Essence
Privacy preserving techniques are a fundamental requirement for building robust, institutional-grade derivatives markets on-chain. The open nature of public blockchains creates a systemic vulnerability: information asymmetry. In traditional finance, market makers rely on proprietary models and private order books to protect their pricing strategies.
When every transaction, collateral level, and pending order is publicly broadcast, these strategies become exploitable. The core function of these techniques is to allow a party to prove a financial condition ⎊ such as having sufficient collateral for a trade or meeting a liquidation threshold ⎊ without revealing the specific data points underlying that proof. This capability transforms the market microstructure by mitigating front-running and eliminating maximal extractable value (MEV) opportunities that arise from transaction ordering and information leakage.
The challenge in decentralized derivatives is creating a truly permissionless environment where participants can interact without compromising their strategic advantage. A transparent system, while ideal for auditability, exposes market makers to immediate exploitation by sophisticated high-frequency trading (HFT) bots. These bots can observe large incoming orders and front-run them, extracting value from the legitimate market maker before the trade executes.
Privacy preserving techniques address this by allowing for confidential transactions and hidden order books, creating a more level playing field. The ability to transact without revealing intent is not a luxury; it is a prerequisite for achieving deep liquidity and attracting professional market participants who operate on razor-thin margins.
Privacy preserving techniques are essential to mitigate information asymmetry and front-running in decentralized derivatives markets.

Origin
The necessity for private trading environments originates from the earliest days of financial markets. In traditional finance, this need led to the creation of dark pools and over-the-counter (OTC) markets, where large institutional orders could be executed without public price discovery. The advent of high-frequency trading further emphasized the need for order flow protection.
In the context of crypto, the problem intensified with the rise of decentralized exchanges (DEXs). While initial DEX designs prioritized transparency, they quickly became battlegrounds for sophisticated bots that exploited the public mempool ⎊ the pending transaction queue ⎊ to profit from transaction ordering. This phenomenon, known as MEV, revealed that the very transparency celebrated by early DeFi protocols was a design flaw for derivatives trading.
The initial attempts to solve this problem involved simple batch auctions, where orders were collected and settled at a specific interval to reduce front-running opportunities. However, these solutions introduced latency and execution risk. The intellectual leap occurred when developers began to apply cryptographic primitives originally designed for privacy coins, like Zcash, to general-purpose financial applications.
The core concept of zero-knowledge proofs (ZKPs) ⎊ proving a statement without revealing the underlying data ⎊ was adapted from its initial use case of hiding transaction amounts to verifying collateral requirements in derivatives protocols. This transition marked a shift from simple design adjustments to cryptographic solutions for market microstructure problems.

Theory
The theoretical foundation of privacy preserving derivatives rests on several cryptographic primitives, each offering a distinct trade-off between privacy, computational cost, and trust assumptions.
The primary tools in this domain are zero-knowledge proofs, secure multi-party computation, and trusted execution environments. Understanding these mechanisms is essential for analyzing protocol design.

Zero-Knowledge Proofs
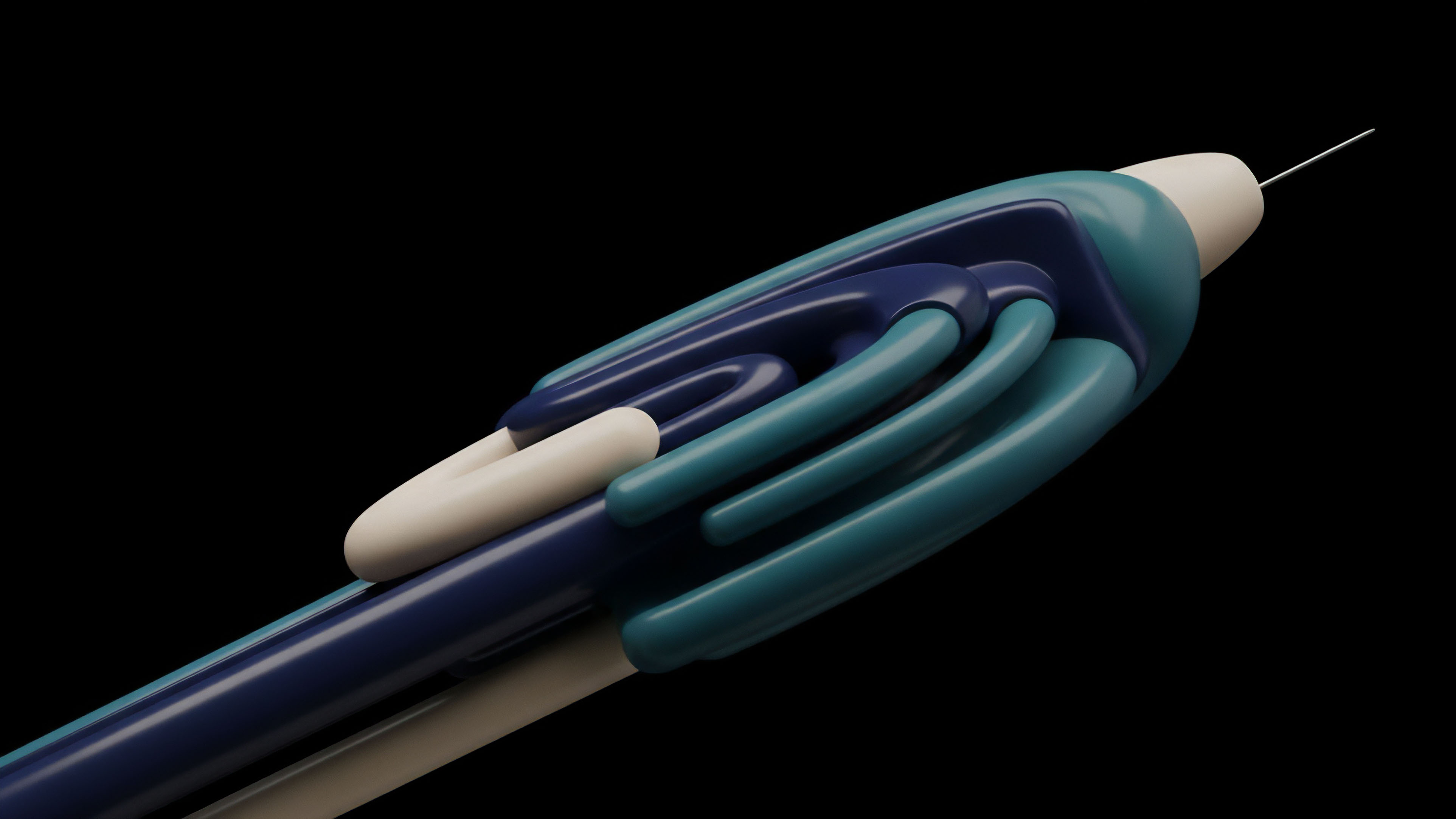
Zero-knowledge proofs (ZKPs) allow a prover to convince a verifier that a statement is true without disclosing any information beyond the validity of the statement itself. In the context of options, this means a user can prove they hold enough collateral to open a position without revealing the specific size of their collateral or the details of their position. The underlying logic relies on complex mathematical equations and cryptographic commitments.
The primary challenge with ZKPs in a high-frequency trading environment is the computational cost associated with generating the proof, which can add significant latency to the trading process. However, recent advancements in specific ZKP types like zk-SNARKs and zk-STARKs have improved efficiency, making them increasingly viable for on-chain derivatives.

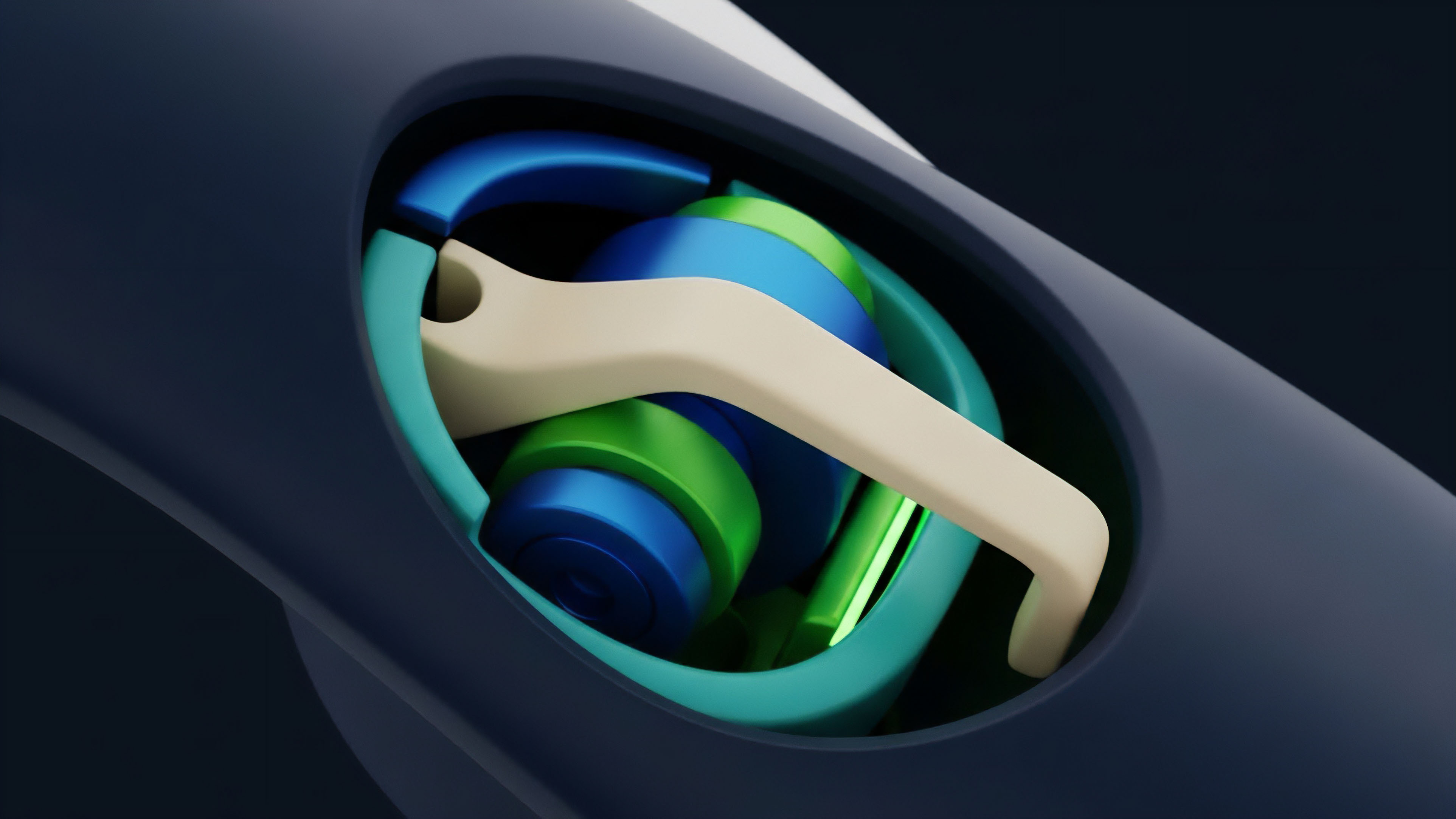
Secure Multi-Party Computation
Secure multi-party computation (MPC) distributes a computation across multiple parties, ensuring that no single party learns the inputs of the others. In a decentralized options market, MPC can be used to manage a private order book. Instead of a single centralized entity matching orders, several independent nodes perform the matching calculation in a way that preserves the privacy of individual bids and asks.
The final result ⎊ the execution price and quantity ⎊ is revealed, but the inputs remain hidden. MPC offers strong privacy guarantees without requiring complex proof generation for every transaction, but it introduces complexity in coordinating multiple parties and managing potential collusion among them.

Trusted Execution Environments
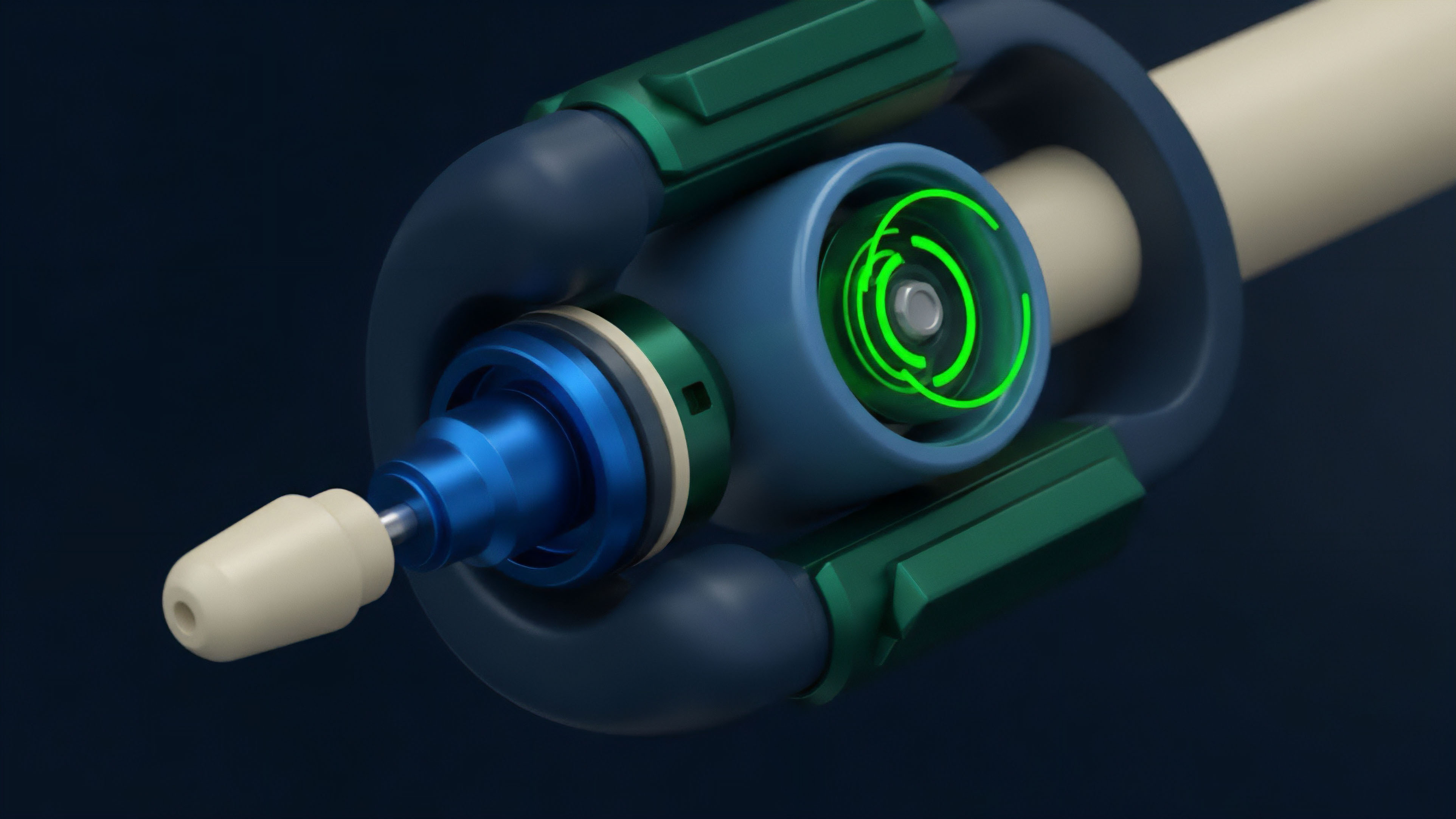
Trusted execution environments (TEEs) offer a hardware-based approach to privacy. A TEE is a secure area within a main processor that guarantees code and data loaded inside are protected in terms of confidentiality and integrity. TEEs create a secure enclave where order matching and liquidation calculations can occur off-chain without being visible to external observers.
The results are then committed back to the blockchain. While highly efficient, TEEs introduce a trust assumption in the hardware manufacturer and require a specific hardware configuration for nodes, which can compromise decentralization and censorship resistance.
| Technique | Mechanism | Trust Assumption | Primary Application in Derivatives |
|---|---|---|---|
| Zero-Knowledge Proofs (ZKPs) | Cryptographic proof generation | Mathematical integrity of the proof system | Collateral verification, position size privacy |
| Secure Multi-Party Computation (MPC) | Distributed computation across multiple nodes | No single node colludes with others | Private order matching, key management |
| Trusted Execution Environments (TEEs) | Hardware-based secure enclave | Integrity of hardware manufacturer and code attestation | Off-chain calculation and settlement |

Approach
Implementing privacy preserving techniques requires a shift in how market microstructure is designed, moving away from simple transparent order books toward more complex mechanisms that prioritize confidentiality. The most critical application of these techniques is in mitigating front-running and protecting the intellectual property of market makers.

Mitigating Front-Running and MEV
Front-running occurs when an entity observes a pending transaction and submits a similar transaction with higher fees to execute first, capturing the profit from the original transaction. In options markets, this is particularly damaging for market makers who provide liquidity by quoting prices. A bot can observe a market maker’s quote and immediately execute a trade based on that information before the market maker can adjust their pricing model.
Privacy preserving techniques address this directly by obfuscating order flow.
- Private Order Matching: The most straightforward approach is to prevent orders from being broadcast to a public mempool before execution. Protocols using MPC or TEEs create private order books where bids and asks are matched confidentially.
- Liquidation Privacy: A user’s margin level is highly sensitive information. If a user approaches liquidation, public knowledge of this state creates an opportunity for liquidation bots to front-run the process. ZKPs allow protocols to verify a user’s margin level against a threshold without revealing the specific value, ensuring that liquidations can only be triggered when necessary, without providing an exploitable window for external actors.
- Volatility Skew Protection: Market makers in options markets rely on proprietary models to price volatility skew ⎊ the implied volatility difference between out-of-the-money and in-the-money options. If trade data is public, competitors can reverse engineer these models. Privacy preserving techniques protect this data, allowing market makers to maintain their strategic edge and provide more competitive pricing.
Impact on Liquidity Provision
The ability to protect order flow directly impacts liquidity provision. Market makers are less willing to commit capital to markets where their strategies are easily exploited. By implementing privacy techniques, protocols can attract deeper institutional liquidity.
This leads to tighter spreads and better execution prices for all participants. The systemic implication is a transition from a market dominated by predatory HFT to one driven by genuine liquidity provision and risk management.
The implementation of private order books protects market makers from front-running, fostering deeper liquidity and more efficient price discovery.
Evolution
The evolution of privacy preserving techniques in crypto derivatives reflects a progression from theoretical ideals to practical, albeit costly, implementations. Early attempts focused on off-chain computation, where a trusted third party or a centralized server handled sensitive calculations before committing the result to the blockchain. This approach sacrificed decentralization for efficiency and privacy.
The current generation of protocols moves toward hybrid models. These models use ZKPs to verify off-chain calculations. A common approach involves using a specialized off-chain computation layer, where all sensitive data and order matching logic are processed.
ZKPs are then used to generate a proof of correct execution, which is submitted to the on-chain settlement layer. This separates the high-cost computation from the main blockchain, maintaining scalability while ensuring data integrity. The development of ZK-rollups has significantly accelerated this evolution.
While ZK-rollups primarily focus on scaling transactions, they provide a strong foundation for privacy-preserving applications. By bundling transactions and verifying them with a ZKP, a ZK-rollup can inherently obscure the individual transactions within the batch, offering a degree of privacy by default. This creates a new architectural pattern where privacy and scalability are integrated rather than treated as separate problems.
The challenge now shifts from proving individual transactions to proving the state transitions of an entire privacy-preserving rollup.
Horizon
The future trajectory of privacy preserving techniques points toward a complete re-architecture of decentralized finance. As ZKP technology matures and hardware acceleration reduces computational overhead, we anticipate a transition to fully on-chain, privacy-preserving derivatives protocols that offer institutional-grade confidentiality without compromising decentralization.
The long-term impact on market microstructure is profound. The current MEV-driven environment will be replaced by a new paradigm where information asymmetry is mitigated by cryptographic design rather than market-based solutions. This will create a more stable and efficient market where genuine liquidity providers can compete based on their pricing models and risk management capabilities, rather than their ability to front-run other participants.
The ultimate goal is to create a decentralized version of traditional dark pools, where large institutions can execute block trades without market impact. This requires not only technical solutions but also a new regulatory framework that recognizes the need for privacy in decentralized markets. The challenge lies in balancing this necessary confidentiality with the requirements for regulatory oversight and anti-money laundering compliance.
The next generation of protocols will need to incorporate selective disclosure mechanisms, allowing users to prove compliance to a regulator without revealing their full trading history to the public. This intersection of cryptography, regulation, and market design defines the next era of decentralized derivatives.
The future of decentralized derivatives involves on-chain dark pools and selective disclosure mechanisms, balancing market confidentiality with regulatory requirements.

Glossary

Proof Aggregation Techniques

Front-Running Mitigation Techniques

Crypto Trading Techniques
Privacy-Preserving Defi

Order Flow Analysis Tools and Techniques

Information Privacy

Privacy

Privacy Enhancing Technology

Pre-Trade Privacy