Essence
Code execution without verifiable source mapping represents a systemic blind spot in decentralized derivative markets. Smart Contract Verification functions as the cryptographic attestation that the high-level logic authored by developers matches the hexadecimal bytecode residing on a blockchain. This process eliminates the opacity inherent in compiled machine instructions, allowing market participants to audit the risk parameters, liquidation thresholds, and settlement logic of a protocol before committing capital.
In a landscape where code serves as the final arbiter of value, the ability to verify that “what you see is what you execute” becomes the basal requirement for institutional trust.
Verification establishes the requisite transparency for institutional capital to engage with permissionless liquidity pools.
The primary mechanism involves a deterministic comparison between a re-compiled source and the on-chain artifact. When a developer submits their Solidity or Vyper files to a verification service, the system replicates the original compilation environment, including the specific compiler version and optimization settings. If the resulting bytecode matches the deployed version exactly, the contract is marked as verified.
This transparency is vital for complex financial instruments, such as synthetic options or decentralized margin engines, where a single hidden opcode could deviate from the intended risk model.

Systemic Trust and Mathematical Proof
The shift toward Smart Contract Verification represents a move away from reputation-based trust toward mathematical certainty. Market makers and liquidity providers utilize these verified sources to construct high-fidelity simulations of protocol behavior under stress. Without this visibility, the internal state transitions of a derivative contract remain a “black box,” introducing unquantifiable tail risks.
By exposing the underlying logic, verification enables a more robust form of financial engineering where the adversarial nature of the environment is countered by the immutability and transparency of the proven code.

Origin
The necessity for verifying on-chain logic surfaced during the early expansion of the Ethereum network, specifically as decentralized applications began managing significant volumes of user assets. Initially, interacting with a contract required a leap of faith that the provided documentation aligned with the deployed bytecode. The 2016 DAO event underscored the reality that even minor discrepancies in logical flow can lead to catastrophic capital loss.
This spurred the development of block explorers like Etherscan to provide a public interface for source code submission and comparison.

Transition from Manual Audit to Automated Attestation
Early verification was a manual, fragmented process. Developers often neglected to publish their source code, or they provided versions that failed to account for constructor arguments or library links. As the complexity of decentralized finance grew, the industry transitioned toward automated attestation.
The introduction of the Sourcify initiative and the integration of metadata hashes directly into the contract bytecode provided a more decentralized path for verification. This allowed for “full” verification, where the metadata hash points to the exact source files and compiler settings on decentralized storage networks like IPFS.

Regulatory and Institutional Drivers
As traditional finance entities began examining blockchain-based settlement, the demand for rigorous verification standards intensified. Regulatory bodies in various jurisdictions started to view unverified contracts as a compliance failure, akin to executing a legal contract written in an indecipherable language. This pressure transformed Smart Contract Verification from a developer’s courtesy into a mandatory standard for any protocol seeking broad market adoption and professional liquidity.

Theory
The theoretical framework of Smart Contract Verification rests on the principles of deterministic compilation and formal methods.
A compiler must be viewed as a pure function: given the same input and environment, it must produce the identical output. Any deviation, whether from a different compiler version or a subtle change in optimization flags, results in a different bytecode hash, breaking the verification chain. This precision is what allows for the creation of a “source of truth” that links the human-readable intent to the machine-executable reality.
Formal proofs transform smart contract security from a probabilistic guessing game into a deterministic mathematical certainty.

Formal Verification and Symbolic Execution
Beyond simple bytecode matching, advanced verification involves Formal Verification. This methodology uses mathematical proofs to ensure that a contract adheres to specific invariants. Instead of testing for known bugs, formal verification examines every possible state transition to prove that certain conditions ⎊ such as “total supply never exceeds a fixed cap” ⎊ can never be violated.
| Methodology | Primary Mechanism | Security Assurance |
|---|---|---|
| Bytecode Matching | Deterministic Re-compilation | Verifies source matches deployed code |
| Static Analysis | Pattern Recognition | Identifies known vulnerability patterns |
| Symbolic Execution | Mathematical Path Exploration | Tests logical branches for edge cases |
| Formal Verification | Mathematical Proofs | Guarantees adherence to defined invariants |

The Compilation Pipeline
The compilation process translates high-level Solidity into Ethereum Virtual Machine (EVM) opcodes. During this phase, the compiler generates a metadata file containing the settings used. Modern verification tools leverage this metadata to recreate the exact environment.
A failure to match often stems from the Constructor Arguments, which are appended to the bytecode at deployment and must be correctly identified to achieve a successful match. This technical rigor ensures that even the initialization parameters of a derivative contract are transparent to the public. In the context of quantitative finance, the verification of the Margin Engine logic is particularly significant.
If the liquidation formula is not verified, a trader cannot be certain of their bankruptcy price. The mathematical integrity of the system relies on the fact that the code governing the collateral-to-debt ratio is exactly what the user agreed to when opening a position. This level of scrutiny is what separates decentralized derivatives from their legacy counterparts, where internal risk models are often proprietary and opaque.

Approach
Current methodologies for Smart Contract Verification emphasize a multi-layered strategy to ensure absolute logical transparency.
Developers utilize specialized plugins within their development environments, such as Hardhat or Foundry, to automate the submission of source code to block explorers and decentralized repositories. This workflow ensures that verification occurs simultaneously with deployment, preventing any window of opacity where the contract is active but unverified.

Requirements for Full Source Verification
- Compiler Settings: The exact version of the compiler and the number of optimization runs must be specified to ensure bytecode parity.
- Dependency Resolution: All imported libraries and external interfaces must be provided in a flattened format or through a structured JSON input.
- Constructor Arguments: The specific values passed to the contract during the deployment transaction must be encoded in the correct ABI format.
- Metadata Linking: The inclusion of the IPFS or Swarm hash in the bytecode allows for the retrieval of the original source without relying on centralized databases.
Comparative Analysis of Storage Methods
| Storage Type | Accessibility | Decentralization Level |
|---|---|---|
| Block Explorer (Etherscan) | High | Low (Centralized) |
| Decentralized Repository (Sourcify) | Medium | High (IPFS/Swarm) |
| On-chain Source Storage | Low | Maximum (Directly on-chain) |

Verification of Proxy and Upgradeable Patterns
The rise of upgradeable contracts introduces a layer of complexity. Verification must be performed for both the Proxy Contract and the Implementation Contract. The proxy handles the state and storage, while the implementation contains the logic.
A verified proxy alone is insufficient, as it does not reveal the actual financial logic being executed. Strategists must verify that the implementation address stored in the proxy points to a verified contract, ensuring that the entire execution path is visible and audited.
Evolution
The progression of Smart Contract Verification has moved from a reactive, manual task to a proactive, integrated component of the development lifecycle. In the early days, verification was often an afterthought, leading to “ghost contracts” that managed millions in assets with no public source code.
Today, the industry treats unverified code as a critical risk signal. This shift mirrors the evolution of aviation safety, where every component must not only function but also have a documented, verifiable history of its design and testing.
On-chain bytecode verification serves as the final defense against malicious compiler injections and supply chain attacks.
From Static to Dynamic Verification
Modern tools have moved beyond simple source-to-bytecode matching. We now see the rise of Runtime Verification and automated fuzzing. These techniques monitor the contract’s behavior in a simulated environment that mirrors the mainnet state.
By bombarding the verified code with millions of random inputs, these systems can identify edge cases that even a formal proof might miss if the initial assumptions were flawed. This dynamic approach provides a continuous layer of security that evolves as the market conditions change.

Risks of Unverified Bytecode
- Hidden Backdoors: Malicious developers can include functions that allow for the unauthorized withdrawal of user funds.
- Logical Discrepancies: Small errors in the implementation of mathematical formulas can lead to incorrect pricing or liquidation.
- Compiler Exploits: A compromised compiler could inject malicious opcodes that are not present in the original source code.
- Lack of Composability: Other protocols cannot safely integrate with an unverified contract, as they cannot programmatically confirm its behavior.

Horizon
The future of Smart Contract Verification lies in the integration of Zero-Knowledge proofs and compiler-level guarantees. We are moving toward a state where the compiler itself generates a proof of its own correctness. This would mean that every piece of bytecode deployed on a network comes with a cryptographic attestation that it was produced faithfully from a specific source, eliminating the need for third-party verification services.
This “proof of compilation” will become a standard feature of next-generation ZK-EVMs.

Real-Time Verification and Monitoring
As the speed of decentralized markets increases, the window for auditing code narrows. We project the emergence of real-time verification engines that sit between the user and the blockchain. These engines will provide a “safety score” based on the verified logic and current state of the contract, warning users if a transaction would trigger a suspicious logical path.
This proactive defense will be vital for protecting retail participants from increasingly sophisticated exploits.

Regulatory Mandates and Verified-Only Zones
It is highly probable that we will see the emergence of “Verified-Only” execution environments. In these sub-networks, the protocol rules will strictly forbid the deployment or interaction with any contract that does not have a verified source and a corresponding formal proof. This would create a “walled garden” of mathematical certainty, suitable for large-scale institutional settlement and high-value derivative transactions. This transition will mark the final maturation of decentralized finance, where the volatility of human error is replaced by the stability of proven code.

Glossary

Evm Opcodes

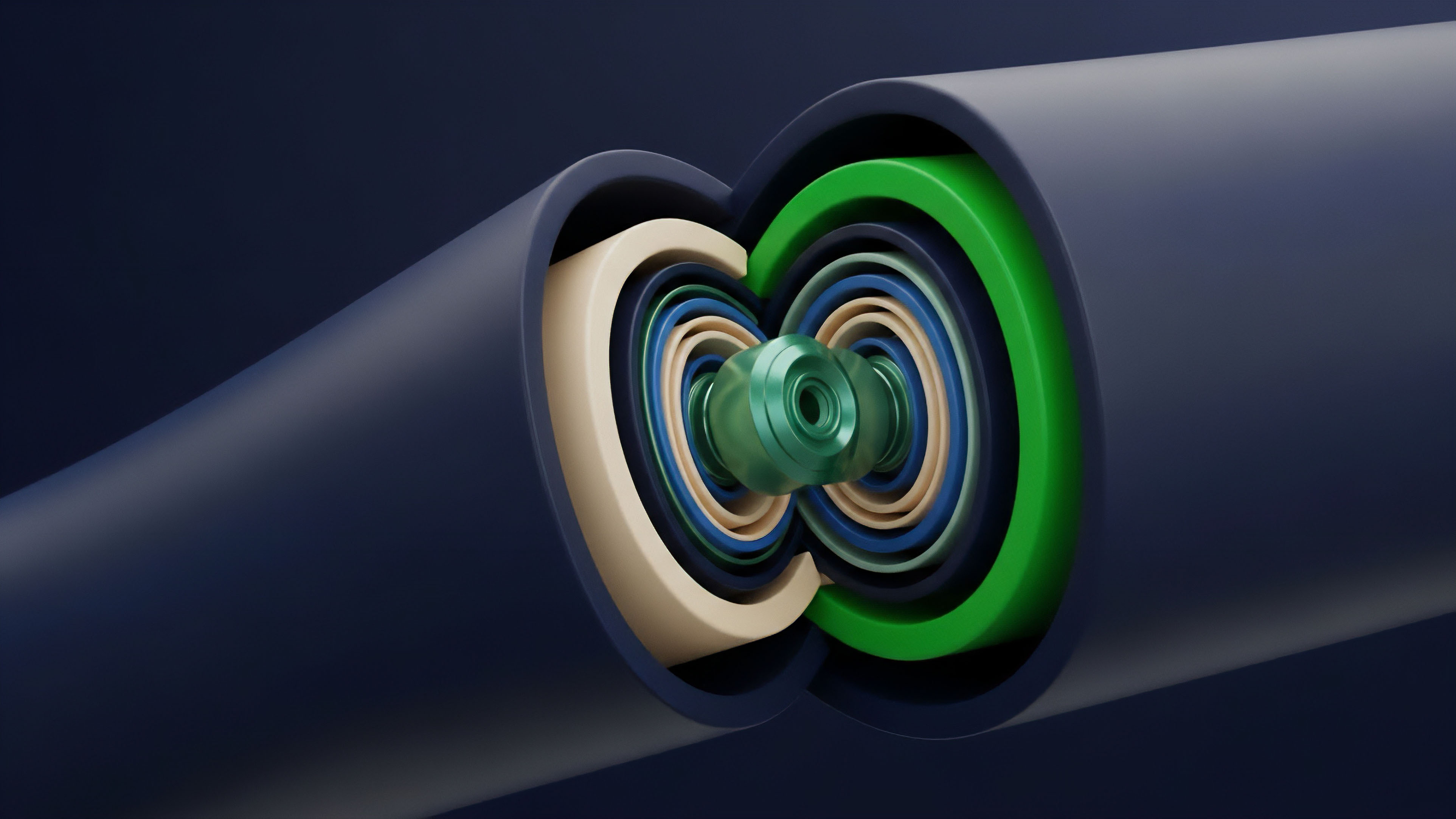
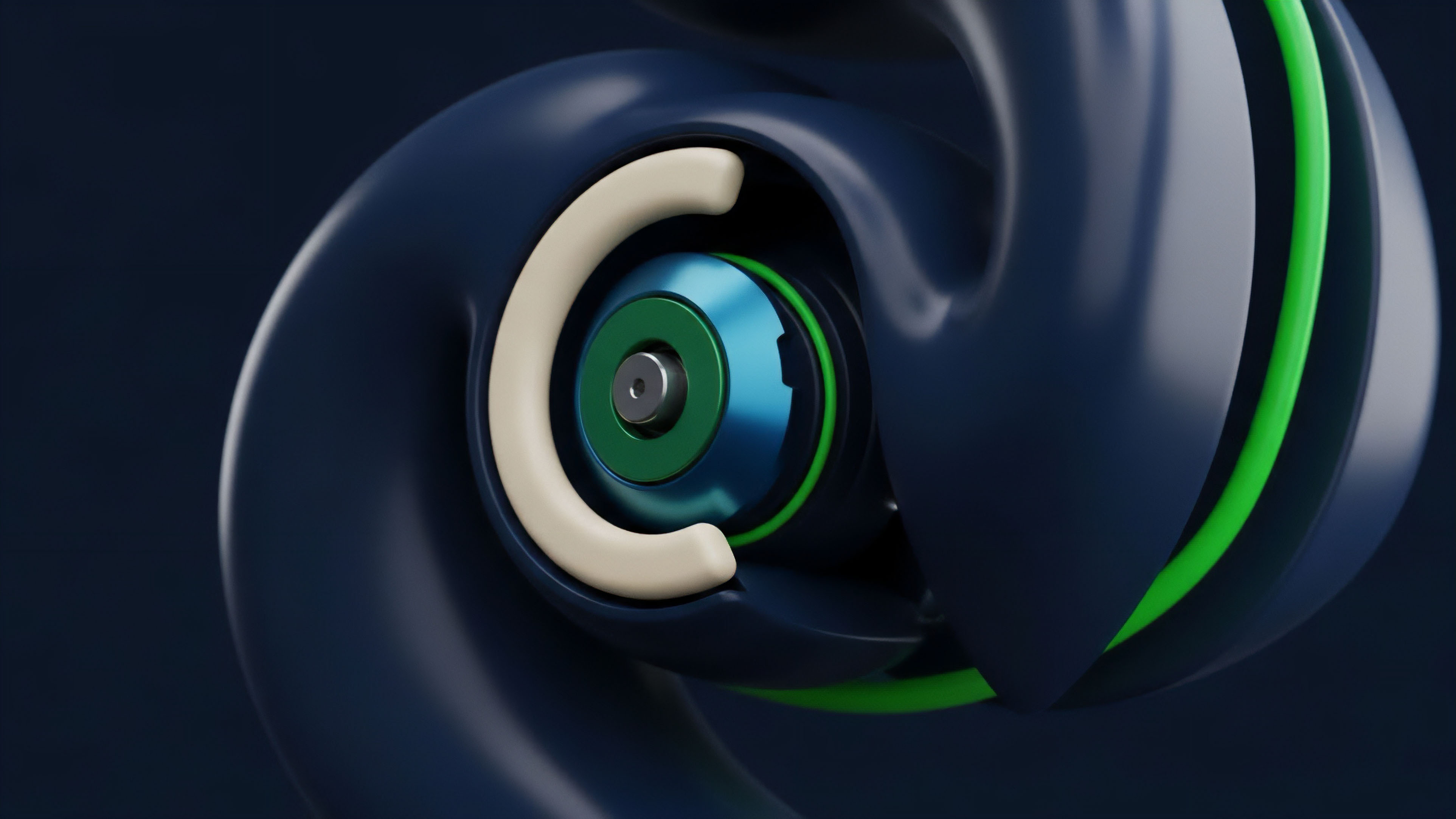
Derivative Architecture
Liquidation Logic

Zk-Evm

Mathematical Invariants

Blockchain Transparency

Cryptographic Attestation

Margin Engine Audit

Decentralized Finance Security