Essence
Cryptographic integrity functions as the primary determinant of capital preservation within decentralized financial architectures. Blockchain Network Security Audits and Vulnerability Assessments represent the systematic verification of programmatic logic against adversarial exploitation. This process establishes the technical solvency of a protocol, transforming subjective trust into verifiable mathematical certainty.
Within the context of autonomous finance, the perimeter of security is defined by the absence of unintended state transitions.
Smart contract verification represents the transformation of legal trust into mathematical proof.
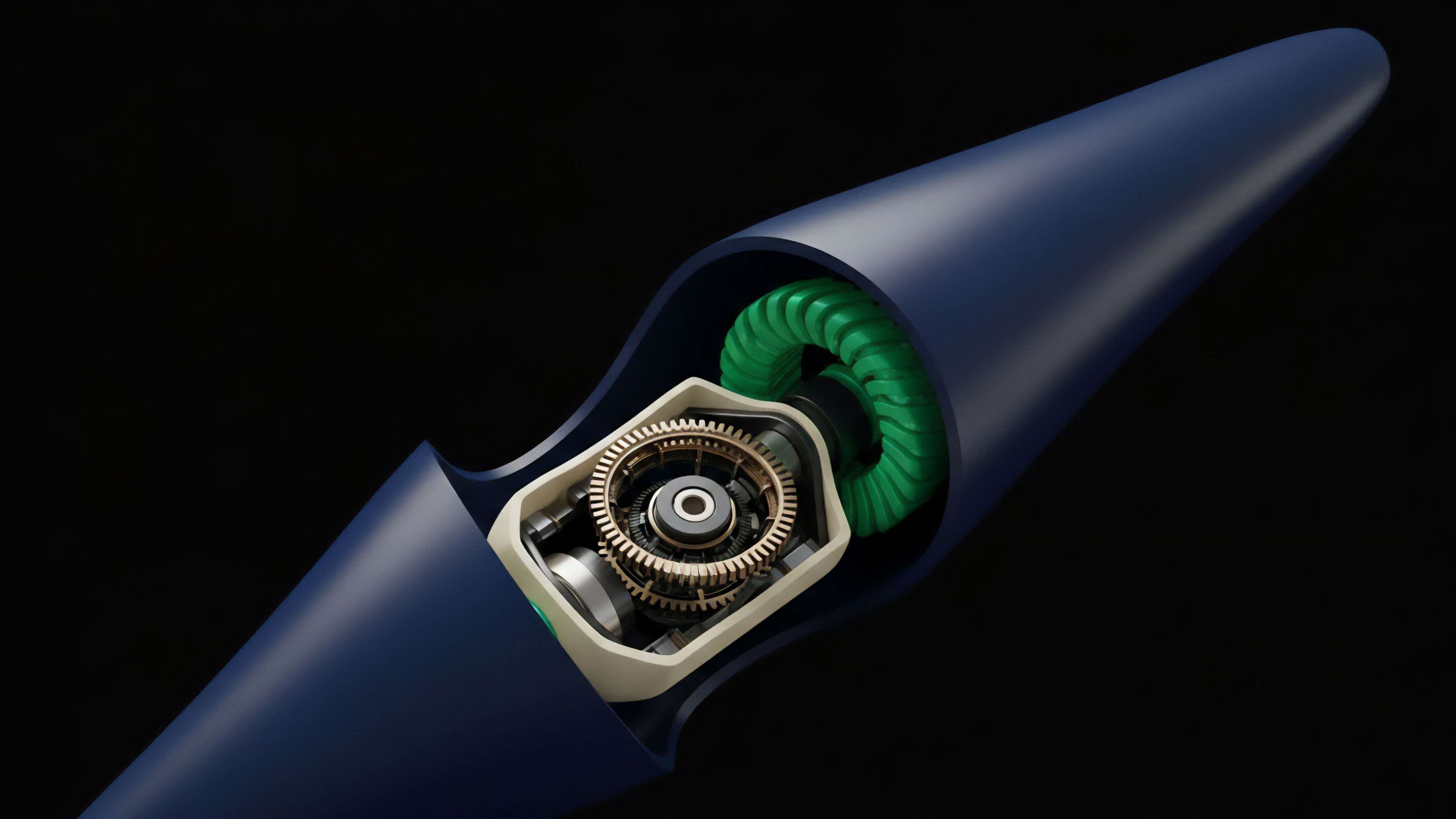
The architectural health of a network relies on the rigorous examination of its execution environment. Security professionals scrutinize the interaction between smart contracts and the underlying consensus layer to identify potential points of failure. This examination ensures that the economic incentives intended by the developers align with the technical realities of the virtual machine.
Every line of code exists as a potential vector for capital loss, necessitating a defensive posture that assumes constant hostility from the environment. The objective of these assessments involves the identification of logic flaws that could lead to unauthorized asset drainage or governance manipulation. By simulating various attack scenarios, auditors provide a probabilistic guarantee of system resilience.
This guarantee serves as the foundation for institutional participation and retail confidence, providing the necessary assurance that the protocol operates as intended under extreme market conditions.

Origin
The necessity for rigorous security protocols emerged from the catastrophic failures of early decentralized experiments. High-profile exploits, such as the 2016 DAO incident, demonstrated that immutable code requires exhaustive validation before deployment. These events established a precedent where the cost of a post-deployment patch is often the total value locked within the system.
The industry shifted from a culture of rapid iteration to one of defensive engineering.
- The DAO Exploit established the requirement for reentrancy protection and rigorous logic flow analysis.
- Parity Multi-sig Failures highlighted the risks associated with library dependencies and uninitialized proxy contracts.
- Flash Loan Attacks necessitated the study of oracle manipulation and cross-protocol price dependencies.
- Cross-Chain Bridge Breaches revealed the vulnerabilities inherent in off-chain validators and multisig orchestration.
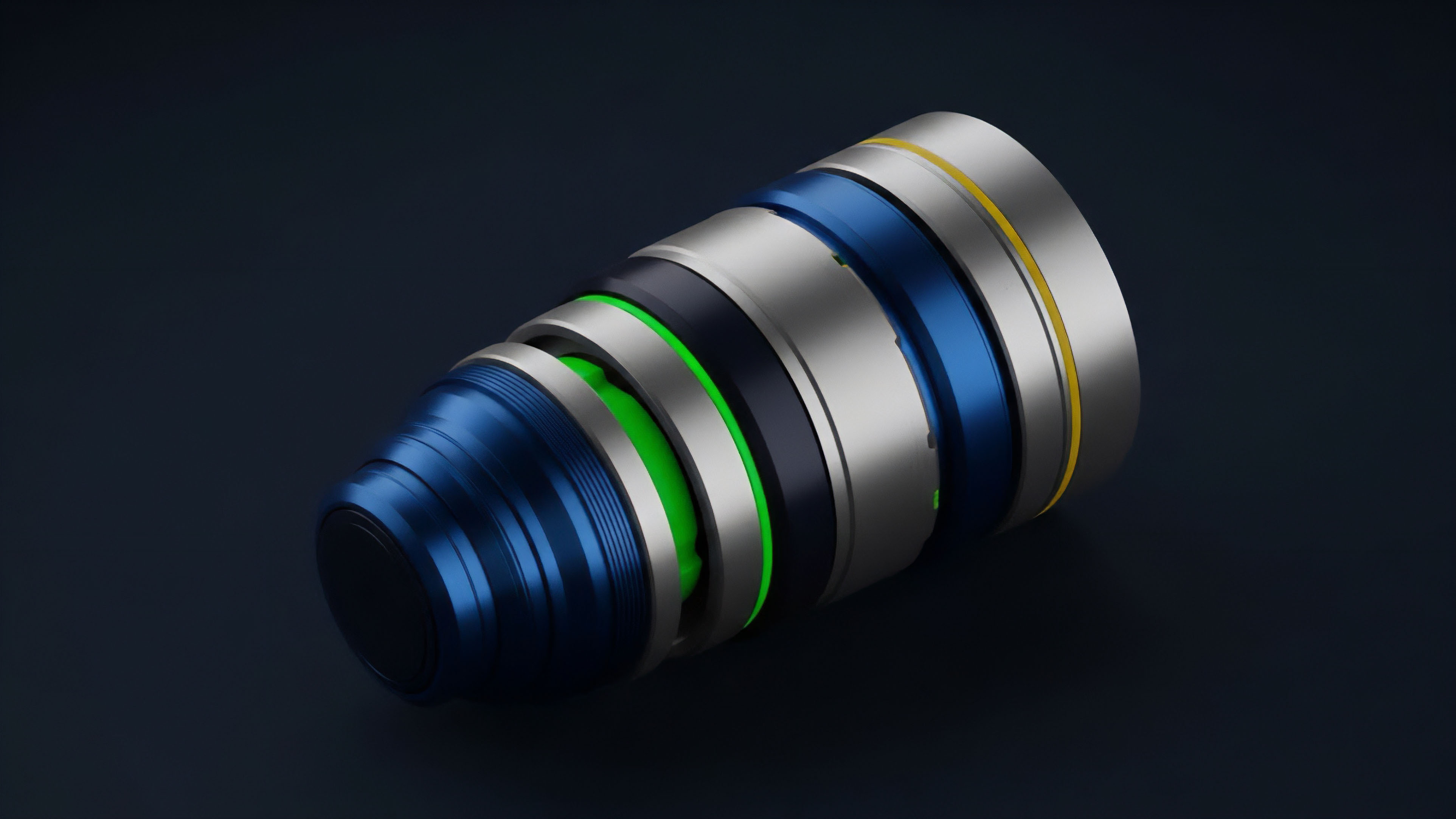
As decentralized finance grew in complexity, the scope of assessments expanded from simple contract reviews to comprehensive system-wide evaluations. The rise of composability meant that a vulnerability in one protocol could propagate through the entire market. This interconnectedness forced the development of standardized security frameworks and the professionalization of specialized auditing firms.
The historical record of losses provides the empirical data used to refine modern detection algorithms.

Theory
The theoretical basis for Blockchain Network Security Audits and Vulnerability Assessments rests upon formal verification and symbolic execution. Formal verification utilizes mathematical proofs to demonstrate that a contract adheres to its specifications under all possible inputs. This methodology treats the code as a set of logical propositions, allowing for the exhaustive search of the state space.
Symbolic execution complements this by replacing concrete values with symbolic variables, identifying paths that lead to erroneous states. Entropy in information systems suggests that without these rigorous checks, the complexity of a codebase will naturally trend toward fragility.
| Methodology | Primary Focus | Verification Depth |
|---|---|---|
| Static Analysis | Code structure and syntax patterns | Surface level vulnerability detection |
| Dynamic Analysis | Runtime behavior and state changes | Execution path validation |
| Formal Verification | Mathematical proof of correctness | Exhaustive logical certainty |
| Fuzzing | Randomized input stress testing | Edge case identification |
Security assessments also incorporate game-theoretic modeling to evaluate the robustness of incentive structures. This involves analyzing the equilibrium states of a protocol to ensure that rational participants cannot profit by subverting the intended operation. Auditors examine the cost of attack versus the potential reward, seeking to maintain a high economic barrier to entry for malicious actors.
The interaction between technical code and economic behavior creates a multi-dimensional risk surface that requires constant monitoring. This analytical rigor ensures that the protocol remains resilient against both technical exploits and strategic manipulation.
Vulnerability assessment protocols quantify the probability of systemic failure across interconnected liquidity pools.
The study of Blockchain Network Security Audits and Vulnerability Assessments requires an understanding of the Ethereum Virtual Machine or equivalent execution environments. Vulnerabilities often arise from the discrepancy between high-level language abstractions and low-level bytecode execution. Common issues include integer overflows, timestamp dependence, and improper access control.
Professional auditors utilize automated tools to flag these patterns while relying on manual review to uncover complex logic errors that machines might overlook. This dual approach maximizes the probability of discovering hidden flaws before they are exploited in a live environment.

Approach
Current industry standards for Blockchain Network Security Audits and Vulnerability Assessments follow a structured sequence of discovery and remediation. The process begins with a comprehensive review of the project documentation to understand the intended functionality and risk profile.
Subsequently, auditors perform automated scans to identify common vulnerabilities, followed by an intensive manual line-by-line code review. This manual phase remains the most effective method for identifying sophisticated logic errors and economic attack vectors.
- Documentation Review involves establishing the intended state transitions and security assumptions of the developers.
- Automated Tooling utilizes static analyzers and linters to detect known vulnerability patterns and coding standard violations.
- Manual Logic Analysis focuses on the interaction between functions and the integrity of the state management system.
- Reporting and Remediation provides the development team with a detailed list of findings categorized by severity and impact.
Vulnerability assessments also utilize bug bounty programs to leverage the collective intelligence of the global security community. These programs offer financial rewards for the disclosure of flaws, creating a market-based incentive for ethical hacking. This continuous testing model supplements periodic audits, providing an ongoing defensive layer as the protocol evolves.
The integration of these various methodologies creates a robust security posture that protects both capital and reputation.
| Severity Level | Impact Description | Action Required |
|---|---|---|
| Critical | Direct risk of total fund loss or system shutdown | Immediate fix before deployment |
| High | Potential for significant asset drainage or manipulation | Remediation required prior to launch |
| Medium | Limited impact on user funds or protocol state | Fix recommended during development cycle |
| Low | Optimization issues or minor coding deviations | Optional improvements for code quality |

Evolution
The transition from manual code reviews to automated, real-time security monitoring marks a significant shift in the defensive capabilities of the sector. Early assessments were static events, providing a snapshot of security at a single point in time. However, the introduction of upgradeable contracts and complex governance mechanisms rendered this approach insufficient.
Modern security strategies now incorporate continuous integration and deployment pipelines that automatically run security suites on every code change. This shift ensures that security remains a constant consideration throughout the lifecycle of the project. The professionalization of the auditing space has led to the emergence of specialized firms that focus on specific niches, such as zero-knowledge circuits or cross-chain messaging protocols.
This specialization allows for a deeper level of expertise in increasingly complex technical domains. Additionally, the market has seen the rise of decentralized security collectives that utilize community-driven reviews to provide a more transparent and diverse set of perspectives. This democratization of security auditing increases the total number of eyes on the code, reducing the likelihood of a single point of failure in the assessment process.
Insurance protocols have also begun to play a role in the security landscape by providing coverage against smart contract exploits. These protocols utilize the results of Blockchain Network Security Audits and Vulnerability Assessments to price their premiums, creating a direct financial link between security quality and capital efficiency. This market-driven approach incentivizes developers to prioritize security, as higher audit scores lead to lower insurance costs and increased liquidity.
The convergence of technical auditing and financial risk management creates a more resilient and sustainable market.

Horizon
The future of Blockchain Network Security Audits and Vulnerability Assessments involves the integration of artificial intelligence and machine learning to predict and prevent exploits before they occur. These technologies can analyze vast amounts of transaction data to identify patterns indicative of an impending attack, allowing for automated circuit breakers to pause the protocol. This proactive stance moves beyond simple code review toward active defense and real-time threat mitigation.
The transition to real-time security monitoring shifts the defensive posture from reactive patching to proactive state validation.
Real-time monitoring tools will become standard for all major protocols, providing constant visibility into the health of the network. These tools track state variables and event logs to detect anomalies that might signal a vulnerability being tested by an adversary. Concomitantly, formal verification tools will become more accessible to developers, allowing for the integration of mathematical proofs directly into the development workflow. This will lead to a future where code is secure by design, rather than secured through after-the-fact assessments. The development of decentralized security standards will further harmonize the industry, providing a clear set of benchmarks for protocol safety. These standards will facilitate better communication between auditors, developers, and users, ensuring that everyone understands the risks and protections associated with a given protocol. As the infrastructure of decentralized finance continues to mature, the role of security assessments will remain central to the stability and growth of the global digital economy.

Glossary

Network Security
Bug Bounty

Proof of Stake Security
Symbolic Execution
Integer Overflow

Static Analysis

Denial of Service

Frontrunning
Smart Contract Security