Essence
The Prover’s Malice represents the most critical systemic risk at the intersection of Zero-Knowledge Proofs (ZKPs) and decentralized derivatives ⎊ specifically, the successful generation of a cryptographically sound proof that deliberately masks a financially unsound reality. This failure mode transcends a simple coding bug; it is an economic exploit rooted in the manipulation of the prover’s private witness, allowing a participant to satisfy a protocol’s solvency check while operating with insufficient collateral or systemic over-leverage. This capability directly compromises the integrity of a ZK-based options exchange, where the core value proposition is trustless verification of margin requirements.
The true danger lies in the asymmetry of information. A centralized exchange relies on an auditor to check the ledger; a decentralized ZK-exchange relies on the proof’s validity. If the proof is valid, yet the hidden state it confirms is a lie ⎊ a lie about collateralization ⎊ the market’s faith in the protocol’s capital efficiency is fundamentally misplaced.
This creates a hidden, unquantifiable counterparty risk, which in traditional finance is the domain of regulatory oversight. In the decentralized context, the Prover’s Malice transforms a technical guarantee into a sophisticated financial deception, poisoning the order book with phantom liquidity.
The Prover’s Malice is the systemic vulnerability where cryptographic proof validity conceals financial insolvency, undermining the core trust model of ZK-based derivatives.
The Core Deception
The deception operates by leveraging the gap between cryptographic correctness and economic reality. The ZKP circuit only checks the consistency of the public output with the private input, according to the predefined arithmetic constraints. If the prover can construct a private witness ⎊ a set of inputs ⎊ that satisfies the circuit’s constraints while simultaneously violating an unstated or external economic constraint, the exploit is successful.
For options markets, this often involves manipulating the value assigned to illiquid collateral or temporarily obscuring a lien on the underlying assets. The systemic implication is a loss of capital fidelity ⎊ the protocol believes capital exists where it does not.

Origin
The genesis of this risk lies in the application of cryptographic primitives ⎊ specifically zk-SNARKs and zk-STARKs ⎊ to financial state compression. These proofs were designed for computational integrity, ensuring a computation was performed correctly.
Their application to financial solvency ⎊ a matter of economic integrity ⎊ introduces a new set of attack vectors. The original concept for ZKPs, rooted in the work of Goldwasser, Micali, and Rackoff, focused on the security of knowledge transfer. When applied to a leveraged financial system, the focus shifts to the security of capital representation.

Cryptographic Foundation and Economic Drift
The problem arises from the drift between the abstract mathematical proof and the volatile, real-world assets it attempts to represent.
- The Bounded Circuit Problem: ZKP circuits are finite and static. They must be designed to capture every possible state transition and constraint. Any economic scenario not explicitly constrained ⎊ such as a sudden, illiquid drop in the price of a specific collateral token ⎊ creates an unconstrained variable that the malicious prover can exploit.
- Trusted Setup Exploits: While not a direct exploit of the proof itself, a compromised Trusted Setup in zk-SNARKs could allow a prover to generate a false proof that is accepted as valid, bypassing the financial check entirely. This is a foundational, though now less common, risk.
- Input Witness Manipulation: The more sophisticated and prevalent failure. The prover feeds the ZKP circuit a carefully constructed private witness that passes the algebraic check for solvency at the moment of proof generation, even if the actual, verifiable market value of the collateral is insufficient for the option position’s risk profile.
This challenge is a direct descendant of the limitations observed in early attempts at verifiable computation, where the environment’s complexity always outpaced the proof’s expressiveness. Our inability to fully constrain the global financial state within a fixed circuit is the ultimate source of the Prover’s Malice.
Theory
The theoretical analysis of The Prover’s Malice requires a synthesis of quantitative finance, adversarial game theory, and the algebraic geometry underlying ZKPs. The core mechanism is a form of Adversarial Witness Construction.

Adversarial Witness Construction
In a ZK-options protocol, the solvency constraint is typically an arithmetic circuit that checks: Collateral Value ge Max Loss Exposure. The Collateral Value is a function of the private collateral amount and the public oracle price. Max Loss Exposure is derived from the option’s Greeks and the underlying asset’s volatility.
The Prover’s Malice involves constructing a private collateral amount, C’, such that: Proof(Public Parameters, Private Witness W) ⎊ True
Where W = (C’, dots)
But where the true, verifiable collateral C is such that C < Max Loss Exposure The divergence, C' - C, is the magnitude of the financial fraud hidden by the ZKP. This is not a failure of the ZKP's zero-knowledge property ⎊ the collateral amount remains hidden ⎊ but a failure of its soundness in the economic domain, as the proof affirms a statement that is economically false.
The divergence between the private witness used for the proof and the true economic state of collateral is the mathematical definition of The Prover’s Malice.

Game Theory of Exploitation
From a behavioral game theory perspective, the Prover’s Malice is an optimal strategy in a non-cooperative, non-zero-sum game, provided the cost of generating the malicious proof is less than the potential profit from the unbacked leverage. The Prover is incentivized to:
- Maximize Opacity: Exploit the most complex parts of the circuit ⎊ often the volatility and risk parameters ⎊ as these are the hardest to audit for constraint completeness.
- Time the Collapse: Maintain the malicious state until a large, profitable trade can be executed, or until the hidden insolvency is too large for the system to absorb, leading to a systemic socialization of loss.
The risk is amplified by the Macro-Crypto Correlation. During periods of high systemic stress, asset correlations converge to one, and volatility spikes, precisely when the hidden under-collateralization of a malicious prover is most likely to cause a chain reaction. This convergence makes the single, hidden failure a catalyst for systemic contagion.
(It is fascinating how closely this mirrors the shadow banking system’s reliance on opaque collateralized debt obligations, where complexity served as the ultimate veil against true risk discovery.)
| Proof State | Financial State | Outcome & Risk |
|---|---|---|
| Valid | Solvent (True) | Ideal State, High Trust |
| Valid | Insolvent (False) | The Prover’s Malice, Hidden Contagion |
| Invalid | Solvent (True) | Circuit Bug, Denied Access |
| Invalid | Insolvent (False) | Correct Rejection, System Sound |

Approach
Countering The Prover’s Malice demands a shift in protocol design, moving beyond simple proof validation to a system of Economically Constrained Cryptography. The current approach in decentralized options protocols is insufficient, relying too heavily on the soundness of the cryptographic proof alone.

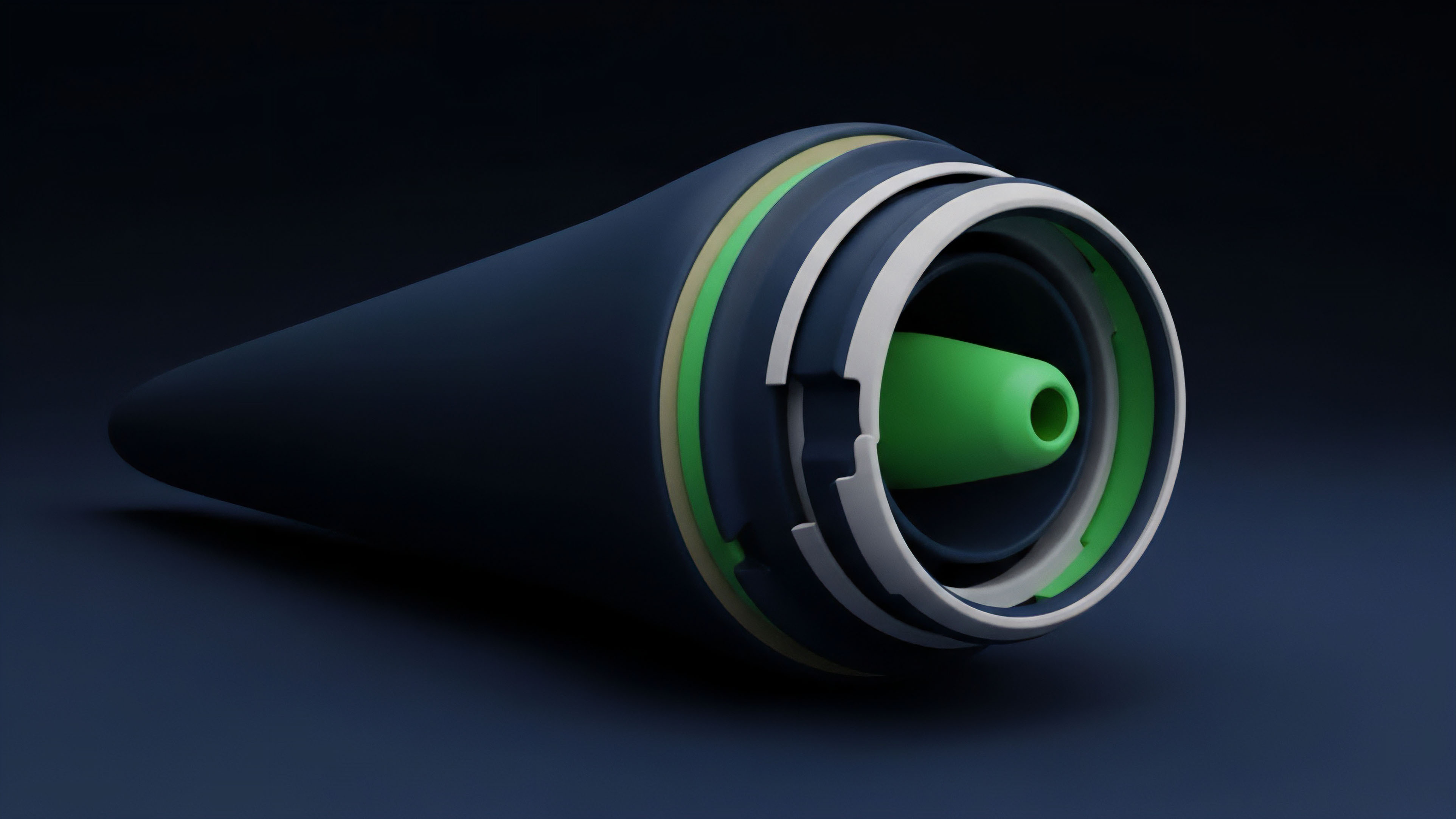
Protocol Physics and Constraint Layering
The practical defense against this attack involves layering financial constraints over the core ZKP circuit, forcing the prover to reveal specific, limited information necessary for economic soundness without sacrificing the zero-knowledge property for competitive advantage.
- Liquidation Oracle Integration: The circuit must be constrained by a proof that the collateral is not currently marked for liquidation on any other integrated protocol. This requires the ZKP to ingest a small, publicly verifiable hash of the prover’s state across a defined set of interconnected DeFi protocols.
- Delta Constraint Disclosure: Instead of hiding the entire collateral position, the ZKP could be forced to prove the collateral’s Delta ⎊ its sensitivity to the underlying price ⎊ falls within a publicly acceptable, narrow band relative to the option position’s Delta. This limits the hidden risk without revealing the precise trading strategy.
- Circuit Complexity Reduction: Protocol designers must actively resist the urge to create excessively complex circuits that attempt to model every financial scenario. Complexity introduces unconstrained edges, which the malicious prover will always find. Simplicity and over-collateralization ⎊ a pragmatic choice ⎊ provide a stronger defense.

The Market Microstructure Defense
The defense against the Prover’s Malice also resides in the market’s microstructure. Order flow and liquidity dynamics can be engineered to penalize hidden insolvency. A protocol can institute dynamic margin requirements that scale with the anonymity of the prover’s position.
A prover that generates proofs less frequently, or one whose positions represent a larger share of the protocol’s total open interest, should be subject to a higher, systemically safer margin floor. This introduces a subtle, friction-based cost to the Prover’s Malice strategy, making the exploit less profitable over time.
| Defense Mechanism | Targeted Risk | Impact on Prover |
|---|---|---|
| External State Hash Check | Hidden Cross-Protocol Liens | Increases Cost of Malicious Witness Construction |
| Delta Constraint Disclosure | Unbacked Systemic Risk (Vega) | Limits Maximum Hidden Leverage |
| Anonymity-Adjusted Margin | Exploit Profitability | Penalizes High Opacity/Large Positions |
Evolution
The understanding of ZKP failure in finance has evolved from a theoretical concern about proof completeness to a practical concern about proof utility in an adversarial financial environment. Early iterations of ZK-options protocols focused almost exclusively on the computational efficiency of the proof generation ⎊ a technical benchmark. The next stage of development, driven by the practical realization of the Prover’s Malice potential, pivots the focus entirely to Financial Soundness Proofs.
From Technical Soundness to Economic Soundness
The initial goal was simple: prove A=B. The evolved goal is: prove A=B and that A represents sufficient capital to cover the maximum probable loss, L, such that A ge L. This evolution necessitates a deeper integration of Quantitative Finance & Greeks directly into the circuit design. For instance, the circuit must not just check the value of collateral; it must check that the collateral value minus the option’s Vega exposure multiplied by a defined volatility shock remains positive. This moves the protocol from passive accounting to active, probabilistic risk management.

The Contagion Vector
Historically, financial crises ⎊ from the Long-Term Capital Management collapse to the 2008 subprime crisis ⎊ were characterized by the opaque leverage of a few interconnected entities. The Prover’s Malice is the decentralized equivalent of this hidden leverage. The evolution of our response must therefore focus on Systems Risk & Contagion modeling.
We are seeing a slow, deliberate move toward “ZK-Auditability” ⎊ a system where a non-zero-knowledge proof of the aggregate solvency of the entire protocol is generated and published periodically. This aggregate proof does not reveal any individual’s position, but it confirms the collective capital buffer against systemic shocks, effectively limiting the maximum possible damage a single malicious prover can inflict before the system is forced to deleverage. This is the painful but necessary trade-off between absolute privacy and collective resilience.
Moving beyond technical proof validity, the evolution of ZK-derivatives demands cryptographic assurances of economic soundness, particularly against hidden systemic leverage.
Horizon
The future of ZK-derivatives is a protracted, intellectual arms race against the Prover’s Malice. The ultimate horizon involves the development of Regulatory Arbitrage & Law -compliant ZKP systems that satisfy jurisdictional requirements for anti-money laundering and counter-terrorism financing without compromising user privacy. The technology that defeats the Prover’s Malice may be the same technology that allows decentralized finance to onboard institutional capital.

The Zero-Knowledge Regulatory Nexus
The next generation of ZKP protocols will likely incorporate a mandatory, auditable “trapdoor” mechanism ⎊ not for malicious backdoor access, but for compliance. This mechanism would allow a designated, auditable third party (a regulator or a decentralized autonomous organization (DAO) with specific, on-chain governance rights) to verify the aggregate solvency of the protocol in the event of a catastrophic failure, while maintaining the privacy of individual positions under normal operating conditions. This structural compromise ⎊ the acceptance of a conditional, external oversight mechanism ⎊ is the necessary price for systemic stability and mass adoption.

Tokenomics and Value Accrual
The tokenomics of future ZK-protocols will directly penalize the potential for Prover’s Malice. We will see a shift toward a Proof-of-Stake model where a portion of a participant’s collateral is permanently locked in a Security Bond. If the protocol’s aggregate solvency proof fails ⎊ indicating a successful Prover’s Malice attack ⎊ all staked security bonds are automatically slashed, with the proceeds used to recapitalize the protocol. This creates an economic disincentive for malicious behavior that outweighs the potential gains from hidden leverage. The system becomes self-healing and adversarial-resistant by design. The very act of participation in the options market requires staking against the possibility of one’s own malfeasance. This structural mechanism aligns the incentives of the individual trader with the collective stability of the market. The architecture of a truly resilient financial system must assume malice and price it accordingly.
Glossary

Collateral Sufficiency Proof

Tokenomics

Code Failure Risk
Identity Proof
Systemic Failure Response

Portfolio Var Proof

Proof of Correctness in Blockchain

Merkle Tree Proof
Counterparty Failure