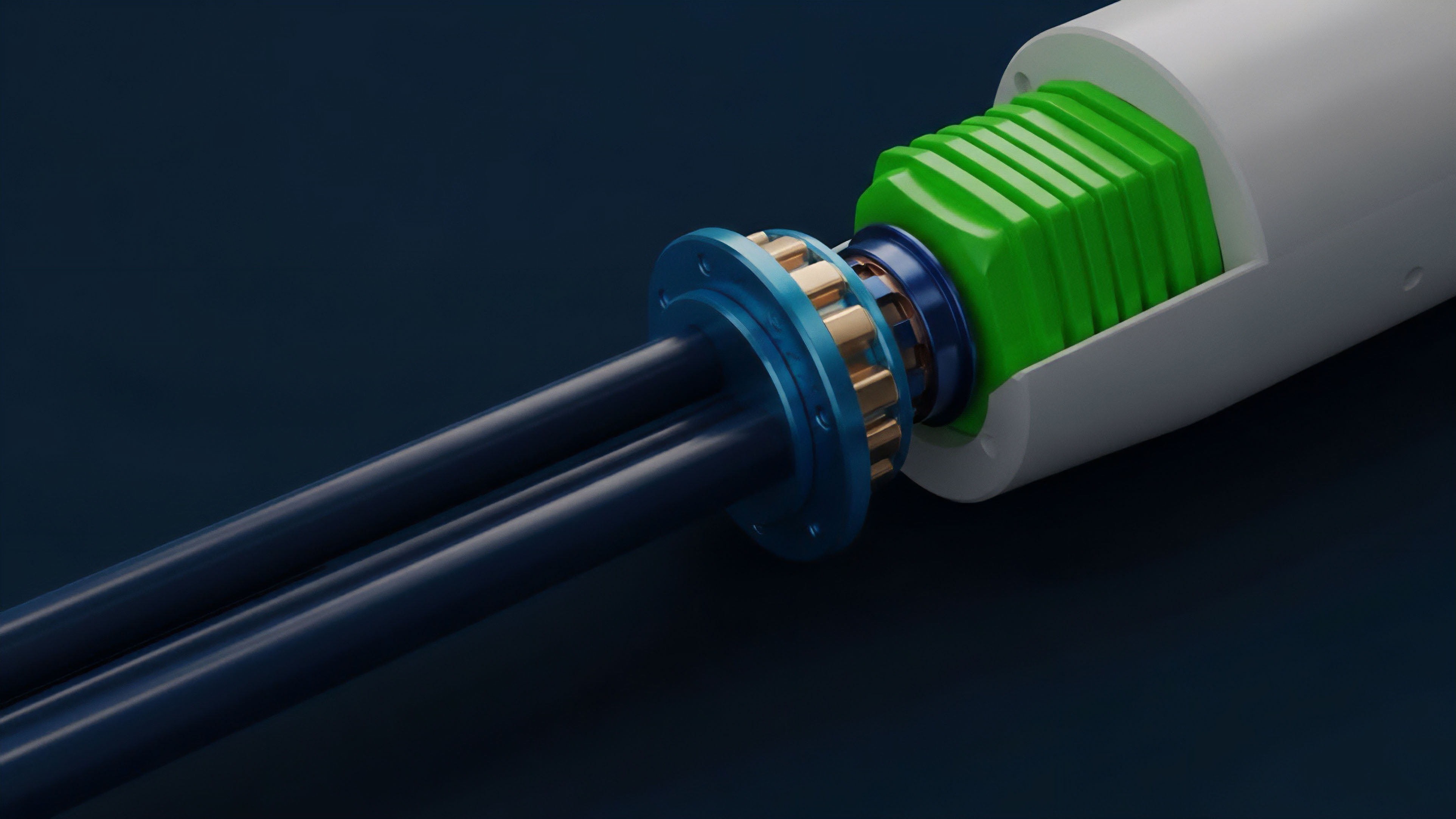
Liquidation Logic and Backstop Funds
When a user’s margin falls below a specific threshold, the protocol initiates a liquidation. The speed and method of this liquidation are critical to Economic Security.
A common approach is the use of automated liquidators ⎊ bots that monitor the blockchain for undercollateralized positions. These liquidators are incentivized to close positions by receiving a portion of the collateral. The design must ensure that these liquidators operate efficiently, even during periods of network congestion, when transaction fees (gas) may spike, potentially preventing liquidations from executing in time.
To address the possibility of liquidations failing to cover losses, protocols often establish an insurance fund or backstop mechanism. This fund acts as a buffer to cover any shortfall, preventing the protocol from becoming insolvent. The fund is typically capitalized by a portion of trading fees or by specific “backstop providers” who stake capital in exchange for rewards.
| Risk Management Component | Traditional Finance (Centralized) | Decentralized Finance (Protocol) |
|---|---|---|
| Counterparty Risk Guarantee | Central Clearinghouse (e.g. OCC) | Protocol Insurance Fund/Backstop Mechanism |
| Margin Calculation | Risk-based models (e.g. SPAN) | Algorithm-based margin engines (e.g. Portfolio Margin) |
| Liquidation Process | Human intervention and manual closeouts | Automated liquidation bots/smart contract logic |

Evolution
The evolution of Economic Security in options protocols has been driven by a cycle of innovation, failure, and refinement. Early protocols, often inspired by traditional finance models, quickly encountered systemic vulnerabilities related to oracle manipulation and liquidation cascades. The first generation of protocols struggled with high-volatility events where liquidations could not be processed fast enough.
This led to a critical insight: Economic Security requires not only accurate pricing models but also efficient execution logic that functions reliably during network congestion. The evolution moved from simple, static margin requirements to dynamic models where collateralization thresholds adjust based on current market volatility. The shift toward “Options Vaults” represents a significant evolution in risk management.
These protocols bundle options strategies into automated vaults, allowing users to participate passively while the protocol manages risk internally. This approach shifts the burden of risk management from individual users to the protocol’s automated strategy. A further evolution involves the development of protocols that utilize advanced portfolio risk calculations, similar to traditional portfolio margin systems.
These systems calculate the risk of a user’s entire portfolio, allowing for offsets between different positions. This increases capital efficiency significantly, but requires a highly sophisticated risk engine to prevent a single undercollateralized position from compromising the entire portfolio. The most advanced systems are now exploring how to manage cross-chain risk, ensuring that collateral held on one blockchain can secure positions on another.

Horizon
Looking ahead, the future of Economic Security for options protocols will focus on three key areas: advanced risk modeling, cross-chain integration, and regulatory-driven design. The next generation of risk modeling must move beyond current models that still rely on assumptions of market efficiency. The future requires models that account for “Protocol Physics” ⎊ the specific constraints and feedback loops of the blockchain itself.
This involves incorporating factors like network congestion, gas price spikes, and block time variability into the risk calculations. The models will need to be able to dynamically adjust liquidation thresholds based on real-time network conditions to prevent a situation where liquidations are economically rational but technically impossible to execute. Cross-chain integration presents a major challenge to Economic Security.
As protocols expand to multiple blockchains, managing collateral across different networks introduces new risks related to bridging mechanisms and data integrity. The future will require protocols to develop unified risk engines that can accurately calculate and manage a user’s total risk exposure across disparate chains, ensuring that a failure on one chain does not compromise the protocol’s solvency on another. The long-term horizon for Economic Security is intertwined with regulatory development.
As options protocols gain adoption, they will face increasing scrutiny from regulators. This will likely drive protocols toward greater transparency in risk reporting and potentially require new mechanisms to ensure a minimum level of capital adequacy, mirroring traditional financial regulations. The challenge will be to maintain decentralization while complying with these new standards.
The goal is to create a system where Economic Security is not just a technical feature but a core, verifiable public good that underpins a robust decentralized financial system.
| Risk Modeling Evolution | Current State (2024) | Horizon (Next 3-5 Years) |
|---|---|---|
| Volatility Modeling | Generalized Black-Scholes adaptations | Stochastic volatility models; volatility clustering models |
| Liquidation Mechanism | Automated liquidation bots; single-chain focus | Dynamic, multi-chain liquidation engines; gas-aware logic |
| Collateral Management | Isolated/Portfolio margin; single-chain assets | Cross-chain risk aggregation; tokenized real-world assets |

Glossary

Economic Finality Attack

Economic Structure

Protocol Physics Security
Security-to-Value Ratio
Network Security Expertise Development

Economic Games

Protocol Security Vulnerability Database

Collateral Security in Defi Protocols
Economic Bottleneck