Essence
Protocol-Native Compliance (PNC) is the architectural embedding of regulatory requirements directly into the smart contract logic of a decentralized options protocol. This design choice transforms compliance from an external, post-trade adversarial overhead ⎊ a massive friction point for institutional capital ⎊ into an automated, pre-trade systemic constraint. The functional goal is not to satisfy regulators; the functional goal is to secure the necessary deep liquidity pools by reducing the Regulatory Friction Factor (RFF) that currently inhibits traditional finance (TradFi) participation.
PNC achieves a profound efficiency gain by replacing slow, human-mediated legal attestations with instantaneous, cryptographic proofs, thereby lowering the cost of capital for market makers.
The core principle dictates that a contract cannot execute unless all required jurisdictional and identity constraints are cryptographically satisfied at the time of order flow. This structural shift is the key to unlocking true systemic efficiency in decentralized derivatives. The system’s resilience ⎊ and its capacity for high-frequency options settlement ⎊ is directly proportional to the speed and certainty of its compliance layer.
Protocol-Native Compliance is the architectural embedding of regulatory requirements into smart contract logic to transform legal friction into a cryptographic constraint.
This approach is a strategic necessity for the options market, which requires continuous, high-volume order book depth to function safely. Without PNC, the capital needed for robust margin systems and tight bid-ask spreads remains siloed in traditional, licensed venues. The efficiency gain is realized in the reduction of counterparty risk and the elimination of jurisdictional ambiguity, which are two of the largest implicit costs in any cross-border financial contract.

Origin
The need for Protocol-Native Compliance arose from the fundamental tension between the initial ethos of decentralized finance ⎊ permissionless and anonymous ⎊ and the market’s insatiable demand for deep, resilient options liquidity. The first wave of crypto derivatives protocols were architected on a principle of Regulatory Arbitrage , positioning themselves outside established legal frameworks to gain a speed advantage. This worked well for retail-scale speculation but failed to attract the multi-billion-dollar balance sheets necessary for stable, low-slippage options markets.
The moment of origin can be traced to the realization that the Liquidity-Compliance Paradox was the primary systemic bottleneck. This paradox states that the more liquid a market becomes, the more regulatory scrutiny it attracts, but institutional liquidity will not enter a market without clear regulatory guardrails. This required a re-architecture ⎊ a move away from avoidance and toward integration.

Early Compliance Mechanisms
Initial attempts at on-chain compliance were crude, relying on simple, centralized blocklists or geographic IP restrictions. These were trivial to bypass and did not satisfy the legal standard of “Know Your Customer” (KYC) or “Anti-Money Laundering” (AML) diligence. The market required something that respected the privacy of the user while simultaneously providing an auditable proof of eligibility.
- Centralized Blocklists: Ineffective, single-point-of-failure solutions that relied on off-chain entities for maintenance and enforcement.
- Sanctions Oracles: A slightly more sophisticated approach, using decentralized oracle networks to push official sanctions lists to the smart contract layer, blocking specific addresses from interacting with the protocol’s core functions.
- Multi-Signature Gateways: Employed by early institutional-focused protocols, requiring a quorum of whitelisted, licensed custodians to sign off on a transaction, which slowed settlement and reintroduced centralized chokepoints.
The true origin of PNC lies in the cryptographic solution to this problem: the use of Zero-Knowledge Proofs (ZKPs). ZKPs allowed the system to prove that a user possessed a valid, compliant identity credential ⎊ issued by a trusted third party ⎊ without revealing the identity itself. This was the first architectural bridge between the non-negotiable legal requirement for identity and the non-negotiable cryptographic requirement for privacy.

Theory
The formal theory of Protocol-Native Compliance is best understood as the integration of a Regulatory Constraint Set (RCS) into the financial system’s state transition function, specifically within the margin and liquidation engine. In classical quantitative finance, option pricing and risk ⎊ the Greeks ⎊ are functions of market variables like volatility, time, and interest rates. In a PNC-enabled system, a new variable is introduced: the Compliance Validity State (ψ) , which is a binary or tiered input derived from a cryptographic attestation.
Our inability to respect the skew is the critical flaw in our current models, and PNC provides a structured way to account for a non-market risk. The primary analytical reasoning involves modeling the cost reduction achieved by replacing legal uncertainty with computational certainty. The systemic friction of a non-compliant market can be quantified as a high, non-linear premium on the implied volatility surface ⎊ a structural, unhedgeable risk that market makers must price in.
PNC seeks to eliminate this premium by guaranteeing that every counterparty is eligible, effectively reducing the necessary capital reserves against regulatory fines and operational shutdowns. This efficiency is formally expressed by reducing the required Value-at-Risk (VaR) capital buffer that institutions must hold against an unforeseen regulatory event. A protocol’s solvency and its ability to maintain low liquidation thresholds ⎊ a key to capital efficiency ⎊ becomes directly linked to the cryptographic integrity of its PNC layer.
The core function is the deterministic enforcement of position limits and margin requirements based on the user’s attested tier, which prevents single entities from accumulating systemic risk and mitigates the possibility of a cascade failure that transcends jurisdictional boundaries. This is the difference between a system that hopes for compliance and a system that mathematically enforces it.
Approach
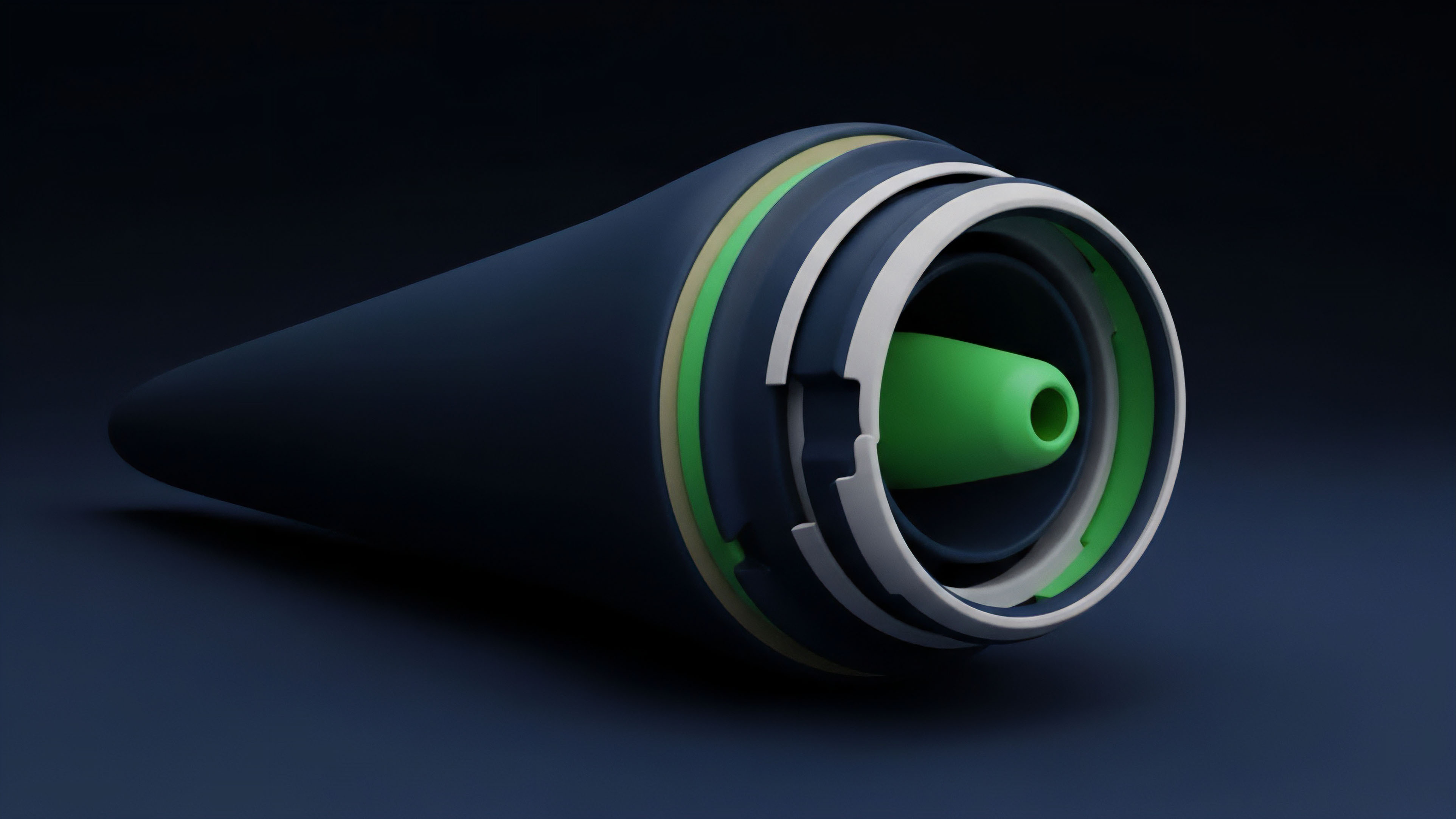
The current approach to implementing Protocol-Native Compliance is characterized by a hybrid architecture that leverages the cryptographic strength of the blockchain while acknowledging the necessity of off-chain legal entities for identity verification. This is a pragmatic, survival-oriented strategy to onboard institutional capital.
Zero-Knowledge Attestation ZKA
This is the most potent technical lever. ZKA allows a user to prove a statement ⎊ such as “I am an accredited investor in jurisdiction X,” or “My total notional exposure is below limit Y” ⎊ without revealing the underlying data (their identity or exact portfolio size). This is achieved through a decentralized identity (DID) credential issued by a trusted third-party verifier.
The smart contract only checks the validity of the ZK-proof, a computational task that is fast and private.
The implementation of Protocol-Native Compliance hinges on the use of Zero-Knowledge Proofs to decouple identity verification from data disclosure.
This approach grounds the entire financial structure in verifiable mathematics, a clear advantage over traditional systems where identity checks are siloed and subject to human error and data leakage. The trade-off, however, is the reliance on the integrity of the initial credential issuer ⎊ a necessary centralized chokepoint.

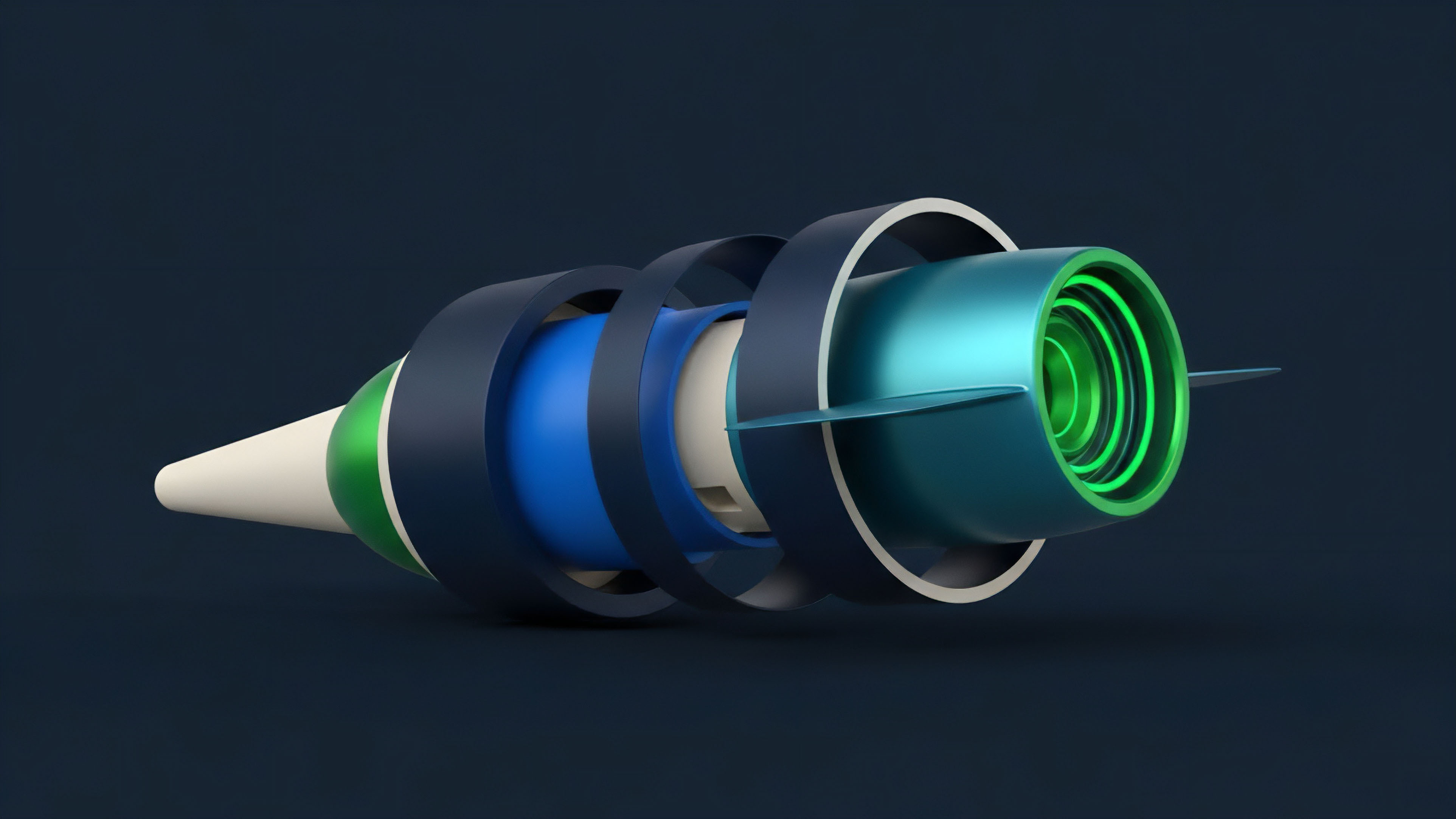
Tiered Access Controls
PNC protocols often utilize a tiered system to manage access to different derivative instruments based on the user’s compliance profile. This allows the protocol to offer highly leveraged, complex options to attested institutional players while restricting retail access to simpler, lower-leverage products, thereby adhering to global retail protection laws.
| Compliance Tier | Required Attestation | Access to Instruments | Max Leverage/Limits |
|---|---|---|---|
| Tier 1 (Anonymous) | None/Basic Geofence | Spot Swaps, Low-Cap Perpetuals | Low (e.g. 2x) |
| Tier 2 (Attested Retail) | KYC Hash Proof (ZK-SNARK) | Simple Calls/Puts, Vanilla Futures | Medium (e.g. 10x), Position Limits |
| Tier 3 (Institutional) | Accreditation Status Proof | Exotic Options, Structured Products | High/Uncapped (Subject to Margin) |
This table illustrates the strategic segregation of risk and opportunity, a framework for action that makes the market navigable for all participant types. The enforcement of these rules is entirely automated by the smart contract, eliminating the latency and potential for human error inherent in legacy systems.

Evolution
The evolution of Protocol-Native Compliance reflects the increasing sophistication of the adversarial environment. It began as a defensive mechanism and is rapidly transitioning into a competitive market feature. Early PNC was static ⎊ a simple, fixed set of rules baked into a version of the smart contract.
Any change required a full governance vote and a costly, high-risk contract migration. This lack of agility made the systems brittle against rapidly shifting global regulatory mandates.

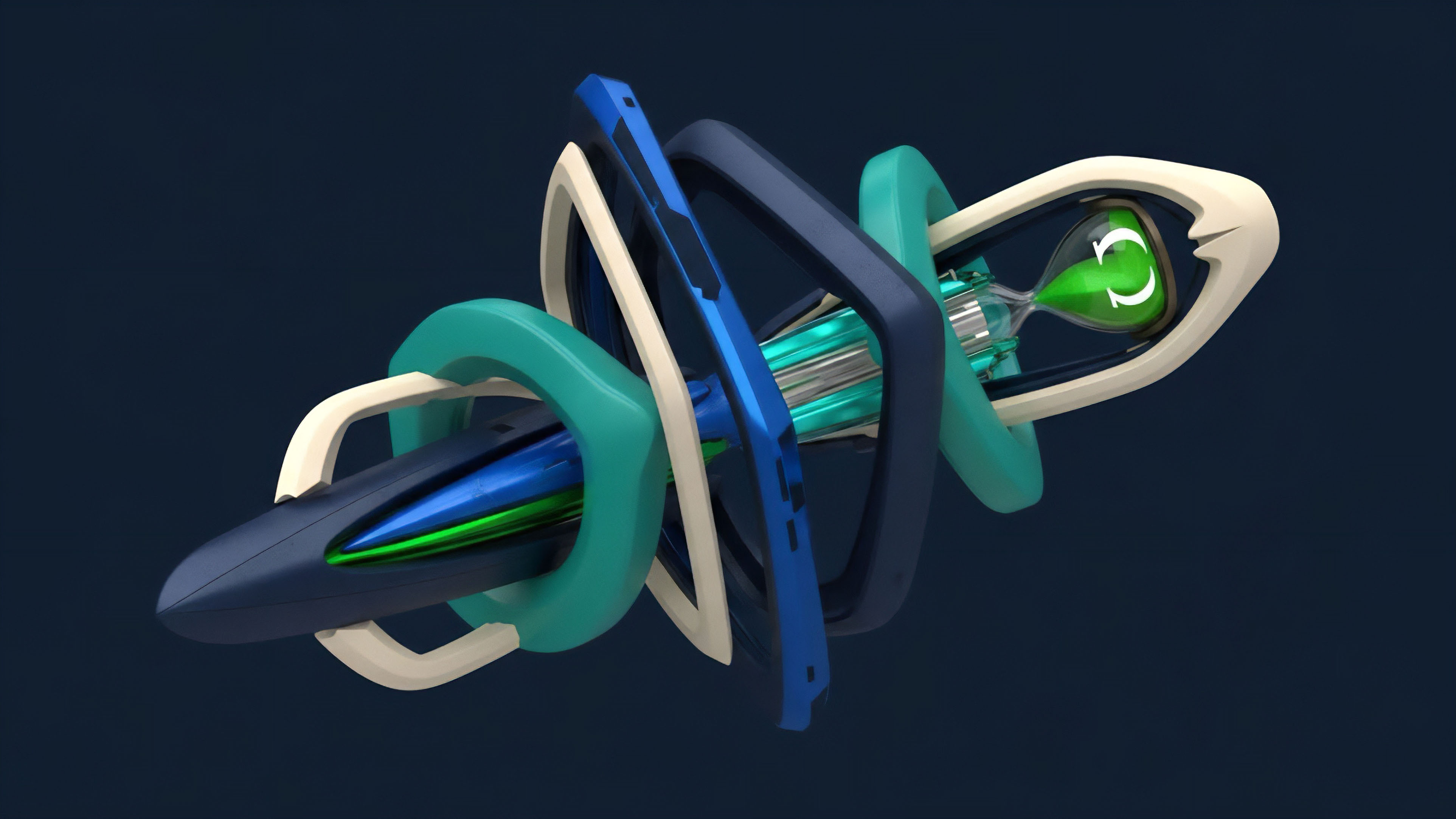
Dynamic Policy Enforcement
The current generation of PNC is characterized by Dynamic Policy Enforcement. This architectural leap uses an On-Chain Policy Engine that can receive and implement new regulatory parameters via a governance or administrative oracle without needing to redeploy the core options contract. This engine is designed for survival, providing the necessary operational flexibility to respond to unforeseen legislative changes in real-time.
The protocol is not a static legal document; it is a continuously adaptive system.
This is achieved by externalizing the compliance logic from the financial logic. The options pricing and settlement contracts remain immutable, while the access and eligibility rules are housed in a separate, upgradeable policy layer.
- Decoupling of Logic: Separating the core financial engine (pricing, settlement) from the compliance gatekeeper (KYC/AML checks).
- Governance-Controlled Oracles: Utilizing decentralized autonomous organization (DAO) governance to approve and push new policy parameters to the compliance engine, ensuring a clear audit trail for all rule changes.
- State-Channel Attestation: Moving the intensive computation of ZK-proof verification off-chain to state channels, allowing the main chain to record only the final, compressed proof of compliance, dramatically increasing throughput and reducing gas costs.
The structural shift in the market is that protocols are now competing on their ability to offer Regulatory Interoperability ⎊ the capacity to simultaneously serve users under multiple, conflicting jurisdictional regimes. This competition is driving the efficiency of PNC, as protocols that can offer broader, legally sound access gain a critical advantage in market depth and trading volume.
Horizon
The future of Protocol-Native Compliance is not about satisfying the current regulatory environment; it is about architecting a new global financial operating system that makes the concept of regulatory arbitrage obsolete. The ultimate horizon is Global Compliance Interoperability (GCI) , where a single, standardized ZK-proof of financial identity is recognized as legally valid across sovereign jurisdictions.

Synthesis of Divergence
The critical pivot point determining whether the market achieves GCI or fragments into regulatory silos is the willingness of sovereign financial bodies ⎊ the SEC, the CFTC, MiFID II ⎊ to accept a cryptographic proof as an equivalent to a paper-based legal attestation. If they reject ZK-proofs as insufficient, the market will fragment, creating dozens of small, high-friction, jurisdiction-specific options pools. If they accept them, a single, global, low-friction market for compliant derivatives becomes possible.
The tension is between legal precedent and mathematical proof.

Novel Conjecture
The systemic adoption of Protocol-Native Compliance will shift options volatility skew from being primarily a function of tail-risk hedging to a function of jurisdictional liquidity fragmentation. That is, the cost of out-of-the-money puts will no longer solely reflect fear of market collapse; it will increasingly reflect the cost of accessing deep, compliant liquidity pools under different regulatory regimes.

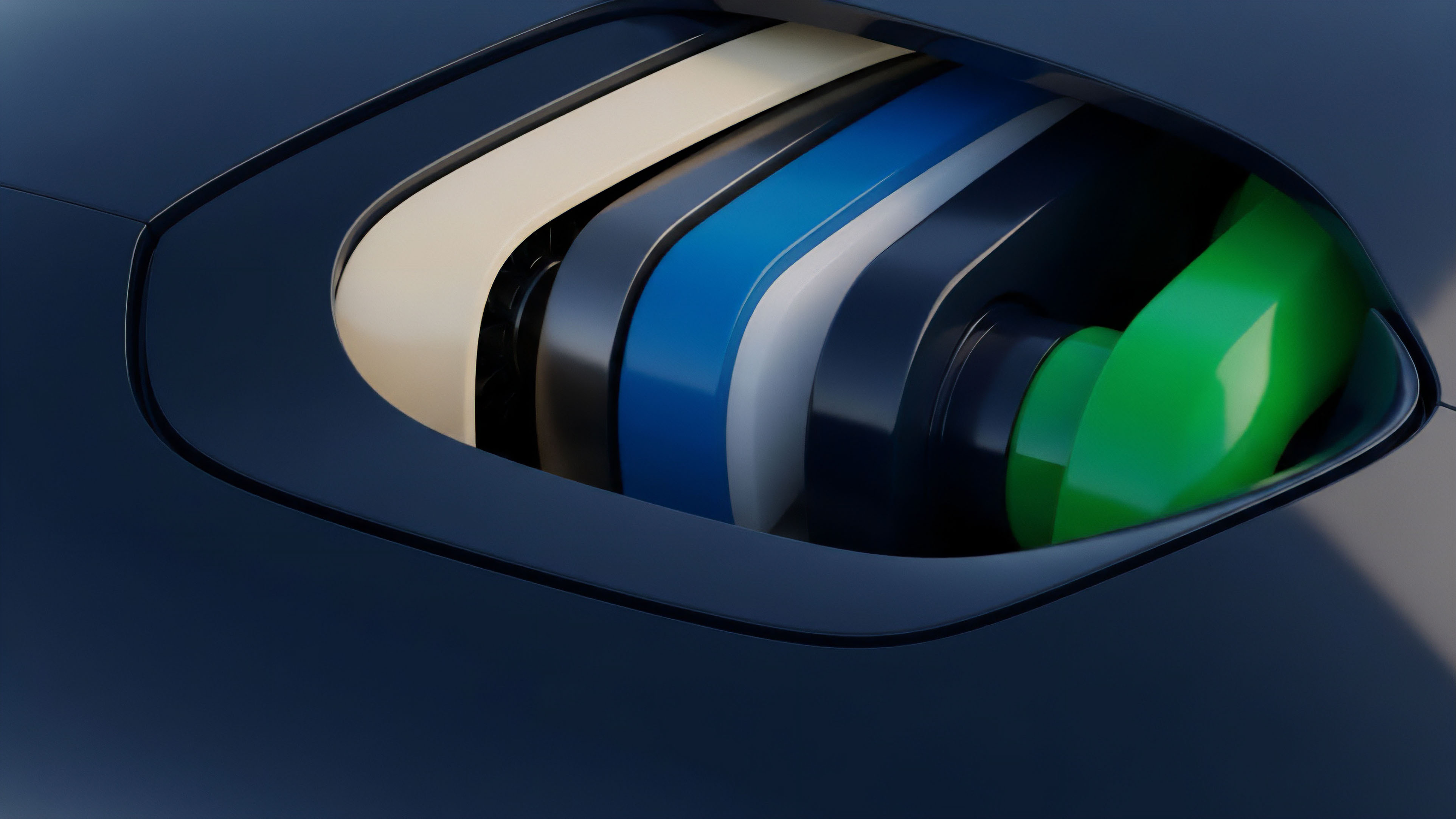
Instrument of Agency Cross-Jurisdictional Attestation Layer CJAL
To realize GCI, we require a shared, public utility. The Cross-Jurisdictional Attestation Layer (CJAL) is a technology specification designed to translate diverse national KYC/AML standards into a unified, on-chain proof.
| Component | Function | PNC Relevance |
|---|---|---|
| Credential Issuers (Off-Chain) | Licensed VSPs (Verifier Service Providers) in each jurisdiction issue DIDs. | Initial legal grounding and data verification. |
| ZK-SNARK Circuit (On-Chain) | Standardized circuit that accepts diverse VSP credentials and outputs a single boolean proof. | The cryptographic engine that enforces the compliance state (ψ). |
| Policy Registry (On-Chain) | Immutable record of accepted VSP public keys and current regulatory parameters (e.g. maximum leverage limits). | Auditability and transparent rule-setting for all options protocols. |
This architecture ensures that a user attested in one jurisdiction can generate a proof of eligibility recognized by a protocol governed in another, drastically reducing the latency and cost associated with global options trading. This is the pathway to capital efficiency at a planetary scale.
What systemic risks ⎊ currently masked by jurisdictional opacity ⎊ will be revealed when every counterparty’s compliance status is made computationally transparent?

Glossary

High-Frequency Options Settlement

Behavioral Game Theory Strategy
Smart Contract Vulnerability Analysis

Systemic Risk Mitigation

Smart Contract Logic
Adversarial Market Environment
Decentralized Autonomous Organization Governance

Computational Certainty

Accredited Investor Proof