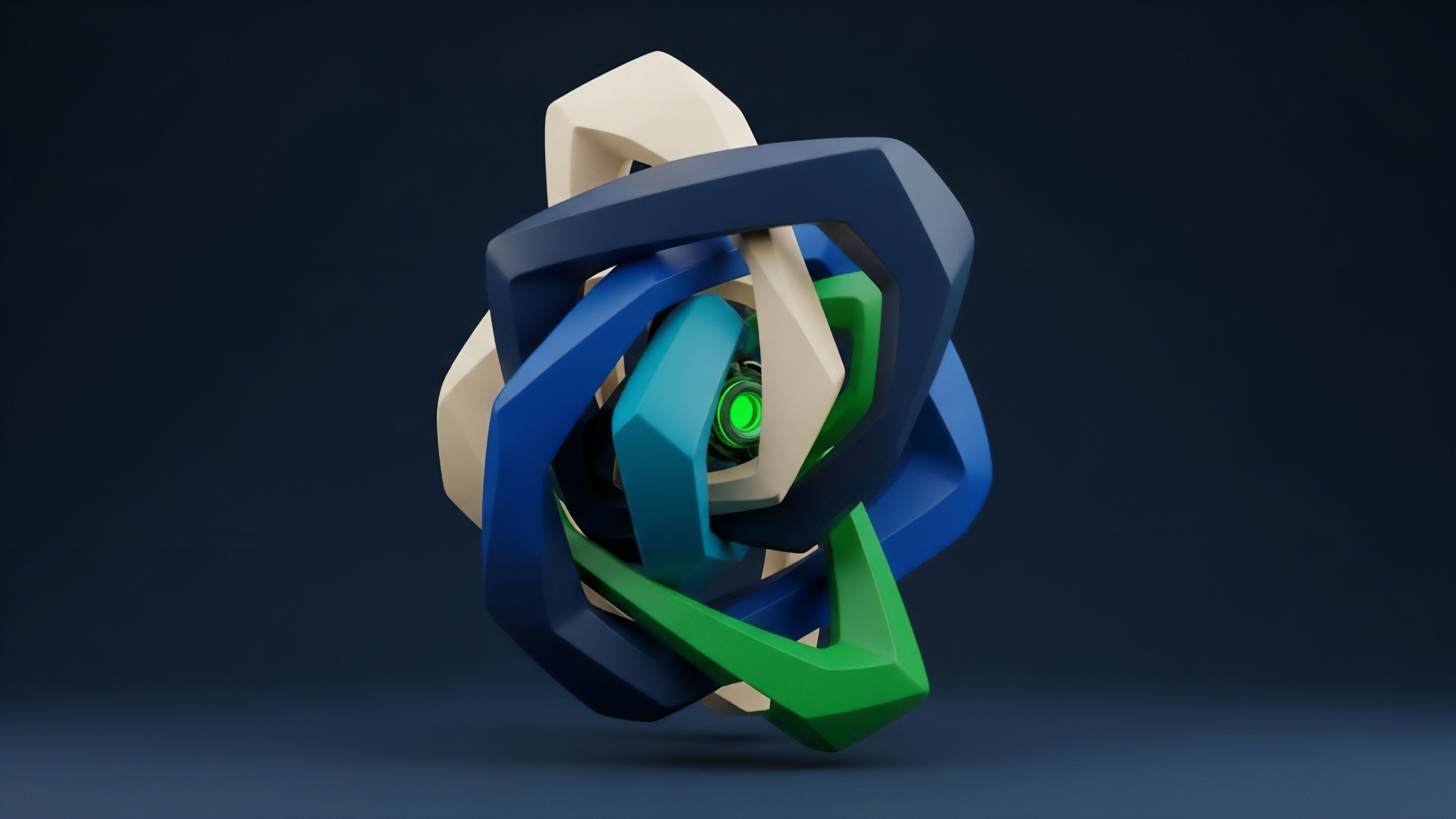
Essence
Trustless computation within the context of crypto derivatives refers to the execution of complex financial logic ⎊ such as options pricing, margin calculations, and automated liquidations ⎊ in a verifiable environment that removes reliance on a centralized clearinghouse or counterparty. This concept extends the fundamental principle of blockchain technology from simple value transfer to the automated, risk-free execution of financial contracts. The core challenge in traditional finance (TradFi) options markets is counterparty risk, where the solvency and integrity of the exchange or clearinghouse are essential to guarantee settlement.
Trustless computation directly addresses this by making the entire process transparent and verifiable on a public ledger, where code acts as the final arbiter. The objective is to achieve a state where a participant can enter into a derivatives contract knowing that the calculation of their profit and loss (P&L), the management of their collateral, and the final settlement will be performed exactly as specified by the smart contract code, without any possibility of external manipulation or discretionary intervention by an operator. This architecture fundamentally shifts the trust model from human institutions to mathematical and cryptographic guarantees.
The design of a robust trustless system for options requires careful consideration of computational complexity, as a full Black-Scholes calculation on a Layer 1 blockchain is prohibitively expensive in terms of gas costs. This necessitates a move toward off-chain computation with on-chain verification, often through zero-knowledge proofs.
Trustless computation transforms the options market by replacing counterparty trust with cryptographic verification, ensuring that complex financial logic executes exactly as coded.

Origin
The genesis of trustless computation in DeFi options stems from the limitations of early smart contracts. The first generation of decentralized applications (dApps) on platforms like Ethereum were designed primarily for basic token swaps and lending, utilizing relatively simple state transitions. However, derivatives, particularly options, require far more sophisticated calculations.
The computational requirements for pricing options ⎊ which involve integrating multiple variables including time decay, volatility, and interest rates ⎊ exceeded the gas limits and computational capacity of Layer 1 blockchains. Early attempts at decentralized options often relied on centralized off-chain components to handle the heavy computational lifting. These designs reintroduced a single point of failure, undermining the “decentralized” claim.
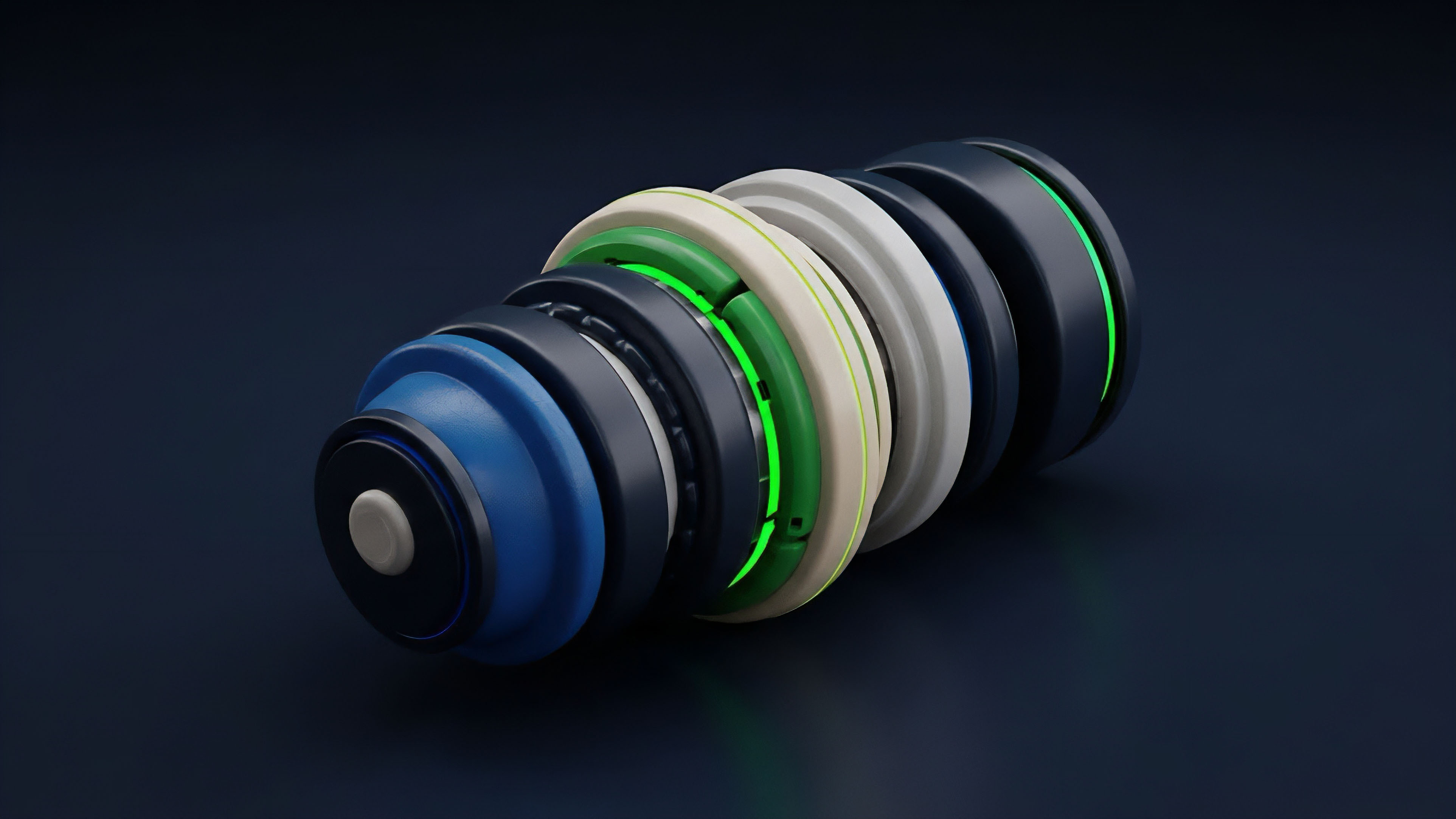
The solution emerged from advances in cryptography, specifically zero-knowledge proofs (ZKPs). ZKPs allow a “prover” to perform a complex calculation off-chain and then generate a cryptographic proof that a “verifier” can check on-chain. This verification process is significantly cheaper than performing the calculation itself on the blockchain.
The development of ZK-rollups and other Layer 2 scaling solutions provided the necessary infrastructure to make this off-chain computation both cost-effective and secure, enabling the creation of complex financial instruments like options with full trustless guarantees.
Theory
The theoretical foundation of trustless options computation rests on the trade-off between computational accuracy and cost. Traditional options pricing models, such as the Black-Scholes model, rely on continuous-time calculations.
Replicating this model on-chain, where calculations are discrete and computationally expensive, requires significant compromises. A key challenge is managing volatility surfaces, which are complex, multi-dimensional inputs required for accurate pricing. The theoretical solution involves moving from on-chain computation to a hybrid model using ZKPs.
The ZK-SNARK (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) protocol is particularly relevant here. A ZK-SNARK allows a protocol to prove that an options calculation was performed correctly without revealing the specific inputs (like proprietary volatility surfaces or a specific user’s portfolio details) to the public chain. This enables both privacy and verifiable execution.
| Model Component | Traditional Finance Approach | Trustless Computation Approach |
|---|---|---|
| Pricing Model | Black-Scholes (continuous-time) or Monte Carlo simulations. | Binomial trees or simplified Black-Scholes approximations, optimized for discrete on-chain verification. |
| Volatility Inputs | Proprietary data feeds and centralized risk engines. | Decentralized oracle networks or on-chain volatility indices derived from market data. |
| Margin Calculation | Centralized clearinghouse calculates risk based on proprietary algorithms. | Smart contract logic calculates margin based on predefined parameters and on-chain collateral. |
The design of the margin engine is equally critical. In a trustless system, margin calculations must be deterministic and verifiable. This means the system must precisely define when and how liquidations occur.
The challenge here is balancing capital efficiency ⎊ allowing users to leverage their collateral ⎊ with system solvency, ensuring that a rapid market movement does not cause a cascade of insolvencies that drain the insurance fund. The mathematical rigor of a trustless margin system must account for worst-case scenarios and be designed to prevent systemic contagion.

Approach
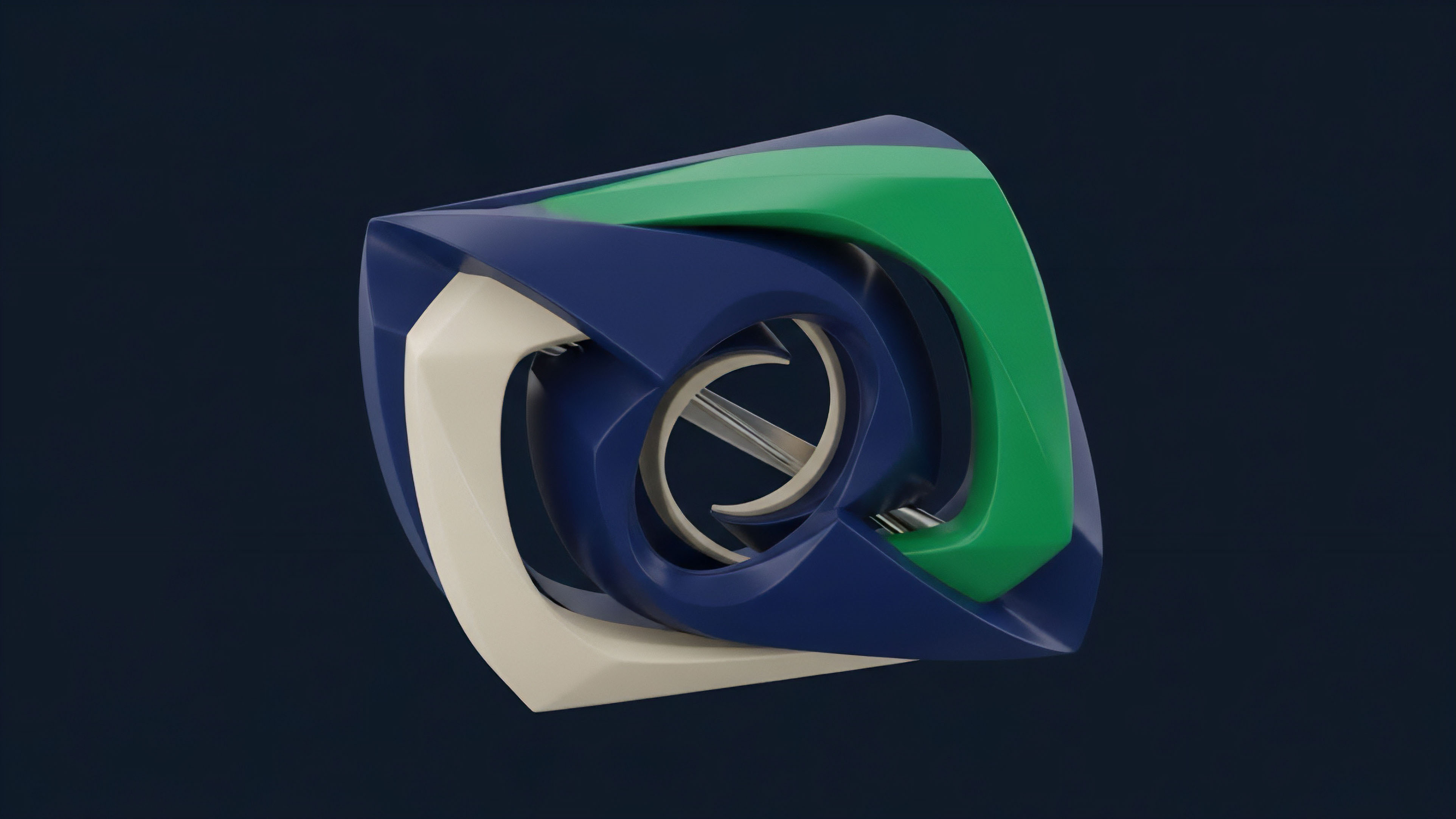
Current implementations of trustless options markets primarily utilize two architectural approaches: decentralized order books and options AMMs (Automated Market Makers).
Both approaches rely heavily on Layer 2 solutions and verifiable computation to scale. A decentralized order book for options mimics a traditional exchange. Market makers submit bids and asks, and the smart contract matches them.
This approach requires high throughput and low latency, making Layer 2 solutions essential. The trustless element here lies in ensuring that the order matching logic, margin checks, and settlement process are all executed on the Layer 2 rollup, with proofs posted to the Layer 1 chain. This architecture requires a robust system for calculating margin requirements for complex portfolios, which can be computationally intensive.
Options AMMs, on the other hand, offer a different approach to liquidity provision. They use a pool of collateral and an algorithm to price options dynamically based on supply and demand within the pool. This simplifies the user experience by removing the need for an order book, but introduces a different set of risks.
The pricing algorithm itself must be trustless and resistant to manipulation. This approach often uses ZKPs to verify the complex pricing calculations off-chain, ensuring that the AMM’s pricing curve accurately reflects market conditions and avoids front-running or arbitrage opportunities.
| Feature | Decentralized Order Book (e.g. Lyra, Opyn) | Options AMM (e.g. Hegic, Dopex) |
|---|---|---|
| Liquidity Provision | Requires market makers to actively manage bids and asks. | Liquidity providers deposit collateral into a pool; algorithm prices options. |
| Risk Model | Margin-based; individual portfolio risk management. | Pool-based; shared risk and capital efficiency. |
| Pricing Method | Price discovery via order matching. | Algorithmic pricing based on utilization and volatility parameters. |
| Execution Speed | Requires high-speed Layer 2 environment. | Can be slower, with a focus on pool health over individual trade speed. |
Both models face the challenge of accurately reflecting real-time market volatility. Oracles play a significant role here, providing external data feeds to the trustless system. The security of the oracle network is paramount, as a compromised oracle could feed false volatility data, leading to mispricing and potential systemic failure of the options protocol.

Evolution
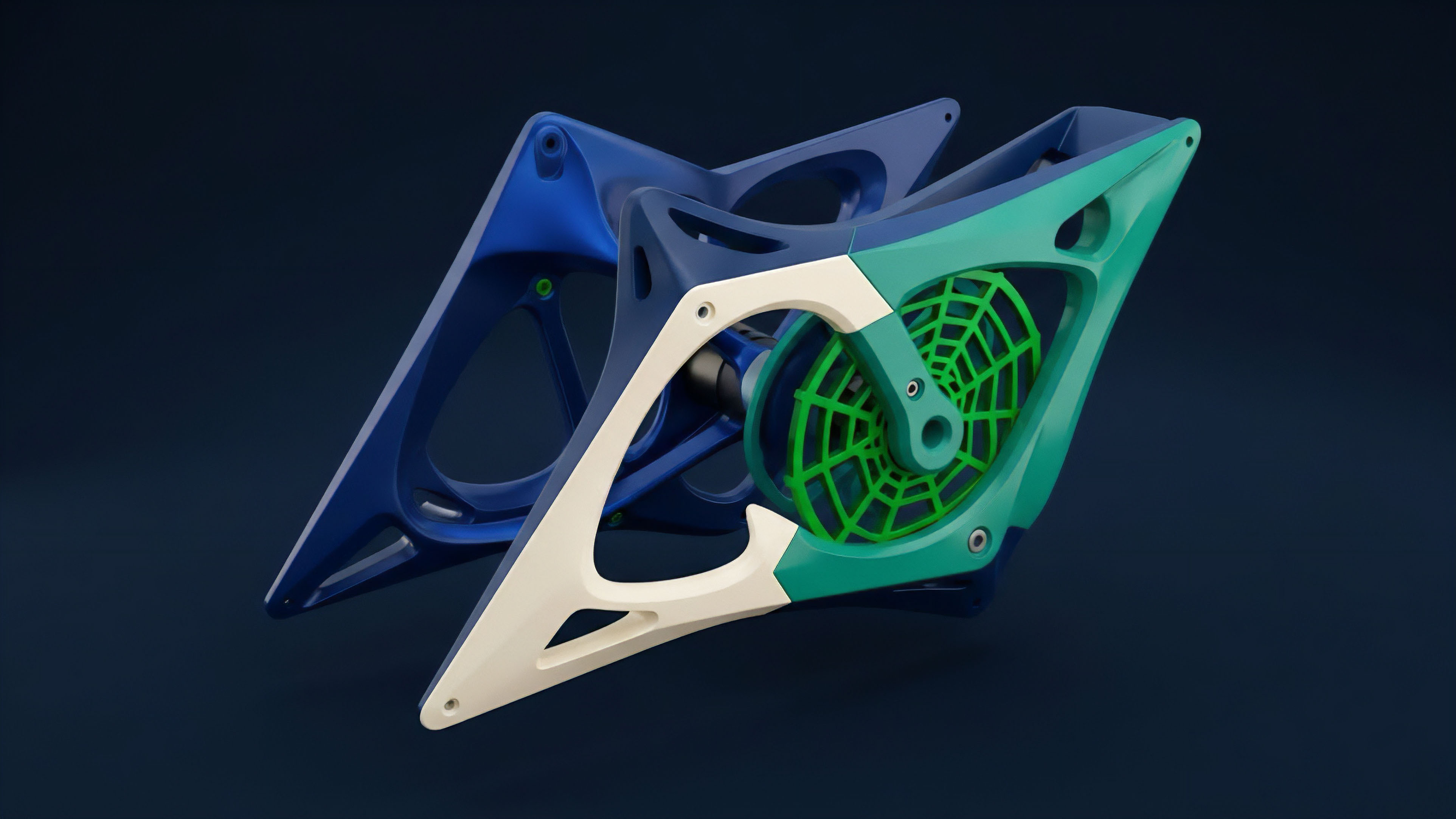
The evolution of trustless computation in derivatives markets reflects a progression from simple, single-asset options to more complex structured products and exotic derivatives. Initially, protocols focused on basic European options, where settlement occurs only at expiration. This simplicity reduced the computational load and risk management complexity.
However, the true utility of trustless computation emerges with more complex instruments. The shift to American options, which allow early exercise, requires continuous monitoring of the option’s intrinsic value. This necessitates a more sophisticated margin engine capable of performing real-time calculations.
The ability to trustlessly verify these continuous calculations is a major architectural hurdle.
The development of Layer 2 solutions and ZKPs allows for the creation of exotic options and structured products that were previously impossible to implement in a fully decentralized manner.
We are now seeing the rise of structured products, where options are combined with other financial instruments to create tailored risk profiles. For example, a “yield vault” might sell options to generate income, with the trustless computation verifying that the premiums are correctly calculated and distributed to depositors. This level of complexity requires a robust framework for composability, where different trustless financial primitives can interact seamlessly without introducing new security vulnerabilities. The next step involves integrating trustless computation with advanced risk management techniques like portfolio margining, where the overall risk of a portfolio (including multiple assets and derivatives) is calculated rather than just individual positions.
Horizon
The horizon for trustless computation points toward a future where derivatives markets are not just decentralized, but fully verifiable global risk engines. The next generation of protocols will move beyond simply verifying options calculations to creating fully synthetic assets and structured products that replicate real-world financial instruments. This requires a new level of integration between off-chain data feeds and on-chain logic. One significant development on the horizon is the use of fully homomorphic encryption (FHE) in combination with ZKPs. FHE allows computations to be performed on encrypted data without decrypting it first. While still in early research phases, FHE could enable a level of privacy in derivatives trading that is currently impossible. A trader could execute a complex options strategy without revealing their position or collateral to the public blockchain, while still providing a cryptographic guarantee that the calculation and settlement logic are sound. The ultimate goal is to create a fully permissionless financial system where any participant can create, trade, and settle any derivative instrument without relying on a central authority. This requires a robust, scalable infrastructure where computation costs are near zero, and verification is instantaneous. The regulatory landscape will inevitably converge on these trustless systems. As traditional financial institutions look to integrate blockchain technology, they will be forced to confront the implications of verifiable computation and its ability to disintermediate traditional clearinghouses. The architectural choices we make now will determine whether this future system is resilient and fair, or whether it simply replicates existing systemic risks in a new, more opaque form.

Glossary

Trustless Settlement Logic
Quantitative Finance

Trustless Margin Management

Bounded Computation
Trustless Settlement

Decentralized Computation
Trustless Asset Transfer

Trustless Financial Stack

Trustless Derivatives