Essence
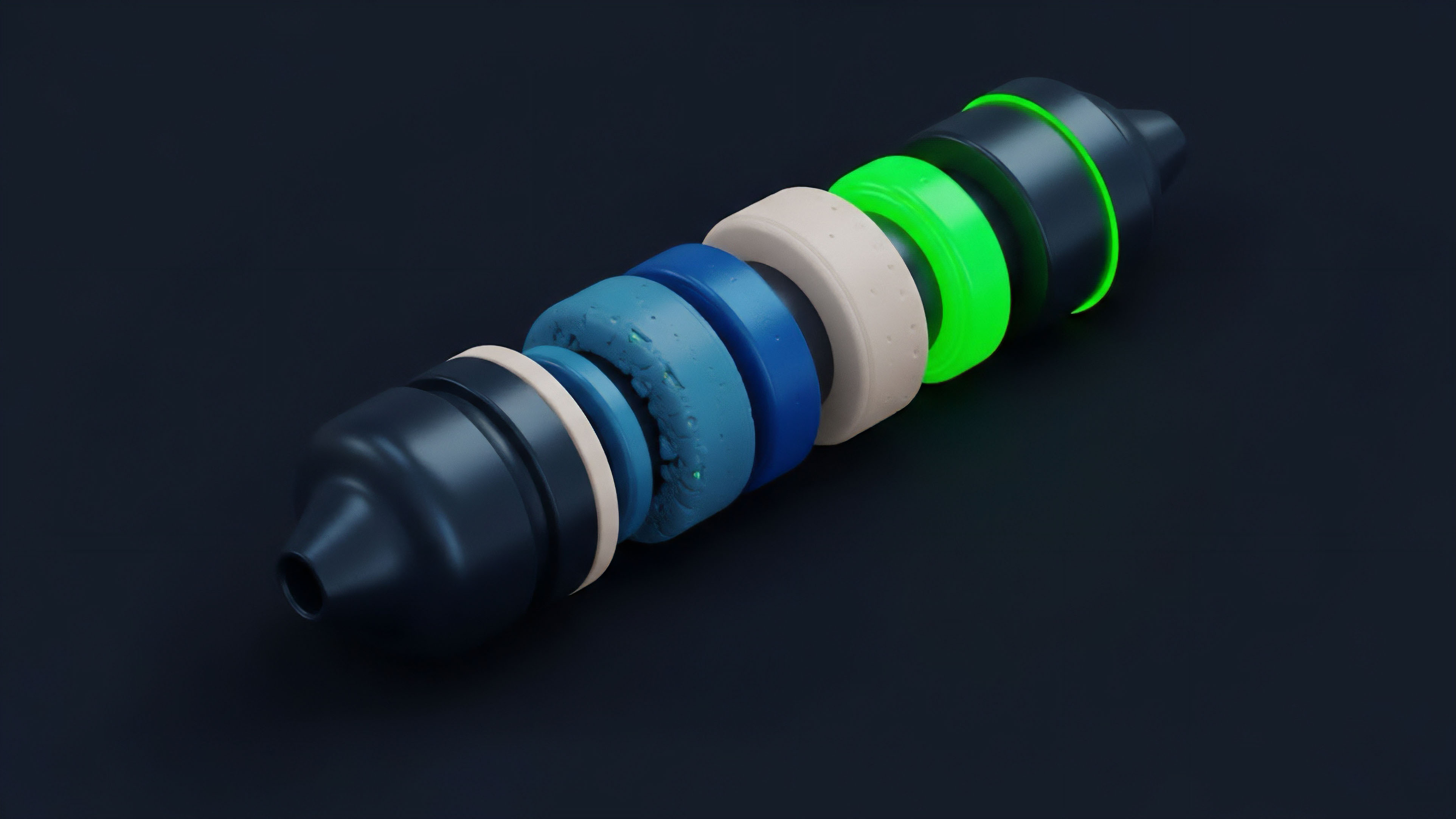
A security audit for crypto options protocols serves as the foundational risk assessment layer for decentralized financial systems. Unlike traditional finance where legal frameworks and centralized institutions manage counterparty risk, a decentralized derivatives protocol relies entirely on the correctness and integrity of its smart contract code. The audit process verifies that the code functions precisely as intended, specifically focusing on the financial logic of the options protocol’s core mechanisms.
This includes validating the margin engine, collateral management, liquidation logic, and oracle dependencies. A flaw in any of these components creates an immediate and potentially catastrophic vector for an economic exploit, leading to a loss of user funds and systemic failure.
A security audit validates the financial integrity of a decentralized options protocol by ensuring its smart contract logic aligns perfectly with its economic design.
The core objective extends beyond simple bug hunting. It involves a rigorous analysis of the protocol’s game theory and incentive structures to ensure they remain robust against adversarial behavior. The audit must confirm that the protocol’s architecture prevents participants from gaining an unfair advantage through code manipulation or market manipulation.
This analysis is particularly vital for options protocols where the financial complexity introduces new risks related to pricing models and settlement mechanisms.

Origin
The need for formalized smart contract audits arose directly from the early, costly failures of decentralized applications. The most significant event, the 2016 DAO attack, demonstrated that code vulnerabilities could lead to irreversible financial losses on a massive scale. The initial iterations of DeFi protocols were relatively simple, but as complexity increased with the introduction of lending platforms and options protocols, the attack surface expanded dramatically.
The “DeFi Summer” of 2020, characterized by a rapid proliferation of new protocols and large amounts of capital locked in smart contracts, highlighted the necessity of a standardized security practice. Without a central authority to guarantee funds, external validation became the primary source of trust for users and investors.
The evolution of security audits has mirrored the development of financial primitives in DeFi. Early audits focused on basic access control and token standards. As options protocols emerged, a new set of risks related to quantitative finance came to the forefront.
The audit process adapted to incorporate analysis of complex mathematical models and pricing logic. The industry moved from informal reviews by individual developers to highly structured methodologies provided by specialized firms. This transition was driven by the recognition that a single code vulnerability in a derivatives protocol could create systemic contagion, affecting interconnected protocols and the broader market microstructure.
Theory
The theoretical foundation of a security audit for options protocols rests on two distinct, yet interconnected, risk models: technical vulnerabilities and economic exploits. Technical vulnerabilities are programming errors, such as reentrancy or integer overflows, that allow an attacker to deviate from the protocol’s intended execution flow. Economic exploits, however, are far more subtle.
They leverage a protocol’s design flaws, often in conjunction with market conditions, to drain value without technically violating the code’s execution rules. An audit must identify both types of risk vectors.
The core challenge for options protocols lies in managing the oracle risk. Options pricing and liquidation calculations are highly dependent on accurate, real-time price feeds. An attacker who can manipulate the price oracle ⎊ even temporarily ⎊ can execute an economic exploit.
This might involve artificially inflating the price of collateral to over-leverage or manipulating the price to trigger liquidations at an incorrect value. The audit process must therefore extend its scope beyond the code itself to include a rigorous analysis of the protocol’s external dependencies and their potential for manipulation. This requires understanding the adversarial game theory at play, where market participants actively seek to exploit the system’s weaknesses for profit.
A successful audit must account for both technical code vulnerabilities and the more complex economic exploits that leverage flaws in oracle dependencies and incentive design.
The theoretical approach to audit methodology often involves formal verification. This technique uses mathematical proofs to demonstrate that a protocol’s code adheres to its specification under all possible inputs. For derivatives, this means proving that the margin calculation and settlement logic are mathematically sound.
While highly rigorous, formal verification is resource-intensive and often limited to critical sections of the code. The majority of audits rely on a combination of automated static analysis and manual code review, where human expertise identifies logical flaws that automated tools cannot recognize.
| Risk Type | Description | Example Vulnerability | Impact on Options Protocol |
|---|---|---|---|
| Technical Vulnerability | Flaws in programming logic or implementation. | Reentrancy attack, integer overflow, access control error. | Unauthorized fund withdrawal, incorrect collateral calculations, total loss of assets. |
| Economic Exploit | Flaws in design logic or incentive structures. | Oracle manipulation, flash loan attack, under-collateralization. | Incorrect liquidations, manipulation of options pricing, systemic debt creation. |

Approach
The audit approach for a derivatives protocol begins with a comprehensive review of the protocol’s whitepaper and technical documentation. The auditors first attempt to understand the intended financial behavior of the system, including how margin is calculated, how liquidations are triggered, and how options are settled. This forms the basis for comparing the protocol’s intended design against its actual code implementation.
The process then moves through several phases, combining automated tools with human analysis to achieve maximum coverage.
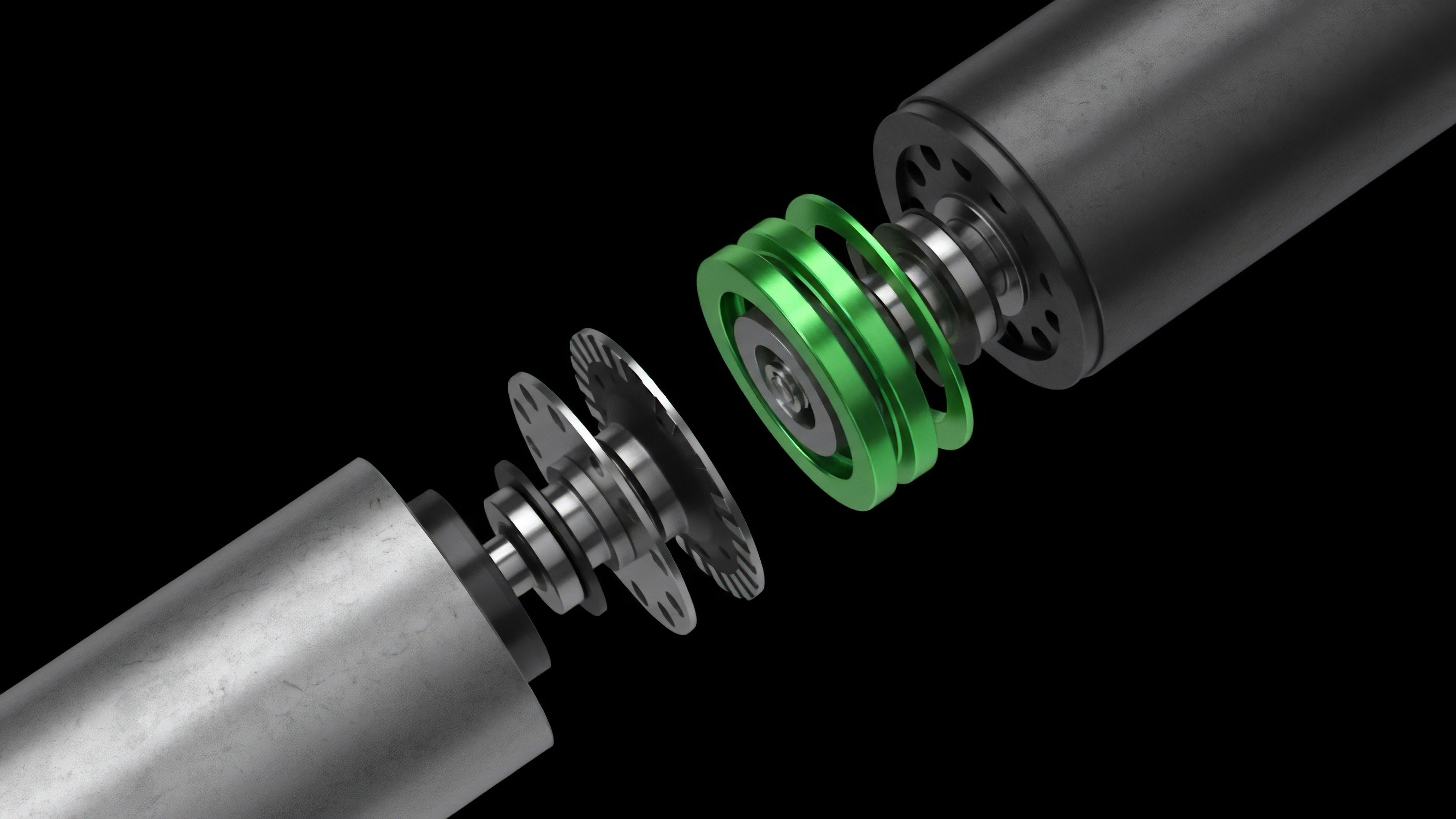
The methodology typically involves a structured, multi-stage process:
- Automated Static Analysis: Tools scan the code for common vulnerability patterns without executing the code. This provides a baseline report of known issues.
- Manual Code Review: Senior auditors meticulously examine the code line by line, focusing on critical sections like the margin engine and liquidation logic. This phase is crucial for identifying subtle logic flaws that automated tools often miss.
- Economic and Game Theory Analysis: The audit team models adversarial scenarios, simulating flash loan attacks or oracle manipulations to assess the protocol’s resilience against financial exploits.
- Formal Verification (Selective): For high-value protocols, formal verification techniques are applied to mathematically prove the correctness of core functions, ensuring the code matches the specification under all conditions.
The final deliverable of an audit is a report detailing identified vulnerabilities, categorized by severity, along with recommendations for remediation. The protocol team then implements the fixes, and a re-audit confirms that the vulnerabilities have been successfully addressed. This iterative process is essential for achieving a robust level of security before deployment.
The audit must also analyze the protocol’s external dependencies, specifically the price oracles used for pricing options and collateral values. A flaw in the oracle integration can be as detrimental as a flaw in the core logic.

Evolution
The security landscape for decentralized derivatives has rapidly evolved from pre-launch, single-instance audits to continuous, multi-layered security frameworks. The initial model, where a protocol received a single audit report before launch, proved insufficient as protocols grew in complexity and value. The “set it and forget it” approach failed to account for new vulnerabilities introduced during code updates or changes in external dependencies.
The current state demands a proactive and continuous approach to risk management.
The shift to continuous security involves several key developments. First, bug bounty programs have become standard practice. Protocols offer financial rewards to white-hat hackers for discovering vulnerabilities in live code.
This creates a market-driven incentive for ongoing security monitoring. Second, specialized security monitoring tools continuously scan a protocol’s transactions and state changes in real-time, looking for anomalous activity that might indicate an active exploit. Third, the rise of decentralized insurance protocols provides a financial backstop for users against smart contract risks, effectively creating a market for residual risk transfer.
This evolution highlights a fundamental change in the relationship between security and protocol development. Security is no longer a one-time gatekeeping function; it is an ongoing process integrated into the protocol’s lifecycle. This continuous model acknowledges that the adversarial environment of decentralized finance requires constant vigilance.
The most robust protocols today operate with a multi-layered defense system, combining pre-launch audits with post-launch bug bounties and real-time monitoring to mitigate the risk of systemic failure.
| Traditional Audit Model | Continuous Security Framework |
|---|---|
| Single pre-launch audit. | Ongoing monitoring and bug bounties. |
| Focus on code logic at a specific point in time. | Dynamic analysis of code behavior in real-time. |
| Reactive approach to known vulnerabilities. | Proactive defense against emergent attack vectors. |
| Trust based on a static report. | Trust based on continuous verification and risk transfer mechanisms. |
Horizon
Looking ahead, the future of security audits for options protocols points toward greater automation and mathematical rigor. The current reliance on manual code review, while essential, cannot scale with the rapid pace of innovation in DeFi. The next generation of security solutions will prioritize formal verification and AI-assisted analysis.
Formal verification will move beyond niche applications to become a standard requirement for high-value derivatives protocols, offering mathematical proof of correctness for core financial logic.
Furthermore, we will see the integration of advanced machine learning models trained on vast datasets of past exploits. These models will predict potential attack vectors in new codebases, allowing auditors to focus on novel, non-obvious vulnerabilities. This shift will make the audit process faster and more reliable.
The concept of security as a service will also expand, with protocols subscribing to continuous monitoring services that provide real-time risk assessments and automated responses to threats. The ultimate goal is to move beyond human-centric security reviews toward a system where the protocol itself is designed with mathematically verifiable guarantees of financial integrity. This will allow decentralized derivatives markets to scale to a level of trust required for mainstream adoption.
- Automated Formal Verification: Using mathematical models to prove the correctness of derivatives pricing and liquidation logic, minimizing human error.
- AI-Assisted Threat Modeling: Leveraging machine learning to predict potential attack vectors based on historical exploit data and code patterns.
- Decentralized Insurance Integration: Protocols offering integrated insurance against smart contract risk, transferring residual risk to specialized capital pools.
- Real-Time On-Chain Monitoring: Continuous scanning of protocol state and transaction flow to detect anomalous behavior before a full exploit occurs.

Glossary

Security Auditing Process

Protocol Security Training Program Development
Pos Network Security

Real-Time Audits

Data Feed Security Model
Decentralized Finance Security Metrics Dashboard

Decentralized Protocol Security
Protocol Design for Security and Efficiency
Blockchain Security Architecture