Essence
Protocol Integrity defines the operational fidelity of a decentralized financial application. It represents the assurance that a smart contract system, particularly one managing complex financial instruments like options, will execute exactly according to its pre-defined logic, regardless of external market conditions or adversarial actions. In a decentralized environment, integrity replaces counterparty trust with cryptographic and economic guarantees.
The core challenge lies in creating systems where the code’s execution aligns perfectly with the economic intent of the protocol’s designers, even when facing highly motivated attackers. The system’s integrity must hold against both technical exploits of the code and economic exploits of the underlying incentive structures. This requires a shift in perspective from traditional financial integrity, which relies on legal frameworks and centralized oversight, to a model where integrity is an emergent property of robust system design.
Integrity in decentralized systems requires that the cost of violating the protocol’s rules always exceeds the potential profit from doing so.
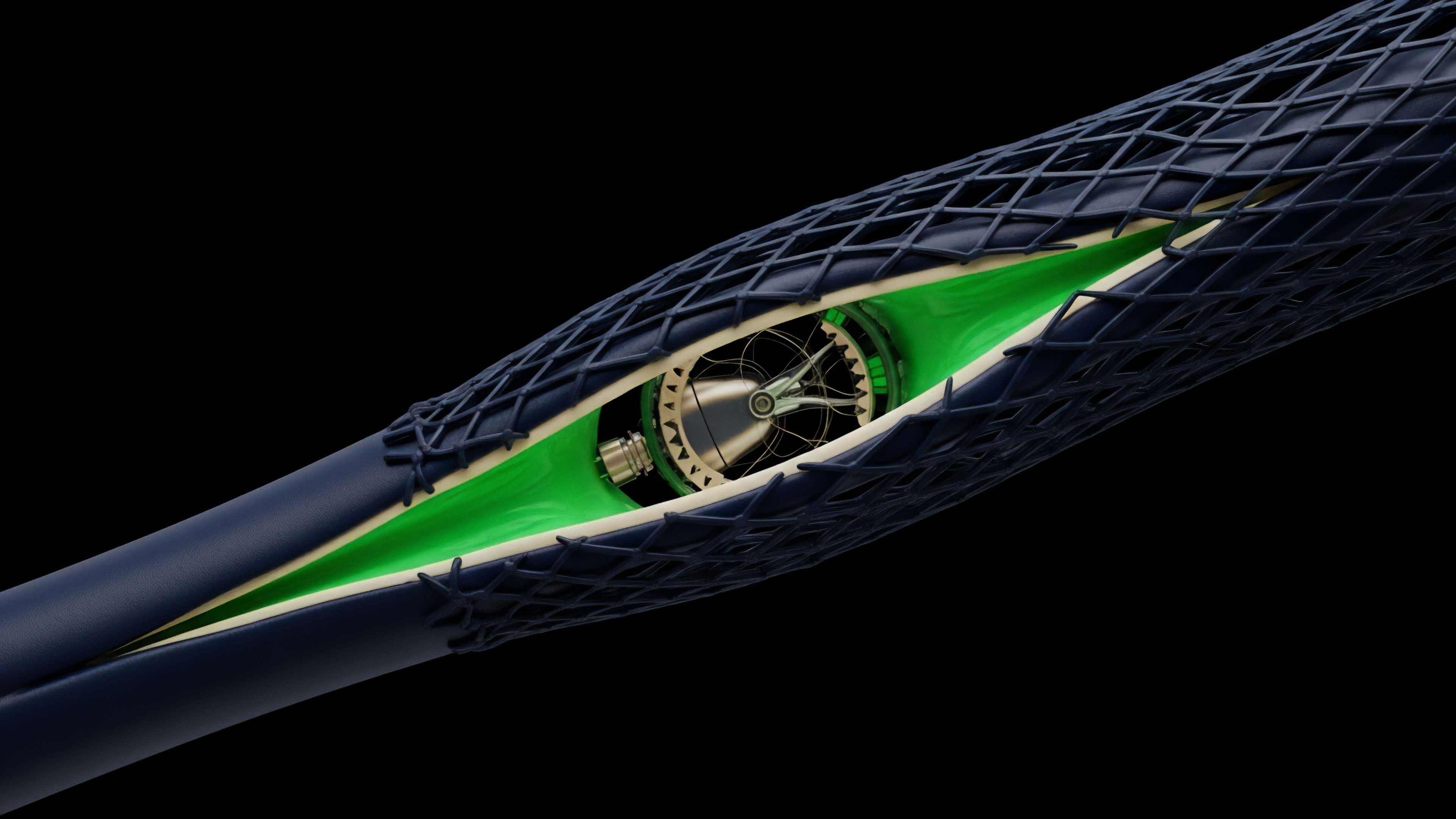
The integrity of a derivatives protocol is not a single point of failure but a complex chain of dependencies. It begins with the accuracy of the underlying asset price feed, extends through the mathematical correctness of the pricing model, and concludes with the reliability of the liquidation engine and collateral management system. If any link in this chain fails, the entire system can unravel, leading to cascading liquidations and a loss of confidence.
The design of these systems must anticipate and mitigate a wide range of attack vectors, including oracle manipulation, front-running, and flash loan attacks, all of which exploit the time-sensitive nature of options pricing and settlement.

Origin
The concept of protocol integrity emerged from the failures of early crypto derivatives platforms. Before the rise of decentralized finance, crypto derivatives were primarily traded on centralized exchanges (CEXs).
These platforms were susceptible to opaque counterparty risk, market manipulation, and flash crashes. The integrity of these systems relied on the discretion of the centralized operator. The transition to on-chain derivatives protocols introduced new challenges, specifically the need to replicate complex financial operations within the deterministic constraints of a blockchain environment.
Early attempts to create options protocols struggled with fundamental issues, such as accurately calculating volatility and managing margin requirements in real time without a central clearinghouse. The “DeFi Summer” of 2020 exposed significant vulnerabilities in protocols that attempted to create derivatives without fully considering the adversarial nature of the blockchain. A common failure mode involved oracle manipulation, where attackers could temporarily skew the reported price of an asset, triggering incorrect liquidations or allowing for under-collateralized loans to be taken out.
These events highlighted that integrity could not simply be assumed by moving code onto a blockchain; it had to be meticulously engineered into the economic model itself. The evolution of integrity in options protocols has been a response to these early exploits, leading to the development of more sophisticated oracle architectures and risk parameter management systems.
Theory
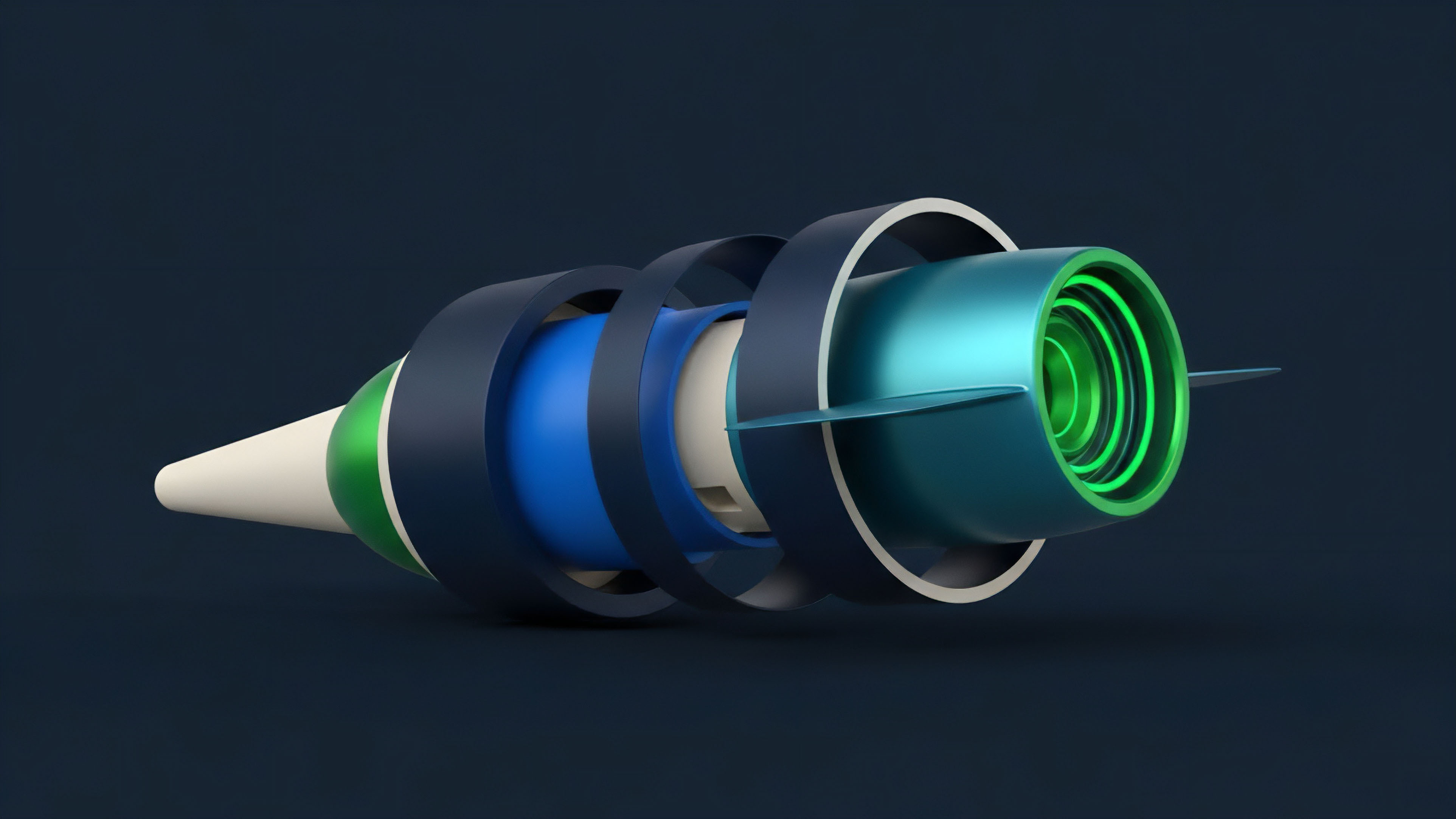
The theoretical foundation of protocol integrity rests on three pillars: cryptographic security, economic incentive alignment, and system resilience.
Cryptographic security ensures that the state transitions of the protocol are verifiable and tamper-proof. Economic incentive alignment ensures that rational actors are incentivized to maintain the system’s integrity rather than exploit it. System resilience ensures the protocol can withstand extreme market volatility and adversarial pressure without catastrophic failure.
Oracle Vulnerability and Price Discovery
A primary theoretical challenge for options integrity is the “oracle problem.” Options pricing models rely heavily on accurate, real-time data for the underlying asset price and volatility. A compromised oracle can render all subsequent calculations incorrect, leading to mispricing, incorrect margin calls, and systemic risk. The theoretical design of an oracle must balance several trade-offs:
- Latency vs. Cost: Faster updates (lower latency) are more expensive due to gas fees, but slower updates (higher latency) create a window for price manipulation.
- Decentralization vs. Reliability: Using a single, highly reliable data source creates a single point of failure. Using a decentralized network of sources reduces this risk but introduces coordination challenges and potential data discrepancies.
- Data Source Quality: The choice between on-chain Automated Market Makers (AMMs) and off-chain data feeds (CEXs) presents a fundamental trade-off. AMMs can be manipulated via flash loans, while CEX feeds are subject to centralized control and network latency issues.

Collateralization and Liquidation Mechanics
The integrity of a derivatives protocol hinges on its collateralization model and liquidation mechanism. The theoretical goal is to maintain full collateralization at all times. This requires a robust liquidation process that can quickly and efficiently close under-collateralized positions.
The liquidation engine itself must be designed with game theory in mind. If liquidators are not sufficiently incentivized to act quickly, or if the system creates a “bank run” scenario during extreme volatility, the protocol’s integrity fails.

The Role of Greeks in Protocol Physics
In traditional finance, the “Greeks” (Delta, Gamma, Vega, Theta) quantify risk exposure. In decentralized options protocols, these metrics are essential for maintaining integrity. The protocol’s internal risk engine must continuously calculate these values to ensure that a protocol’s overall exposure remains within acceptable limits.
A sudden increase in Gamma or Vega exposure across all open positions can quickly destabilize the protocol if not properly managed. This requires a high-frequency, on-chain calculation capability, which is often difficult to implement efficiently due to blockchain constraints.
| Risk Component | Traditional Finance (Centralized) | Decentralized Finance (Protocol Integrity) |
|---|---|---|
| Counterparty Risk | Mitigated by legal contracts and clearinghouses. | Mitigated by collateral and smart contract logic. |
| Price Feed Integrity | Provided by regulated data vendors (e.g. Bloomberg, Refinitiv). | Provided by decentralized oracle networks (e.g. Chainlink, Tellor). |
| Liquidation Process | Managed by a central risk desk or clearinghouse. | Managed by autonomous liquidator bots and incentive structures. |
| Systemic Failure Mode | Contagion through interconnected institutions. | Contagion through shared smart contract vulnerabilities or oracle failures. |

Approach
The practical approach to building protocol integrity involves a layered defense strategy, focusing on both pre-emptive design and real-time risk mitigation. This strategy acknowledges that perfect integrity is unattainable and instead aims for maximum resilience against known attack vectors.

Designing Resilient Oracles
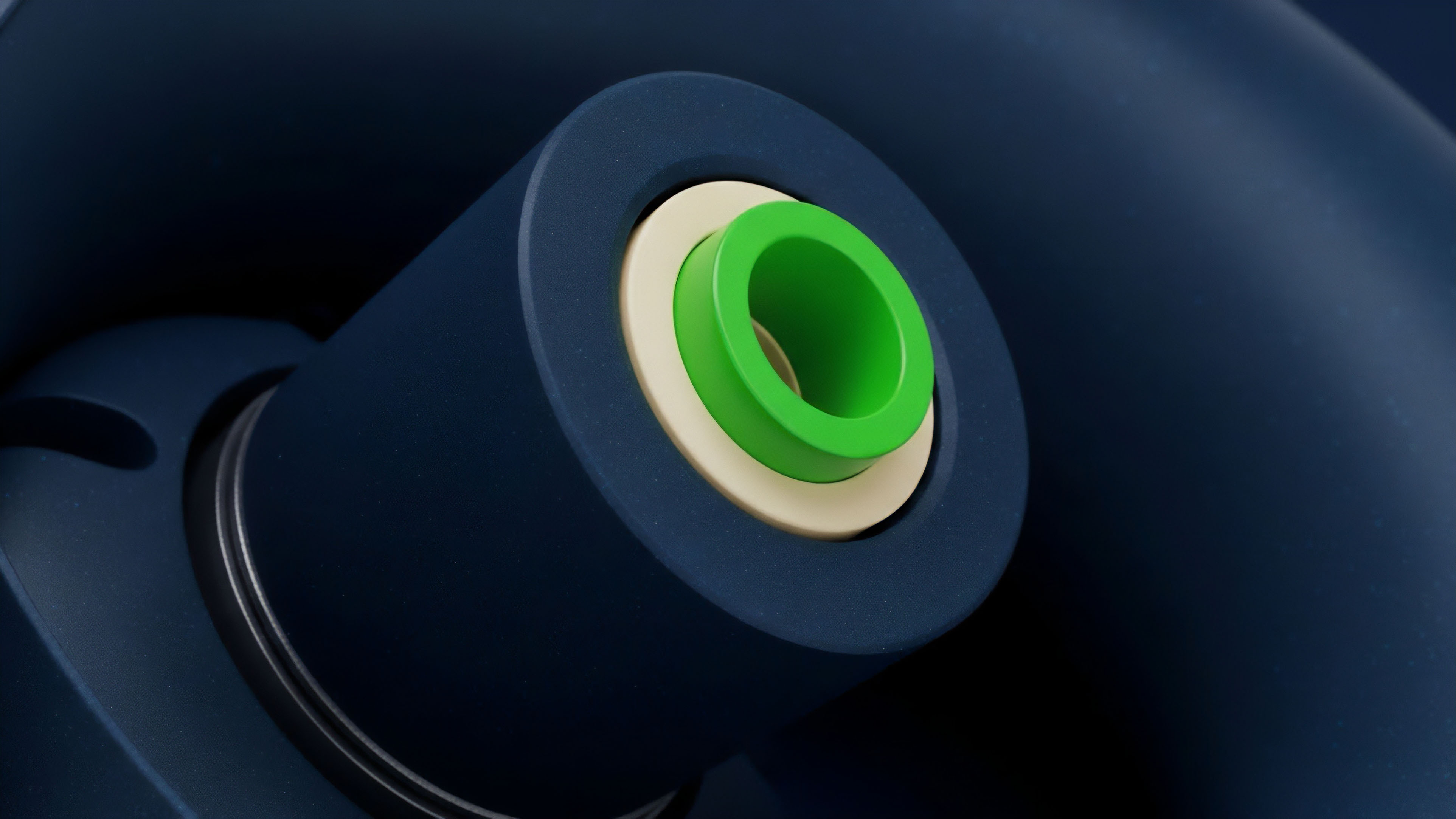
To protect against price manipulation, protocols must implement resilient oracle architectures. This involves moving beyond a single price feed to a composite model.
- Time-Weighted Average Price (TWAP): This method mitigates flash loan attacks by calculating the average price over a specified time window, making sudden price spikes less impactful.
- Decentralized Oracle Networks: Utilizing multiple independent oracle providers, often through a consensus mechanism, ensures that no single data provider can compromise the system.
- Volatility-Based Circuit Breakers: Protocols implement logic that pauses liquidations or trading if the price change exceeds a certain threshold within a short period. This prevents a cascading failure during extreme volatility events or manipulation attempts.

Liquidation Game Theory
A key aspect of integrity design is ensuring that liquidations happen promptly. The protocol must create incentives for external actors (liquidators) to monitor positions and close them when necessary. The “Pragmatic Market Strategist” approach to this involves designing the liquidation bonus to be high enough to incentivize action but not so high that it encourages front-running or a “liquidation race” that could overwhelm the network.
The goal is to create a stable, predictable mechanism that guarantees solvency without creating new attack surfaces.
A protocol’s integrity is only as strong as its liquidation engine’s ability to operate under stress. When liquidators stop performing, the system collapses.

Smart Contract Security and Audits
Before deployment, protocols undergo rigorous security audits and formal verification processes. These processes aim to identify vulnerabilities in the code that could compromise integrity. The audit process has evolved from simple code reviews to complex analyses of economic logic and incentive structures.
This proactive approach aims to find flaws in the design before they can be exploited by adversarial actors.

Evolution
The evolution of protocol integrity in options protocols has mirrored the increasing complexity of decentralized finance itself. Early protocols were simple, often relying on basic collateralization ratios and single-asset collateral.
The next generation of protocols introduced more sophisticated risk management techniques, including dynamic margin requirements based on real-time volatility and multi-asset collateral pools.

Cross-Protocol Risk and Contagion
As the DeFi ecosystem expanded, protocols became interconnected. A failure in one protocol, such as a lending platform, can now create systemic risk for an options protocol that uses its tokens as collateral. This “systemic risk contagion” presents a new challenge for integrity.
Protocols must now consider not only their internal integrity but also the integrity of all external protocols they rely upon. This has led to the development of “Protocol-Owned Liquidity” (POL) models, where protocols attempt to reduce external dependencies by holding their own assets, thereby insulating themselves from broader market failures.
The Rise of Layer 2 Integrity
The shift to Layer 2 scaling solutions introduces new integrity challenges. Optimistic rollups, for example, rely on a challenge period where users can dispute incorrect state transitions. The integrity of an options protocol on an optimistic rollup depends on the assumption that an honest actor will always challenge a fraudulent state transition.
This creates a new layer of game theory and economic security to manage, distinct from the base layer’s integrity.
The integrity of a system is a function of its security, decentralization, and scalability. Trade-offs in one area inevitably impact the others.

Horizon
Looking ahead, the future of protocol integrity will be defined by the integration of AI-driven risk management and the expansion of cross-chain operations. As protocols become more complex, manual risk parameter tuning will become insufficient. AI models will be necessary to analyze real-time market data and adjust collateralization ratios, liquidation thresholds, and volatility surfaces automatically.

AI-Driven Risk Engines
The next generation of options protocols will use machine learning to predict market behavior and preemptively adjust risk parameters. This moves integrity from a static state to a dynamic one. The system will learn from past failures and adapt to new market conditions, making it more resilient against novel attack vectors.
However, this introduces a new risk: the integrity of the AI model itself. If the model is flawed or trained on manipulated data, it could introduce new vulnerabilities.
Cross-Chain Integrity and Atomicity
As liquidity fragments across different blockchains, maintaining integrity requires ensuring atomic settlement across multiple chains. This involves complex messaging protocols and cross-chain bridges. A failure in a cross-chain bridge could compromise the integrity of collateral locked on one chain that is backing a derivative position on another.
The future of integrity will depend on solving this “interoperability dilemma,” ensuring that the integrity of the overall system is not compromised by the weakest link in the cross-chain communication stack. The challenge is to maintain the deterministic guarantees of a single blockchain across a heterogeneous network.
The Systems Architect’s Challenge
The systems architect must move beyond a simple view of code security. The true challenge lies in designing systems where the economic incentives and game theory ensure that a protocol’s integrity is maintained even when a technical exploit might be possible. This requires a deep understanding of human behavior under stress, combined with rigorous quantitative modeling.
The long-term success of decentralized finance hinges on our ability to build systems where integrity is not just a feature, but an unassailable property of the design.
| Integrity Challenge | Current State of Solution | Horizon Goal |
|---|---|---|
| Oracle Latency | TWAP and decentralized oracle networks. | AI-driven predictive price feeds. |
| Liquidation Efficiency | Incentivized liquidator bots with fixed bonuses. | Dynamic, automated liquidation engines based on real-time risk. |
| Cross-Chain Risk | Single-chain deployments or bridge reliance. | Atomic cross-chain settlement protocols. |

Glossary

Collateral Integrity

Protocol Integrity Financialization

Order Submission Integrity
Collateral Pool Integrity

Financial Integrity Standards

Decentralized Volatility Integrity Protocol
Protocol Integrity Valuation

Digital Asset Market Integrity

Derivative Systems Integrity