
Essence
Proof of Integrity represents a cryptographic mandate for the verifiable execution of derivative logic, ensuring that every state transition in an options contract adheres to predefined mathematical constraints. This mechanism shifts the burden of trust from institutional intermediaries to computational proofs, where the validity of a margin call or an exercise event is mathematically certain. Within decentralized finance, this principle guarantees that the solvency of a protocol remains transparent and irrefutable, regardless of market volatility or participant behavior.
Computational integrity transforms financial trust into a verifiable mathematical property of the system architecture.
The primary function involves the generation of succinct proofs that attest to the correct application of risk parameters and price data. By utilizing zero-knowledge primitives, Proof of Integrity allows a protocol to prove that a specific liquidation was necessary without exposing the underlying sensitive trader data. This creates a high-fidelity environment where the execution of the contract is decoupled from the identity of the operator, fostering a resilient infrastructure for complex financial instruments.

Origin
The genesis of this concept lies in the structural failures of legacy clearing systems, which often rely on opaque risk models and delayed settlement cycles.
Traditional finance operates on a “trust-but-verify” model that frequently breaks during liquidity crises, as seen in the systemic collapses where collateral valuations became disputed. Proof of Integrity emerged as a technical response to these vulnerabilities, drawing from early research in verifiable computing and the necessity for trustless settlement in adversarial environments.

The Shift from Legal to Cryptographic Assurance
Initial implementations focused on simple asset transfers, but the requirement for sophisticated derivatives necessitated a more robust framework. The transition began when developers integrated arithmetic circuits to validate complex payoff functions. This evolution moved the industry away from subjective legal recourse toward objective cryptographic finality.
- Asymmetric Information Resolution: Cryptographic proofs eliminate the advantage held by centralized entities during trade disputes.
- Deterministic Settlement: The move toward code-based execution ensures that the outcome of an option contract is determined solely by the initial parameters and verified data.
- Collateral Transparency: Real-time verification of margin requirements prevents the hidden leverage that historically triggered contagion.
The historical move from subjective clearing to objective proof-based validation marks the end of the opaque institutional era.

Theory
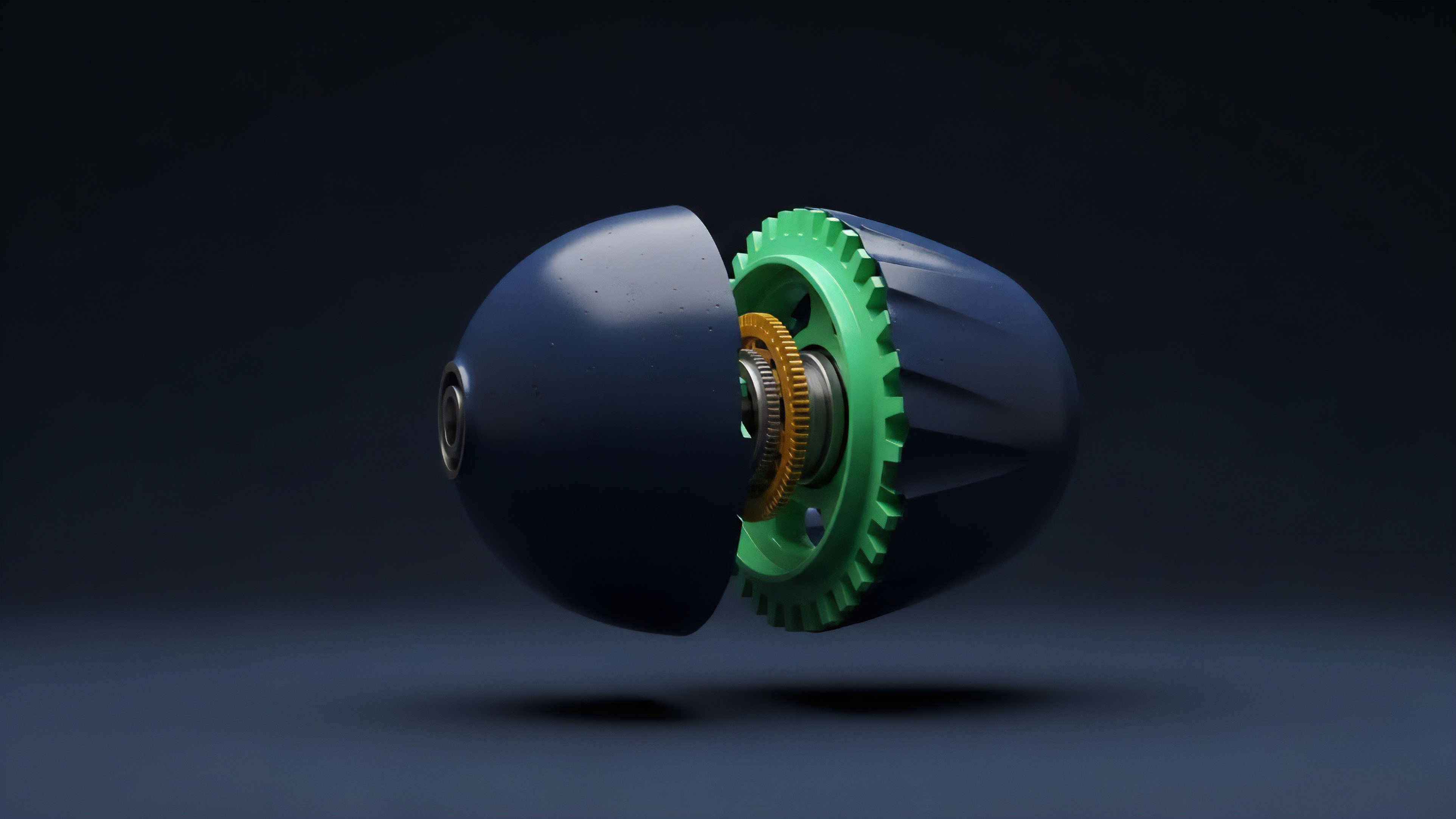
The theoretical framework of Proof of Integrity rests on the ability to represent financial logic as a series of polynomial constraints. In this model, every action ⎊ from depositing collateral to calculating the delta of an option ⎊ is treated as a computation that must produce a valid proof. The system utilizes a prover-verifier architecture where the prover (the exchange or protocol) generates evidence of correct execution, and the verifier (the blockchain or a decentralized network) confirms this evidence with minimal computational cost.

Mathematical Constraints and Margin Engines
The margin engine within a Proof of Integrity system operates through a set of recursive proofs. These proofs validate that the net equity of a portfolio exceeds the maintenance margin at every timestamp. If a liquidation occurs, the system generates a proof showing that the price input from the oracle triggered the liquidation threshold according to the immutable protocol rules.
| Feature | Optimistic Verification | Integrity Proofs (ZK) |
|---|---|---|
| Validation Speed | Delayed by challenge periods | Instantaneous via proof verification |
| Capital Efficiency | Low due to withdrawal delays | High through immediate finality |
| Data Privacy | Publicly exposed on-chain | Shielded via cryptographic circuits |
Polynomial Commitments in Options Pricing
To maintain Proof of Integrity in options pricing, the Black-Scholes or similar models are encoded into circuits. This ensures that the implied volatility and Greeks used for margin calculations are not manipulated by the platform operator. The integrity of the pricing model becomes a verifiable constant, protecting participants from “phantom” liquidations caused by artificial price spikes in the internal engine.
Approach
Current methodologies for implementing Proof of Integrity involve the use of Zero-Knowledge Scalable Transparent Arguments of Knowledge (zk-STARKs) or Succinct Non-Interactive Arguments of Knowledge (zk-SNARKs).
These technologies allow the off-chain execution of high-frequency trading logic while maintaining the security guarantees of the underlying layer-one blockchain. The protocol executes the matching engine and risk calculations in a high-performance environment, then submits a compressed proof to the mainnet.

Implementation Architecture
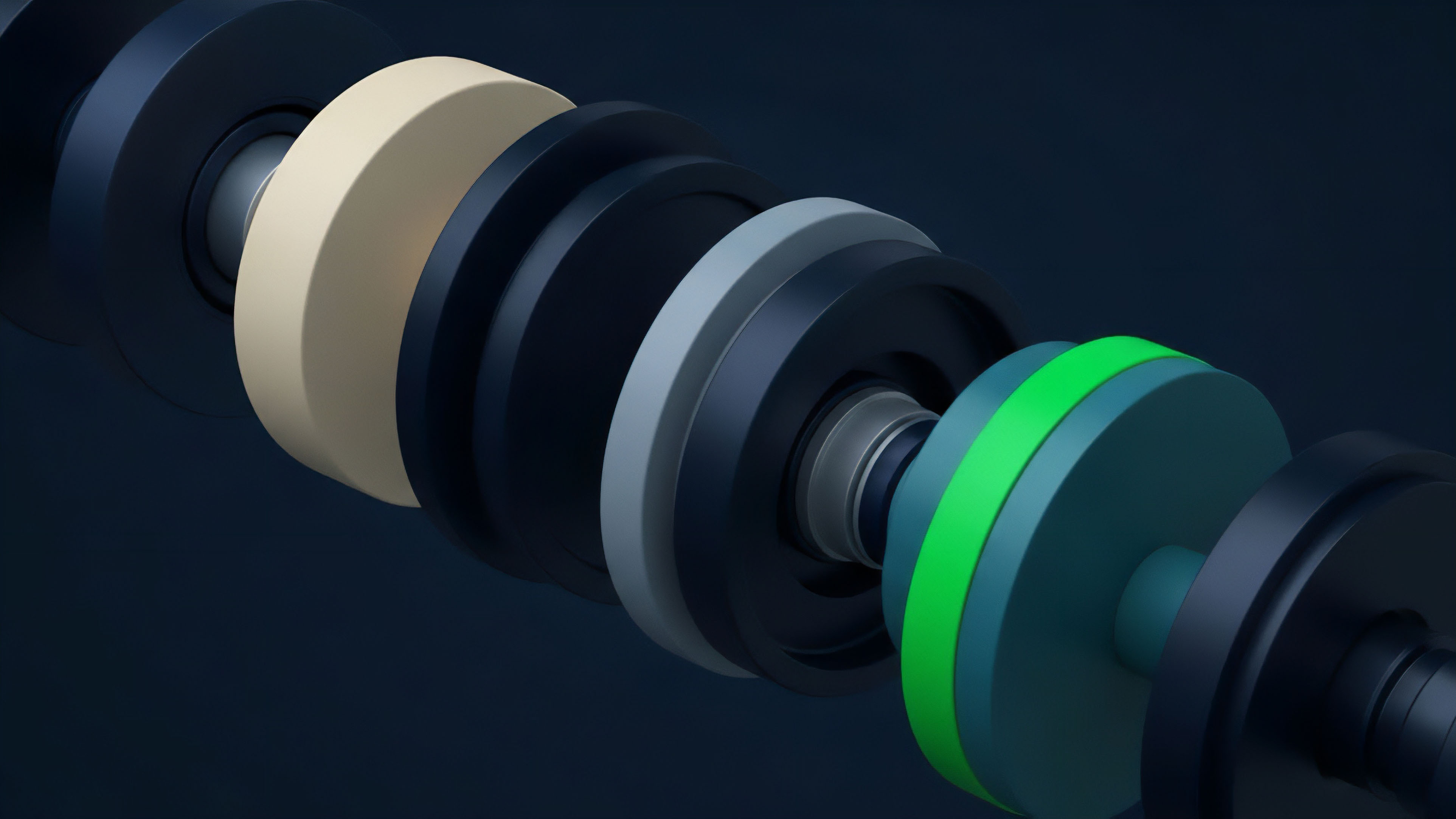
The integration of Proof of Integrity requires a multi-layered stack where data availability and execution are strictly separated. The execution layer handles the heavy lifting of calculating Greeks and managing order books, while the integrity layer ensures that no unauthorized state changes occurred.
- Circuit Compilation: Financial logic is translated into a format compatible with cryptographic proof systems.
- Oracle Integration: Signed data feeds are fed into the circuit to provide a verifiable source of truth for price action.
- Proof Generation: For every batch of trades, a proof is constructed that validates the entire state transition of the exchange.
- On-chain Verification: A smart contract verifies the proof, updating the global state only if the math is flawless.
Modern derivative architectures utilize succinct proofs to maintain global solvency without sacrificing execution speed.
| Component | Functionality | Integrity Mechanism |
|---|---|---|
| Matching Engine | Order pairing | Sequence validation proofs |
| Risk Engine | Margin monitoring | Arithmetic circuit constraints |
| Oracle Gateway | External data ingestion | Cryptographic signature verification |

Evolution
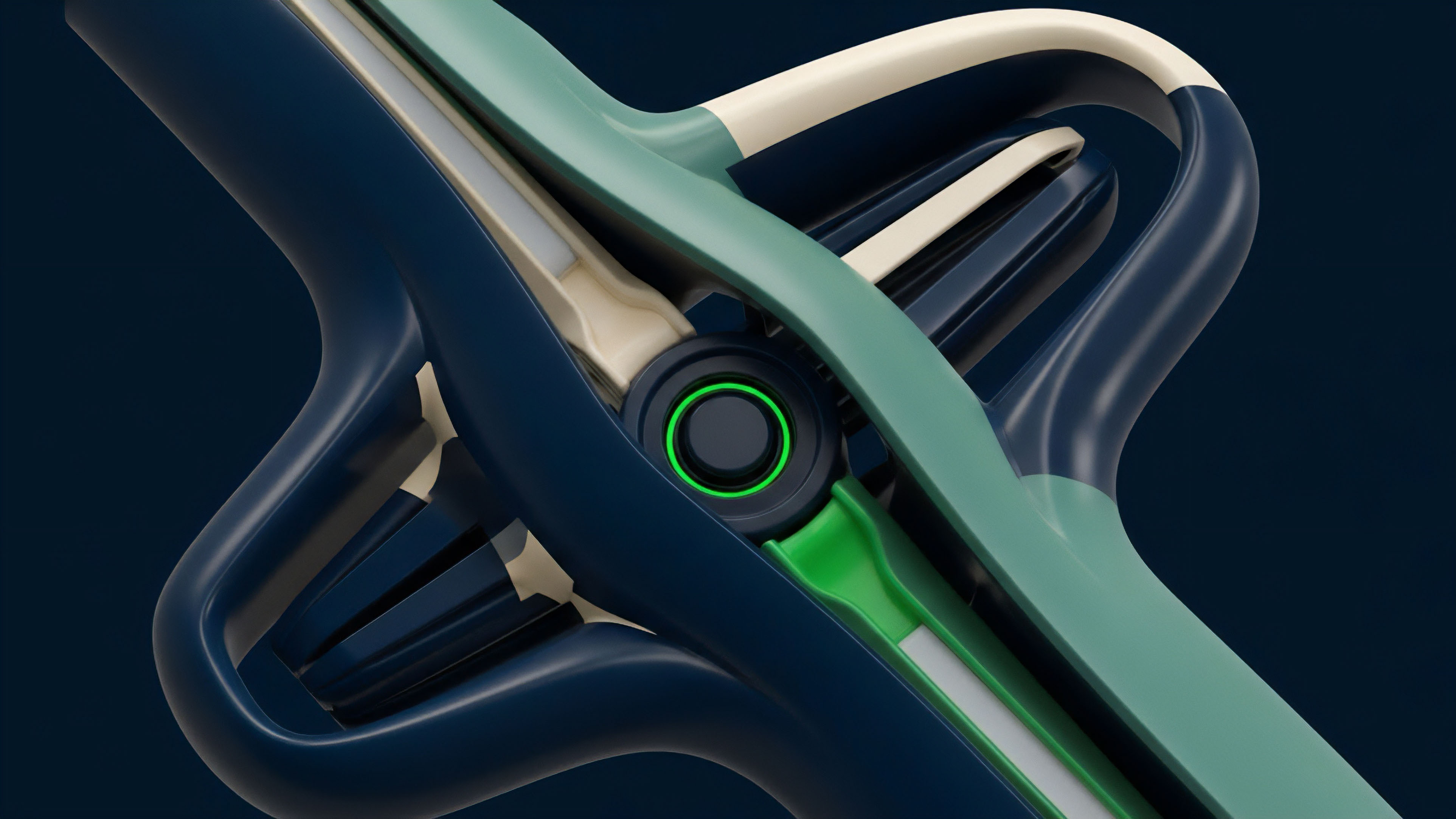
The trajectory of Proof of Integrity has moved from simple validity proofs for payments to the complex validation of multi-legged option strategies. Early decentralized exchanges lacked the capacity for sophisticated risk management, often resulting in systemic insolvency during extreme market moves. The introduction of verifiable computation changed this by allowing protocols to enforce strict collateralization ratios without manual intervention.

From Escrow to Autonomous Risk Management
The first stage involved basic multisig escrows where humans or simple scripts controlled the funds. This was replaced by automated market makers (AMMs), which provided transparency but lacked capital efficiency. The current state represents the third generation: order-book-based derivatives platforms that use Proof of Integrity to offer professional-grade trading experiences with the security of non-custodial systems.
This shift has significantly reduced the cost of capital by eliminating the need for large insurance funds that were previously required to cover “trust gaps.”

Horizon
The future of Proof of Integrity points toward a unified liquidity environment where cross-chain derivative positions are verified through recursive proof aggregation. This will enable a trader to hold an option on one chain while their collateral resides on another, with the integrity of the entire position maintained by a single, verifiable proof. As hardware acceleration for proof generation improves, the latency between execution and verification will vanish, making decentralized options indistinguishable from their centralized counterparts in terms of performance.

Verifiable Artificial Intelligence in Risk Modeling
The next frontier involves integrating machine learning models into the Proof of Integrity framework. Future risk engines will likely use AI to predict volatility and adjust margin requirements dynamically. By proving the correct execution of these AI models through zk-ML (Zero-Knowledge Machine Learning), protocols will ensure that the automated risk adjustments are fair, transparent, and free from algorithmic bias or developer manipulation.
This represents the ultimate convergence of advanced computation and financial stability.
- Hyper-Scalable Proofs: New proof systems will allow millions of transactions per second to be verified on consumer-grade hardware.
- Atomic Cross-Chain Integrity: Simultaneous verification of state across disparate networks will eliminate bridge risks.
- Sovereign Risk Management: Individual users will possess the tools to verify the solvency of their counterparties in real-time.

Glossary

Data Availability Sampling

Succinctness

Arithmetic Circuits

Decentralized Clearinghouse

Succinct Non-Interactive Arguments of Knowledge

Proof-of-Solvency

Black-Scholes Circuit

State Root Validation
Computational Integrity






