Essence
Real-Time Surveillance defines the continuous, sub-second observation of cryptographic state transitions and market participant behavior within decentralized derivative environments. This protocol-level vigilance functions as a decentralized immune system, detecting adversarial patterns before they compromise the integrity of the financial engine. By maintaining an unbroken stream of verification, the system preserves the mathematical sanctity of the smart contract, ensuring that the rules of the game remain invariant even under extreme volatility.
The nature of this oversight is rooted in the immediate detection of anomalies within order books, mempools, and liquidation queues. Unlike traditional financial systems that rely on T+1 or T+2 settlement and retrospective audits, cryptographic markets demand a proactive posture where the latency of detection is the primary determinant of system security. Real-Time Surveillance monitors the velocity of price changes, the depth of liquidity at specific strikes, and the concentration of risk among participants to prevent the accumulation of toxic debt.
Real-Time Surveillance maintains protocol integrity by identifying adversarial behavior before state finality occurs.
This mechanism ensures that the margin engines and liquidation protocols operate within their intended parameters. When the system detects a deviation ⎊ such as an oracle delay or a sudden drop in order book depth ⎊ it triggers automated responses to protect the solvency of the protocol. This level of transparency and immediate response is what allows decentralized options to scale while mitigating the risks of flash crashes or manipulation.

Origin
The requirement for such vigilance surfaced following the collapse of early trust-based trading venues and the rise of automated market makers that lacked protection against toxic order flow.
These historical failures demonstrated that opaque order books and hidden liabilities create systemic fragility. As the industry transitioned toward permissionless settlement, the demand for transparency necessitated a shift from periodic audits to persistent monitoring. This transition mirrors the move from centralized banking to open-source finance, where the ability to verify the state of the system at any moment becomes the primary guarantee of solvency.
Early decentralized exchanges were vulnerable to front-running and sandwich attacks, which eroded the capital of liquidity providers. The genesis of Real-Time Surveillance was a direct response to these vulnerabilities, leading to the development of tools that could monitor the mempool for pending transactions. This allowed protocols to implement slippage protections and anti-MEV strategies that are now standard in institutional-grade decentralized finance.
| Phase | Surveillance Method | Primary Objective |
|---|---|---|
| Early DEX | Post-Trade Analysis | Historical Auditing |
| AMM Maturation | Mempool Monitoring | Front-Running Mitigation |
| Derivative Scaling | Continuous State Verification | Systemic Solvency Protection |
The ancestry of these systems can be traced back to high-frequency trading in traditional markets, where latency is the ultimate weapon. However, in the cryptographic domain, this technology is utilized not just for profit, but for the preservation of the protocol itself. The shift from human-led compliance to code-driven monitoring represents a major leap in financial engineering, where the observer and the observed are part of the same immutable ledger.

Theory
From a quantitative perspective, Real-Time Surveillance utilizes high-frequency data to analyze order flow toxicity and liquidity concentration.
It relies on statistical anomaly detection to differentiate between organic price discovery and predatory manipulation. The mathematical basis for this involves monitoring the VPIN (Volume-Synchronized Probability of Informed Trading) and other metrics that indicate when a market is becoming imbalanced.
Quantitative monitoring of order flow toxicity prevents predatory liquidity extraction in decentralized option markets.
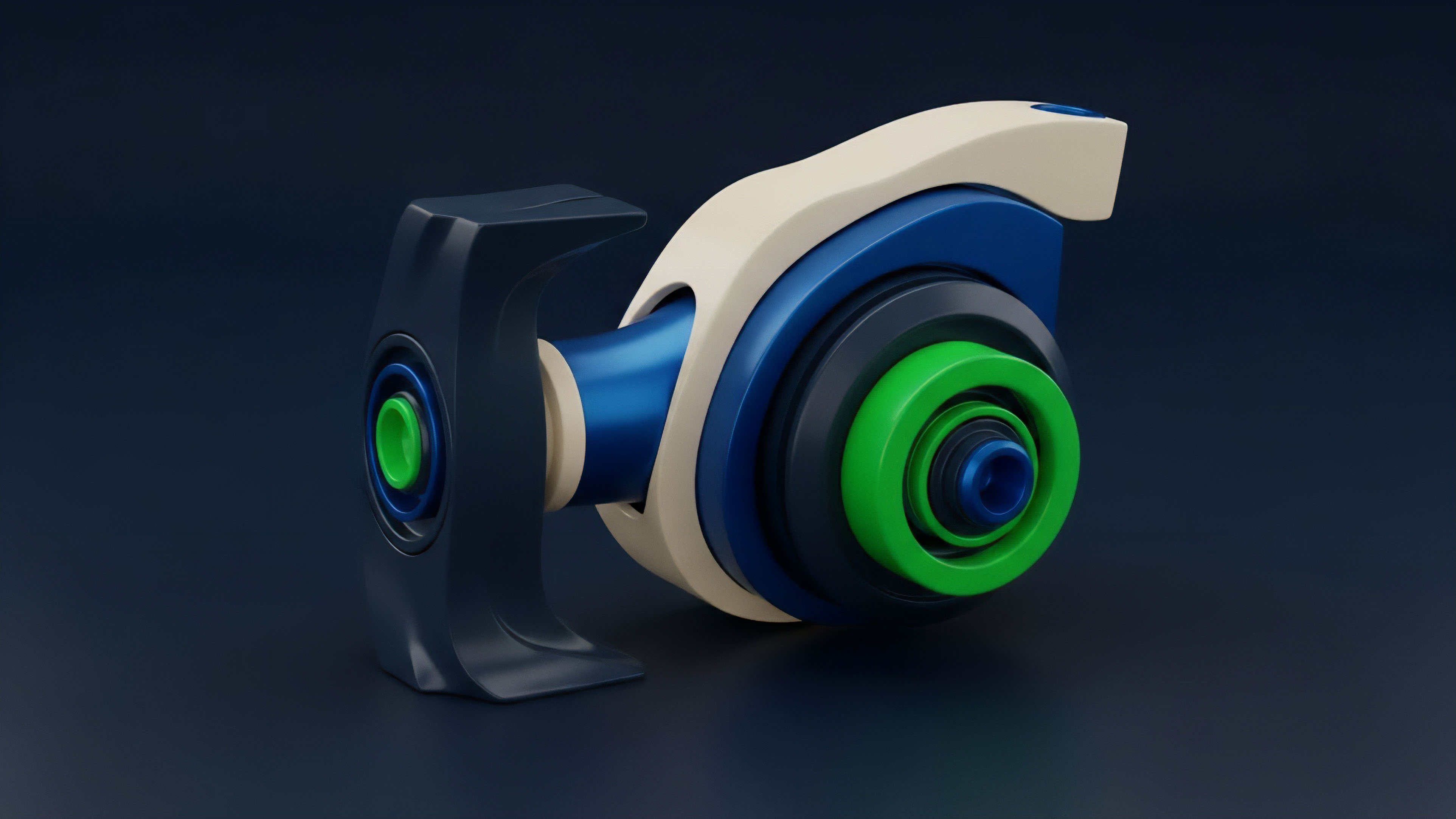
The architecture of these systems is built on the study of market microstructure, where every tick and every order update is scrutinized. By analyzing the Greeks ⎊ Delta, Gamma, Theta, and Vega ⎊ in real-time across the entire protocol, Real-Time Surveillance can identify when the system is becoming over-leveraged or when a specific strike price is becoming a point of systemic failure. This allows the protocol to adjust its margin requirements or funding rates dynamically to maintain equilibrium.
- Order Flow Toxicity: The measurement of the probability that a trade is informed and predatory, leading to adverse selection for liquidity providers.
- Liquidation Cascades: The analysis of how a single liquidation event can trigger a chain reaction of price drops and further liquidations.
- Oracle Latency: The monitoring of the time delay between the external price movement and its reflection on the blockchain.
- Convexity Risk: The observation of how non-linear price movements in options impact the collateralization ratios of the protocol.

Approach
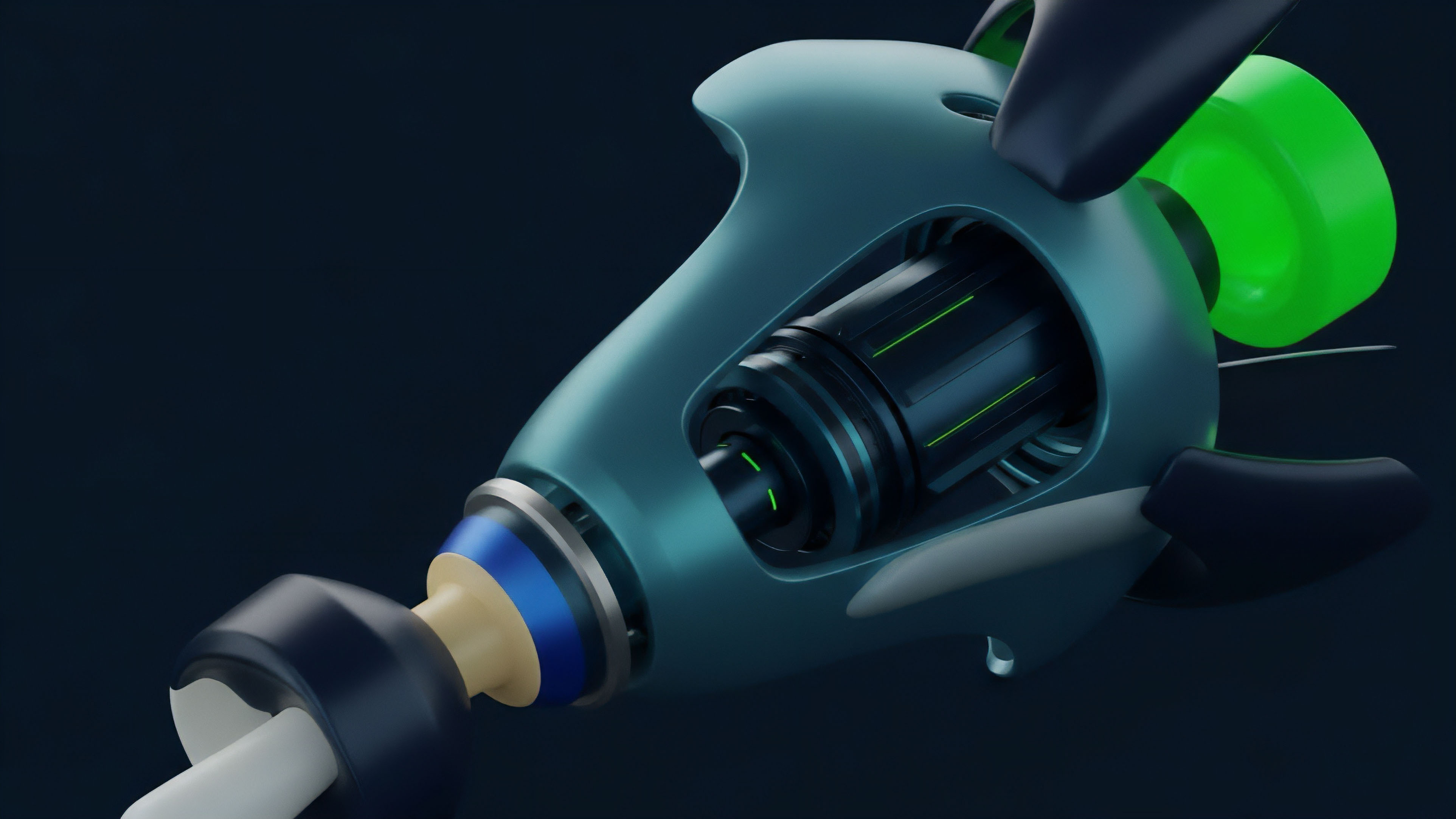
Current methodology involves the deployment of sentinel nodes that scan the mempool for pending transactions and monitor the health of the liquidation engine. These agents assess the impact of incoming trades on the protocol’s risk parameters before they are finalized. This pre-trade validation is vital for maintaining the solvency of complex option spreads, where a single large move can wipe out the collateral of multiple participants.
| Metric | Surveillance Focus | Risk Mitigation |
|---|---|---|
| Mempool Depth | Pending Transactions | Sandwich Attack Prevention |
| Funding Rates | Basis Deviation | Arbitrage Stabilization |
| Oracle Heartbeat | Price Feed Consistency | Manipulation Detection |
| Margin Ratios | Account Solvency | Automated Liquidation |
This methodology also incorporates the use of decentralized data oracles that provide a tamper-proof stream of external market data. By comparing these feeds in real-time, Real-Time Surveillance can detect when a single oracle has been compromised or is providing stale data. This redundancy is a structural requirement for any protocol that handles billions of dollars in notional value.

Evolution
The maturation of monitoring has shifted from reactive alerts to proactive risk mitigation.
Early systems focused on post-trade analysis, whereas modern architectures emphasize pre-trade validation and automated circuit breakers. This development reflects a maturation of the market, where survival depends on the ability to anticipate and neutralize threats in milliseconds. The transition from simple threshold-based monitoring to complex machine learning models has allowed protocols to handle higher volumes with lower risk.
Proactive liquidation analysis maintains system solvency during periods of extreme market dislocation.
Beyond this, the integration of cross-chain monitoring has become a primary focus. As liquidity fragments across different Layer 2 solutions and sidechains, Real-Time Surveillance must now track the movement of assets and the correlation of prices across multiple networks. This prevents arbitrageurs from exploiting price discrepancies that could lead to the drainage of liquidity from a specific protocol.
- Static Monitoring: Initial systems used fixed thresholds for liquidations and margin calls, which were often too slow during high volatility.
- Dynamic Adjustments: Protocols began using variable parameters based on market conditions, such as increasing margin requirements during periods of high Gamma.
- Predictive Analysis: Current systems use historical data and real-time flows to predict where liquidations are likely to occur, allowing for better liquidity management.

Horizon
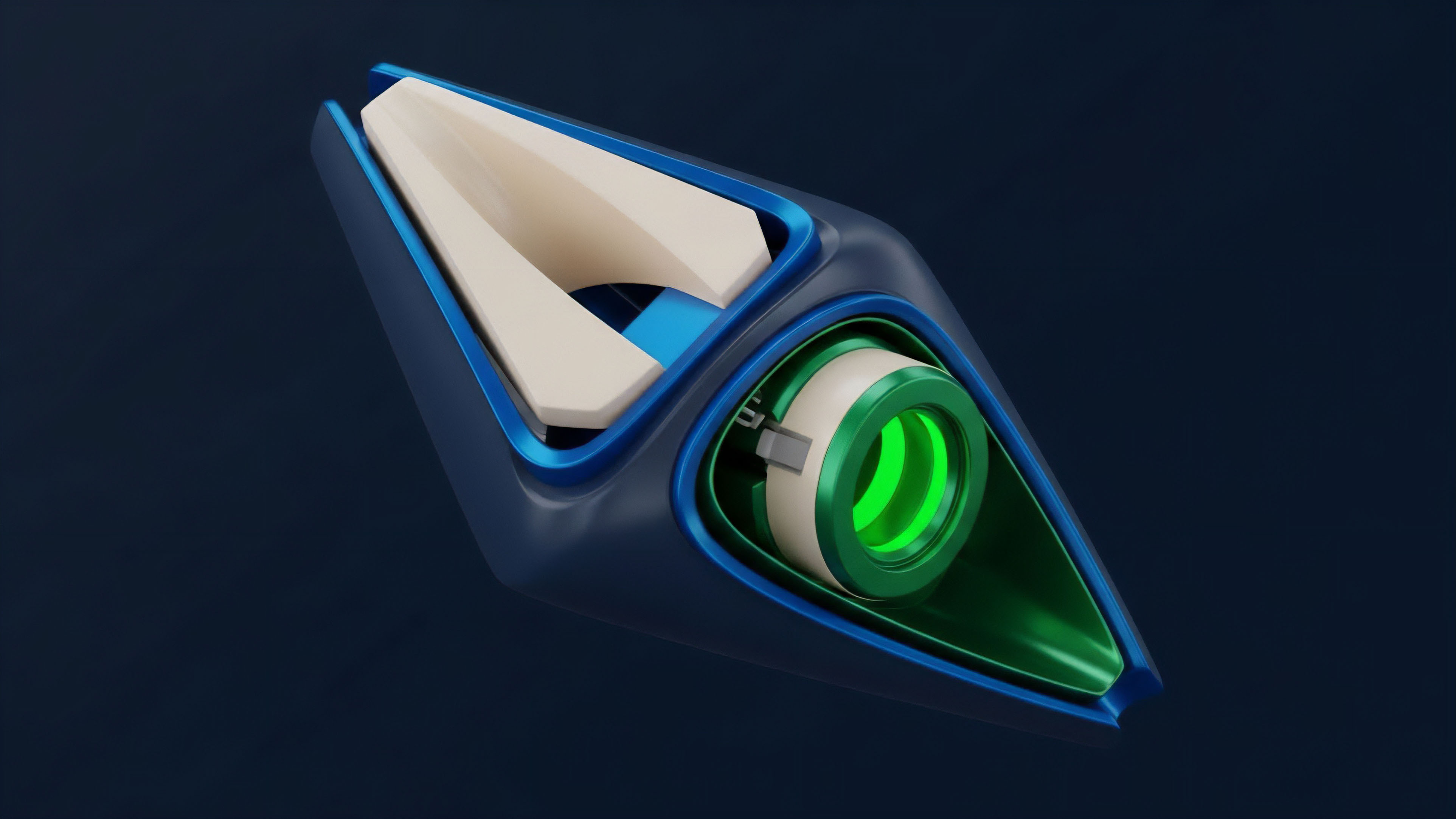
The future trajectory involves the unification of cross-chain monitoring and the application of zero-knowledge proofs for privacy-preserving oversight. As decentralized derivatives scale, the ability to model contagion across disparate protocols will become the standard for institutional-grade security. This will allow for regulatory compliance without compromising the anonymity of the participants, a vital requirement for the mass adoption of decentralized finance.
The development of autonomous surveillance agents that can negotiate with other protocols to stabilize the market is also on the outlook. These agents would use game-theoretic models to determine the best course of action during a systemic crisis, such as providing emergency liquidity or adjusting protocol parameters to prevent a total collapse. This level of automation will further decouple the financial system from human error and institutional bias.
| Future Trend | Technological Driver | Systemic Impact |
|---|---|---|
| ZK-Surveillance | Zero-Knowledge Proofs | Privacy-Preserving Compliance |
| Cross-Chain Contagion Modeling | Interoperability Protocols | Global Risk Management |
| AI-Driven Risk Engines | Machine Learning | Predictive Solvency Protection |
As the boundary between traditional and decentralized finance continues to blur, Real-Time Surveillance will be the bridge that ensures stability and trust. The ability to monitor every transaction and every state change in real-time is not a luxury; it is the structural foundation upon which the future of global finance will be built.

Glossary

Order Book Depth

Perpetual Swaps

Trading Volume

Market Manipulation Detection

Staking Derivatives

Liquidation Engine

Atomic Swaps
Proof of Reserves

Cross-Chain Risk