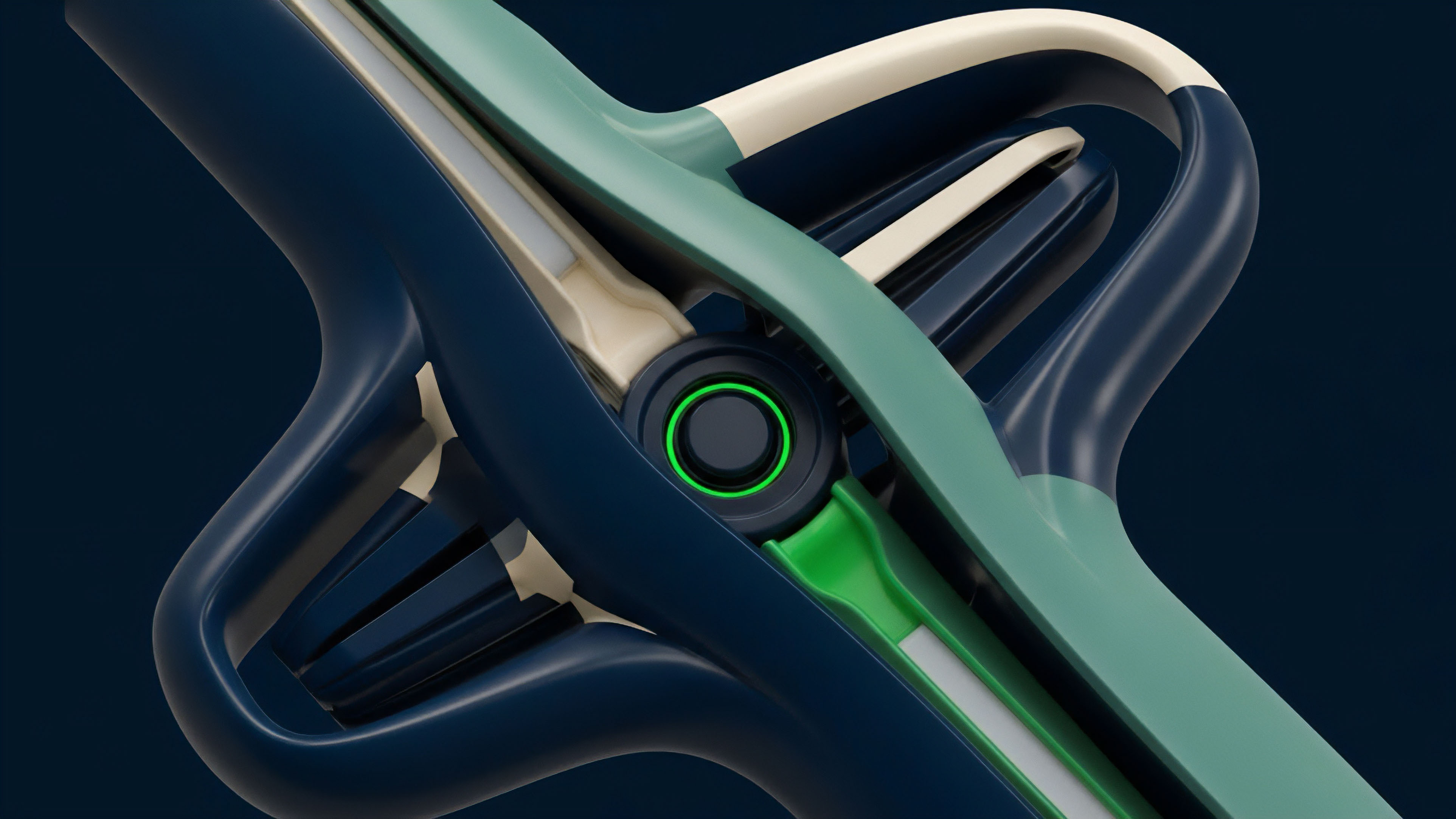
Zero-Knowledge Proofs Integration


Meaning ⎊ Zero-Knowledge Options Settlement uses cryptographic proofs to verify trade solvency and contract validity without revealing sensitive execution parameters, thus mitigating front-running and enhancing capital efficiency.
Zero Knowledge IVS Proofs
Meaning ⎊ Zero Knowledge IVS Proofs facilitate the secure, private verification of implied volatility surfaces to ensure market integrity without exposing data.
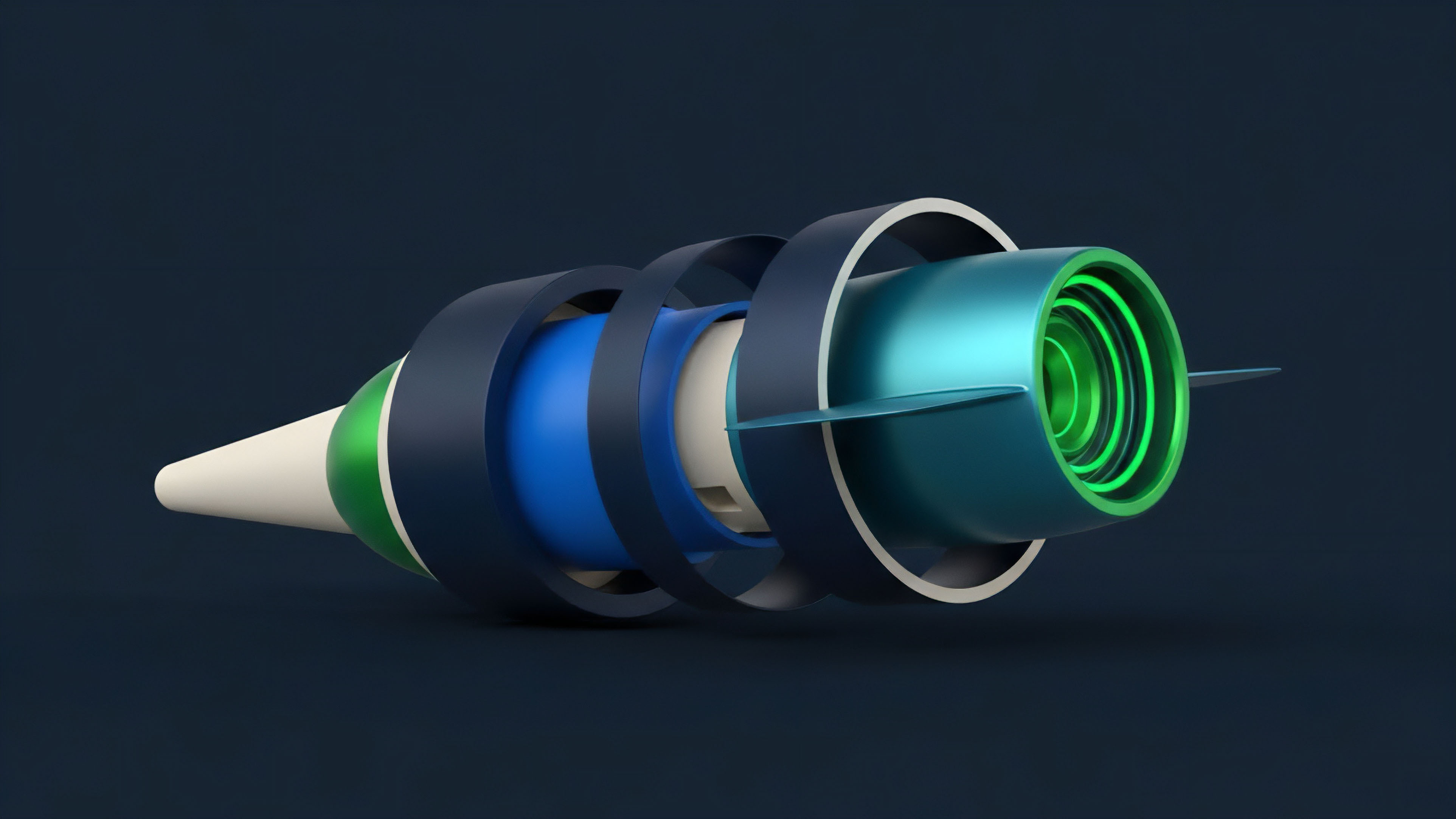
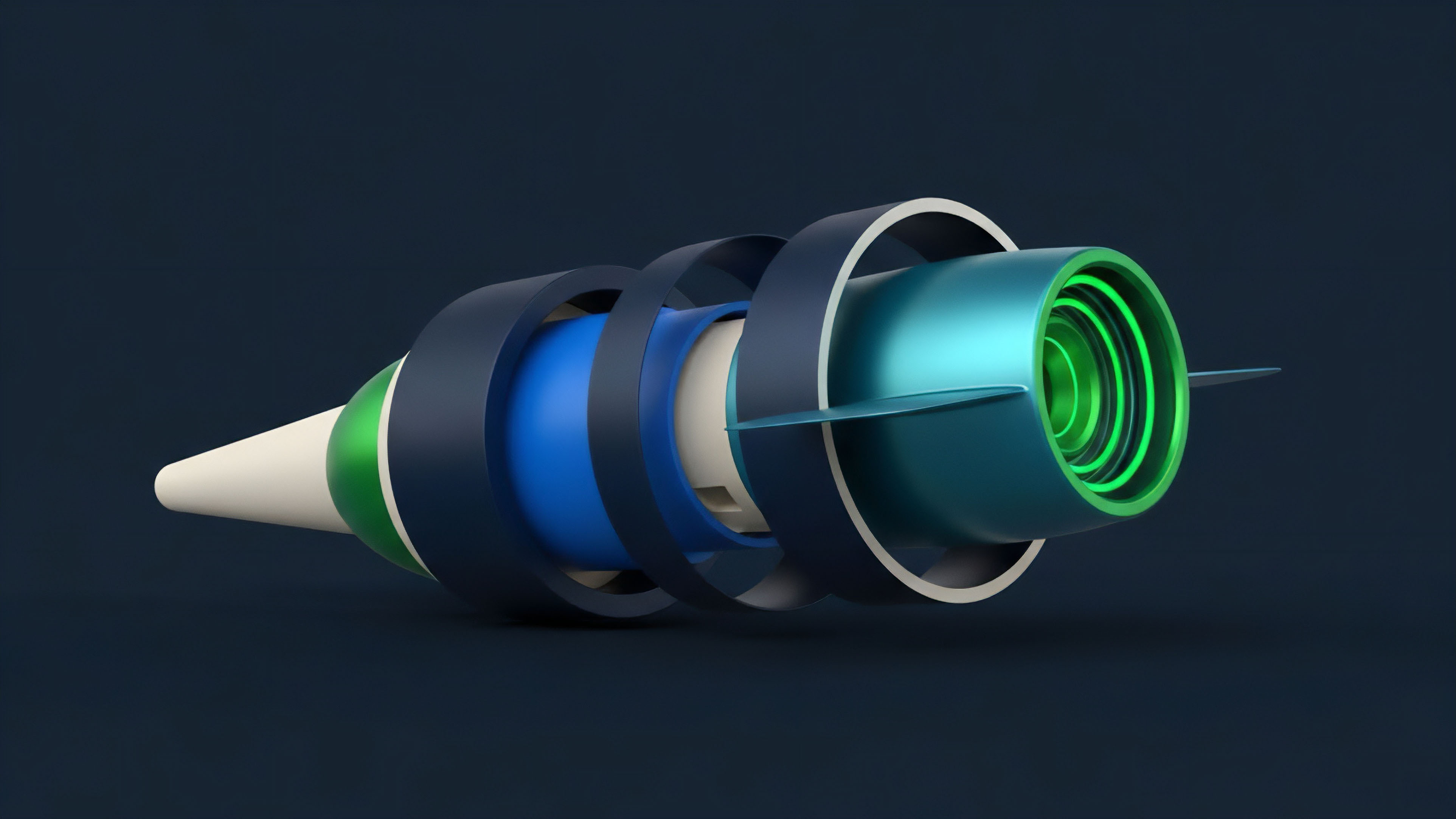
Cryptographic Proofs Verification


Meaning ⎊ Cryptographic Proofs Verification is the mathematical layer guaranteeing off-chain derivative computation integrity, enabling scalable, capital-efficient, and privacy-preserving decentralized finance.
Zero-Knowledge State Proofs


Meaning ⎊ ZK-SNARK State Proofs cryptographically enforce the integrity of complex, off-chain options settlement and margin calculations, enabling trustless financial scaling.
Zero-Knowledge Margin Proofs
Meaning ⎊ Zero-Knowledge Margin Proofs enable private, verifiable solvency, allowing traders to prove collateral adequacy without disclosing sensitive portfolio data.
Zero-Knowledge Price Proofs
Meaning ⎊ Zero-Knowledge Price Proofs cryptographically guarantee that a derivative trade's execution price is fair, adhering to public oracle feeds, without revealing the sensitive price or volume data required for market privacy.
Zero Knowledge Proofs Cryptography
Meaning ⎊ ZK-Settlement Architectures use cryptographic proofs to enable private, verifiable off-chain options trading, fundamentally mitigating front-running and boosting capital efficiency.
Zero-Knowledge Proofs Application


Meaning ⎊ Zero-Knowledge Proofs Application secures financial confidentiality by enabling verifiable execution of complex derivatives without exposing trade data.
Delta Gamma Vega Proofs
Meaning ⎊ Delta Gamma Vega Proofs enable private, verifiable attestation of portfolio risk sensitivities to ensure systemic solvency without exposing trade data.
Margin Sufficiency Proofs


Meaning ⎊ Zero-Knowledge Margin Proofs cryptographically affirm a derivatives portfolio's solvency without revealing the underlying positions, transforming opaque counterparty risk into verifiable computational assurance.
Off-Chain State Transition Proofs
Meaning ⎊ Off-chain state transition proofs enable high-frequency derivative execution by mathematically verifying complex risk calculations on a secure base layer.
Cryptographic Proofs for Transaction Integrity


Meaning ⎊ Cryptographic Proofs for Transaction Integrity replace institutional trust with mathematical certainty, ensuring verifiable and private settlement.
Margin Solvency Proofs


Meaning ⎊ Zero-Knowledge Margin Solvency Proofs cryptographically guarantee a derivatives exchange's capital sufficiency without revealing proprietary positions or risk models.
Margin Calculation Proofs


Meaning ⎊ Zero-Knowledge Margin Proofs enable verifiable collateral sufficiency in options markets without revealing private user positions, enhancing capital efficiency and systemic integrity.
Zero-Knowledge Proofs for Pricing
Meaning ⎊ ZK-Encrypted Valuation Oracles use cryptographic proofs to verify the correctness of an option price without revealing the proprietary volatility inputs, mitigating front-running and fostering deep liquidity.
Zero-Knowledge Liquidation Proofs
Meaning ⎊ ZK-LPs cryptographically verify a solvency breach without exposing sensitive account data, transforming derivatives market microstructure to mitigate front-running and MEV.
Zero-Knowledge Risk Proofs
Meaning ⎊ Zero-Knowledge Collateral Risk Verification cryptographically assures a derivatives protocol's solvency and risk exposure without revealing sensitive position data.
Zero-Knowledge Proofs for Finance
Meaning ⎊ ZK-Private Settlement cryptographically verifies the correctness of options trade execution and margin calls without revealing the private financial data, mitigating MEV and enabling institutional liquidity.
Zero-Knowledge Proofs in Trading


Meaning ⎊ Zero-Knowledge Option Primitives use cryptographic proofs to enable confidential trading and verifiable computation of financial logic like margin checks and pricing, resolving the tension between privacy and auditability in decentralized derivatives.
Zero-Knowledge Pricing Proofs


Meaning ⎊ Zero-Knowledge Pricing Proofs enable decentralized options protocols to verify the correctness of complex derivative valuations without revealing the proprietary model inputs.
Zero-Knowledge Solvency Proofs


Meaning ⎊ Zero-Knowledge Solvency Proofs cryptographically assure that a financial entity's assets exceed its liabilities without revealing the underlying balances, fundamentally eliminating counterparty risk in derivatives markets.
Zero-Knowledge Proofs Compliance


Meaning ⎊ Zero-Knowledge Proofs Compliance balances cryptographic privacy with regulatory requirements, enabling verifiable audits without revealing sensitive financial data in decentralized markets.
Smart Contract Exploit


Meaning ⎊ The bZx flash loan attack demonstrated that decentralized derivative protocols are highly vulnerable to oracle manipulation, revealing a critical design flaw in relying on single-source price feeds.
Protocol Solvency Proofs


Meaning ⎊ Protocol solvency proofs are cryptographic mechanisms that verify a decentralized options protocol's ability to cover its dynamic liabilities, providing trustless assurance of financial stability.
Zero-Knowledge Proofs Risk Verification


Meaning ⎊ Zero-Knowledge Proofs Risk Verification enables verifiable risk assessment in decentralized options markets without compromising counterparty privacy.
Zero-Knowledge Proofs KYC


Meaning ⎊ ZK-KYC allows decentralized protocols to enforce regulatory compliance by verifying specific identity attributes without requiring access to the user's underlying personal data.
Verifiable Credit Scores


Meaning ⎊ Verifiable Credit Scores enable undercollateralized lending in DeFi by quantifying counterparty risk through a composite metric of on-chain behavior and verified off-chain data.
Flash Loan Exploit Vectors


Meaning ⎊ Flash loan exploit vectors leverage atomic transactions to manipulate price oracles within options protocols, enabling attackers to extract value through incorrect premium calculations or collateral liquidations.
Zero Knowledge Proofs for Derivatives


Meaning ⎊ Zero Knowledge Proofs enable decentralized derivatives by allowing private calculation and verification of complex financial logic without exposing underlying data, enhancing market efficiency and security.