Essence
The mechanism of staking and slashing serves as the foundational economic primitive for Proof-of-Stake (PoS) consensus systems, creating a framework where capital acts as a commitment to network integrity. Staking is the act of locking a native protocol asset to participate in validation, thereby earning rewards. Slashing is the corresponding disincentive mechanism, where a portion of the staked assets is programmatically destroyed if the validator acts maliciously or demonstrates gross negligence.
This duality forms the core security model of a PoS network. The staked asset itself transforms into a form of collateralized bond, where the validator’s capital is placed at risk against the integrity of their actions. This capital commitment provides economic finality to the state transitions proposed by validators.
The introduction of staking fundamentally alters the risk profile of holding the underlying asset. A staked asset carries a different risk vector than an unstaked asset; it is subject to specific smart contract risks and operational risks associated with validation. The value accrual mechanism of staking rewards creates a natural yield on the underlying asset, which in turn influences market microstructure.
This yield becomes the baseline risk-free rate for the decentralized finance ecosystem built upon that chain. The opportunity cost of not staking is the yield foregone, a critical consideration for capital allocation.
Staking and slashing are two sides of a single mechanism that transforms native protocol assets into collateral for network security, establishing a baseline yield and altering the asset’s risk profile.

The Economic Commitment
A validator’s decision to stake represents a calculation of risk versus reward, where the expected value of future rewards must outweigh the potential cost of being slashed. This cost includes both the direct penalty and the loss of future rewards. The protocol’s design must ensure that the economic cost of an attack (the total amount of collateral at risk) exceeds the potential gain from a successful attack.
This principle, known as economic security, is paramount in PoS design. The specific parameters of slashing ⎊ the severity of penalties for different offenses ⎊ are carefully calibrated to create a robust deterrent against rational actors attempting to compromise the network. The slashing mechanism effectively hardens the protocol against certain classes of attacks, particularly those involving double-spending or proposing invalid blocks.

Origin
The concept of staking first emerged as a response to the inherent energy consumption and centralization risks associated with Proof-of-Work (PoW) systems. Early implementations, such as Peercoin in 2012, introduced a form of PoS where coin age determined staking weight, attempting to achieve consensus without the intensive computational requirements of mining. This early model, however, lacked a robust penalty mechanism and proved susceptible to “nothing at stake” attacks, where validators could safely vote on multiple competing chain histories without consequence.
The critical evolution occurred with the development of formal BFT (Byzantine Fault Tolerance) consensus models adapted for PoS. The breakthrough came with the realization that to solve the nothing-at-stake problem, a financial cost had to be imposed on malicious behavior. This led to the creation of the slashing mechanism.
The development of protocols like Tendermint and later Ethereum’s transition to PoS solidified slashing as an essential component of PoS security. The design principle shifted from simply rewarding good behavior to actively punishing bad behavior, thereby aligning economic incentives with network integrity. The transition of major networks to PoS, particularly Ethereum, demonstrated the market’s acceptance of this model as a viable alternative to PoW.

Historical Challenges and Solutions
The initial attempts at PoS faced a significant challenge in ensuring finality and preventing network splits. Without the computational cost of PoW to deter re-orgs, a validator could easily vote on multiple chains. The introduction of slashing, particularly for “double-signing” (voting for two conflicting blocks at the same height), provided the necessary economic deterrent.
This mechanism ensures that a validator faces a direct financial loss for attempting to undermine consensus, making a coordinated attack prohibitively expensive. The severity of the slashing penalty is calibrated based on the perceived severity of the offense.
| PoS Consensus Model | Primary Incentive Mechanism | Primary Slashing Trigger | Risk Profile for Staker |
|---|---|---|---|
| Early PoS (e.g. Peercoin) | Coin Age and Staking Rewards | None (High Nothing-at-Stake Risk) | Low (No penalty for malicious behavior) |
| BFT-based PoS (e.g. Cosmos, Avalanche) | Validation Rewards | Double Signing, Validator Downtime | Moderate (Collateral at risk for specific offenses) |
| Ethereum PoS (Beacon Chain) | Validation Rewards, MEV | Double Signing, Inactivity Leaks | High (Collateral at risk for specific offenses and inactivity) |

Theory
The theory underpinning staking and slashing is rooted in mechanism design and behavioral game theory. The core problem is to design a system where rational, self-interested participants will collectively choose to act honestly to maximize their individual gain. Slashing serves as the penalty function in this game, ensuring that the expected utility of attacking the network is negative.

Game Theory of Slashing
The effectiveness of slashing depends on the assumption that validators are rational actors. The protocol sets up a game where the payoff matrix for a validator is determined by:
- Honest Behavior: Receive staking rewards.
- Malicious Behavior: Potential gain from the attack (e.g. double-spend, front-running) minus the cost of slashing.
For the system to be secure, the cost of slashing must always be greater than the potential gain from any attack. The cost of a successful attack, where a malicious actor controls 51% of the staked assets, is the sum of all slashed assets. The total economic security of the network is therefore directly proportional to the total value staked.
This model ensures that a coordinated attack requires a significant capital investment that is put at risk.

Risk Modeling and Collateralization
From a quantitative finance perspective, staking introduces a new layer of risk for the asset holder. The staked asset becomes a form of collateral that generates yield but also carries specific operational and smart contract risks. The risk modeling for a validator involves calculating the probability of a slashing event.
The primary risks include:
- Downtime Slashing: A penalty for failing to attest to the network state. This risk is primarily operational and depends on the validator’s infrastructure reliability.
- Equivocation Slashing: A severe penalty for signing conflicting messages. This risk is primarily related to malicious intent or a critical software bug.
- Opportunity Cost: The loss of liquidity and potential yield from other decentralized finance protocols.
The collateralization ratio of the network (total value staked versus total value locked in the ecosystem) determines the robustness of the system. A high collateralization ratio ensures that a significant portion of the asset’s supply is committed to security, increasing the cost of attack. The “Derivative Systems Architect” persona understands that this collateralization ratio is a key metric for systemic risk.

Approach
The implementation of staking and slashing varies significantly across different protocols, primarily due to differing consensus algorithms and governance models. Ethereum’s PoS model utilizes a system where validators propose blocks and attest to the validity of other blocks, with slashing penalties tied to both downtime and malicious actions. Cosmos-based chains, which use the Tendermint consensus, implement slashing for specific offenses like double-signing and extended periods of downtime.
The approach to slashing must be tailored to the specific protocol’s requirements for finality and security.
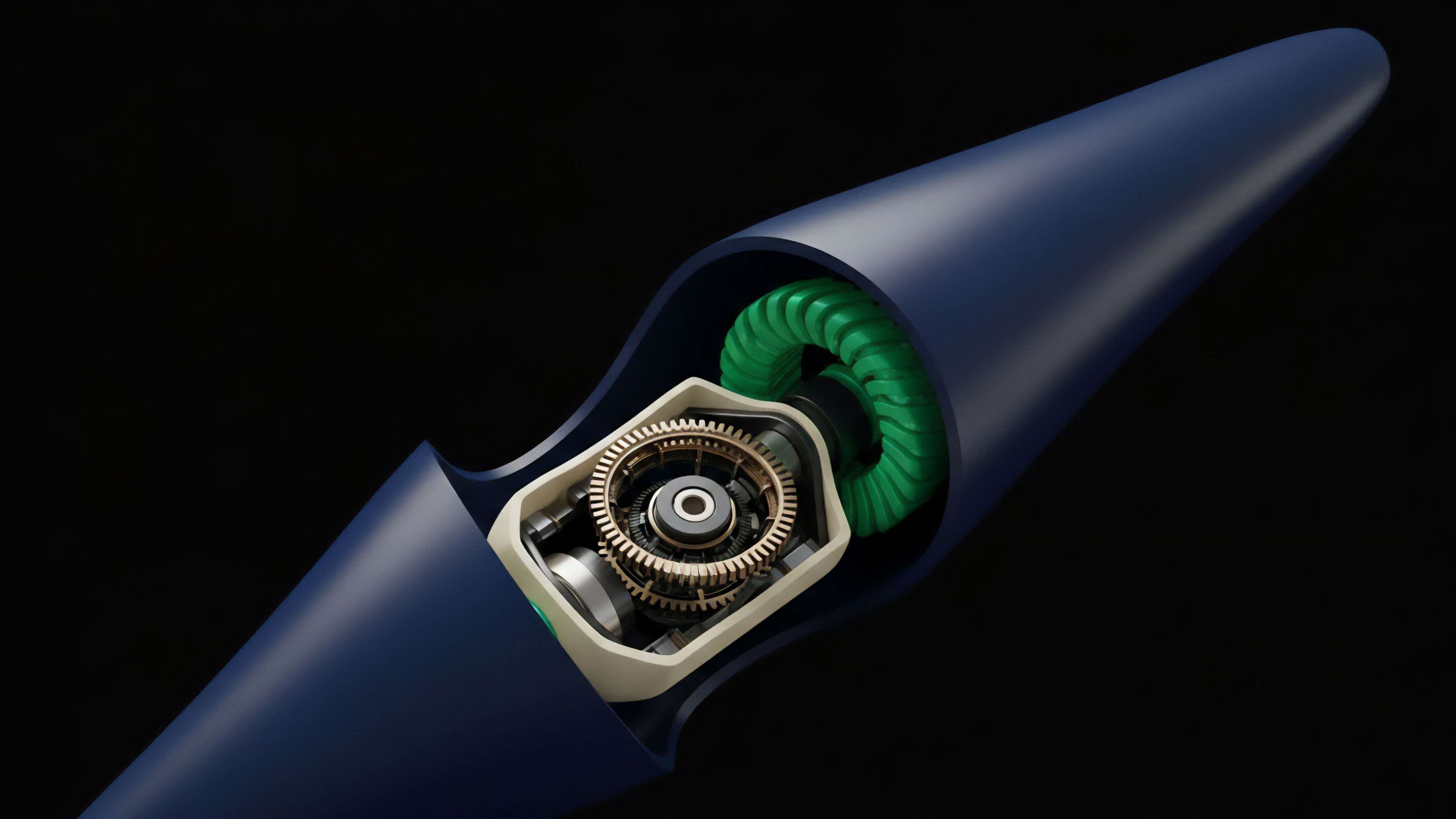
Delegation Models and Liquidity Staking
The need for a high capital threshold to run a validator node led to the development of delegation models. In delegated PoS (DPoS), individual stakers delegate their assets to a professional validator, sharing the rewards and risks. This introduces a new layer of agency risk, where the delegator relies on the validator’s operational integrity to avoid slashing.
The emergence of liquid staking derivatives (LSDs) like Lido and Rocket Pool provides a solution to the liquidity problem inherent in staking.
Liquid staking derivatives (LSDs) address the opportunity cost of staking by tokenizing the staked asset, allowing stakers to retain liquidity and participate in other financial activities while earning staking rewards.
LSDs represent a tokenized claim on the underlying staked asset plus accrued rewards. The mechanism works by allowing users to stake assets with a protocol and receive a derivative token in return. This derivative token can then be used in other decentralized finance protocols, effectively allowing the staker to earn both staking rewards and yield from lending or providing liquidity.
This innovation fundamentally changes the capital efficiency calculation for stakers, transforming a illiquid asset into a liquid one.
Operational Risks and MEV Extraction
The operational reality of staking involves managing infrastructure, monitoring network conditions, and ensuring high uptime. The slashing mechanism places a premium on operational excellence. Validators must implement redundant systems and carefully manage their key signing processes to avoid accidental slashing.
Additionally, the rise of Maximal Extractable Value (MEV) introduces a new dynamic. Validators can maximize their returns by strategically ordering transactions within blocks. This creates a complex incentive structure where validators are incentivized to engage in sophisticated strategies to capture MEV, which can lead to further centralization risks if not properly managed.

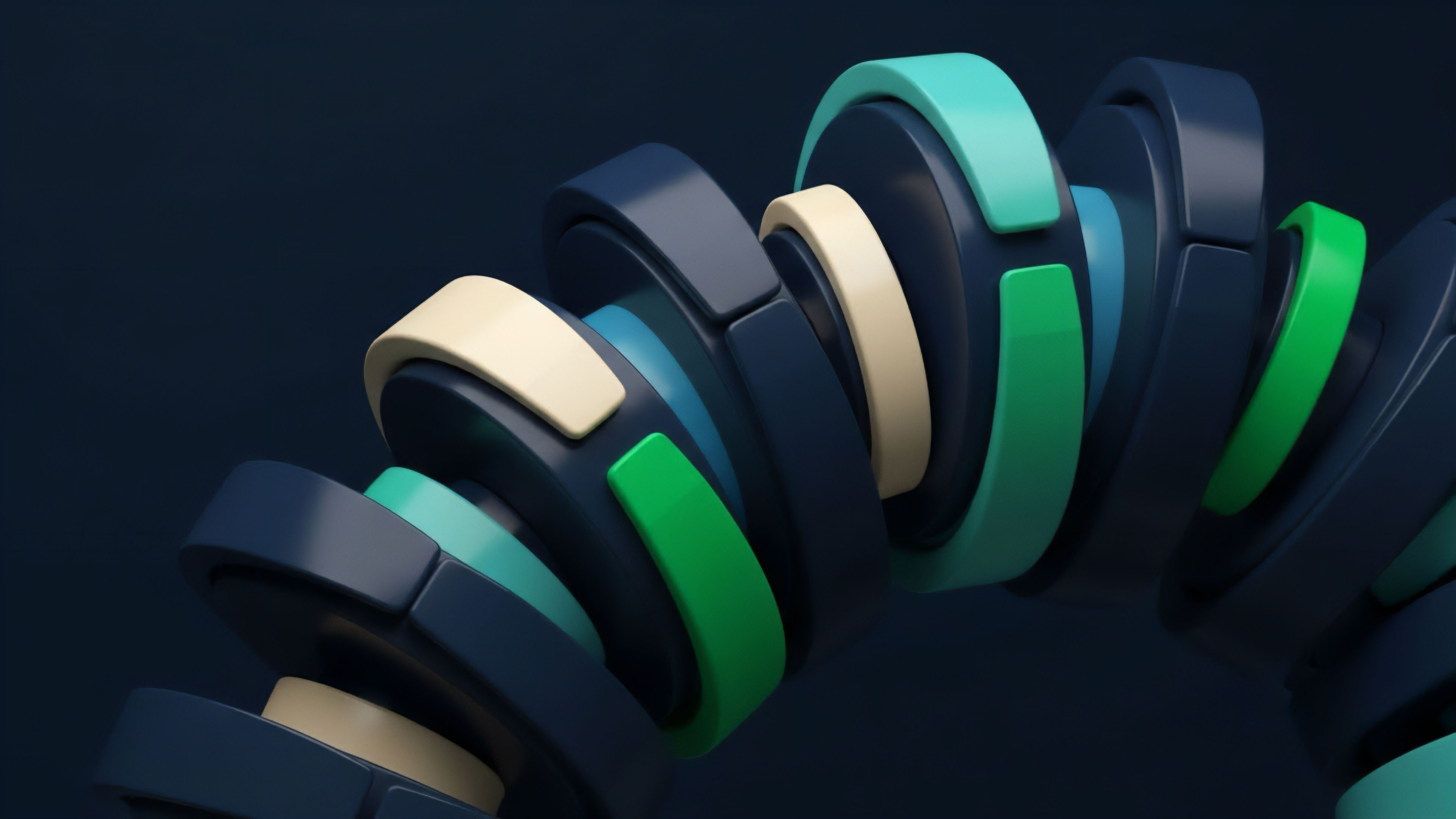
Evolution
The evolution of staking has moved rapidly from simple asset locking to a sophisticated financial ecosystem centered around derivatives. The development of liquid staking derivatives (LSDs) created the first major financial primitive built on top of the staking mechanism. LSDs allow stakers to maintain liquidity, effectively turning a yield-bearing asset into a collateralizable asset.
This innovation significantly increased the capital efficiency of PoS networks and accelerated the growth of decentralized finance by creating new yield opportunities. The most recent development in this space is restaking, pioneered by protocols like EigenLayer. Restaking allows stakers to reuse their staked collateral from one protocol (e.g.
Ethereum) to secure other decentralized applications (AVSs, or Actively Validated Services). This creates a powerful mechanism for shared security. However, it also introduces a new layer of systemic risk.
The collateral is now securing multiple protocols simultaneously, meaning a slashing event on one AVS could trigger cascading liquidations across multiple systems. This creates a complex web of interconnected risk where the failure of one small protocol could have broader implications for the entire ecosystem.
Restaking and Systemic Risk
Restaking fundamentally changes the risk-reward calculation for stakers. Stakers receive additional yield for securing AVSs, but they take on new slashing risks specific to those AVSs. The core challenge lies in quantifying this new risk.
The total value locked in restaking represents a potential point of contagion. If a critical AVS fails or is exploited, the resulting slashing could lead to significant sell pressure on the underlying asset. The “Derivative Systems Architect” persona views this as a complex system where the interdependencies must be carefully modeled.
| Staking Model | Capital Efficiency | Slashing Risk Profile | Liquidity Status |
|---|---|---|---|
| Direct Staking | Low (Illiquid Asset) | Protocol-specific risks (downtime, equivocation) | Illiquid (Locked) |
| Liquid Staking Derivatives (LSDs) | High (Liquid Asset) | Protocol-specific risks, plus smart contract risk of the LSD protocol | Liquid (Tokenized) |
| Restaking (e.g. EigenLayer) | Very High (Reused Collateral) | Protocol-specific risks, plus AVS-specific risks, high contagion risk | Liquid (Tokenized) |
Horizon
The future of staking and slashing will likely be defined by the further financialization of staked assets and the development of more complex derivatives. We can expect the emergence of options and futures markets specifically tailored to restaked assets and their associated risks. These new financial instruments will allow market participants to hedge against specific slashing risks or speculate on the yield generated by AVSs.

Slashing Risk Derivatives
The inherent volatility and specific nature of slashing events create an opportunity for a new class of financial derivatives. Stakers will seek ways to hedge against the risk of downtime or equivocation slashing. This could lead to the creation of insurance protocols or options contracts where stakers can pay a premium to protect their collateral.
Conversely, speculators could purchase options that pay out in the event of a slashing incident, essentially betting against the operational integrity of a validator set. This development would create a liquid market for operational risk, allowing for more precise pricing of network security.

The Regulatory Challenge
As staking mechanisms evolve into complex financial structures, the regulatory landscape will become increasingly critical. The classification of LSDs and restaking derivatives presents a challenge for regulators. Are these considered securities?
The yield generated by staking and the pooling of assets in protocols like Lido could lead to stricter regulatory oversight. The “Derivative Systems Architect” persona must consider how these regulatory decisions will shape the future architecture of decentralized finance. The implementation of specific regulatory frameworks will determine whether these new instruments can achieve mainstream adoption and whether they will be confined to specific jurisdictions.
The future financialization of staking collateral through derivatives will create new mechanisms for risk transfer, but it also introduces complex regulatory challenges regarding the classification of these instruments.
The ultimate goal for the next generation of PoS systems is to create a highly efficient market for security where the cost of capital is minimized, while the cost of attack remains prohibitively high. This involves optimizing the slashing mechanism to be precise and efficient, ensuring that only malicious actors are penalized, and minimizing the impact on honest participants. The future of staking is a continuous refinement of the economic game theory, pushing toward a more robust and efficient decentralized security model.

Glossary

Staking Slash Mechanisms

Liquidity Staking Derivatives

Single Staking Option Vault
Slashing Severity
Staking Slashing Mechanism

Slashing Mechanism
Validator Collateralization
Blockchain Consensus Mechanisms and Scalability
Staking Tokens