Systemic Integrity Protocol
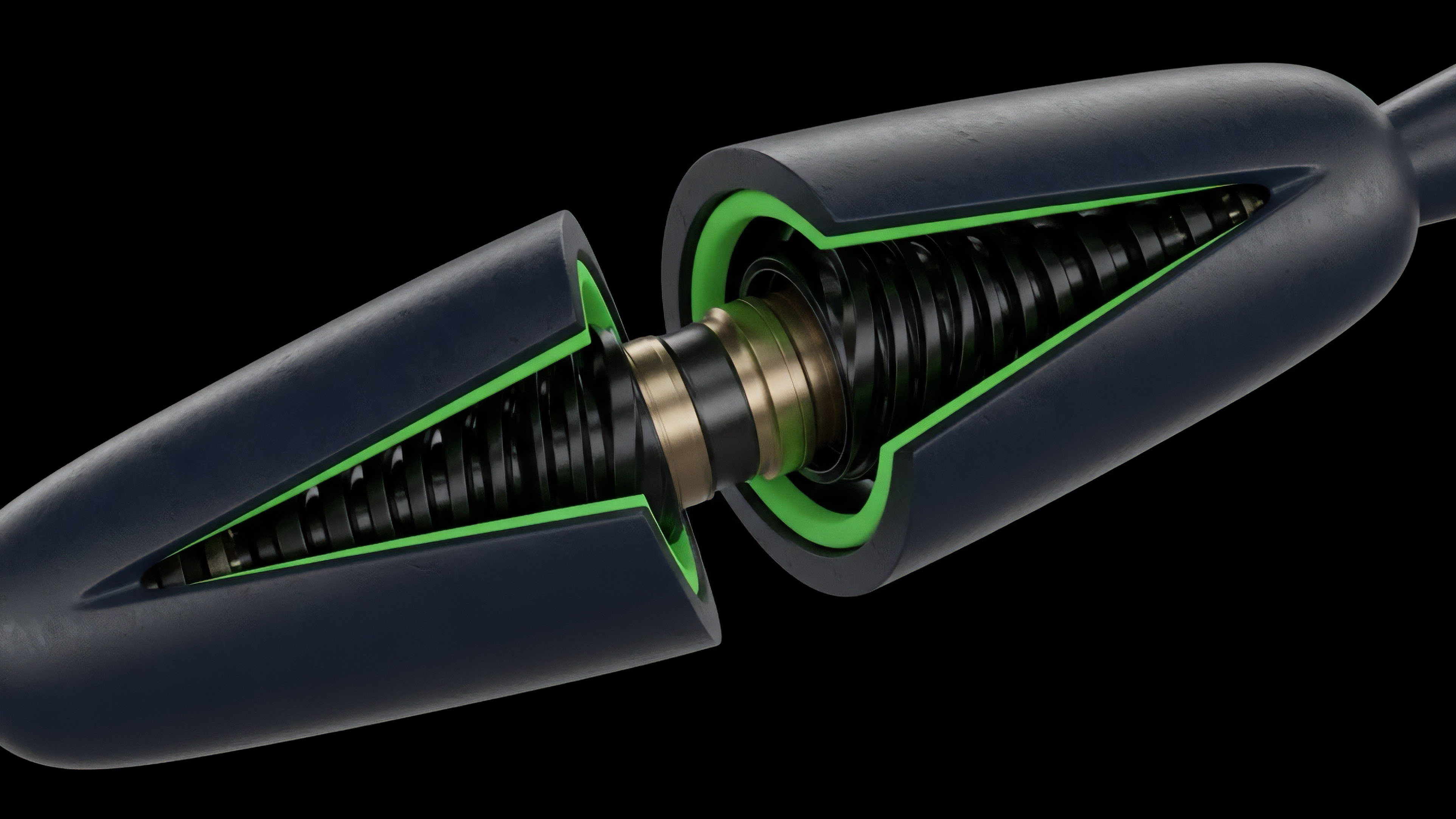
Economic Invariant Stress Testing functions as the rigorous validation of a protocol’s internal logic against adversarial market conditions. This process identifies immutable properties that must remain true under every possible state transition. Within the sphere of decentralized options, these properties relate to the solvency of the vault and the mathematical consistency of the automated market maker.
This methodology shifts the security burden from reactive patching to proactive verification.
Economic Invariant Stress Testing ensures that the mathematical laws governing a protocol remain valid despite extreme market volatility or adversarial manipulation.
The focus remains on the preservation of solvency. In a decentralized derivative environment, the absence of a central clearing house necessitates that the code itself acts as the final guarantor of settlement. Economic Invariant Stress Testing subjects the protocol to simulated environments where liquidity vanishes, volatility spikes to unprecedented levels, and oracle feeds provide distorted data.
The objective is to prove that the system can gracefully handle these shocks without a total collapse of the collateralization ratio. By defining these boundaries, architects can construct systems that are resilient by design. This is a move toward a financial infrastructure where the risk is quantified and bounded by mathematical proofs rather than the subjective assessments of external auditors.
The integrity of the system is a function of its code, and Economic Invariant Stress Testing is the tool used to verify that this function is sound.

Verification History
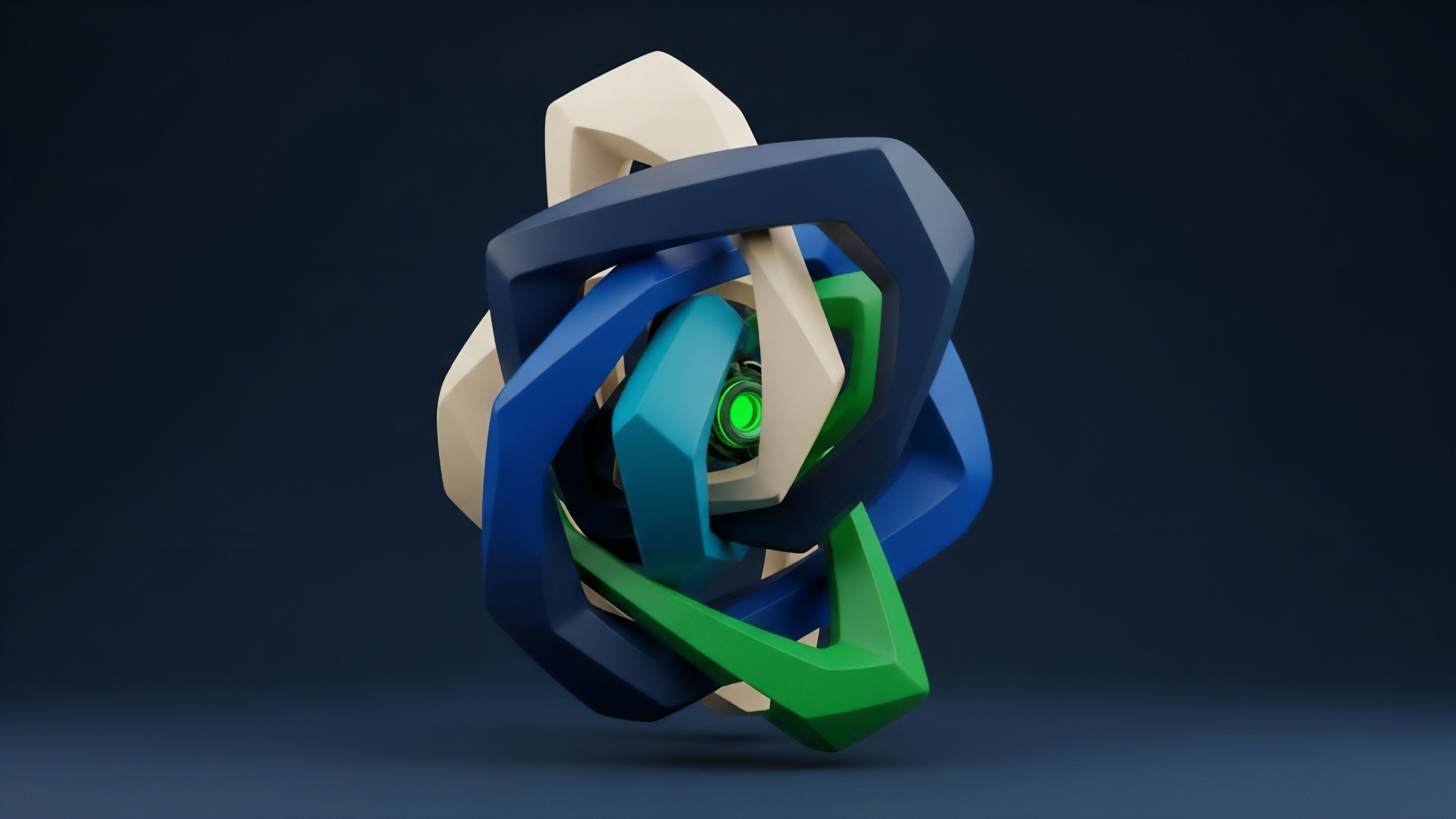
The requirement for rigorous validation arose from the systemic fragility observed in early decentralized finance iterations. Initial security measures relied on static code reviews, which failed to account for the complex interactions between different financial primitives. As the volume of capital within these systems increased, the cost of failure became prohibitive, leading to the adoption of more sophisticated methods from high-stakes industries like aerospace and cryptography.
The transition from human-centric auditing to machine-verifiable proofs represents a shift toward objective security in decentralized financial systems.
Traditional finance relies on legal recourse and regulatory oversight to manage systemic risk. In the permissionless environment of blockchain, these mechanisms are absent. The Economic Invariant Stress Testing methodology fills this void by providing a technical substitute for trust.
It draws upon the principles of formal methods, where the behavior of a program is described as a set of mathematical equations that can be proven correct. This historical shift was accelerated by the realization that code vulnerabilities are often economic rather than purely technical. An exploit might not involve a bug in the traditional sense but rather a flaw in the incentive structure or a failure to account for flash loan-driven price manipulation.
Economic Invariant Stress Testing was developed to address these multi-dimensional risks by simulating the game-theoretic interactions between different market participants.
Mathematical Security Models
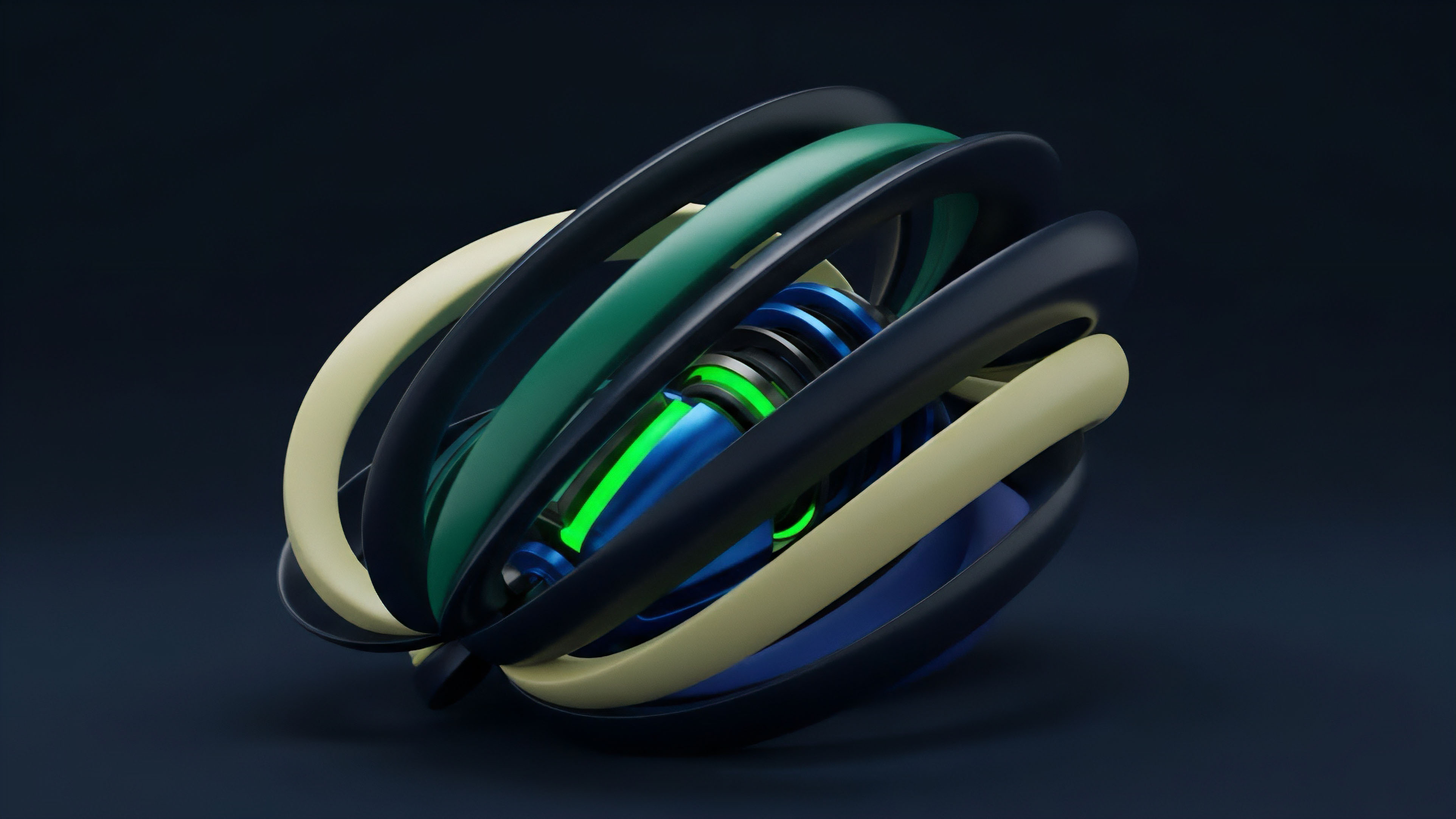
State space analysis defines the boundaries of safe operation for a derivative protocol. Every action ⎊ whether it is a trade, a liquidity deposit, or a liquidation ⎊ represents a transition from one state to another. Economic Invariant Stress Testing identifies the invariants that must be preserved across these transitions.
For instance, the total value of collateral must always exceed the total value of outstanding liabilities, adjusted for a specific safety margin.
| Testing Tier | Focus Area | Certainty Level |
|---|---|---|
| Unit Testing | Individual Functions | Low |
| Economic Simulation | Market Volatility | Medium |
| Formal Proofs | Logical Invariants | Absolute |
These invariants are similar to the conservation laws in physics, where certain quantities remain constant within a closed system. In a decentralized options protocol, the conservation of value is maintained through the pricing engine and the margin requirements. Economic Invariant Stress Testing uses symbolic execution to explore all possible paths through the state space, ensuring that no sequence of actions can lead to an insolvent state.
Mathematical invariants act as the physical laws of a protocol, preventing state transitions that would lead to systemic insolvency.
The application of quantitative finance models allows for the stress testing of the Greeks ⎊ Delta, Gamma, Theta, and Vega. By simulating extreme shifts in these parameters, the testing process reveals how the protocol’s risk profile changes under pressure. This level of analysis is necessary for maintaining the stability of a decentralized margin engine, where the liquidation of underwater positions must occur in a timely and efficient manner.

Technical Execution Paths
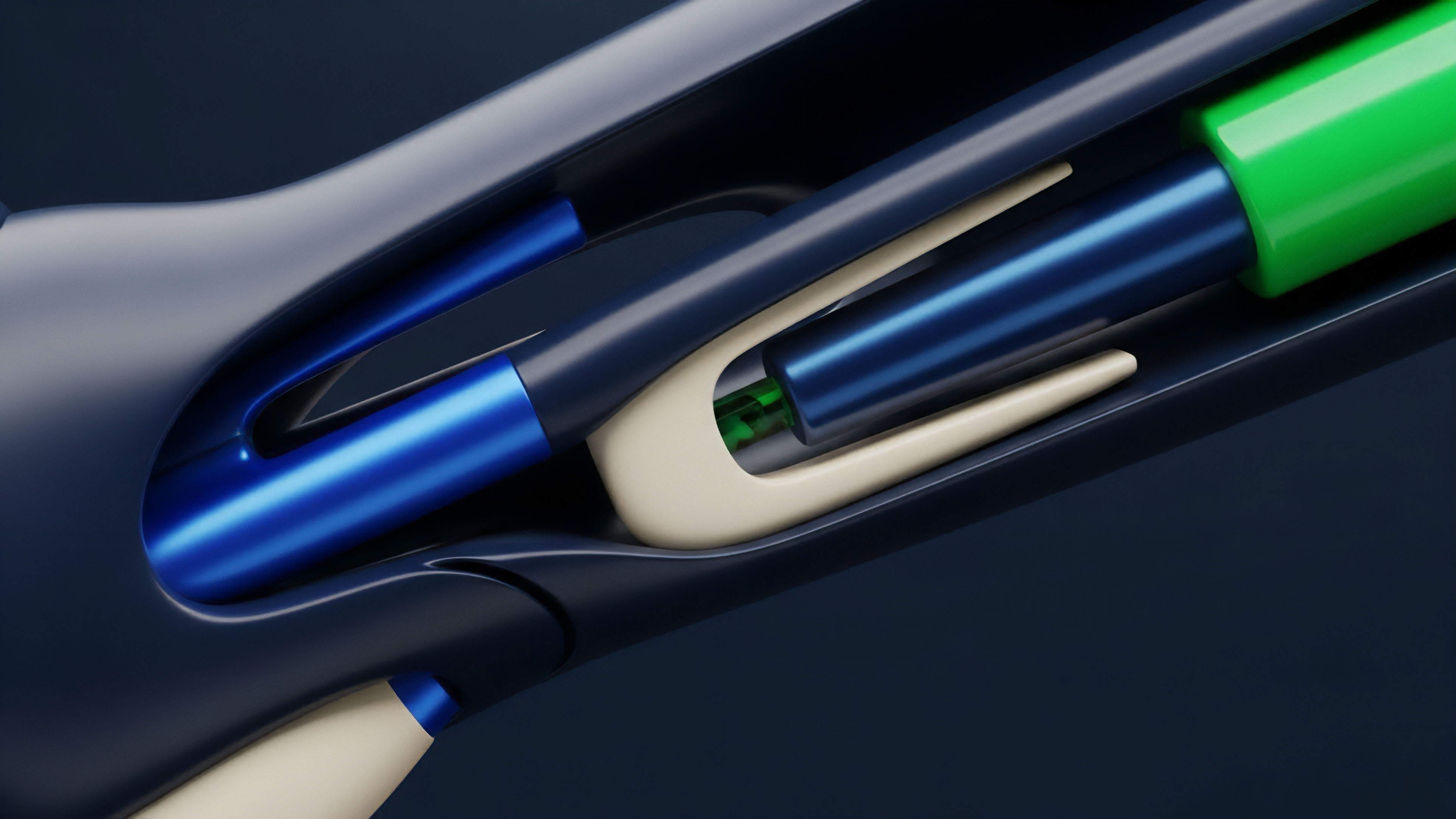
The execution of Economic Invariant Stress Testing involves a multi-layered approach that combines automated tools with manual adversarial analysis.
Property-based testing is used to subject the code to millions of randomized inputs, searching for edge cases that might have been missed during the design phase. This is complemented by formal verification, where the protocol’s logic is translated into a formal specification and proven against a set of security properties.
- Symbolic execution generates mathematical representations of all possible program states to identify unreachable or dangerous logic paths.
- Property-based fuzzing subjects the code to randomized inputs to detect edge cases that could lead to economic failure.
- Formal verification produces a mathematical proof that the implementation matches the security specification.
- Agent-based modeling simulates the behavior of rational and adversarial actors to test the protocol’s incentive alignment.
These technical paths provide a high degree of confidence in the protocol’s resilience. By automating the search for vulnerabilities, architects can identify and remediate flaws before they can be exploited in a live environment. The use of Economic Invariant Stress Testing also facilitates the development of more complex financial instruments, as the risks associated with these instruments can be rigorously quantified and managed.
| Method | Description | Primary Risk Addressed |
|---|---|---|
| Fuzzing | Randomized input generation | Coding errors and edge cases |
| Formal Methods | Mathematical proof of logic | Structural and logical flaws |
| Game Theory Simulation | Adversarial actor modeling | Economic and incentive exploits |

Testing Strategy Shift
The methodology has progressed from point-in-time audits to continuous security monitoring. In the early stages of decentralized finance, a single audit was considered sufficient for a protocol launch. However, the introduction of upgradable contracts and the integration of multiple protocols created a need for a more persistent form of validation.
Economic Invariant Stress Testing is now integrated into the development lifecycle, with tests running automatically every time the code is modified.
Continuous verification replaces static auditing as the standard for maintaining the integrity of high-value decentralized protocols.
This progression also includes the use of real-time economic monitoring. By embedding Economic Invariant Stress Testing logic into the protocol itself, architects can create circuit breakers that trigger when certain invariants are at risk of being violated. This provides an additional layer of protection against unforeseen market events or sophisticated exploits that were not captured during the initial testing phase. The focus has also expanded to include cross-chain risks. As liquidity moves between different blockchain environments, the security of a protocol depends on the integrity of the connections between these environments. Economic Invariant Stress Testing is being adapted to account for the unique risks of cross-chain communication, such as finality delays and validator collusion.

Future Security States
The next phase of security involves the use of autonomous agents and zero-knowledge proofs to enhance the testing process. Autonomous agents can be deployed to continuously probe a protocol for vulnerabilities, simulating a never-ending adversarial environment. This creates a constant pressure on the protocol to maintain its integrity, leading to a more robust and resilient financial infrastructure. Economic Invariant Stress Testing will become more sophisticated as these agents learn to identify and exploit complex economic flaws. Zero-knowledge proofs offer a way to verify the results of a security test without revealing the underlying logic or data. This is particularly useful for private security testing, where a protocol might want to prove its solvency to external parties without disclosing its proprietary trading strategies or user data. The integration of these technologies will further strengthen the security of decentralized derivatives. The ultimate goal is the creation of a self-healing financial system. In this future state, Economic Invariant Stress Testing logic will not only detect vulnerabilities but also automatically generate and deploy patches to remediate them. This would represent a significant leap forward in the evolution of decentralized finance, moving toward a system that is not only secure by design but also capable of adapting to new threats in real-time.

Glossary
Zero-Knowledge Security Proofs
Volatility Surface Analysis

Mev Protection Mechanisms

Greeks Risk Management

Agent-Based Modeling

Delta Neutrality Verification

Circuit Breaker Logic
Liquidity Fragmentation Risk

Permissionless Financial Infrastructure