
Essence
The core function of ZK-STARKs, Zero-Knowledge Scalable Transparent Arguments of Knowledge, is to provide computational integrity for decentralized financial systems. This technology allows a prover to demonstrate that a specific computation was performed correctly without revealing the inputs of that computation. In the context of derivatives, this means a protocol can verify the state transitions of an order book or a margin account without exposing individual user balances or trading strategies.
The financial architecture of decentralized exchanges fundamentally relies on provable state changes. Without a mechanism like ZK-STARKs, every participant must re-verify every transaction, leading to significant bottlenecks in throughput and capital efficiency. ZK-STARKs resolve this by separating computation from verification, allowing a single proof to validate thousands of transactions.
The fundamental financial innovation of ZK-STARKs is decoupling computational complexity from verification cost, enabling scalable and trustless settlement for derivatives markets.
This capability directly addresses the scalability trilemma for decentralized finance. It allows for the construction of Layer 2 solutions where high-frequency trading and complex financial operations can occur off-chain, while only a small, cryptographically verifiable proof is posted to the main chain. This shift moves beyond simple token transfers to enable complex financial primitives, such as options pricing models, liquidation engines, and automated market makers, to run efficiently and securely outside the constraints of Layer 1 block space.
The systemic implication is a new foundation for decentralized market microstructure where trust is replaced by cryptographic certainty.

Origin
The concept of zero-knowledge proofs originated in the mid-1980s with the work of Goldwasser, Micali, and Rackoff, establishing the theoretical possibility of proving knowledge without revealing information. The subsequent evolution led to the development of ZK-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge).
While ZK-SNARKs provided succinct proofs, their initial implementation required a trusted setup phase. This trusted setup involved generating cryptographic parameters that, if compromised, could allow an attacker to create false proofs, undermining the integrity of the system. The reliance on a trusted setup created a central point of failure, which runs counter to the core principles of decentralization.
This architectural vulnerability, along with the potential threat posed by quantum computing to elliptic curve cryptography used in SNARKs, motivated the search for alternatives. The research into STARKs began with a focus on eliminating this trusted setup and improving scalability. STARKs achieve “transparency” by relying on public randomness for their setup, removing the need for a specific, trusted entity to generate initial parameters.
The work by Eli Ben-Sasson and others at StarkWare laid the mathematical foundation for this new type of proof system. The shift from SNARKs to STARKs represents a progression in cryptographic engineering, prioritizing transparency and quantum resistance for long-term system stability.
Theory
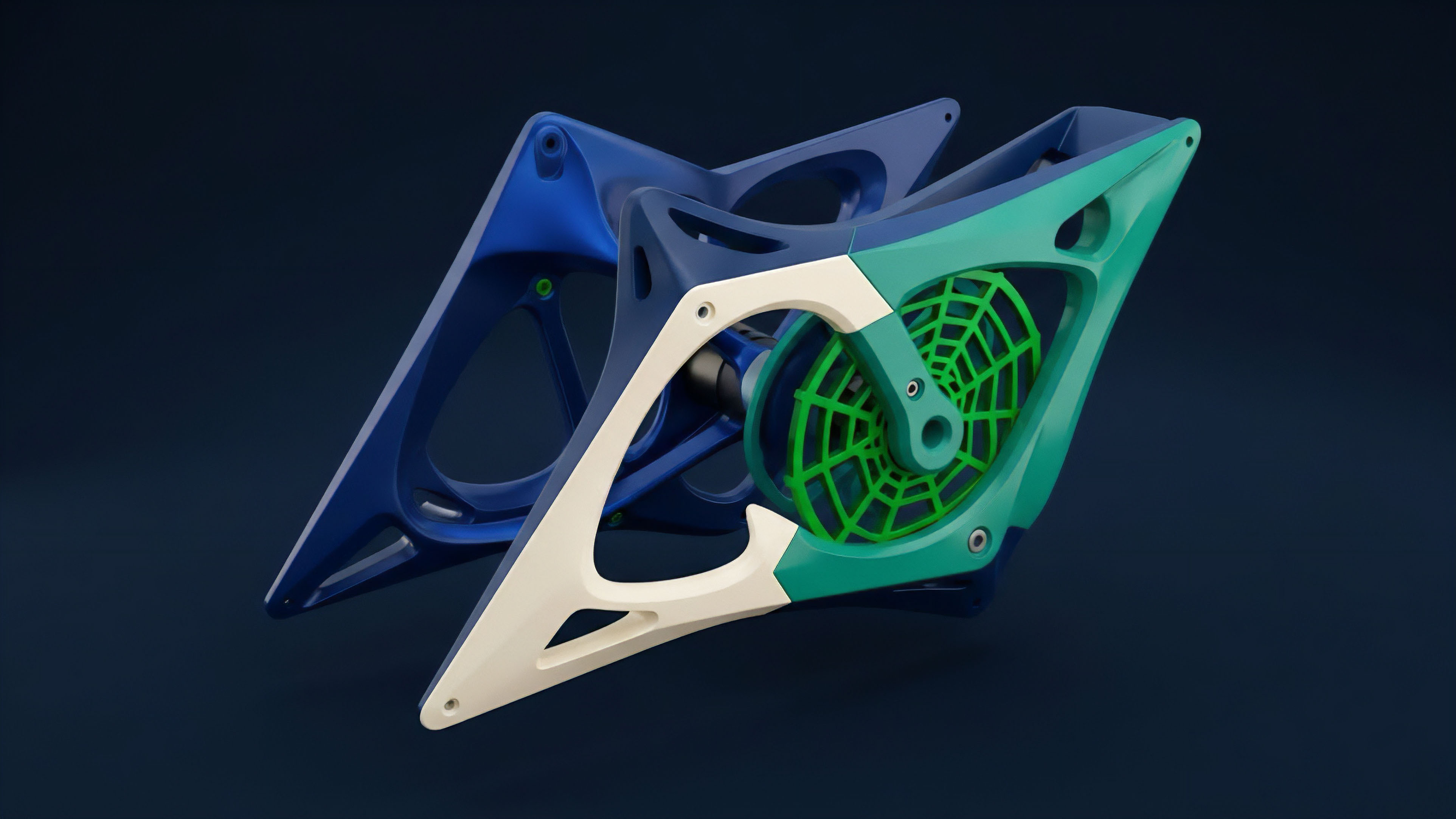
The technical underpinnings of ZK-STARKs are rooted in two key mathematical concepts: Interactive Oracle Proofs (IOPs) and Polynomial Commitment Schemes (PCS).
The IOP framework provides a structure where a prover can create a succinct argument for a complex computation. The core idea is to encode the computation into a polynomial, where the properties of the polynomial allow for efficient verification. This encoding process involves representing the computation’s execution trace as a low-degree polynomial.
The prover commits to this polynomial using a FRI (Fast Reed-Solomon Interactive Oracle Proof of Proximity) protocol, which allows the verifier to check the low-degree property of the polynomial by querying a small number of random points. This approach offers significant advantages in scalability. The verification time for a STARK proof scales logarithmically with the size of the computation.
This means verifying a proof for one million transactions takes roughly the same time as verifying a proof for ten thousand transactions. The transparency aspect of STARKs comes from its reliance on collision-resistant hash functions instead of elliptic curves, making them resistant to quantum attacks. This is a critical consideration for financial systems designed to persist for decades.
The trade-off for this transparency and scalability is a larger proof size and a more computationally intensive process for the prover.
| Feature | ZK-SNARKs (e.g. Groth16) | ZK-STARKs (e.g. StarkEx) |
|---|---|---|
| Trusted Setup | Required (specific to each application) | Not Required (transparent) |
| Verification Cost | Constant time (low cost) | Logarithmic time (sublinear, higher cost than SNARKs) |
| Prover Time | Logarithmic time (fast) | Quasilinear time (slower) |
| Quantum Resistance | No (vulnerable to Shor’s algorithm) | Yes (based on hash functions) |

Approach
In decentralized derivatives markets, the practical application of ZK-STARKs centers on enabling Layer 2 scalability for order book exchanges and perpetual futures protocols. A common implementation involves a centralized sequencer that aggregates user trades off-chain. The sequencer processes thousands of transactions, updates the internal state of all user accounts, and then generates a single ZK-STARK proof of the correct state transition.
This proof is then submitted to the Layer 1 smart contract, which verifies the proof and updates the on-chain state. This approach ensures that all off-chain trades are processed with the same integrity guarantees as on-chain transactions, without incurring the high gas fees of Layer 1. The architecture of a STARK-based exchange requires careful consideration of data availability.
While the proof guarantees computational integrity, users must be able to retrieve their account data to reconstruct the state themselves. If the sequencer withholds this data, users cannot access their funds. Solutions like Volition address this by allowing users to choose between a data-on-chain model (higher cost, full security) and a data-off-chain model (lower cost, relies on a data availability committee).
The choice of implementation determines the specific risk profile and capital efficiency of the derivative platform.
The trade-off between prover cost and verification cost defines the viability of ZK-STARKs for specific financial applications; high-throughput systems prioritize low verification costs for Layer 1 settlement.
The strategic challenge for a derivatives architect is balancing the high computational cost for the prover with the desire for high throughput. The prover’s complexity means that a significant amount of computing power is required to generate the proofs in real time. This cost must be factored into the platform’s fee structure.
The current state of implementation often involves a trade-off where a STARK-based system can support high-frequency trading but requires specialized hardware and robust economic incentives to ensure proof generation is profitable for sequencers.

Evolution
The evolution of ZK-STARKs in financial applications began with a focus on simple payment channels and basic token transfers. The initial challenge was translating complex financial logic into a format compatible with STARK proofs.
Early implementations were often limited in scope due to the high computational overhead for the prover. However, advancements in both the cryptographic protocols themselves and in specialized hardware (like FPGAs and ASICs) have significantly improved the efficiency of proof generation. This has allowed for a transition from simple transfers to supporting complex financial instruments.
The shift in focus has moved from proving simple state transitions to proving the execution of an entire virtual machine. The development of STARK-based Layer 2 solutions like Starknet allows developers to write smart contracts in a language like Cairo, which is specifically optimized for STARK proof generation. This abstraction allows for the creation of sophisticated derivatives protocols without requiring deep cryptographic expertise from the application developer.
The evolution represents a move from a specific-application proof system to a general-purpose computational layer for decentralized finance.
- Early ZK-Rollups (2019-2020): Focused on basic token transfers and simple exchanges. The primary goal was to reduce Layer 1 transaction fees.
- STARK-Based Derivatives (2021-2022): Integration of STARKs into order book exchanges (e.g. dYdX) to scale perpetual futures trading. This required proving complex calculations like margin requirements and liquidation logic.
- General Purpose ZK-VMs (2023-Present): Development of ZK-STARK virtual machines (e.g. Starknet) that enable arbitrary smart contract logic to be executed and proven off-chain, opening the door for complex options and structured products.

Horizon
The future potential of ZK-STARKs extends beyond simply scaling existing financial primitives. The technology enables new forms of market microstructure that were previously impossible due to privacy and scalability constraints. One area of significant potential is privacy-preserving derivatives.
By using ZK-STARKs, traders could prove they meet margin requirements without revealing their positions to other market participants. This eliminates the information asymmetry inherent in public ledger systems, where front-running and market manipulation are significant risks. A truly private order book could dramatically change trading dynamics, moving away from the current adversarial environment.
Another area is the creation of cross-chain financial instruments. ZK-STARKs can be used to prove state transitions across different blockchains without requiring a trusted bridge or intermediary. This allows for the creation of derivatives where the underlying assets are on one chain and the collateral is on another, creating a truly interconnected financial ecosystem.
The application of STARKs in this context allows for the development of trustless settlement layers that can support complex, multi-asset financial products. The integration of STARKs into decentralized autonomous organizations (DAOs) could also reshape governance. By allowing for private voting and proof of eligibility without revealing individual holdings, ZK-STARKs enable more robust and secure governance models.
The technology’s impact on financial strategies is profound ⎊ it moves beyond simply replicating traditional finance on-chain to creating new financial tools built on cryptographic certainty.
The next generation of decentralized financial systems will likely utilize ZK-STARKs to create private order books, enabling market microstructures that mitigate front-running and information leakage.
The strategic challenge for the future lies in standardizing these technologies and reducing the complexity of development. As ZK-STARKs become a foundational layer for decentralized finance, the focus shifts to creating efficient tooling and frameworks for developers. This will accelerate the creation of novel financial products and enable a new generation of high-throughput, private, and quantum-resistant markets.
Glossary

Starks
Decentralized Autonomous Organizations

Perpetual Futures

Verification Cost
Proving Systems

Zk-Snarks Zk-Starks

Trustless Settlement

Front-Running Mitigation
Financial Engineering






