Essence
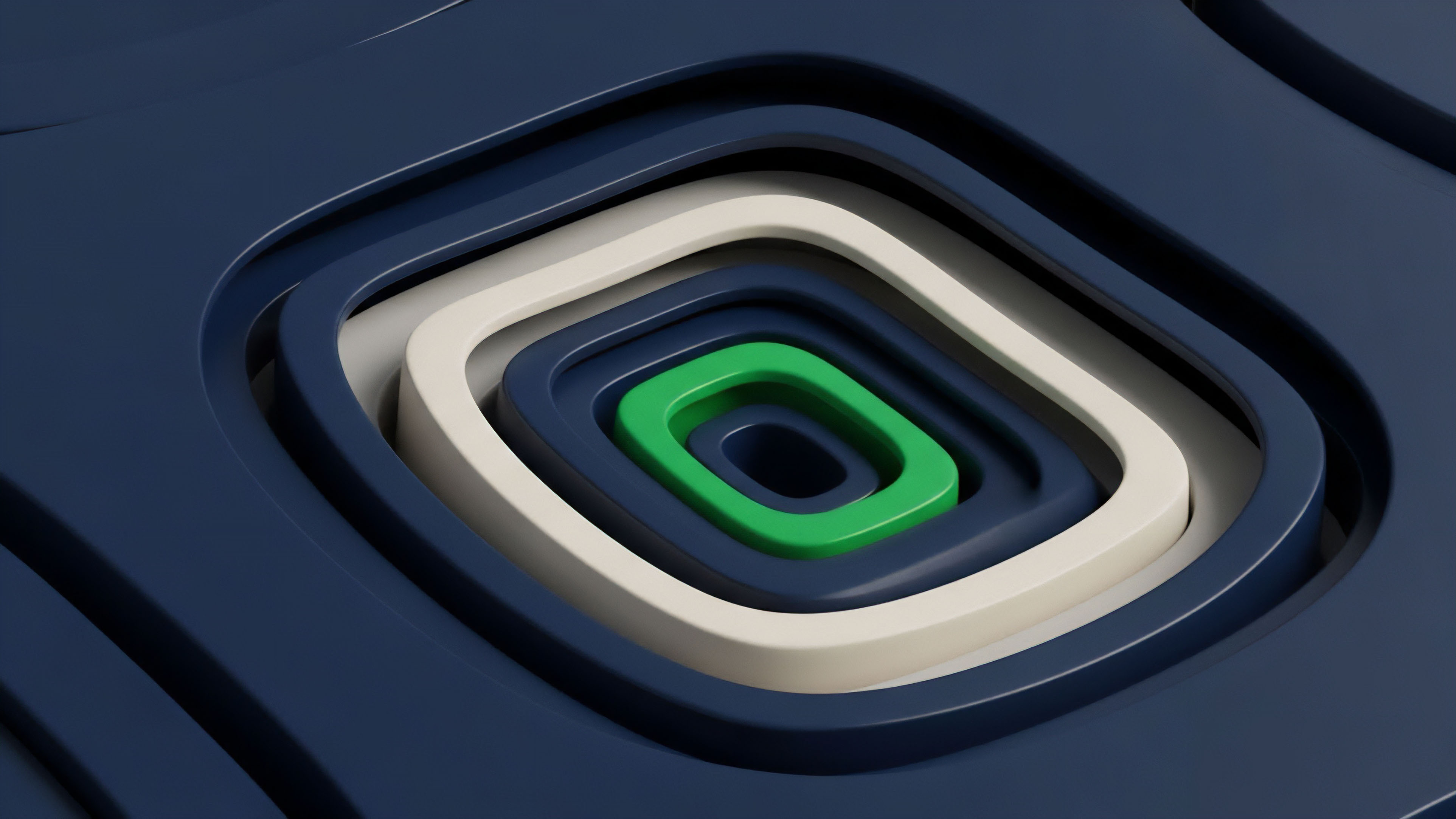
Verification without disclosure defines the operational logic of Zero-Knowledge Architectures. This cryptographic framework allows a prover to demonstrate the validity of a specific statement to a verifier without revealing the underlying data that makes the statement true. In the context of decentralized finance, this translates to the ability to settle complex options contracts, verify margin requirements, or execute liquidations while maintaining the absolute confidentiality of the participant’s position and strategy.
The systemic value of these architectures lies in their capacity to decouple information from validation. By utilizing mathematical proofs rather than data transparency, Zero-Knowledge Architectures resolve the inherent tension between the public nature of distributed ledgers and the private requirements of institutional capital. This shift moves the market away from a model of “trust through visibility” toward a model of “trust through mathematical certainty,” where the protocol enforces rules without ever seeing the inputs.
Zero-Knowledge Architectures enable the validation of complex financial states without disclosing the underlying proprietary data.
Within the microstructure of crypto derivatives, Zero-Knowledge Architectures function as a shield against toxic order flow and predatory MEV (Maximal Extractable Value). By obscuring transaction details until settlement, or even post-settlement, these systems prevent adversaries from front-running large options orders or identifying the specific collateral thresholds of market participants. This architectural choice fosters a more resilient market environment where strategic intent remains a private asset rather than a public vulnerability.

Information Asymmetry and Market Integrity
Traditional markets rely on centralized intermediaries to manage the balance between transparency and privacy. Zero-Knowledge Architectures replace these intermediaries with non-interactive proofs. This ensures that even the infrastructure providers ⎊ sequencers, validators, or relayers ⎊ cannot gain an unfair advantage by observing the contents of the mempool.
The integrity of the price discovery process is thus protected by the physics of the protocol itself, rather than the regulatory oversight of a third party.
Computational Integrity in Derivative Engines
The application of Zero-Knowledge Architectures to margin engines allows for the verification of solvency across highly leveraged positions without exposing the specific assets held by a trader. This is achieved through validity proofs that confirm a state transition ⎊ such as a change in account balance after an options premium payment ⎊ adheres to the predefined rules of the smart contract. The result is a system where the risk of insolvency is mathematically mitigated before it can propagate through the network.
Origin
The genesis of Zero-Knowledge Architectures traces back to the 1985 paper by Goldwasser, Micali, and Rackoff, which introduced the concept of interactive proof systems.
These early theoretical models focused on the “knowledge complexity” of a proof, seeking to quantify how much information is leaked during the verification process. While initially an academic pursuit in the field of complexity theory, the rise of decentralized networks provided the first practical environment where such proofs were not a luxury, but a requirement for survival. The transition from theoretical interactive proofs to non-interactive versions (NIZKs) was the catalyst for the current state of Zero-Knowledge Architectures.
This shift allowed for proofs to be generated and verified without a back-and-forth dialogue between parties, making them suitable for the asynchronous nature of blockchain settlement. The launch of Zcash in 2016 marked the first significant implementation of ZK-SNARKs (Succinct Non-Interactive Arguments of Knowledge) in a production environment, proving that financial privacy could be enforced at the protocol level.
| Era | Mechanism | Financial Application |
|---|---|---|
| Theoretical Foundations | Interactive Proofs | Academic Cryptography |
| Early Implementations | ZK-SNARKs (Trusted Setup) | Shielded Asset Transfers |
| Scaling Era | ZK-STARKs (Transparent) | High-Throughput Rollups |
| Programmable Era | zkEVM / zkVM | Private Smart Contracts |
The demand for Zero-Knowledge Architectures intensified as the limitations of Ethereum’s base layer became apparent. The “scalability trilemma” forced a realization that on-chain compute is too expensive for complex derivative calculations. This led to the development of ZK-Rollups, where Zero-Knowledge Architectures are used to compress thousands of transactions into a single proof.
This historical trajectory reflects a move from simple privacy to a comprehensive strategy for global financial scaling.

The Shift toward Succinctness
The evolution of Zero-Knowledge Architectures has been defined by a relentless drive toward reducing the size of the proof and the time required for verification. Early proofs were computationally heavy, making them impractical for mobile devices or low-latency trading. The development of newer polynomial commitment schemes, such as KZG and FRI, has drastically reduced these overheads, allowing Zero-Knowledge Architectures to support the high-frequency demands of modern crypto options markets.

Theory
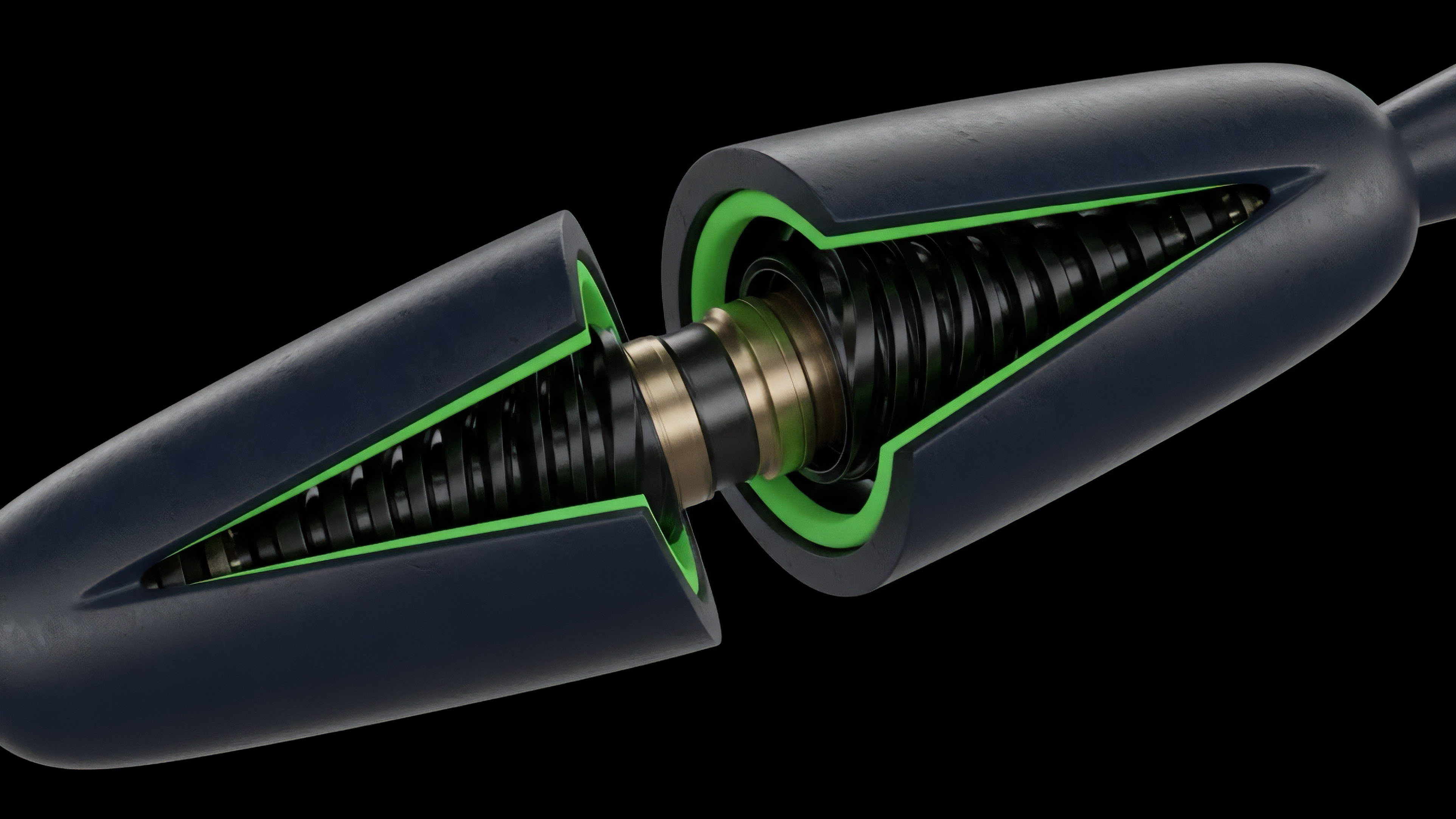
The theoretical framework of Zero-Knowledge Architectures rests on the transformation of computational logic into algebraic polynomials.
This process, known as arithmetization, converts a financial program ⎊ such as a Black-Scholes pricing model or a liquidation check ⎊ into a set of mathematical constraints. If the prover can demonstrate they know a set of values that satisfy these constraints, they provide a validity proof without revealing the values themselves. In Zero-Knowledge Architectures, the distinction between SNARKs and STARKs represents a major theoretical divide.
SNARKs rely on elliptic curve pairings and often require a “trusted setup,” whereas STARKs utilize hash functions and are “transparent,” meaning they require no initial secret generation. STARKs also offer quantum resistance, a vital property for the long-term security of multi-billion dollar derivative protocols.
The mathematical succinctness of a proof allows a single validator to confirm the integrity of an entire market’s state transitions in milliseconds.

Polynomial Commitment Schemes
The strength of Zero-Knowledge Architectures is derived from how they commit to and open polynomials. These schemes allow a prover to “lock” a polynomial and later prove its value at a specific point. This is the foundation of succinctness: the verifier does not need to check the entire computation, only a few random points on the polynomial.
- KZG Commitments provide extremely small proof sizes but require a one-time trusted setup, making them efficient for settlement on constrained layers.
- FRI (Fast Reed-Solomon Interactive Proof of Proximity) enables STARKs to achieve transparency and quantum resistance by using hash-based structures.
- Bulletproofs offer a way to perform range proofs without a trusted setup, frequently used for verifying that a transaction amount is positive without revealing the sum.

The Prover-Verifier Dynamic
The asymmetry between the prover and the verifier is the defining characteristic of Zero-Knowledge Architectures. The prover performs the heavy lifting ⎊ calculating the proof for a complex set of options trades ⎊ while the verifier only needs to perform a light check. This allows the network to scale because the verification cost remains constant or grows logarithmically, even as the complexity of the underlying financial transactions increases.
| Property | ZK-SNARK | ZK-STARK |
|---|---|---|
| Proof Size | Very Small (~288 bytes) | Large (~100 KB) |
| Trusted Setup | Required (usually) | Not Required |
| Quantum Resistance | No | Yes |
| Verification Speed | Constant Time | Logarithmic Time |

Approach
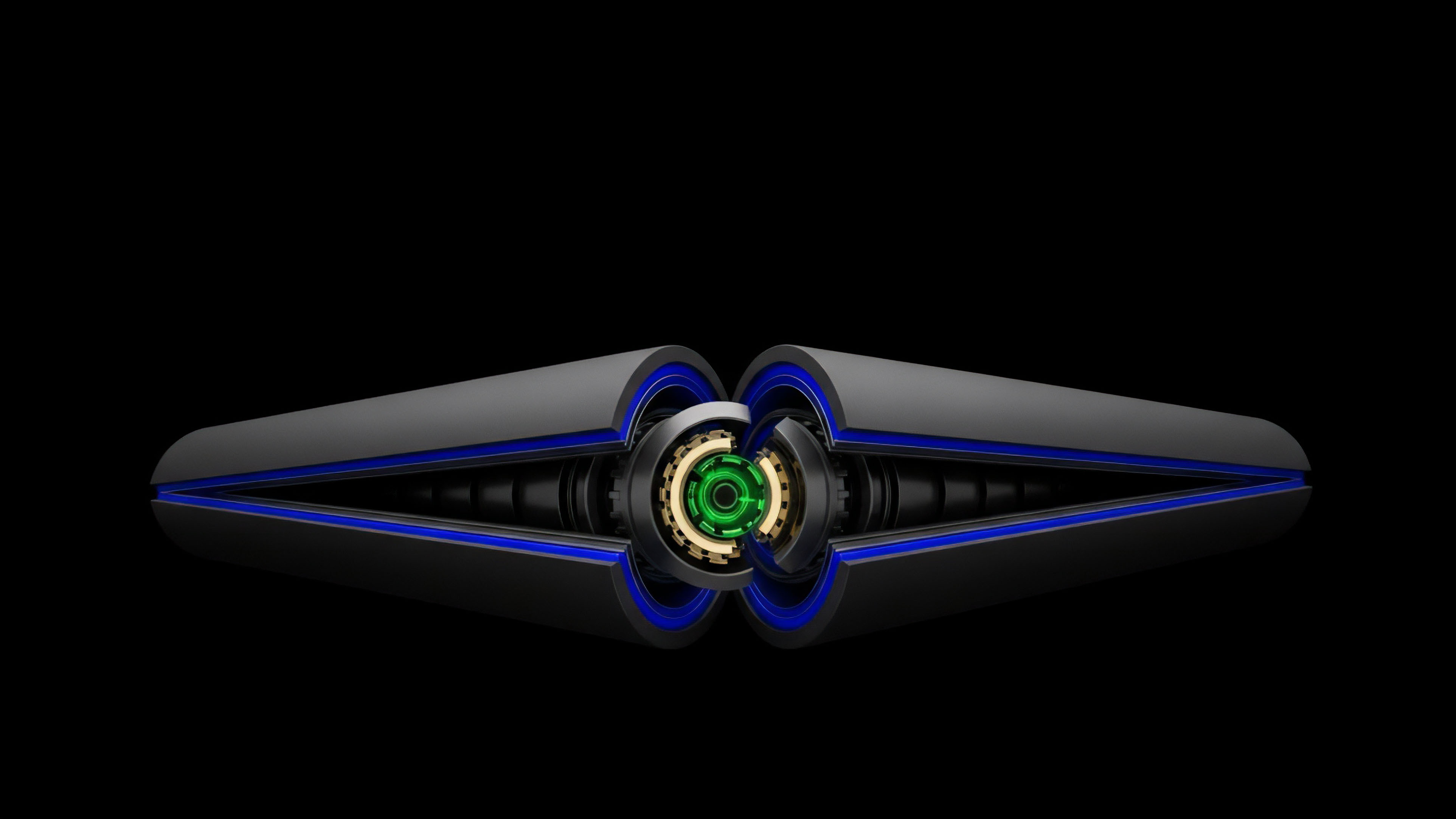
Current implementations of Zero-Knowledge Architectures focus on the deployment of ZK-Rollups and zkEVMs. These systems act as execution layers that sit above the base blockchain, processing transactions off-chain and submitting a validity proof to the main net. This approach allows for the high throughput necessary for decentralized options order books, where thousands of limit orders and cancellations occur every minute.
In the derivative space, Zero-Knowledge Architectures are being used to build “dark pools” for institutional traders. These venues allow for the execution of large block trades without signaling the market. The protocol uses ZK proofs to verify that both parties have the necessary collateral and that the trade adheres to the venue’s rules, but the price and size of the trade are only revealed after the execution is finalized, minimizing market impact.

Validity Proofs Vs Fraud Proofs
The industry is shifting toward validity proofs as the preferred method for securing Layer 2 networks. Unlike optimistic rollups, which assume transactions are valid unless challenged (fraud proofs), Zero-Knowledge Architectures ensure that every state transition is mathematically proven before it is accepted. This eliminates the seven-day withdrawal delay associated with optimistic systems, providing the immediate capital efficiency required by professional options traders.

Custom Circuit Design for Options
Developers are increasingly moving away from general-purpose zkVMs toward application-specific circuits. By designing a circuit specifically for options Greeks ⎊ Delta, Gamma, Theta, Vega ⎊ architects can optimize the prover’s performance. These specialized Zero-Knowledge Architectures reduce the latency between a price move and a margin call, ensuring the system remains solvent during periods of extreme volatility.
- Circuit Optimization involves minimizing the number of gates in the algebraic representation of the financial logic.
- Recursive Proof Aggregation allows multiple proofs to be folded into one, further reducing the gas cost of on-chain verification.
- Data Availability Sampling ensures that the underlying transaction data, while private, is accessible enough to reconstruct the state if the prover fails.

Evolution
The trajectory of Zero-Knowledge Architectures has moved from simple privacy-preserving payments to the creation of fully programmable, private execution environments. Early iterations were rigid and could only support specific transaction types. The emergence of the zkEVM (Zero-Knowledge Ethereum Virtual Machine) represents a massive leap, allowing developers to port existing Solidity-based options protocols into a ZK environment without rewriting the logic from scratch.
Another significant development is the rise of recursive SNARKs. Recursion allows a ZK proof to verify another ZK proof. This creates a “proof of proofs” that can collapse an entire history of transactions into a single, tiny commitment.
For derivative markets, this means a trader can prove their entire trading history and current solvency status to a counterparty or regulator without revealing a single individual trade.

From Privacy to Scalability
While Zero-Knowledge Architectures were born from a desire for anonymity, their primary driver today is scalability. The ability to verify compute off-chain is the only viable path for decentralized derivatives to compete with centralized exchanges like Deribit or Binance. The evolution has seen a shift in focus from the “Zero-Knowledge” property (privacy) to the “Succinctness” property (scaling).
Regulatory-Compliant Anonymity
The narrative is evolving to include “selective disclosure.” Zero-Knowledge Architectures are being designed to allow users to prove they are not on a sanctions list or that they meet “Accredited Investor” criteria without sharing their full identity. This middle ground between total transparency and total anonymity is the key to bringing institutional liquidity into the decentralized options ecosystem.
- Proof of Solvency allows exchanges to prove they hold enough assets to cover all liabilities without revealing their cold wallet addresses.
- Compliance Proofs enable protocols to block users from restricted jurisdictions at the cryptographic level.
- Shielded Pools provide a sanctuary for liquidity providers to hedge their positions without being targeted by MEV bots.

Horizon
The next frontier for Zero-Knowledge Architectures is the integration of ZK-Coprocessors. These are dedicated off-chain environments that handle the heavy computational load of risk management and margin calculations, returning only the proof to the smart contract. This will allow for the creation of sophisticated, real-time risk engines that were previously impossible to run on-chain due to gas constraints.
We are also moving toward a future of “Client-Side Proving,” where the user’s own device generates the ZK proof. This ensures that the user’s private keys and trade data never leave their hardware, providing the highest possible level of security and privacy. In this model, Zero-Knowledge Architectures turn the user’s browser into a private clearinghouse for their own derivative positions.
Future markets will rely on recursive proof structures to collapse entire trading histories into single, verifiable commitments.

ZK-Proofs for AI-Driven Trading
As AI agents become the primary participants in crypto options markets, Zero-Knowledge Architectures will be used to verify the integrity of their models. A trader could use a ZK proof to demonstrate that their AI bot is following a specific, audited strategy without revealing the weights of the neural network. This creates a market for “verifiable intelligence,” where the performance of an algorithm can be trusted without its proprietary logic being stolen.

The End of the Scalability Trilemma
The ultimate destination for Zero-Knowledge Architectures is a world where the distinction between Layer 1 and Layer 2 vanishes. Through the use of recursive proofs, the entire state of a global financial system could be verified by a single smartphone. This represents the final democratization of financial infrastructure, where the power to verify the world’s markets is held by every participant, not just a handful of centralized gatekeepers.

Glossary

Trusted Setup

Proof Aggregation

Qap

Cryptographic Primitives

Cross-Chain Zk

Liquidity Fragmentation

Hashing Algorithms

Poseidon Hash

Data Availability